SQL
... login_name='trinity'-We will probably get a "Page Not Found" error. The reason being, the password "31173" will be converted into a number, before UNION with an integer (10 in this case). Since it is a valid UNION statement, SQL server will not throw ODBC error message, and thus, we will not be able ...
... login_name='trinity'-We will probably get a "Page Not Found" error. The reason being, the password "31173" will be converted into a number, before UNION with an integer (10 in this case). Since it is a valid UNION statement, SQL server will not throw ODBC error message, and thus, we will not be able ...
High Availability for Windows SharePoint Services Using Double-Take
... permissions and attributes) written to NTFS, FAT or FAT32 file systems by any application or process, subject to specific exceptions called out in the User’s Guide or readme.txt file. Maintaining point-in-time consistent file system replicas and providing server monitoring and automatic or manual fa ...
... permissions and attributes) written to NTFS, FAT or FAT32 file systems by any application or process, subject to specific exceptions called out in the User’s Guide or readme.txt file. Maintaining point-in-time consistent file system replicas and providing server monitoring and automatic or manual fa ...
SQL
... login_name='trinity'-We will probably get a "Page Not Found" error. The reason being, the password "31173" will be converted into a number, before UNION with an integer (10 in this case). Since it is a valid UNION statement, SQL server will not throw ODBC error message, and thus, we will not be able ...
... login_name='trinity'-We will probably get a "Page Not Found" error. The reason being, the password "31173" will be converted into a number, before UNION with an integer (10 in this case). Since it is a valid UNION statement, SQL server will not throw ODBC error message, and thus, we will not be able ...
SQL Server 2005 New Features & Courses - e
... Every Feature, especially the Scalability and Recovery Features, like Database Snapshots, Database Mirroring, and Failover Clustering 32 bit and 64 bit ...
... Every Feature, especially the Scalability and Recovery Features, like Database Snapshots, Database Mirroring, and Failover Clustering 32 bit and 64 bit ...
SQLrand: Preventing SQL Injection Attacks
... expected the suffix of integers applied to all keywords. As a “middle man,” it had to conceal its identity by masquerading as the database to the client and vice versa. Although our implementation focused on CGI scripts as the query generators, a similar approach applies when using JDBC. The random ...
... expected the suffix of integers applied to all keywords. As a “middle man,” it had to conceal its identity by masquerading as the database to the client and vice versa. Although our implementation focused on CGI scripts as the query generators, a similar approach applies when using JDBC. The random ...
Change Management for SQL Server
... • Edgewood Solutions (www.edgewoodsolutions.com) – Customer focused SQL Server solutions ...
... • Edgewood Solutions (www.edgewoodsolutions.com) – Customer focused SQL Server solutions ...
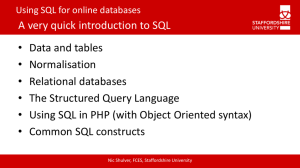
table - Staffordshire University
... Tables may be joined together – this is very powerful but can get complex Database systems which allow join relationships are known as Relational Databases (see RDSD) To build, use and maintain joins between tables, it is often easiest to use tools built into database programs (e.g. MS Access, ...
... Tables may be joined together – this is very powerful but can get complex Database systems which allow join relationships are known as Relational Databases (see RDSD) To build, use and maintain joins between tables, it is often easiest to use tools built into database programs (e.g. MS Access, ...
Pass4sure 70
... D: An Access database doesn't have a Windows NT account. An Access database could have a username and a password. QUESTION 5 You want to configure SQL Server to notify you by e-mail when an alert occurs. Which series of steps must you perform? A. Configure the SQL Server Agent service to log on as t ...
... D: An Access database doesn't have a Windows NT account. An Access database could have a username and a password. QUESTION 5 You want to configure SQL Server to notify you by e-mail when an alert occurs. Which series of steps must you perform? A. Configure the SQL Server Agent service to log on as t ...
database - Dl4a.org
... Resist putting software products on the db server machine so that their maintenance does not inhibit the running of the database. Further, if the product breaks, it could inhibit access to the database for a long period. Example, a logging application, monitoring users on the db goes wild, fills all ...
... Resist putting software products on the db server machine so that their maintenance does not inhibit the running of the database. Further, if the product breaks, it could inhibit access to the database for a long period. Example, a logging application, monitoring users on the db goes wild, fills all ...
SQL Object Level Recovery Native 1.1
... SQL Object Level Recovery Pro is included with SQL Backup Pro (http://www.redgate.com/products/SQL_Backup/index.htm), and enables you to recover objects from SQL Backup (.sqb) files. SQL Object Level Recovery Pro requires a SQL Backup Pro license on the server you are restoring objects to. For more ...
... SQL Object Level Recovery Pro is included with SQL Backup Pro (http://www.redgate.com/products/SQL_Backup/index.htm), and enables you to recover objects from SQL Backup (.sqb) files. SQL Object Level Recovery Pro requires a SQL Backup Pro license on the server you are restoring objects to. For more ...
SQL Server Performance Tuning and Optimization
... Qualify database objects (object name resolution does take time) ...
... Qualify database objects (object name resolution does take time) ...
Overview Of Database and Java
... flexible: can change one part without affecting others can connect to different databases without changing code specialization: presentation / business logic / data management can cache queries can implement proxies and firewalls ...
... flexible: can change one part without affecting others can connect to different databases without changing code specialization: presentation / business logic / data management can cache queries can implement proxies and firewalls ...
Slide Deck
... They don’t retain data when you remove power X They’re not very quick at write operations X They’re difficult to configure X You need special hardware X They run hot X They’re expensive X ...
