SAP R/3`s ability to support a number of different databases
... © 1998 Technical Enterprises, Inc. Reproduction of this document without permission is prohibited. ...
... © 1998 Technical Enterprises, Inc. Reproduction of this document without permission is prohibited. ...
Oracle Database System
... run (or /): execute the statement in the current buffer save : save current sql stmt to a file
get : load sql statements into buffer
spool : send output from sql stmt to a file
start : load script file with sql stmts and run
them
• help
• quit
...
... run (or /): execute the statement in the current buffer save
Module 1: Getting Started with Databases and Transact
... Enable fast retrieval, built from one or more columns in table or view ...
... Enable fast retrieval, built from one or more columns in table or view ...
Getting Started with Databases and Transact
... Enable fast retrieval, built from one or more columns in table or view ...
... Enable fast retrieval, built from one or more columns in table or view ...
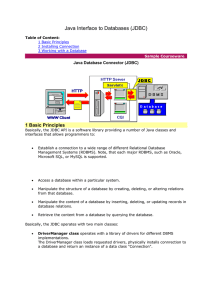
Java Interface to Databases (JDBC)
... catch(SQLException exc){exc.printStackTrace();} ... Similarly, to retrieve data from a database we need to obtain an instance of the Statment class, and then to invoke executeQuery() method on this instance. This method takes a string containing SQL source as an argument. ...
... catch(SQLException exc){exc.printStackTrace();} ... Similarly, to retrieve data from a database we need to obtain an instance of the Statment class, and then to invoke executeQuery() method on this instance. This method takes a string containing SQL source as an argument. ...
Microsoft SQL Server 2005 certification and course
... Course code: M2786 – 2 days Course code: M2787 – 2 days ...
... Course code: M2786 – 2 days Course code: M2787 – 2 days ...
Idaho1 - University of Tulsa
... Placing very severe restrictions on intermixing of types Variety of definitions for it ...
... Placing very severe restrictions on intermixing of types Variety of definitions for it ...
KorthDB6_ch17 - Internet Database Lab.
... Parallel Database Architectures Shared memory -- processors share a common memory Shared disk -- processors share a common disk, sometimes called clusters Shared nothing -- processors share neither a common memory nor common disk Hierarchical -- hybrid of the above architectures ...
... Parallel Database Architectures Shared memory -- processors share a common memory Shared disk -- processors share a common disk, sometimes called clusters Shared nothing -- processors share neither a common memory nor common disk Hierarchical -- hybrid of the above architectures ...
SQL Injection Attacks
... Access control and security within the database system itself, including the users and databases granted with access to the databases, views and stored programs in use within the database. For more information, see Section 6.2, “The MySQL Access Privilege System”, and Section 6.3, “MySQL User Accoun ...
... Access control and security within the database system itself, including the users and databases granted with access to the databases, views and stored programs in use within the database. For more information, see Section 6.2, “The MySQL Access Privilege System”, and Section 6.3, “MySQL User Accoun ...
SQL Server Management Studio (SSMS)
... retrieve selected data. The first step in creating a database is creating a plan that serves both as a guide to be used when implementing the database and as a functional specification for the database after it has been implemented. The complexity and detail of a database design is dictated by the ...
... retrieve selected data. The first step in creating a database is creating a plan that serves both as a guide to be used when implementing the database and as a functional specification for the database after it has been implemented. The complexity and detail of a database design is dictated by the ...
Fuzzy Structured Query Language (FSQL) for Relational Database
... Abstract A fuzzy query language, called FSQL, in the relational databases is introduced in this paper. In general, database systems have query systems which are able to retrieve and manipulate precise data. However, such queries are hard to operate on the real world applications since their queries ...
... Abstract A fuzzy query language, called FSQL, in the relational databases is introduced in this paper. In general, database systems have query systems which are able to retrieve and manipulate precise data. However, such queries are hard to operate on the real world applications since their queries ...
A Case for Staged Database Systems
... instructions of the previous module, to replace them with its own ones. The performance loss in this example is due to (a) a large number of worker threads: since no I/O takes place, one worker thread would be sufficient, (b) preemptive thread scheduling: optimization and parsing of a single query i ...
... instructions of the previous module, to replace them with its own ones. The performance loss in this example is due to (a) a large number of worker threads: since no I/O takes place, one worker thread would be sufficient, (b) preemptive thread scheduling: optimization and parsing of a single query i ...
Learning Fingerprints for a Database Intrusion Detection System
... overruled because of oversummarised fingerprints, but also illegitimate fingerprints are included to the signature database. ...
... overruled because of oversummarised fingerprints, but also illegitimate fingerprints are included to the signature database. ...
Lab7 - Computer Science & Information Systems. BITS, Pilani
... Database Systems Lab No #7 Today's Topics: Transactions PL/SQL ...
... Database Systems Lab No #7 Today's Topics: Transactions PL/SQL ...
sql server dba ****** (mar 2016 – present) – chester
... components and architectural patterns, product roadmaps, new product evaluation and new product service introduction) Capturing of business requirements through collaboration with key stakeholders (internal and external) Production of high-level Solution Designs based on Architectural principles ...
... components and architectural patterns, product roadmaps, new product evaluation and new product service introduction) Capturing of business requirements through collaboration with key stakeholders (internal and external) Production of high-level Solution Designs based on Architectural principles ...
