lecture6
... an array and not a scalar int mysql_affected_rows ($conn) This function returns the number of rows that were affected by the most recently executed INSERT, UPDATE, REPLACE or DELETE query (i.e. if the number of rows you expected to be updated were actually updated) ...
... an array and not a scalar int mysql_affected_rows ($conn) This function returns the number of rows that were affected by the most recently executed INSERT, UPDATE, REPLACE or DELETE query (i.e. if the number of rows you expected to be updated were actually updated) ...
complete_notes_salal..
... Lecturer-IT Salalah College of Technology Prepared by: Deepak Gour Lecturer-IT, SCT ...
... Lecturer-IT Salalah College of Technology Prepared by: Deepak Gour Lecturer-IT, SCT ...
CIS6930: CGI and Servlets
... Object used for executing an SQL statement. The most important methods for us will be: ResultSet executeQuery(String sql) throws SQLException Executes an SQL statement that returns a single result set. Typically sql will be a SELECT statement. int executeUpdate(String sql) throws SQLException Execut ...
... Object used for executing an SQL statement. The most important methods for us will be: ResultSet executeQuery(String sql) throws SQLException Executes an SQL statement that returns a single result set. Typically sql will be a SELECT statement. int executeUpdate(String sql) throws SQLException Execut ...
Print Slides - IfIS - Technische Universität Braunschweig
... • Find all individuals who have been photographed with “Tony Soprano” and who have been convicted of attempted murder in New Jersey and who have recently had electronic fund transfers made into their bank accounts from ABC Corp. ...
... • Find all individuals who have been photographed with “Tony Soprano” and who have been convicted of attempted murder in New Jersey and who have recently had electronic fund transfers made into their bank accounts from ABC Corp. ...
Select
... Object used for executing an SQL statement. The most important methods for us will be: ResultSet executeQuery(String sql) throws SQLException Executes an SQL statement that returns a single result set. Typically sql will be a SELECT statement. int executeUpdate(String sql) throws SQLException Execut ...
... Object used for executing an SQL statement. The most important methods for us will be: ResultSet executeQuery(String sql) throws SQLException Executes an SQL statement that returns a single result set. Typically sql will be a SELECT statement. int executeUpdate(String sql) throws SQLException Execut ...
peewee Documentation Release 2.4.0 charles leifer October 19, 2014
... Uncle Bob decides that too many animals have been dying at Herb’s house, so he adopts Fido: ...
... Uncle Bob decides that too many animals have been dying at Herb’s house, so he adopts Fido: ...
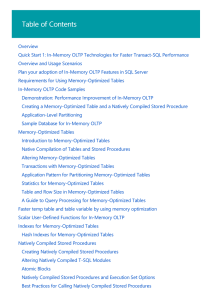
In-Memory OLTP (In-Memory Optimization) | Microsoft Docs
... processing. For the SQL Server technology that improves reporting and analytical query performance see Columnstore Indexes Guide. Several improvements have been made to In-Memory OLTP in SQL Server 2016 as well as in Azure SQL Database. The Transact-SQL surface area has been increased to make it eas ...
... processing. For the SQL Server technology that improves reporting and analytical query performance see Columnstore Indexes Guide. Several improvements have been made to In-Memory OLTP in SQL Server 2016 as well as in Azure SQL Database. The Transact-SQL surface area has been increased to make it eas ...
g EMC VSPEX FOR VIRTUALIZED ORACLE DATABASE 11 OLTP
... Business value Database management systems software continues to be the dominant software used to manage data in nearly all commercial segments. This growth is expected to continue despite the increasing market share of other data management tools. This growth is expected to accelerate as customers ...
... Business value Database management systems software continues to be the dominant software used to manage data in nearly all commercial segments. This growth is expected to continue despite the increasing market share of other data management tools. This growth is expected to accelerate as customers ...
KEMI-TORNIO UNIVERSITY OF APPLIED
... control the connection to database, all the transaction to the database can take the SSL connection after authenticate, it increases the security of protection. PostgreSQL enforces users to use user-defined constraints when adding or modifying data, to ensure data quality follows the limit of rules. ...
... control the connection to database, all the transaction to the database can take the SSL connection after authenticate, it increases the security of protection. PostgreSQL enforces users to use user-defined constraints when adding or modifying data, to ensure data quality follows the limit of rules. ...
