privacy anonymity
... In essence, a Chaum mixing network for HTTP JAP uses a single static address which is shared by many JAP users. That way neither the visited website, nor an eavesdropper can determine which user visited which website. Instead of connecting directly to a Web server, users take a detour, connecting wi ...
... In essence, a Chaum mixing network for HTTP JAP uses a single static address which is shared by many JAP users. That way neither the visited website, nor an eavesdropper can determine which user visited which website. Instead of connecting directly to a Web server, users take a detour, connecting wi ...
we know all the incoming query templates beforehand
... because of the synchronization requirements for multiple copies of the data. Different techniques have been investigated for data placement across multiple database servers, such as replication, partitioning and de-normalization. In this poster, we describe our architecture that utilizes these data ...
... because of the synchronization requirements for multiple copies of the data. Different techniques have been investigated for data placement across multiple database servers, such as replication, partitioning and de-normalization. In this poster, we describe our architecture that utilizes these data ...
Time Series Analyst - Jeffery S. Horsburgh
... WQ&Station=10109000&Variable=00010&StartDate=01/0 1/1975&EndDate=12/31/1994&Plotgraph=True ...
... WQ&Station=10109000&Variable=00010&StartDate=01/0 1/1975&EndDate=12/31/1994&Plotgraph=True ...
Explore Internet Resources
... that information you find may not be reliable. The databases the library offers on the internet are screened and edited. 2. Search Tools for the Internet Search engines are used to search for vast amounts of resources on the Internet. These engines are very useful when searching unique words or phra ...
... that information you find may not be reliable. The databases the library offers on the internet are screened and edited. 2. Search Tools for the Internet Search engines are used to search for vast amounts of resources on the Internet. These engines are very useful when searching unique words or phra ...
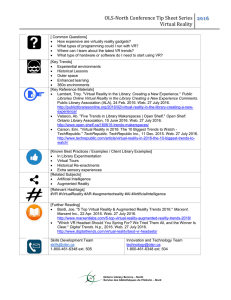
OLS-North Conference Tip Sheet Series Virtual Reality
... OLS-North Conference Tip Sheet Series 2016 Virtual Reality [ Common Questions] How expensive are virtually reality gadgets? What types of programming could I run with VR? Where can I learn about the latest VR trends? What type of hardware or software do I need to start using VR? [Key Trends] ...
... OLS-North Conference Tip Sheet Series 2016 Virtual Reality [ Common Questions] How expensive are virtually reality gadgets? What types of programming could I run with VR? Where can I learn about the latest VR trends? What type of hardware or software do I need to start using VR? [Key Trends] ...
Creating a Knowledge Base From a Collaboratively Generated
... of hyponymic/hyperonymic relations will allow us to compute lexical semantic measures which will further increase the performance of our coreference resolution system, as well as further bringing forward Wikipedia as a direct competitor of manuallydesigned resources such as WordNet. In order to make ...
... of hyponymic/hyperonymic relations will allow us to compute lexical semantic measures which will further increase the performance of our coreference resolution system, as well as further bringing forward Wikipedia as a direct competitor of manuallydesigned resources such as WordNet. In order to make ...
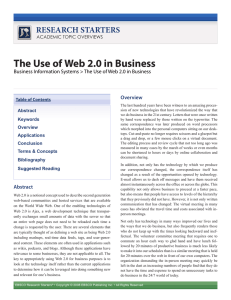
The Use of Web 2.0 in Business
... One of the enabling technologies of Web 2.0 is Ajax, or asynchronous JavaScript + XML. Ajax is a web development technique that transparently exchanges small amounts of data with the server so that an entire web page does not need to be reloaded each time a change is requested by the user. Ajax help ...
... One of the enabling technologies of Web 2.0 is Ajax, or asynchronous JavaScript + XML. Ajax is a web development technique that transparently exchanges small amounts of data with the server so that an entire web page does not need to be reloaded each time a change is requested by the user. Ajax help ...
RDF Resource Description Framework
... A standard for encoding metadata and other information on the Semantic Web ...
... A standard for encoding metadata and other information on the Semantic Web ...
EnviroInfo 2002: Hydroinformatic Web Application and Web Service
... A prediction of high water situation is one of the most essential hydrological tasks for a river basin management and is mainly performed by means of traditional conceptual and deterministic models using predicted precipitation. Due to ever increasing urbanization and the consequential short hydrolo ...
