Networking in Linux
... Routers ports (book page 398). If no ports found means security is in place. If you find ports open you may be able to identify the type of device (routers, switches, hubs) and their manufacturers. ...
... Routers ports (book page 398). If no ports found means security is in place. If you find ports open you may be able to identify the type of device (routers, switches, hubs) and their manufacturers. ...
Adaptive Modules G24/G30/H24 GPRS Terminal Card
... Equipment DTE connected to the RS232 interface and it is managed by AT commands according to the GSM 07.07 and 07.05 specification and additional Motorola supported commands, listed in the Motorola AT Commands Reference Guides. ...
... Equipment DTE connected to the RS232 interface and it is managed by AT commands according to the GSM 07.07 and 07.05 specification and additional Motorola supported commands, listed in the Motorola AT Commands Reference Guides. ...
Network Layer
... Fixed length instructions help to align, fetch, prefetch, optimize, synchronize, reorder etc. ◦ See the original 360 and Robert Tomasulo ...
... Fixed length instructions help to align, fetch, prefetch, optimize, synchronize, reorder etc. ◦ See the original 360 and Robert Tomasulo ...
TECHNICAL SUPPORT and HARDWARE/SOFTWARE/NETWORK MAINTENANCE for
... as a backup to the fiber optic line. Dolnick Telephone Configuration and Support The current IPFW campus phone service does not extend to Dolnick Learning Center, therefore, the Center uses Voice Over IP (VOIP) technology as their phone service. This technology uses a B1 connection to the IPFW data ...
... as a backup to the fiber optic line. Dolnick Telephone Configuration and Support The current IPFW campus phone service does not extend to Dolnick Learning Center, therefore, the Center uses Voice Over IP (VOIP) technology as their phone service. This technology uses a B1 connection to the IPFW data ...
NOT permitted beyond the intended personal use. personal routers, wireless routers,
... These restrictions include, but are not limited to, the use of personal routers, wireless routers, wireless access points, NAT devices, or any other device that acts as a router (i.e. personal computer configured to bridge or share network connections).These devices can cause unexpected network outa ...
... These restrictions include, but are not limited to, the use of personal routers, wireless routers, wireless access points, NAT devices, or any other device that acts as a router (i.e. personal computer configured to bridge or share network connections).These devices can cause unexpected network outa ...
TCP, UDP, ICMP - Dr. Stephen C. Hayne
... has more overhead SYN, ACK, RST help attackers find open ports ...
... has more overhead SYN, ACK, RST help attackers find open ports ...
Lecture Note Ch.2
... time with port addresses a, b, and c. The receiving computer is running two processes at this time with port addresses j and k. Process a in the sending computer needs to communicate with process j in the receiving computer. Note that although physical addresses change from hop to hop, logical and p ...
... time with port addresses a, b, and c. The receiving computer is running two processes at this time with port addresses j and k. Process a in the sending computer needs to communicate with process j in the receiving computer. Note that although physical addresses change from hop to hop, logical and p ...
Chapter 6 – Connectivity Devices
... associated with what ports. The Forwarding Table must be built • Once a bridge is installed, it polls the clients on each of its ports to provide their MAC address • Once the bridge receives this information, it is recorded in its Forwarding Table • The filtering of traffic enhances the network perf ...
... associated with what ports. The Forwarding Table must be built • Once a bridge is installed, it polls the clients on each of its ports to provide their MAC address • Once the bridge receives this information, it is recorded in its Forwarding Table • The filtering of traffic enhances the network perf ...
EIR-x-Sx Series Datasheet
... locations (Applicable to versions with Terminal Block power option). This equipment is suitable for use in Class I, Division 2, Groups A, B, C and D OR non-hazardous locations only. WARNING – EXPLOSION HAZARD – Do not disconnect equipment unless power has been removed or the area is known to be non- ...
