ORACLE: PL/SQL
... For a client application, the location and platform of the databases are transparent. ...
... For a client application, the location and platform of the databases are transparent. ...
The Definitive Guide to SQLite
... (RDBMS) on board. The program would just do its job and manage its data somehow, making no fanfare about how it went about doing so. But inside, there is a complete, self-contained database engine at work. One advantage of having a database server inside your program is that no network configuration ...
... (RDBMS) on board. The program would just do its job and manage its data somehow, making no fanfare about how it went about doing so. But inside, there is a complete, self-contained database engine at work. One advantage of having a database server inside your program is that no network configuration ...
SAP HANA SPS 09 - What`s New? SAP HANA Multitenant Database
... Prerequisites: User in the system database with DATABASE ADMIN privilege; tenant database running 1. In the Systems view in SAP HANA studio, expand the system database and double-click on Backup 2. Open the Backup Catalog tab and select the database for which you want to view the information ...
... Prerequisites: User in the system database with DATABASE ADMIN privilege; tenant database running 1. In the Systems view in SAP HANA studio, expand the system database and double-click on Backup 2. Open the Backup Catalog tab and select the database for which you want to view the information ...
SQL Tutrial
... Note the distinction made between SQL*Plus Commands and SQL Statements. SQL*Plus commands are proprietary to the Oracle SQL*Plus tool. SQL is a standard language that can be used is just about any Relational Database Management System (RDBMS). ...
... Note the distinction made between SQL*Plus Commands and SQL Statements. SQL*Plus commands are proprietary to the Oracle SQL*Plus tool. SQL is a standard language that can be used is just about any Relational Database Management System (RDBMS). ...
Chapter 1 INTRODUCTION.
... and seminars. IBM, which already had a large share of the commercial database market with hierarchical and network model DBMSs, realised quite quickly that the relational model would figure prominently in future database products. The project at IBM's San Jose labs was started in 1974 and was named ...
... and seminars. IBM, which already had a large share of the commercial database market with hierarchical and network model DBMSs, realised quite quickly that the relational model would figure prominently in future database products. The project at IBM's San Jose labs was started in 1974 and was named ...
sql – structured query language
... keys are called candidate keys. The candidate key constraint indicates that the table cannot contain two different rows with the same values under candidate key columns. • foreign keys (referential integrity): Many a times, it is necessary to include column names from one table in another table. Exa ...
... keys are called candidate keys. The candidate key constraint indicates that the table cannot contain two different rows with the same values under candidate key columns. • foreign keys (referential integrity): Many a times, it is necessary to include column names from one table in another table. Exa ...
Coupling Logic Programming with Relational Databases
... a logic programming language and a relational database management system, is the combination of the efficiency and safety of database systems in dealing with large amounts of data with the higher expressive power of logic systems. A logic programming language is a concise and intuitive way of specif ...
... a logic programming language and a relational database management system, is the combination of the efficiency and safety of database systems in dealing with large amounts of data with the higher expressive power of logic systems. A logic programming language is a concise and intuitive way of specif ...
Evaluating and Comparing Oracle Database Appliance X6
... support of database solutions for organizations of every size. Optimized for the world’s most popular database—Oracle Database—it integrates software, compute, storage, and network resources to deliver database services for a wide range of custom and packaged online transaction processing (OLTP), in ...
... support of database solutions for organizations of every size. Optimized for the world’s most popular database—Oracle Database—it integrates software, compute, storage, and network resources to deliver database services for a wide range of custom and packaged online transaction processing (OLTP), in ...
How to Use SQL Calls to Secure Your Web Site
... Among the nine vulnerabilities discussed in the How to Secure Your Web Site, SQL injection is the one that needs a special attention and must be dealt with immediately considering the large impact and serious damage it could cause. In addition, the use of open source software became active in the la ...
... Among the nine vulnerabilities discussed in the How to Secure Your Web Site, SQL injection is the one that needs a special attention and must be dealt with immediately considering the large impact and serious damage it could cause. In addition, the use of open source software became active in the la ...
Upgrade from Oracle9i to Oracle Database 11g
... must be executed to upgrade the Automatic Workload Repository (AWR) to the new database release: SQL> @?/rdbms/admin/catuppst.sql ...
... must be executed to upgrade the Automatic Workload Repository (AWR) to the new database release: SQL> @?/rdbms/admin/catuppst.sql ...