... A prediction of high water situation is one of the most essential hydrological tasks for a river basin management and is mainly performed by means of traditional conceptual and deterministic models using predicted precipitation. Due to ever increasing urbanization and the consequential short hydrolo ...
Dept.of Computer Science, KU. MCA 2013-14
... 3. ARTIFICIAL INTELLIGENCE By Patrick Henry Winston( Pearson) 4. PRINCIPLES OF ARTIFICIAL INTELLIGENCE (Narosa) 5. Artificial Intelligence By Shiart Russel Peter Norvig (Pearson) 6. EXPERT SYSTEMS SYSTEMS AND PRACTICE By Giarratano & Riely (Thomson) 7. ARTIFICIAL INTELLIGENCE APPLICATIONS PROGRAMMIN ...
... 3. ARTIFICIAL INTELLIGENCE By Patrick Henry Winston( Pearson) 4. PRINCIPLES OF ARTIFICIAL INTELLIGENCE (Narosa) 5. Artificial Intelligence By Shiart Russel Peter Norvig (Pearson) 6. EXPERT SYSTEMS SYSTEMS AND PRACTICE By Giarratano & Riely (Thomson) 7. ARTIFICIAL INTELLIGENCE APPLICATIONS PROGRAMMIN ...
Implementing a Web Browser with Web Defacement Detection
... Abstract—Website Defacement is an attack on a website that changes the visual appearance of the site or a webpage. These are typically the work of system crackers, who break into a web server and replace the hosted website with one of their own. The most common method of defacement is using SQL Inje ...
... Abstract—Website Defacement is an attack on a website that changes the visual appearance of the site or a webpage. These are typically the work of system crackers, who break into a web server and replace the hosted website with one of their own. The most common method of defacement is using SQL Inje ...
Deploying Softbots on the World Wide Web
... to learning about home pages; user feedback may be harnessed to learn in a variety of Web domains. ShopBot ShopBot5 is a softbot that carries out comparison shopping at Web vendors on a person’s behalf (Doorenbos, Etzioni, & Weld 1996). Whereas virtually all previous Web agents rely on hard-coded in ...
... to learning about home pages; user feedback may be harnessed to learn in a variety of Web domains. ShopBot ShopBot5 is a softbot that carries out comparison shopping at Web vendors on a person’s behalf (Doorenbos, Etzioni, & Weld 1996). Whereas virtually all previous Web agents rely on hard-coded in ...
Presentation
... • Use the “Hibernate” package to make the data access from the MDSPlus server faster • Allow researchers to retrieve and view the required dataset from the MDSPlus server using a web browser • Obtain information about researchers who use the data from the MDSPlus. • Track the actions of the Research ...
... • Use the “Hibernate” package to make the data access from the MDSPlus server faster • Allow researchers to retrieve and view the required dataset from the MDSPlus server using a web browser • Obtain information about researchers who use the data from the MDSPlus. • Track the actions of the Research ...
Integrating Multiple Web Sources
... – Mapping tables For finite domains (such as cities, countries, companies …) Simply maintain an enumerated list of possible formats for each object (New York, N.Y., NYC, New York City, Big Apple) ...
... – Mapping tables For finite domains (such as cities, countries, companies …) Simply maintain an enumerated list of possible formats for each object (New York, N.Y., NYC, New York City, Big Apple) ...
document - Greensprings School
... secure), FTP (file transfer protocol), TCP/IP (transmission control protocol/internet protocol) IP address Modem, browser, internet service provider (ISP), bandwidth, download, upload, streaming audio/ video, compression, decompression, cache Domain names, domain name system (DNS) Featur ...
... secure), FTP (file transfer protocol), TCP/IP (transmission control protocol/internet protocol) IP address Modem, browser, internet service provider (ISP), bandwidth, download, upload, streaming audio/ video, compression, decompression, cache Domain names, domain name system (DNS) Featur ...
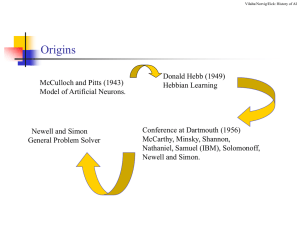
Pattern Classification: An Introduction
... Simon’s prediction: “computers will beat a chess champion in 10 years” “a significant theorem will be proved by a machine” ...