... They don’t retain data when you remove power X They’re not very quick at write operations X They’re difficult to configure X You need special hardware X They run hot X They’re expensive X ...
Integration and Virtualization of Relational SQL and NoSQL Systems
... NoSQL (“Not Only SQL”) systems have been released and widely adopted in many domains. NoSQL systems have been developed to support applications not well served by relational systems, often involving Big Data processing. NoSQL systems can be categorized as key-value stores, document stores, and graph ...
... NoSQL (“Not Only SQL”) systems have been released and widely adopted in many domains. NoSQL systems have been developed to support applications not well served by relational systems, often involving Big Data processing. NoSQL systems can be categorized as key-value stores, document stores, and graph ...
Retrieving Data from a Database
... This statement returns all record rows from the join of the Customers and Orders tables. However, if you want to count the number of OrderIDs assigned to a customer, you must use a so-called aggregate function. In Listing 14.2, the script is using the COUNT function, which counts the number of all O ...
... This statement returns all record rows from the join of the Customers and Orders tables. However, if you want to count the number of OrderIDs assigned to a customer, you must use a so-called aggregate function. In Listing 14.2, the script is using the COUNT function, which counts the number of all O ...
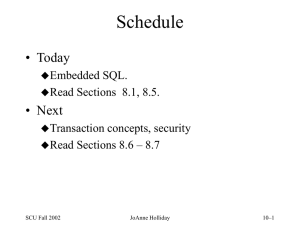
Chapter 8 - Advanced SQL
... • Subquery that executes once for each row in the outer query • Correlated because inner query is related to the outer query – Inner query references column of outer subquery – Works like a nested loop for x=1 to 2 for y=1 to 3 ...
... • Subquery that executes once for each row in the outer query • Correlated because inner query is related to the outer query – Inner query references column of outer subquery – Works like a nested loop for x=1 to 2 for y=1 to 3 ...
SQL - La Salle University
... Advantage – can be used to encapsulate an entire business transaction – group statements together as a transaction and don’t let them be separated Advantage – code resides at the DB and is executed at the DB – less communication – faster processing Advantage – reduce redundant code – since cod ...
... Advantage – can be used to encapsulate an entire business transaction – group statements together as a transaction and don’t let them be separated Advantage – code resides at the DB and is executed at the DB – less communication – faster processing Advantage – reduce redundant code – since cod ...
This resume has been forwarded to you at the request of Monster
... Optimized by tweaking certain important parameters in the postgresql.conf file such as sort_mem, random_page_cost, shared buffers etc. · Worked with daily backup and restore monitor and maintenance for Unix and Windows instance of PostgreSQL · Worked with Performed database migration from MS SQL s ...
... Optimized by tweaking certain important parameters in the postgresql.conf file such as sort_mem, random_page_cost, shared buffers etc. · Worked with daily backup and restore monitor and maintenance for Unix and Windows instance of PostgreSQL · Worked with Performed database migration from MS SQL s ...
Oracle Database 10g Performance Overview
... Materialized views are schema objects that can be used to summarize, pre-compute, replicate, and distribute data. They are suitable in many computing environments, such as data warehousing, decision support, and distributed or mobile computing. In a data warehousing application, for example, users o ...
... Materialized views are schema objects that can be used to summarize, pre-compute, replicate, and distribute data. They are suitable in many computing environments, such as data warehousing, decision support, and distributed or mobile computing. In a data warehousing application, for example, users o ...
File
... status for a list of docIDs passed. Time is essential • Shell script meant to be interactive (input/invoke CLP/SQL/Commit) • Programming language, such as C, may allow streamline the logic, reuse the stmts, more cursor ...
... status for a list of docIDs passed. Time is essential • Shell script meant to be interactive (input/invoke CLP/SQL/Commit) • Programming language, such as C, may allow streamline the logic, reuse the stmts, more cursor ...
Chapter 4: Advanced SQL - United International College
... Forms of authorization to modify the database schema (covered in Chapter 8): Index - allows creation and deletion of indices. Resources - allows creation of new relations. Alteration - allows addition or deletion of attributes in a relation. ...
... Forms of authorization to modify the database schema (covered in Chapter 8): Index - allows creation and deletion of indices. Resources - allows creation of new relations. Alteration - allows addition or deletion of attributes in a relation. ...
Tandem Computers

Tandem Computers, Inc. was the dominant manufacturer of fault-tolerant computer systems for ATM networks, banks, stock exchanges, telephone switching centers, and other similar commercial transaction processing applications requiring maximum uptime and zero data loss. The company was founded in 1974 and remained independent until 1997. It is now a server division within Hewlett Packard.Tandem's NonStop systems use a number of independent identical processors and redundant storage devices and controllers to provide automatic high-speed ""failover"" in the case of a hardware or software failure. To contain the scope of failures and of corrupted data, these multi-computer systems have no shared central components, not even main memory. Conventional multi-computer systems all use shared memories and work directly on shared data objects. Instead, NonStop processors cooperate by exchanging messages across a reliable fabric, and software takes periodic snapshots for possible rollback of program memory state.Besides handling failures well, this ""shared-nothing"" messaging system design also scales extremely well to the largest commercial workloads. Each doubling of the total number of processors would double system throughput, up to the maximum configuration of 4000 processors. In contrast, the performance of conventional multiprocessor systems is limited by the speed of some shared memory, bus, or switch. Adding more than 4–8 processors that way gives no further system speedup. NonStop systems have more often been bought to meet scaling requirements than for extreme fault tolerance. They compete well against IBM's largest mainframes, despite being built from simpler minicomputer technology.