... locations (Applicable to versions with Terminal Block power option). This equipment is suitable for use in Class I, Division 2, Groups A, B, C and D OR non-hazardous locations only. WARNING – EXPLOSION HAZARD – Do not disconnect equipment unless power has been removed or the area is known to be non- ...
xDirect Product Brief, Partners
... easy Ethernet connectivity to virtually any device or machine with a serial interface. With an integrated Ethernet port and serial cable, multiple power options including PoE, and an industry-best five year warranty, xDirect provides a portable, extremely flexible, and highly affordable network conn ...
... easy Ethernet connectivity to virtually any device or machine with a serial interface. With an integrated Ethernet port and serial cable, multiple power options including PoE, and an industry-best five year warranty, xDirect provides a portable, extremely flexible, and highly affordable network conn ...
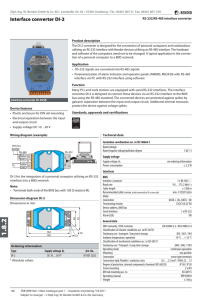
Interface converter DI-2
... utilising an RS-232 interface with Bender devices utilising an RS-485 interface. The hardware and software of the computers need not to be changed. A typical application is the connection of a personal computer to a BMS network. Application • RS-232 signals are converted into RS-485 signals • Parame ...
... utilising an RS-232 interface with Bender devices utilising an RS-485 interface. The hardware and software of the computers need not to be changed. A typical application is the connection of a personal computer to a BMS network. Application • RS-232 signals are converted into RS-485 signals • Parame ...
The Internet of Unpatched Things Sarthak Grover and Nick Feamster Princeton University
... The Internet of Unpatched Things Sarthak Grover and Nick Feamster Princeton University ...
... The Internet of Unpatched Things Sarthak Grover and Nick Feamster Princeton University ...
Cellular IP Modems
... The OnCell G3100 comes bundled with Real COM drivers for Windows 98, ME, NT, 2000, XP, 2003, and Vista systems. In Real COM mode, the bundled drivers are able to establish a transparent connection between a host and a serial device by mapping the serial port on the OnCell G3100 to a local COM port o ...
... The OnCell G3100 comes bundled with Real COM drivers for Windows 98, ME, NT, 2000, XP, 2003, and Vista systems. In Real COM mode, the bundled drivers are able to establish a transparent connection between a host and a serial device by mapping the serial port on the OnCell G3100 to a local COM port o ...
Medi-Kool (tm) USB Instructions
... The LOG data can be downloaded from the unit to a computer using a USB port located in the front of the control panel. For this, the operator needs to install an USB driver and use a terminal program or other download software compatible with the Kermit transfer protocol. The downloaded LOG data wil ...
... The LOG data can be downloaded from the unit to a computer using a USB port located in the front of the control panel. For this, the operator needs to install an USB driver and use a terminal program or other download software compatible with the Kermit transfer protocol. The downloaded LOG data wil ...
The Network Layer - Computer Science
... Forwarding: Prefix Matching • Routing table would be too large, if every single possible address were included • Instead, each entry contains range of addresses, specified by common bit prefix – 10110000 through 10111111 represented as 1011 – 11000000 through 11111111 represented as 11 – 11000100 t ...
... Forwarding: Prefix Matching • Routing table would be too large, if every single possible address were included • Instead, each entry contains range of addresses, specified by common bit prefix – 10110000 through 10111111 represented as 1011 – 11000000 through 11111111 represented as 11 – 11000100 t ...
Using VDOMs to host two FortiOS instances on a single FortiGate unit
... Using VDOMs to host two FortiOS instances on a single FortiGate unit Virtual Domains (VDOMs) can be used to divide a single FortiGate unit into two or more virtual instances of FortiOS that function as independent FortiGate units. This example simulates an ISP that provides Company A and Company B w ...
