Environment Optimization Guide
... idle resources to ensure nothing is negatively impacted. Most current SAN and NAS devices include technologies to avoid or limit fragmentation on the block level. Windows sees the data logically from the software level, outside of the storage realm. If Windows detects a file in hundreds of pieces, S ...
... idle resources to ensure nothing is negatively impacted. Most current SAN and NAS devices include technologies to avoid or limit fragmentation on the block level. Windows sees the data logically from the software level, outside of the storage realm. If Windows detects a file in hundreds of pieces, S ...
SQL - Structured Query Language
... When designing and implementing a database, keep in mind these four guidelines. Atomicity Your coded statements flow without the constant need to update or "fix" your data. Consistency Your statements are either executed 100% or fail 100%, do not implement code that partially works. Isolation Keep d ...
... When designing and implementing a database, keep in mind these four guidelines. Atomicity Your coded statements flow without the constant need to update or "fix" your data. Consistency Your statements are either executed 100% or fail 100%, do not implement code that partially works. Isolation Keep d ...
Upgrading from SQL Server 2005 Express Edition to Workgroup or
... needs grow, other editions of SQL Server 2005 will provide more capabilities and scalability. As your business applications grow in sophistication, require more data storage, require more simultaneous users, or need higher availability, consider upgrading the edition of SQL Server 2005 that your org ...
... needs grow, other editions of SQL Server 2005 will provide more capabilities and scalability. As your business applications grow in sophistication, require more data storage, require more simultaneous users, or need higher availability, consider upgrading the edition of SQL Server 2005 that your org ...
PDF - Microsoft Docs
... grew and more computer hardware and software became available, companies started to acquire different DBMSs. The reasons were many: People bought what was cheapest, what was fastest, what they already knew, what was latest on the market, what worked best for a single application. Other reasons were ...
... grew and more computer hardware and software became available, companies started to acquire different DBMSs. The reasons were many: People bought what was cheapest, what was fastest, what they already knew, what was latest on the market, what worked best for a single application. Other reasons were ...
SQL Injection
... 1. Check if the web application connects to a database server to access some data. 2. List all input fields, hidden fields, and post requests whose values can be used to craft a SQL query. 3. Try to inject codes into the input fields to produce an error. 4. Attempt to insert a string value where a n ...
... 1. Check if the web application connects to a database server to access some data. 2. List all input fields, hidden fields, and post requests whose values can be used to craft a SQL query. 3. Try to inject codes into the input fields to produce an error. 4. Attempt to insert a string value where a n ...
EMC EXTREME PERFORMANCE AND EFFICIENCY FOR MICROSOFT SQL SERVER
... Working together, Microsoft and EMC supply the critical components to deliver highperformance, enterprise-class availability solutions for SQL Server environments. With EMC® XtremIO™, EMC provides you with a storage solution that is optimized for extreme online transactional processing (OLTP) databa ...
... Working together, Microsoft and EMC supply the critical components to deliver highperformance, enterprise-class availability solutions for SQL Server environments. With EMC® XtremIO™, EMC provides you with a storage solution that is optimized for extreme online transactional processing (OLTP) databa ...
Chapter 17: Parallel Databases
... covers distributed database systems, revisiting the issues of database design, transaction management, and query evaluation and optimization, in the context of distributed databases. The chapter also covers issues of system availability during failures and describes the LDAP directory system. ...
... covers distributed database systems, revisiting the issues of database design, transaction management, and query evaluation and optimization, in the context of distributed databases. The chapter also covers issues of system availability during failures and describes the LDAP directory system. ...
DBA Guide to Databases on VMware
... platform addresses many difficult design problems such as scalability, high availability, and resource isolation that traditionally exist in the physical environment. With VMware features and tools, you can design database solutions that scale on demand to meet any throughput or organizational growt ...
... platform addresses many difficult design problems such as scalability, high availability, and resource isolation that traditionally exist in the physical environment. With VMware features and tools, you can design database solutions that scale on demand to meet any throughput or organizational growt ...
Using AlwaysOn Availability Groups for High Availability and
... Step 3: Prepare DQS for Availability Group Configuration 1. Enable AlwaysOn Availability Group for all the SQL Server instances on all the three nodes. For more information, see Enable and Disable AlwaysOn Availability Groups. 2. On the second and third nodes, connect to SQL Server instance using S ...
... Step 3: Prepare DQS for Availability Group Configuration 1. Enable AlwaysOn Availability Group for all the SQL Server instances on all the three nodes. For more information, see Enable and Disable AlwaysOn Availability Groups. 2. On the second and third nodes, connect to SQL Server instance using S ...
Oracle Exadata Database Machine X5
... Configurations, the system can be custom configured to meet any business use case. In addition to upgrading within a rack, multiple racks can be connected using the integrated InfiniBand fabric to form even larger configurations. For example, a system composed of four Full Racks is simply four times ...
