3 - Terena
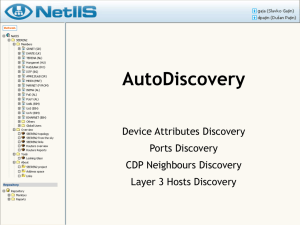
... CDP offers the information about models of these devices, as well as connected ports ...
... CDP offers the information about models of these devices, as well as connected ports ...
reliability of wireless networks and devices
... “A wireless network is a flexible data communications system, which uses wireless media such as radio frequency technology to transmit and receive data over the air, minimizing the need for wired connections.Wireless networks are used to augment rather than replace wired networks and are most common ...
... “A wireless network is a flexible data communications system, which uses wireless media such as radio frequency technology to transmit and receive data over the air, minimizing the need for wired connections.Wireless networks are used to augment rather than replace wired networks and are most common ...
Smart Grid in Distribution Network
... – Different coding rate depending on remaining time to deadline – Tradeoff between throughput and how much redundancy is needed – Additional processing such as majority voting – Decoder keeps information for future use (efficiency) ...
... – Different coding rate depending on remaining time to deadline – Tradeoff between throughput and how much redundancy is needed – Additional processing such as majority voting – Decoder keeps information for future use (efficiency) ...
Wireless LAN Management
... used for one channel is 22 Mbps In 2.4 GHz band , bandwidth is only 83 MHz available So, we need 5 channel space for nonoverlapping channel ...
... used for one channel is 22 Mbps In 2.4 GHz band , bandwidth is only 83 MHz available So, we need 5 channel space for nonoverlapping channel ...
Accessing Oakton`s Wireless Network
... Please be advised that the wireless network does not enforce any security or encryption. At this time, Oakton is providing public access to the Internet and all Internet accessible Oakton resources (email, www.oakton.edu, etc.). For security reasons, access to internal applications is not allowed. T ...
... Please be advised that the wireless network does not enforce any security or encryption. At this time, Oakton is providing public access to the Internet and all Internet accessible Oakton resources (email, www.oakton.edu, etc.). For security reasons, access to internal applications is not allowed. T ...
Basic Service Set (BSS)
... • The BSSID is the “name” of the BSS (not same as SSID) • APs can be positioned so that cells overlap to facilitate roaming – Wireless devices choose AP based on signal strength – Stations going from one BSS to another will deal with Handoff Wired LAN ...
... • The BSSID is the “name” of the BSS (not same as SSID) • APs can be positioned so that cells overlap to facilitate roaming – Wireless devices choose AP based on signal strength – Stations going from one BSS to another will deal with Handoff Wired LAN ...
Quick-Start Guide
... Connect the SpeedStream® Device 1. Connect the straightthrough Ethernet cable (RJ-45) to the Ethernet port on the SpeedStream® device (yellow port). 2. Connect the other end of the straight-through Ethernet cable (RJ-45) to the Ethernet port on your computer. 3. Plug the DSL cable (RJ-11) into the D ...
... Connect the SpeedStream® Device 1. Connect the straightthrough Ethernet cable (RJ-45) to the Ethernet port on the SpeedStream® device (yellow port). 2. Connect the other end of the straight-through Ethernet cable (RJ-45) to the Ethernet port on your computer. 3. Plug the DSL cable (RJ-11) into the D ...
Download the bC Wireless datasheet here
... The METTLER TOLEDO Wireless Solution for bC scales (available as an option) provides retailers new freedom in their fresh food sales. The factory-installed WLAN module ensures a secure wireless connection of the bC scale to an existing network. Set up, switch on – and right away you are in the netwo ...
... The METTLER TOLEDO Wireless Solution for bC scales (available as an option) provides retailers new freedom in their fresh food sales. The factory-installed WLAN module ensures a secure wireless connection of the bC scale to an existing network. Set up, switch on – and right away you are in the netwo ...
MESH NETWORK SIMULAION Pei Ping Belarusian National
... where concrete walls create non-line-of-sight transmission environment. The solid line indicates the connectivity among nodes. By connected, it means a node can directly (without routing) ping another node in the network with more than 50% successful rate at 6 Mbps. Otherwise, the link between them ...
... where concrete walls create non-line-of-sight transmission environment. The solid line indicates the connectivity among nodes. By connected, it means a node can directly (without routing) ping another node in the network with more than 50% successful rate at 6 Mbps. Otherwise, the link between them ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... collectively known as Wi-Fi technologies. Additionally, Bluetooth and various other non Wi-Fi technologies also exist, each also designed for specific networking applications. ...
... collectively known as Wi-Fi technologies. Additionally, Bluetooth and various other non Wi-Fi technologies also exist, each also designed for specific networking applications. ...
Changes in Power System Communications
... • The IEEE 1394 interface is a serial bus interface standard for high-speed communications and isochronous real-time data transfer, frequently used in a personal computer (and digital audio and digital video). The interface is also known by the brand names of FireWire (Apple Inc.), i.LINK (Sony), an ...