... Using VDOMs to host two FortiOS instances on a single FortiGate unit Virtual Domains (VDOMs) can be used to divide a single FortiGate unit into two or more virtual instances of FortiOS that function as independent FortiGate units. This example simulates an ISP that provides Company A and Company B w ...
National Semiconductor® General Purpose I/O Controller
... Each input pin can be enabled to provide level-sensitive interrupt capabability, with programmable polarity. The interrupt output signal from the General Purpose I/O Controller is the logic OR of all interrupt-enabled inputs. A functional test feature enables the I/O pins to be controlled and driven ...
... Each input pin can be enabled to provide level-sensitive interrupt capabability, with programmable polarity. The interrupt output signal from the General Purpose I/O Controller is the logic OR of all interrupt-enabled inputs. A functional test feature enables the I/O pins to be controlled and driven ...
Switching
... • Half duplex – link shared by many hosts via a hub – Data can travel in both directions but only one direction at a time (1 lane bridge) – Uses CSMA/CD to detect and manage collisions – Hub based networks – Lower performance – lots of waiting for the media – 50–60% efficiency ...
... • Half duplex – link shared by many hosts via a hub – Data can travel in both directions but only one direction at a time (1 lane bridge) – Uses CSMA/CD to detect and manage collisions – Hub based networks – Lower performance – lots of waiting for the media – 50–60% efficiency ...
ppt
... Using Divide and Conquer, check many in parallel. only a very small portion of addresses are monitored, so send same probe to many addresses ...
... Using Divide and Conquer, check many in parallel. only a very small portion of addresses are monitored, so send same probe to many addresses ...
Mountain Sky
... • IDF 1’s catchments area is the Administration Block. • This IDF must be able to service 6 offices with 4 runs going to each. • We have decided to use one 24 port switch as not all runs going into the offices will be used. • This in turn will allow for any installation of extra network devices. • A ...
... • IDF 1’s catchments area is the Administration Block. • This IDF must be able to service 6 offices with 4 runs going to each. • We have decided to use one 24 port switch as not all runs going into the offices will be used. • This in turn will allow for any installation of extra network devices. • A ...
Security Management System - Remote Client
... Security Management System – Remote Client In most of the deployment scenarios, the server application is hosted on a computer which is on the internal network of an enterprise. Hence it is not accessible from the client applications running on computers outside this internal enterprise network. Thi ...
... Security Management System – Remote Client In most of the deployment scenarios, the server application is hosted on a computer which is on the internal network of an enterprise. Hence it is not accessible from the client applications running on computers outside this internal enterprise network. Thi ...
5a4d8f0d-4e31-4759-80ea-1d10c6350681-rtf
... Running in two shifts, the new medium-format Rapida 105 prints covers and other high-quality jobs. It joins a fleet of four KBA Rapida 162a large-format presses for four and five colours that were installed between 1999 and 2002 and have contributed in no small measure to the company’s success. Book ...
... Running in two shifts, the new medium-format Rapida 105 prints covers and other high-quality jobs. It joins a fleet of four KBA Rapida 162a large-format presses for four and five colours that were installed between 1999 and 2002 and have contributed in no small measure to the company’s success. Book ...
Parallel port

A parallel port is a type of interface found on computers (personal and otherwise) for connecting peripherals. In computing, a parallel port is a parallel communication physical interface. It is also known as a printer port or Centronics port. It was an industry de facto standard for many years, and was finally standardized as IEEE 1284 in the late 1990s, which defined the Enhanced Parallel Port (EPP) and Extended Capability Port (ECP) bi-directional versions. Today, the parallel port interface is seeing decreasing use because of the rise of Universal Serial Bus (USB) devices, along with network printing using Ethernet.The parallel port interface was originally known as the Parallel Printer Adapter on IBM PC-compatible computers. It was primarily designed to operate a line printer that used IBM's 8-bit extended ASCII character set to print text, but could also be used to adapt other peripherals. Graphical printers, along with a host of other devices, have been designed to communicate with the system.