... Configurations, the system can be custom configured to meet any business use case. In addition to upgrading within a rack, multiple racks can be connected using the integrated InfiniBand fabric to form even larger configurations. For example, a system composed of four Full Racks is simply four times ...
Advanced SQL - Computer Engineering Department
... Procedures and functions can be invoked also from dynamic SQL SQL:1999 allows more than one function/procedure of the same name (called name overloading), as long as the number of arguments differ, or at least the types of the arguments differ Database System Concepts - 6th Edition ...
... Procedures and functions can be invoked also from dynamic SQL SQL:1999 allows more than one function/procedure of the same name (called name overloading), as long as the number of arguments differ, or at least the types of the arguments differ Database System Concepts - 6th Edition ...
SQL Statements
... 2000. This machine runs either a PI3 Server Node or the PI-API Node and can connect to any PI Node in the network. The PI Interface makes internal use of the PI-API-NT in order to keep a standard way of interfacing from a client node to the PI Server Node. This version of the Interface only supports ...
... 2000. This machine runs either a PI3 Server Node or the PI-API Node and can connect to any PI Node in the network. The PI Interface makes internal use of the PI-API-NT in order to keep a standard way of interfacing from a client node to the PI Server Node. This version of the Interface only supports ...
EMC INFRASTRUCTURE FOR HIGH PERFORMANCE MICROSOFT AND ORACLE DATABASE SYSTEMS
... This white paper describes the design, testing, and validation of an enterprise VMware infrastructure using the Symmetrix VMAX 40K storage platform with Enginuity 5876, XtremSF, and XtremCache as its foundation. This solution demonstrates how XtremSF and XtremCache complement FAST VP in providing pe ...
... This white paper describes the design, testing, and validation of an enterprise VMware infrastructure using the Symmetrix VMAX 40K storage platform with Enginuity 5876, XtremSF, and XtremCache as its foundation. This solution demonstrates how XtremSF and XtremCache complement FAST VP in providing pe ...
EMC AVAILABILITY FOR EXTREME PERFORMANCE OF MICROSOFT SQL SERVER
... driven to deliver responsive, continuously available applications that provide customers with an uninterrupted user experience. There are also higher demands on IT infrastructure performance and data availability. This environment is typically driven by: ...
... driven to deliver responsive, continuously available applications that provide customers with an uninterrupted user experience. There are also higher demands on IT infrastructure performance and data availability. This environment is typically driven by: ...
DTS
... The internal architecture of SSIS is completely different from DTS. The data flow engine is completely segregated from the control flow engine or SSIS Runtime Engine and hence the performance is improved significantly in SSIS. SSIS is now no longer a stand-alone designer. SSIS uses the new devel ...
... The internal architecture of SSIS is completely different from DTS. The data flow engine is completely segregated from the control flow engine or SSIS Runtime Engine and hence the performance is improved significantly in SSIS. SSIS is now no longer a stand-alone designer. SSIS uses the new devel ...
Environment Optimization Guide
... If you don't virtualize the Relativity roles, there will likely be a mirrored array housing the OS and required Relativity components (unless you’re also booting from the storage device). If these disks are heavily fragmented, roles including the web servers (IIS) may experience poor performance. Th ...
... If you don't virtualize the Relativity roles, there will likely be a mirrored array housing the OS and required Relativity components (unless you’re also booting from the storage device). If these disks are heavily fragmented, roles including the web servers (IIS) may experience poor performance. Th ...
Answers to Chapters 7, 9 and 10
... This SQL sequence represents a distributed request. In this case, the PRODUCT table is partitioned between two DP sites, A and B. Although the request accesses only one remote DP site, it accesses a table that is partitioned into two fragments: PROD-A and PROD-B. A single request can access a partit ...
... This SQL sequence represents a distributed request. In this case, the PRODUCT table is partitioned between two DP sites, A and B. Although the request accesses only one remote DP site, it accesses a table that is partitioned into two fragments: PROD-A and PROD-B. A single request can access a partit ...
5. Advanced SQL
... error = SQLExecDirect(stmt, sqlquery, SQL NTS); if (error == SQL SUCCESS) { SQLBindCol(stmt, 1, SQL C CHAR, deptname , 80, &lenOut1); SQLBindCol(stmt, 2, SQL C FLOAT, &salary, 0 , &lenOut2); while (SQLFetch(stmt) == SQL SUCCESS) { printf (" %s %g\n", deptname, salary); ...
... error = SQLExecDirect(stmt, sqlquery, SQL NTS); if (error == SQL SUCCESS) { SQLBindCol(stmt, 1, SQL C CHAR, deptname , 80, &lenOut1); SQLBindCol(stmt, 2, SQL C FLOAT, &salary, 0 , &lenOut2); while (SQLFetch(stmt) == SQL SUCCESS) { printf (" %s %g\n", deptname, salary); ...
