Internetworking Technologies
... The presented material should be adequate for a one-semester course at the senior undergraduate / graduate level. The organization is largely modular and therefore would permit an instructor to choose his own set of chapters in almost any sequence he considers suitable. The book assumes a basic know ...
... The presented material should be adequate for a one-semester course at the senior undergraduate / graduate level. The organization is largely modular and therefore would permit an instructor to choose his own set of chapters in almost any sequence he considers suitable. The book assumes a basic know ...
TCAM - Renesas e-Learning
... flow obey a pre-defined rule and are processed in a similar manner by the router. ...
... flow obey a pre-defined rule and are processed in a similar manner by the router. ...
Chapter 21 - William Stallings, Data and Computer Communications
... traffic within a tunnel that belongs to a Provider edge (PE) A device or set of particular VPN; i.e., the VC label is the tunnel devices at the edge of the provider network multiplexer in networks that use MPLS labels. with the functionality that is needed to interface with the customer. Virtual pri ...
... traffic within a tunnel that belongs to a Provider edge (PE) A device or set of particular VPN; i.e., the VC label is the tunnel devices at the edge of the provider network multiplexer in networks that use MPLS labels. with the functionality that is needed to interface with the customer. Virtual pri ...
Bluetooth Wireless System
... – emulates a serial-port to support a large base of legacy (serial-port-based) applications – allows multiple “ports” over a single physical channel between two devices ...
... – emulates a serial-port to support a large base of legacy (serial-port-based) applications – allows multiple “ports” over a single physical channel between two devices ...
IPv6 based NGN
... Relationship between NGN and IP NGN, by definition, is identified an infrastructure using packet technologies. – There is no specific mention which packet technology NGN should use, but generally assuming IP as a dominant packet technology today. – There are also no specific statement to specify t ...
... Relationship between NGN and IP NGN, by definition, is identified an infrastructure using packet technologies. – There is no specific mention which packet technology NGN should use, but generally assuming IP as a dominant packet technology today. – There are also no specific statement to specify t ...
DutyCon: A dynamic duty-cycle control approach to end
... Ohio State University, 805 Dreese Labs, 2015 Neil Ave., Columbus, OH 43210; emails: {wangxi, xwang, liul}@ece.osu.edu; G. Xing, Department of Computer Science and Engineering, Michigan State University, ...
... Ohio State University, 805 Dreese Labs, 2015 Neil Ave., Columbus, OH 43210; emails: {wangxi, xwang, liul}@ece.osu.edu; G. Xing, Department of Computer Science and Engineering, Michigan State University, ...
Sample Chapter
... to change the whole machine. In the present situation, they need to change only the second layer machine; the other two can remain the same. This is referred to as modularity. Modularity in this case means independent layers. A layer (module) can be defined as a black box with inputs and outputs, wi ...
... to change the whole machine. In the present situation, they need to change only the second layer machine; the other two can remain the same. This is referred to as modularity. Modularity in this case means independent layers. A layer (module) can be defined as a black box with inputs and outputs, wi ...
Chapter27(IPv6 and ICMPv6)
... assign to any new system that wants to be connected to the Internet. The Internet must accommodate real-time audio and video transmission. This type of transmission requires minimum delay strategies and reservation of resources not provided in the IPv4 design. The Internet must accommodate encryptio ...
... assign to any new system that wants to be connected to the Internet. The Internet must accommodate real-time audio and video transmission. This type of transmission requires minimum delay strategies and reservation of resources not provided in the IPv4 design. The Internet must accommodate encryptio ...
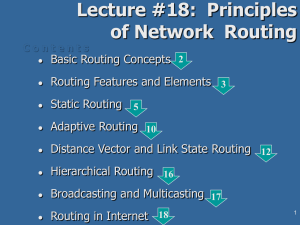
18. Principles of Network Routing
... service oriented (consider real-time and priority of the IP datagrames) congestion control (load balancing) considerations conservative: frequent alternative events are ignored! support of hierarchical routing: splitting of AS in areas and backbones security: routing table protection tunneling and t ...
... service oriented (consider real-time and priority of the IP datagrames) congestion control (load balancing) considerations conservative: frequent alternative events are ignored! support of hierarchical routing: splitting of AS in areas and backbones security: routing table protection tunneling and t ...
No Slide Title
... Maximum Transmission Unit There is a limit on the frame size of each data link layer protocol. This limit is called maximum transmission unit (MTU). MTUs for various data link layers: ...
... Maximum Transmission Unit There is a limit on the frame size of each data link layer protocol. This limit is called maximum transmission unit (MTU). MTUs for various data link layers: ...
pptx - Cambridge Computer Laboratory
... • LS: each node learns the complete network map; each node computes shortest paths independently and in parallel • DV: no node has the complete picture; nodes cooperate to compute shortest paths in a distributed manner ...
... • LS: each node learns the complete network map; each node computes shortest paths independently and in parallel • DV: no node has the complete picture; nodes cooperate to compute shortest paths in a distributed manner ...
3-1-3_Scalable
... • Each subnetwork has at least one Home Agent to manage membership • Each member of the subnet registers its own hierarchical address with Home Agent – periodical/event driven registration; stale addresses are timed out by Home Agent • Home Agent hierarchical addresses propagated via routing tables; ...
... • Each subnetwork has at least one Home Agent to manage membership • Each member of the subnet registers its own hierarchical address with Home Agent – periodical/event driven registration; stale addresses are timed out by Home Agent • Home Agent hierarchical addresses propagated via routing tables; ...
2 - Cambridge Computer Laboratory
... • LS: each node learns the complete network map; each node computes shortest paths independently and in parallel • DV: no node has the complete picture; nodes cooperate to compute shortest paths in a distributed manner ...
... • LS: each node learns the complete network map; each node computes shortest paths independently and in parallel • DV: no node has the complete picture; nodes cooperate to compute shortest paths in a distributed manner ...
TCP/IP Course - The Technology Firm
... A - IP Version: 4 bits (version 4) & IP Header Length: 8 bits. B - Type of Service: 8 bits. Routers ignore these values by default C – Total Length: 2 Bytes. Indicates the total length of IP header and IP Payload. D – Identification: 2 Bytes. Used to identify a specific packet sent between two stati ...
... A - IP Version: 4 bits (version 4) & IP Header Length: 8 bits. B - Type of Service: 8 bits. Routers ignore these values by default C – Total Length: 2 Bytes. Indicates the total length of IP header and IP Payload. D – Identification: 2 Bytes. Used to identify a specific packet sent between two stati ...