Securing SQL Server 2005
... – Logical collection of related database objects – Part of full object name: • Server.Database.Schema.Object ...
... – Logical collection of related database objects – Part of full object name: • Server.Database.Schema.Object ...
Database performance tuning
... different version of the original SQL code which is fully equivalent and more efficient Query optimizer: Analyzes SQL query and finds most efficient way to access data Access plans: DBMS-specific and translate client’s SQL query into a series of complex I/O operations ...
... different version of the original SQL code which is fully equivalent and more efficient Query optimizer: Analyzes SQL query and finds most efficient way to access data Access plans: DBMS-specific and translate client’s SQL query into a series of complex I/O operations ...
Become a SQL Server DBA - Madeira | Data Solutions
... This course teaches the DBA (Database Administrator) profession based on Microsoft SQL Server. It covers all aspects of DBA work and all the components and features in SQL Server. The course begins with relational database basics, and goes through all the development as well as administration aspect ...
... This course teaches the DBA (Database Administrator) profession based on Microsoft SQL Server. It covers all aspects of DBA work and all the components and features in SQL Server. The course begins with relational database basics, and goes through all the development as well as administration aspect ...
Connect To an SSL-Enabled Microsoft SQL Server
... Use the instructions in the PDF provided by Informatica Global Customer Support to install the software. After the installation completes, the new Windows services SLAgent60 and SLSocket60 are visible. 5. Stop the SLAgent60 and SLSocket60 services. 6. Right-click the SLAgent60 service and set up the ...
... Use the instructions in the PDF provided by Informatica Global Customer Support to install the software. After the installation completes, the new Windows services SLAgent60 and SLSocket60 are visible. 5. Stop the SLAgent60 and SLSocket60 services. 6. Right-click the SLAgent60 service and set up the ...
Navitaire-SQL2005 - Platform Modernization Alliance
... during times of peak demand,” says Mike Padgen, Principal Architect, at Navitaire. “We needed more processing power and the ability to scale as quickly as possible to meet the needs of our fast growing customers.” The move to SQL Server 2005 and Windows Server 2003 running on 64-bit hardware gave th ...
... during times of peak demand,” says Mike Padgen, Principal Architect, at Navitaire. “We needed more processing power and the ability to scale as quickly as possible to meet the needs of our fast growing customers.” The move to SQL Server 2005 and Windows Server 2003 running on 64-bit hardware gave th ...
Alava Consulting TANYA D. BRIDGES
... Support for the Oracle 9i documentation system known as Documentum Creating security accounts for use in the Documentum system Setting up security for the groups defined within Documentum Managing performance issues Daily monitoring of the database Creation of databases and their applications for di ...
... Support for the Oracle 9i documentation system known as Documentum Creating security accounts for use in the Documentum system Setting up security for the groups defined within Documentum Managing performance issues Daily monitoring of the database Creation of databases and their applications for di ...
ids_opensource_jleffler
... • Intended as an alternative to ‘isql’. • Before DB-Access was created. • Designed for use in shell scripts. • Exits with non-zero status on error. • Careful use of standard input, output, error. • Output layout independent of selected data. ...
... • Intended as an alternative to ‘isql’. • Before DB-Access was created. • Designed for use in shell scripts. • Exits with non-zero status on error. • Careful use of standard input, output, error. • Output layout independent of selected data. ...
Title of Presentation
... This is an online operation and doesn’t use a lot of resources. You must update statistics afterwards, as this is not automatically done for you. Ideally, you should only rebuild or reorganize indexes that need rebuilding, especially for very large databases. Use sys.dm_db_index_physical_stats to id ...
... This is an online operation and doesn’t use a lot of resources. You must update statistics afterwards, as this is not automatically done for you. Ideally, you should only rebuild or reorganize indexes that need rebuilding, especially for very large databases. Use sys.dm_db_index_physical_stats to id ...
Tandem Computers

Tandem Computers, Inc. was the dominant manufacturer of fault-tolerant computer systems for ATM networks, banks, stock exchanges, telephone switching centers, and other similar commercial transaction processing applications requiring maximum uptime and zero data loss. The company was founded in 1974 and remained independent until 1997. It is now a server division within Hewlett Packard.Tandem's NonStop systems use a number of independent identical processors and redundant storage devices and controllers to provide automatic high-speed ""failover"" in the case of a hardware or software failure. To contain the scope of failures and of corrupted data, these multi-computer systems have no shared central components, not even main memory. Conventional multi-computer systems all use shared memories and work directly on shared data objects. Instead, NonStop processors cooperate by exchanging messages across a reliable fabric, and software takes periodic snapshots for possible rollback of program memory state.Besides handling failures well, this ""shared-nothing"" messaging system design also scales extremely well to the largest commercial workloads. Each doubling of the total number of processors would double system throughput, up to the maximum configuration of 4000 processors. In contrast, the performance of conventional multiprocessor systems is limited by the speed of some shared memory, bus, or switch. Adding more than 4–8 processors that way gives no further system speedup. NonStop systems have more often been bought to meet scaling requirements than for extreme fault tolerance. They compete well against IBM's largest mainframes, despite being built from simpler minicomputer technology.