INTRODUCTION TO RDBMS
... The most popular RDBMS are MS SQL Server, DB2, Oracle and MySQL. The relational model is an example of record-based model. Record based models are so named because the database is structured in fixed format records of several types. Each table contains records of a particular type. Each record type ...
... The most popular RDBMS are MS SQL Server, DB2, Oracle and MySQL. The relational model is an example of record-based model. Record based models are so named because the database is structured in fixed format records of several types. Each table contains records of a particular type. Each record type ...
SQL Tutrial
... The Oracle Relational Database Management System (RDBMS) is an industry leading database system designed for mission critical data storage and retrieval. The RDBMS is responsible for accurately storing data and efficiently retrieving that data in response to user queries. The Oracle Corporation also ...
... The Oracle Relational Database Management System (RDBMS) is an industry leading database system designed for mission critical data storage and retrieval. The RDBMS is responsible for accurately storing data and efficiently retrieving that data in response to user queries. The Oracle Corporation also ...
How to Use SQL Calls to Secure Your Web Site
... Since 2005, security incidents, such as information leak and web site alteration, have become frequent. Among the nine vulnerabilities discussed in the How to Secure Your Web Site, SQL injection is the one that needs a special attention and must be dealt with immediately considering the large impact ...
... Since 2005, security incidents, such as information leak and web site alteration, have become frequent. Among the nine vulnerabilities discussed in the How to Secure Your Web Site, SQL injection is the one that needs a special attention and must be dealt with immediately considering the large impact ...
The Oracle Database (commonly referred to as Oracle RDBMS or
... An Oracle database system — identified by an alphanumeric system identifier or SID[3] — comprises at least one instance of the application, along with data storage. An instance — identified persistently by an instantiation number (or activation id: SYS.V_$DATABASE.ACTIVATION#) — comprises a set of o ...
... An Oracle database system — identified by an alphanumeric system identifier or SID[3] — comprises at least one instance of the application, along with data storage. An instance — identified persistently by an instantiation number (or activation id: SYS.V_$DATABASE.ACTIVATION#) — comprises a set of o ...
Porting to DB2 Universal Database Version 8.1 from Sybase
... Version 8 can help your organization meet these challenges. DB2 Universal Database for UNIX® and Windows® (DB2 UDB) can help improve the performance of database applications. Many solution developers have already chosen DB2 UDB as their primary development database environment, and have ported and c ...
... Version 8 can help your organization meet these challenges. DB2 Universal Database for UNIX® and Windows® (DB2 UDB) can help improve the performance of database applications. Many solution developers have already chosen DB2 UDB as their primary development database environment, and have ported and c ...
NAVAL POSTGRADUATE SCHOOL
... IPsec security attributes and MYSEA security services based upon administrator choices. Use of intrusion detection technology on the unprotected single level networks can provide administrators with actionable information to inform DSS choices. The objective of this thesis is to design an intrusion ...
... IPsec security attributes and MYSEA security services based upon administrator choices. Use of intrusion detection technology on the unprotected single level networks can provide administrators with actionable information to inform DSS choices. The objective of this thesis is to design an intrusion ...
Firebird 2.5 Quick Start Guide
... The Firebird installer lets you choose between Superserver and Classic/SuperClassic. Each model is fully stable and there is no reason to categorically prefer one to the other. Of course you may have your own specific considerations. When in doubt, consult the Classic, SuperClassic or Superserver ch ...
... The Firebird installer lets you choose between Superserver and Classic/SuperClassic. Each model is fully stable and there is no reason to categorically prefer one to the other. Of course you may have your own specific considerations. When in doubt, consult the Classic, SuperClassic or Superserver ch ...
Teradata QueryGrid: Teradata Database-to
... ServiceConnect, Teradata Source Experts, WebAnalyst, and Xkoto are trademarks or registered trademarks of Teradata Corporation or its affiliates in the United States and other countries. Adaptec and SCSISelect are trademarks or registered trademarks of Adaptec, Inc. AMD Opteron and Opteron are trade ...