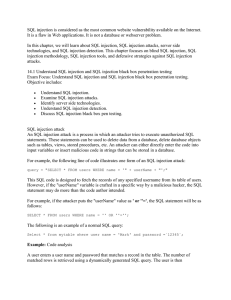
SQL Injection
... database true or false questions and determines the answer on the basis of the applications response. This attack is generally used when the web application is configured to show generic error messages, but has not mitigated the code that is vulnerable to SQL injection. Blind SQL injection is nearly ...
... database true or false questions and determines the answer on the basis of the applications response. This attack is generally used when the web application is configured to show generic error messages, but has not mitigated the code that is vulnerable to SQL injection. Blind SQL injection is nearly ...
Database Processing
... operating systems, including Windows 2000, Windows XP, several variations of UNIX, a number of mainframe operating systems, and Linux. It is a very popular DBMS, and it has a long history of development and use. Oracle exposes much of its technology to the developer; consequently, it can be tuned an ...
... operating systems, including Windows 2000, Windows XP, several variations of UNIX, a number of mainframe operating systems, and Linux. It is a very popular DBMS, and it has a long history of development and use. Oracle exposes much of its technology to the developer; consequently, it can be tuned an ...
Query Optimization
... Steps in Typical Heuristic Optimization 1. Deconstruct conjunctive selections into a sequence of single selection operations (Equiv. rule 1.). 2. Move selection operations down the query tree for the earliest possible execution (Equiv. rules 2, 7a, 7b, 11). 3. Execute first those selection and join ...
... Steps in Typical Heuristic Optimization 1. Deconstruct conjunctive selections into a sequence of single selection operations (Equiv. rule 1.). 2. Move selection operations down the query tree for the earliest possible execution (Equiv. rules 2, 7a, 7b, 11). 3. Execute first those selection and join ...
RDBMS LAB MANUAL Roll.No:1
... CHAR (Size): This data type is used to store character strings values of fixed length. The size in brackets determines the number of characters the cell can hold. The maximum number of character is 255 characters. 1. VARCHAR (Size) / VERCHAR2 (Size): This data type is used to store variable length a ...
... CHAR (Size): This data type is used to store character strings values of fixed length. The size in brackets determines the number of characters the cell can hold. The maximum number of character is 255 characters. 1. VARCHAR (Size) / VERCHAR2 (Size): This data type is used to store variable length a ...
General SQL Parser Java version Developer`s Guide
... The configuration of the General SQL Parser depends on the development environment. This section gives instructions on configuring the General SQL Parser for several development environments. Configuring the General SQL Parser for a Java development environment To configure the General SQL Parser fo ...
... The configuration of the General SQL Parser depends on the development environment. This section gives instructions on configuring the General SQL Parser for several development environments. Configuring the General SQL Parser for a Java development environment To configure the General SQL Parser fo ...
Programmatic SQL
... E.1.3 Host Language Variables A host language variable is a program variable declared in the host language. It can be either a single variable or a structure. Host language variables can be used in embedded SQL statements to transfer data from the database into the program, and vice versa. They can ...
... E.1.3 Host Language Variables A host language variable is a program variable declared in the host language. It can be either a single variable or a structure. Host language variables can be used in embedded SQL statements to transfer data from the database into the program, and vice versa. They can ...
Data-tier Applications in SQL Server 2008 R2
... Moving a data-tier application between instances of SQL Server .......................................................... 12 Step by step - Data-tier applications in SQL Server Management Studio .................................................. 13 Extract Data-tier Application Wizard - Creating a D ...
... Moving a data-tier application between instances of SQL Server .......................................................... 12 Step by step - Data-tier applications in SQL Server Management Studio .................................................. 13 Extract Data-tier Application Wizard - Creating a D ...
Preference SQL - Institut für Informatik
... efficient integration of preferences with SQL technology was available. Recently, [BKS01] can be considered as a move into this direction. The rest of this paper is organized as follows. In section 2 we present the language design of the commercial product Preference SQL [Dat00], its key feature bei ...
... efficient integration of preferences with SQL technology was available. Recently, [BKS01] can be considered as a move into this direction. The rest of this paper is organized as follows. In section 2 we present the language design of the commercial product Preference SQL [Dat00], its key feature bei ...
Android-Chapter17-SQL-Databases
... The select-command extracts from the tblAMIGO table the values indicated in the columns array, namely: recID, name, and phone. The getColumnIndex method is called to determine the position of chosen columns in the current row. The getters: getInt, getString commands are used for field extraction. Th ...