Manual - Animated DataBase Courseware
... Figure I.1.3 shows the One-to-many Binary Non Identifying Relationship in the three other notations. The IDEF1X notation is a notation commonly found in case tools. The IDEF1X notation uses the dashed line to distinguish the one-to-many non-identifying relationship from the one-to-many idenfying re ...
... Figure I.1.3 shows the One-to-many Binary Non Identifying Relationship in the three other notations. The IDEF1X notation is a notation commonly found in case tools. The IDEF1X notation uses the dashed line to distinguish the one-to-many non-identifying relationship from the one-to-many idenfying re ...
Shared Pool Monitoring
... primary role for caching of cursors shared between sessions connected to the database. At the most fundamental level, the shared pool is a metadata cache. While the buffer cache is used for the caching of disk data blocks, the shared pool is used for caching complex objects describing where the data ...
... primary role for caching of cursors shared between sessions connected to the database. At the most fundamental level, the shared pool is a metadata cache. While the buffer cache is used for the caching of disk data blocks, the shared pool is used for caching complex objects describing where the data ...
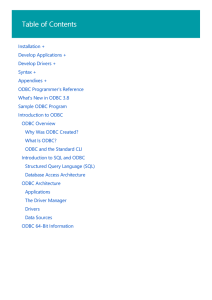
Chapter 1: Introduction
... communicates with the server to carry out the requested action, and fetch results. ODBC program first allocates an SQL environment, then a database connection ...
... communicates with the server to carry out the requested action, and fetch results. ODBC program first allocates an SQL environment, then a database connection ...
Managing SQL Server Express with SQL Server
... Server Express instances installed, server groups allow you to work across servers in an efficient manner. For example, Figure 2 shows a folder called Express Servers. In that folder are two servers. ...
... Server Express instances installed, server groups allow you to work across servers in an efficient manner. For example, Figure 2 shows a folder called Express Servers. In that folder are two servers. ...
Preference SQL - Institut für Informatik
... context of cooperative database systems [Mot88, CYC96, Min98]. There the technique of query relaxation has been studied in order to deal with the empty result problem. Other approaches aiming to provide soft constraints are based on fuzzy logic or case-based reasoning. None of these attempts does su ...
... context of cooperative database systems [Mot88, CYC96, Min98]. There the technique of query relaxation has been studied in order to deal with the empty result problem. Other approaches aiming to provide soft constraints are based on fuzzy logic or case-based reasoning. None of these attempts does su ...
Database Engines on Multicores, Why Parallelize When You Can
... widely applicable for many workloads. 1.1 Background and Trends Most commercial relational database engines are based on a decades old design optimized for disk I/O bottlenecks and meant to run on single CPU computers. Concurrency is achieved through threads and/or processes with few of them actuall ...
... widely applicable for many workloads. 1.1 Background and Trends Most commercial relational database engines are based on a decades old design optimized for disk I/O bottlenecks and meant to run on single CPU computers. Concurrency is achieved through threads and/or processes with few of them actuall ...
Managing SQL Server Express with SQL Server 2005
... Server Express instances installed, server groups allow you to work across servers in an efficient manner. For example, Figure 2 shows a folder called Express Servers. In that folder are two servers. ...
... Server Express instances installed, server groups allow you to work across servers in an efficient manner. For example, Figure 2 shows a folder called Express Servers. In that folder are two servers. ...
Tandem Computers

Tandem Computers, Inc. was the dominant manufacturer of fault-tolerant computer systems for ATM networks, banks, stock exchanges, telephone switching centers, and other similar commercial transaction processing applications requiring maximum uptime and zero data loss. The company was founded in 1974 and remained independent until 1997. It is now a server division within Hewlett Packard.Tandem's NonStop systems use a number of independent identical processors and redundant storage devices and controllers to provide automatic high-speed ""failover"" in the case of a hardware or software failure. To contain the scope of failures and of corrupted data, these multi-computer systems have no shared central components, not even main memory. Conventional multi-computer systems all use shared memories and work directly on shared data objects. Instead, NonStop processors cooperate by exchanging messages across a reliable fabric, and software takes periodic snapshots for possible rollback of program memory state.Besides handling failures well, this ""shared-nothing"" messaging system design also scales extremely well to the largest commercial workloads. Each doubling of the total number of processors would double system throughput, up to the maximum configuration of 4000 processors. In contrast, the performance of conventional multiprocessor systems is limited by the speed of some shared memory, bus, or switch. Adding more than 4–8 processors that way gives no further system speedup. NonStop systems have more often been bought to meet scaling requirements than for extreme fault tolerance. They compete well against IBM's largest mainframes, despite being built from simpler minicomputer technology.