... ServiceConnect, Teradata Source Experts, WebAnalyst, and Xkoto are trademarks or registered trademarks of Teradata Corporation or its affiliates in the United States and other countries. Adaptec and SCSISelect are trademarks or registered trademarks of Adaptec, Inc. AMD Opteron and Opteron are trade ...
Certification Sample Test 700 IBM DB2 UDB V8.1 Family
... To process requests, the DB2 OLAP server supports both relational and multidimensional databases. The DB2 OLAP server processes multidimensional requests that calculate, consolidate, and retrieve information from a multidimensional database, a relational database, or both. The options stating object ...
... To process requests, the DB2 OLAP server supports both relational and multidimensional databases. The DB2 OLAP server processes multidimensional requests that calculate, consolidate, and retrieve information from a multidimensional database, a relational database, or both. The options stating object ...
help file and technical documentation
... Hydra_CleanUpLogs .................................................................................................................................................... 31 Hydra_CommandExecute ............................................................................................................. ...
... Hydra_CleanUpLogs .................................................................................................................................................... 31 Hydra_CommandExecute ............................................................................................................. ...
Videoscape Control Suite 3.5.0 Database User Guide
... A logical entity which is always associated with one or more physical data files. All base-level objects which consume space, such as a non-partitioned table or index, reside in one, and one only, tablespace. The data of such a base-level object can reside in multiple datafiles, all of which must be ...
... A logical entity which is always associated with one or more physical data files. All base-level objects which consume space, such as a non-partitioned table or index, reside in one, and one only, tablespace. The data of such a base-level object can reside in multiple datafiles, all of which must be ...
CAMEO DATA MODELER PLUGIN
... Instance term to signify concrete exemplar from that set. Entity term used in this manual corresponds to Entity Type. • Data modeling world frequently uses term Cardinality to denote the allowable numbers of entity instances, which can be associated. But with the rise of the UML, the more correct te ...
... Instance term to signify concrete exemplar from that set. Entity term used in this manual corresponds to Entity Type. • Data modeling world frequently uses term Cardinality to denote the allowable numbers of entity instances, which can be associated. But with the rise of the UML, the more correct te ...
Oracle Exadata Storage Server and Database Machine Technical
... delivers breakthrough performance with linear I/O scalability, is simple to use and manage, and delivers mission-critical availability and reliability. The Exadata Storage Server is an integral component of the Exadata Database Machine. Extreme performance is delivered by several features of the pro ...
... delivers breakthrough performance with linear I/O scalability, is simple to use and manage, and delivers mission-critical availability and reliability. The Exadata Storage Server is an integral component of the Exadata Database Machine. Extreme performance is delivered by several features of the pro ...
EMC VSPEX ORACLE COMPUTING Oracle Database Virtualization Enabled by EMC Data Protection
... vSphere 5.5 to provide virtualization supported by the EMC XtremIO™ storage array. The compute and network components, while vendor-definable, are designed to provide redundancy and sufficient power to handle the processing and data needs of the virtual machine environment. This Implementation Guide ...
... vSphere 5.5 to provide virtualization supported by the EMC XtremIO™ storage array. The compute and network components, while vendor-definable, are designed to provide redundancy and sufficient power to handle the processing and data needs of the virtual machine environment. This Implementation Guide ...
Informix SNMP Subagent Guide
... This manual assumes that you use the U.S. 8859-1 English locale as the default locale. The default is en_us.8859-1 (ISO 8859-1) on UNIX platforms or en_us.CP1252 (Microsoft 1252) for Windows NT environments. This locale supports U.S. English format conventions for dates, times, and currency, and als ...
... This manual assumes that you use the U.S. 8859-1 English locale as the default locale. The default is en_us.8859-1 (ISO 8859-1) on UNIX platforms or en_us.CP1252 (Microsoft 1252) for Windows NT environments. This locale supports U.S. English format conventions for dates, times, and currency, and als ...
Database Repairing and Consistent Query Answering Database
... certain desirable integrity constraints (ICs). This is usually achieved by means of built-in support provided by database management systems. They allow for the maintenance of limited classes of ICs that can be declared together with the database schema. Another possibility is the use of triggers or ...
... certain desirable integrity constraints (ICs). This is usually achieved by means of built-in support provided by database management systems. They allow for the maintenance of limited classes of ICs that can be declared together with the database schema. Another possibility is the use of triggers or ...