... The select-command extracts from the tblAMIGO table the values indicated in the columns array, namely: recID, name, and phone. The getColumnIndex method is called to determine the position of chosen columns in the current row. The getters: getInt, getString commands are used for field extraction. Th ...
SQL Databases
... The select-command extracts from the tblAMIGO table the values indicated in the columns array, namely: recID, name, and phone. The getColumnIndex method is called to determine the position of chosen columns in the current row. The getters: getInt, getString commands are used for field extraction. Th ...
... The select-command extracts from the tblAMIGO table the values indicated in the columns array, namely: recID, name, and phone. The getColumnIndex method is called to determine the position of chosen columns in the current row. The getters: getInt, getString commands are used for field extraction. Th ...
Evaluating and Comparing Oracle Database Appliance X6
... The Oracle Database Appliance X6-2-HA is an Oracle Engineered System that saves time and money by simplifying deployment, maintenance, and support of high availability database solutions. Optimized for the world’s most popular database— Oracle Database—it integrates software, compute, storage, and n ...
... The Oracle Database Appliance X6-2-HA is an Oracle Engineered System that saves time and money by simplifying deployment, maintenance, and support of high availability database solutions. Optimized for the world’s most popular database— Oracle Database—it integrates software, compute, storage, and n ...
P6 EPPM Database Administration Guide
... Installing a P6 EPPM Database with Oracle ....................................................................................... 17 Installing a P6 EPPM Database with Microsoft SQL Server ............................................................... 18 Upgrading a P6 EPPM Database with Oracle Dat ...
... Installing a P6 EPPM Database with Oracle ....................................................................................... 17 Installing a P6 EPPM Database with Microsoft SQL Server ............................................................... 18 Upgrading a P6 EPPM Database with Oracle Dat ...
- H2 Database Engine
... Error Code Incompatibility........................................................................................................................................33 OSGi................................................................................................................................... ...
... Error Code Incompatibility........................................................................................................................................33 OSGi................................................................................................................................... ...
Database Programming in SQL/Oracle
... the name and {A1 , . . . , An }, n ≥ 0 are the attributes (value properties) of a type. Attribute: a relevant property of entities of a given type. Each attribute can have values from a given domain. Entity: each entity describes a real-world object. Thus, it must be of one of the defined entity typ ...
... the name and {A1 , . . . , An }, n ≥ 0 are the attributes (value properties) of a type. Attribute: a relevant property of entities of a given type. Each attribute can have values from a given domain. Entity: each entity describes a real-world object. Thus, it must be of one of the defined entity typ ...
DBase

dBase (also stylized dBASE) was one of the first database management systems for microcomputers, and the most successful in its day. The dBase system includes the core database engine, a query system, a forms engine, and a programming language that ties all of these components together. dBase's underlying file format, the .dbf file, is widely used in applications needing a simple format to store structured data.dBase was originally published by Ashton-Tate for microcomputer operating system CP/M in 1980, and later ported to Apple II and IBM PC computers running DOS. On the PC platform, in particular, dBase became one of the best-selling software titles for a number of years. A major upgrade was released as dBase III, and ported to a wider variety of platforms, adding UNIX, and VMS. By the mid-1980s, Ashton-Tate was one of the ""big three"" software publishers in the early business software market, the others being Lotus Development and WordPerfect.Starting in the mid-1980s, several companies produced their own variations on the dBase product and especially the dBase programming language. These included FoxBASE+(later renamed FoxPro), Clipper, and other so-called xBase products. Many of these were technically stronger than dBase, but could not push it aside in the market. This changed with the disastrous introduction of dBase IV, whose design and stability were so poor that many users switched to other products. At the same time, there was growing use of IBM-invented SQL (Structured Query Language) in database products. Another factor was user adoption of Microsoft Windows on desktop computers. The shift toward SQL and Windows put pressure on the makers of xBase products to invest in major redesign to provide new capabilities.In spite of growing pressure to evolve, in the early 1990s xBase products constituted the leading database platform for implementing business applications. The size and impact of the xBase market did not go unnoticed, and within one year, the three top xBase firms were acquired by larger software companies. Borland purchased Ashton-Tate, Microsoft bought Fox Software, and Computer Associates acquired Nantucket. However, by the following decade most of the original xBase products had faded from prominence and several disappeared. Products known as dBase still exist, owned by dBase LLC.