Double-Ended Priority Queues
... Since this mapping is slightly more complex than the ones used in twin heaps, min-max pair heaps, and interval heaps, actual implementations of the diamond deque are expected to be slightly slower than implementations of the remaining three structures. Since the twin heaps of [21], the min-max pair ...
... Since this mapping is slightly more complex than the ones used in twin heaps, min-max pair heaps, and interval heaps, actual implementations of the diamond deque are expected to be slightly slower than implementations of the remaining three structures. Since the twin heaps of [21], the min-max pair ...
Chapter 17 - University of Arizona
... Each node is an object with two instance variables: 1. A reference to the data of the current node ("Joe", "Sue", and "Kim" above) 2. A reference to the next element in the collection, indicated by the arrows The node with the reference value of null indicates the end of the linked structure. Becaus ...
... Each node is an object with two instance variables: 1. A reference to the data of the current node ("Joe", "Sue", and "Kim" above) 2. A reference to the next element in the collection, indicated by the arrows The node with the reference value of null indicates the end of the linked structure. Becaus ...
Open Data Structures (in C++)
... There are plenty of books that teach introductory data structures. Some of them are very good. Most of them cost money, and the vast majority of computer science undergraduate students will shell-out at least some cash on a data structures book. There are a few free data structures books available o ...
... There are plenty of books that teach introductory data structures. Some of them are very good. Most of them cost money, and the vast majority of computer science undergraduate students will shell-out at least some cash on a data structures book. There are a few free data structures books available o ...
• Data Structures and Data Types
... Memory. Proportional to client-supplied capacity, not number of items. ...
... Memory. Proportional to client-supplied capacity, not number of items. ...
Data Representation and Linear Structures
... first->data = x; // put x in head node while (current->data != x) { current = current->link); index++; ...
... first->data = x; // put x in head node while (current->data != x) { current = current->link); index++; ...
linked list
... may not issue an error message (depending on the details of the code), and even if it does, the error message may be quite strange – Look for a missing when a program that uses nodes with type
parameters gets a strange error message or doesn't run correctly
...
... may not issue an error message (depending on the details of the code), and even if it does, the error message may be quite strange – Look for a missing
Experimental B+-tree for GPU
... Single thread checks key in the middle of searched array continuing search in left or right part of the array for elements smaller or greater than k. In each step searched area decreases by 2 and locates, in time O(log n), the wanted element or ...
... Single thread checks key in the middle of searched array continuing search in left or right part of the array for elements smaller or greater than k. In each step searched area decreases by 2 and locates, in time O(log n), the wanted element or ...
pptx
... • Bag in which data items are Comparable • Smaller elements (determined by compareTo()) have higher priority • remove() return the element with the highest priority = least element in the compareTo() ordering ...
... • Bag in which data items are Comparable • Smaller elements (determined by compareTo()) have higher priority • remove() return the element with the highest priority = least element in the compareTo() ordering ...
Suffix Trees and their Applications
... If is a leaf it is also a suffix of . Then it must also be a non nested suffix, since if it . The node can were nested, it would appear somewhere else in : then not be a leaf. If is a branching node then there must exist at least two outgoing edges from with different labels. This means that there m ...
... If is a leaf it is also a suffix of . Then it must also be a non nested suffix, since if it . The node can were nested, it would appear somewhere else in : then not be a leaf. If is a branching node then there must exist at least two outgoing edges from with different labels. This means that there m ...
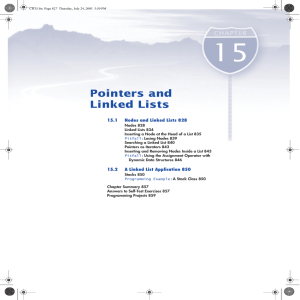
Pointers and Linked Lists
... "Sally" and the number 18. What code would you add in order to set the value of the member variable next of this node equal to NULL? 3 Suppose that your program contains the type definitions and code given in Self-Test Exercise 1. Assuming that the value of the pointer variable head has not been cha ...
... "Sally" and the number 18. What code would you add in order to set the value of the member variable next of this node equal to NULL? 3 Suppose that your program contains the type definitions and code given in Self-Test Exercise 1. Assuming that the value of the pointer variable head has not been cha ...
Burst Tries - Department of Computer Science
... character that alphabetically precedes (respectively, follows) c. y Thus a set of TST nodes connected by left and right pointers are a representation of a trie node. These can be rebalanced on access. y The central pointer is for strings starting with c, thus corresponding to the h `c' ` pointer off ...
... character that alphabetically precedes (respectively, follows) c. y Thus a set of TST nodes connected by left and right pointers are a representation of a trie node. These can be rebalanced on access. y The central pointer is for strings starting with c, thus corresponding to the h `c' ` pointer off ...
Concurrent Data Structures (Book Chapter).
... In many data structures, the undesirable effects of memory contention and sequential bottlenecks discussed above can be reduced by using a fine-grained locking scheme. In finegrained locking, we use multiple locks of small granularity to protect different parts of the data structure. The goal is to ...
... In many data structures, the undesirable effects of memory contention and sequential bottlenecks discussed above can be reduced by using a fine-grained locking scheme. In finegrained locking, we use multiple locks of small granularity to protect different parts of the data structure. The goal is to ...
Quadtree
A quadtree is a tree data structure in which each internal node has exactly four children. Quadtrees are most often used to partition a two-dimensional space by recursively subdividing it into four quadrants or regions. The regions may be square or rectangular, or may have arbitrary shapes. This data structure was named a quadtree by Raphael Finkel and J.L. Bentley in 1974. A similar partitioning is also known as a Q-tree. All forms of quadtrees share some common features: They decompose space into adaptable cells Each cell (or bucket) has a maximum capacity. When maximum capacity is reached, the bucket splits The tree directory follows the spatial decomposition of the quadtree.