... • The IEEE 1394 interface is a serial bus interface standard for high-speed communications and isochronous real-time data transfer, frequently used in a personal computer (and digital audio and digital video). The interface is also known by the brand names of FireWire (Apple Inc.), i.LINK (Sony), an ...
Chapter 6 slides, Computer Networking, 3rd edition
... run applications may be stationary (non-mobile) or mobile ...
... run applications may be stationary (non-mobile) or mobile ...
draft-brandt-coap-subnet
... Limited competition Higher cost High cost Limited market growth ...
... Limited competition Higher cost High cost Limited market growth ...
Wireless Networks
... • They integrate into existing networks through access points which provide a bridging function • They let you stay connected as you roam from one coverage area to another • They have unique security considerations • They have specific interoperability requirements • They require different hardware ...
... • They integrate into existing networks through access points which provide a bridging function • They let you stay connected as you roam from one coverage area to another • They have unique security considerations • They have specific interoperability requirements • They require different hardware ...
SpeedTouch™ 585(i) v6
... All trademarks are owned by their respective owners. Product specifications subject to change without prior notice. ...
... All trademarks are owned by their respective owners. Product specifications subject to change without prior notice. ...
EMBEDDED COMPUTATION MEETS THE WORLD WIDE WEB
... • Lookup service: When a device plugs in, it goes through an add-in protocol. (1) Discovery - The device first locates the lookup service (2) join-in - then uploads an object that implements all of its services' interfaces ...
... • Lookup service: When a device plugs in, it goes through an add-in protocol. (1) Discovery - The device first locates the lookup service (2) join-in - then uploads an object that implements all of its services' interfaces ...
Wireless Communications and Networks
... Higher data rates obtainable with broadband wireless technology ...
... Higher data rates obtainable with broadband wireless technology ...
Document
... frequently due to node mobility and node failure • May leverage broadcasting than point-to-point communications • May operate in aggregate fashion • In-network processing • Sensor nodes are limited in power, computational capacities, and memory • May not have global ID like IP address • Need tight i ...
... frequently due to node mobility and node failure • May leverage broadcasting than point-to-point communications • May operate in aggregate fashion • In-network processing • Sensor nodes are limited in power, computational capacities, and memory • May not have global ID like IP address • Need tight i ...
1 - Cyber-Physical Systems Integration Group @ DGIST
... • It was designed to wirelessly connect small devices to mobile terminals • LEE was released to the public with the name Wibree in 2006 • Its products can be categorized into two groups - dual-mode chips: equipped with sensors/actuators - standalone chips: equipped with a personal server • It will l ...
... • It was designed to wirelessly connect small devices to mobile terminals • LEE was released to the public with the name Wibree in 2006 • Its products can be categorized into two groups - dual-mode chips: equipped with sensors/actuators - standalone chips: equipped with a personal server • It will l ...
- Draytek
... The professional VPN router DrayTek Vigor2832 series provides companies with secure Interenet access. The integrated ADSL2+ modem connects directly to standard ADSL line without additional device. With Gigabit Etherenet and 4G LTE USB WAN, the Vigor2832 series provides a flexible load balancing and ...
... The professional VPN router DrayTek Vigor2832 series provides companies with secure Interenet access. The integrated ADSL2+ modem connects directly to standard ADSL line without additional device. With Gigabit Etherenet and 4G LTE USB WAN, the Vigor2832 series provides a flexible load balancing and ...
Lecture 19
... You’re responsible for saving any variables that are shared by the original program and the interrupt routine. You should then restore these values before you return from the interrupt. But check whether the compiler takes care of this… ...
... You’re responsible for saving any variables that are shared by the original program and the interrupt routine. You should then restore these values before you return from the interrupt. But check whether the compiler takes care of this… ...
ppt
... • As C receives packets, carrier sense would prevent it from sending to D, even though wouldn’t interfere • RTS/CTS can help – C hears RTS from B, but not CTS from A – C knows it’s transmission will not interfere with A – C is safe to transmit to D ...
... • As C receives packets, carrier sense would prevent it from sending to D, even though wouldn’t interfere • RTS/CTS can help – C hears RTS from B, but not CTS from A – C knows it’s transmission will not interfere with A – C is safe to transmit to D ...
Wireless USB

Wireless USB is a short-range, high-bandwidth wireless radio communication protocol created by the Wireless USB Promoter Group. Wireless USB is sometimes abbreviated as ""WUSB"", although the USB Implementers Forum discouraged this practice and instead prefers to call the technology Certified Wireless USB to distinguish it from the competing UWB standard.Wireless USB was based on the (now defunct) WiMedia Alliance's ultra-wideband (UWB) common radio platform, which is capable of sending 480 Mbit/s at distances up to 3 metres (9.8 ft) and 110 Mbit/s at up to 10 metres (33 ft). It was designed to operate in the 3.1 to 10.6 GHz frequency range, although local regulatory policies may restrict the legal operating range for any given country.