... Simon’s prediction: “computers will beat a chess champion in 10 years” “a significant theorem will be proved by a machine” ...
Nuclear Knowledge Bases and Portals
... • Applications based on KOS, e.g. search enhancement, querying KB’s, combining information from many sources, … ...
... • Applications based on KOS, e.g. search enhancement, querying KB’s, combining information from many sources, … ...
chapter1
... Requires that government agencies must give individuals with disabilities access to information technology that is comparable to the access available to others ...
... Requires that government agencies must give individuals with disabilities access to information technology that is comparable to the access available to others ...
Lecture 2
... net systematically (or in some cases, not so systematically), examining nodes, looking for a goal node. • Clearly following a cyclic path through the net is pointless because following A,B,C,D,A will not lead to any solution that could not be reached just by starting from A. • We can represent the p ...
... net systematically (or in some cases, not so systematically), examining nodes, looking for a goal node. • Clearly following a cyclic path through the net is pointless because following A,B,C,D,A will not lead to any solution that could not be reached just by starting from A. • We can represent the p ...
Data Browsing/Mining/Metadata
... • A leader in the development of innovative approaches has been the Open Geospatial Consortium (OGC) which focuses on melding environmental datasets into mapping systems. • Because self-describing formats (HDF, GRIB, NetCDF) are such important formats in these recent developments, general methods fo ...
... • A leader in the development of innovative approaches has been the Open Geospatial Consortium (OGC) which focuses on melding environmental datasets into mapping systems. • Because self-describing formats (HDF, GRIB, NetCDF) are such important formats in these recent developments, general methods fo ...
Outreach: joint slide set
... What is W3C WoT? • W3C WoT works on Web technology standards to enable applications and services that span IoT platforms on devices ranging from microcontrollers to cloud-based server farms. Focus on: – Thing to Thing interaction – Thing to IoT platform interaction ...
... What is W3C WoT? • W3C WoT works on Web technology standards to enable applications and services that span IoT platforms on devices ranging from microcontrollers to cloud-based server farms. Focus on: – Thing to Thing interaction – Thing to IoT platform interaction ...
Summay with a real world example
... SEC (Securities and Exchange Commission) http://www.sec.gov/ . The information relevant to this chapter is conveniently accessed through any of the previously mentioned sites. Let us use Yahoo for the moment. ...
... SEC (Securities and Exchange Commission) http://www.sec.gov/ . The information relevant to this chapter is conveniently accessed through any of the previously mentioned sites. Let us use Yahoo for the moment. ...
Knowledge representation
... The main problems considered in epistemology are: What is knowledge? Is genuine knowledge attainable at all? What are the limits of knowledge? From what faculties of the mind does knowledge originate? Which method should be used to obtain valid knowledge? How do you justify a priori stat ...
... The main problems considered in epistemology are: What is knowledge? Is genuine knowledge attainable at all? What are the limits of knowledge? From what faculties of the mind does knowledge originate? Which method should be used to obtain valid knowledge? How do you justify a priori stat ...
in the web page - University of Greenwich
... • Useful for data exchange and transformation • Facilitates separation of content from presentation • Enabling technology for web services and the semantic web © K.Mc 2008 ...
... • Useful for data exchange and transformation • Facilitates separation of content from presentation • Enabling technology for web services and the semantic web © K.Mc 2008 ...
Semantic Web
The Semantic Web is an extension of the Web through standards by the World Wide Web Consortium (W3C). The standards promote common data formats and exchange protocols on the Web, most fundamentally the Resource Description Framework (RDF).According to the W3C, ""The Semantic Web provides a common framework that allows data to be shared and reused across application, enterprise, and community boundaries"". The term was coined by Tim Berners-Lee for a web of data that can be processed by machines.While its critics have questioned its feasibility, proponents argue that applications in industry, biology and human sciences research have already proven the validity of the original concept.The 2001 Scientific American article by Berners-Lee, Hendler, and Lassila described an expected evolution of the existing Web to a Semantic Web. In 2006, Berners-Lee and colleagues stated that: ""This simple idea…remains largely unrealized"".In 2013, more than four million Web domains contained Semantic Web markup.