sink
... The author wish to design techniques and protocols that lead to efficient data aggregation without explicit maintenance of a structure. ...
... The author wish to design techniques and protocols that lead to efficient data aggregation without explicit maintenance of a structure. ...
Computer Networking viva IT-3
... regardless of whether it is connected to another network or not. Q5 What are the characteristics of the bus topology? A5 In a bus topology, all the communicating equipment is connected through the same cable, or set of cables. Q6 What is star topology A6 Star Topology is the most common type of netw ...
... regardless of whether it is connected to another network or not. Q5 What are the characteristics of the bus topology? A5 In a bus topology, all the communicating equipment is connected through the same cable, or set of cables. Q6 What is star topology A6 Star Topology is the most common type of netw ...
CSC311_UNIT1_Part2
... We use the concept of layers in our daily life. As an example, let us consider two friends who communicate through postal mail. The process of sending a letter to a friend would be complex if there were no services available from the post office. ...
... We use the concept of layers in our daily life. As an example, let us consider two friends who communicate through postal mail. The process of sending a letter to a friend would be complex if there were no services available from the post office. ...
ppt for Chapters 1-5 - Computer and Information Sciences
... * its own unicast address * the network broadcast address ■ promiscuous mode Interface process all received packets (including those addressed to other stations) ...
... * its own unicast address * the network broadcast address ■ promiscuous mode Interface process all received packets (including those addressed to other stations) ...
Improving Security in Anonymizing Networks using a Privacy Enhancing System
... [2] Dingledine.R, Mathewson.N, and Syverson.P, “Tor: The SecondGeneration Onion Router,” Proc. Usenix Security Symp, pp. 303320, Aug. 2004. [3] Holt.J.E and Seamons.K.E, “Nym: Practical Pseudonymity for Anonymous Networks,” Internet Security Research Lab Technical ...
... [2] Dingledine.R, Mathewson.N, and Syverson.P, “Tor: The SecondGeneration Onion Router,” Proc. Usenix Security Symp, pp. 303320, Aug. 2004. [3] Holt.J.E and Seamons.K.E, “Nym: Practical Pseudonymity for Anonymous Networks,” Internet Security Research Lab Technical ...
dbtma
... Stop when completing transmitting RTS BTr (Receiver Busy Tone) Set up by the node which receives RTS Stop when completely receives the data packet All nodes sensing any busy tone are not allowed to send RTS Any node sensing no busy tone is allowed to transmit ...
... Stop when completing transmitting RTS BTr (Receiver Busy Tone) Set up by the node which receives RTS Stop when completely receives the data packet All nodes sensing any busy tone are not allowed to send RTS Any node sensing no busy tone is allowed to transmit ...
... a single protocol can't do everything higher-level protocols build elaborate operations out of simpler ones each layer uses only the services of the one directly below and provides the services expected by the layer above all communication is between peer levels: layer N destination receives exactly ...
Why Big Data Needs Big Buffer Switches
... When many flows pass through a congested switch with limited buffer resources, which packet is dropped and which flow is impacted is a function of whether a packet buffer was available in the precise moment when that packet arrived, and is therefore a function of chance. TCP flows with packets that ...
... When many flows pass through a congested switch with limited buffer resources, which packet is dropped and which flow is impacted is a function of whether a packet buffer was available in the precise moment when that packet arrived, and is therefore a function of chance. TCP flows with packets that ...
Glavlit: Preventing Exfiltration at Wire Speed
... prevent unauthorized release from a protected network while allowing authorized information to pass unhindered. Our goals for Glavlit are transparency, performance, and simplicity. Glavlit provides stringent security guarantees by enforcing complex exit policies while trusting only the systems respo ...
... prevent unauthorized release from a protected network while allowing authorized information to pass unhindered. Our goals for Glavlit are transparency, performance, and simplicity. Glavlit provides stringent security guarantees by enforcing complex exit policies while trusting only the systems respo ...
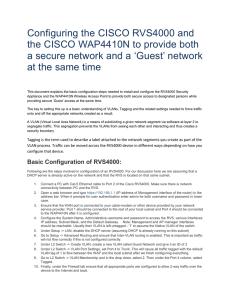
Basic Configuration of WAP4410N
... Enable. Now go to Wireless -> Security and setup an appropriately secure configuration for the secure network. Once that is complete select the Guest Network and setup its security as well. Under Wireless -> VLAN and QoS ensure that VLAN is enabled, that the default VLAN is 1 and that the VLAN for y ...
... Enable. Now go to Wireless -> Security and setup an appropriately secure configuration for the secure network. Once that is complete select the Guest Network and setup its security as well. Under Wireless -> VLAN and QoS ensure that VLAN is enabled, that the default VLAN is 1 and that the VLAN for y ...
MetroFi Cupertino - Wireless Internet Institute
... broadband service led to success Regardless of the business model, the service will be perceived as a partnership by the community – therefore, taking a proactive and collaborative stance will be of mutual benefit and improve the response of the community Agreements between entities need to account ...
... broadband service led to success Regardless of the business model, the service will be perceived as a partnership by the community – therefore, taking a proactive and collaborative stance will be of mutual benefit and improve the response of the community Agreements between entities need to account ...
Workstar iGuard
... iGuard is an Internet-Ready Security System, and is the first and the only security product in the market that uses TCP/IP as the protocol to communicate with other iGuards and the outside world. The protocol enables the device to directly connect to the corporate network via the existing cable wiri ...
... iGuard is an Internet-Ready Security System, and is the first and the only security product in the market that uses TCP/IP as the protocol to communicate with other iGuards and the outside world. The protocol enables the device to directly connect to the corporate network via the existing cable wiri ...
Switching Techniques: Circuit Switching Message Switching packet
... Provide initial delay for setting up the call. Inefficient for bursty traffic. Data rate should be same because of fixed bandwidth. When load increases, some calls may be blocked. In data communication, traffic between terminal and server are not continuous. Sometimes more data may come or sometimes ...
... Provide initial delay for setting up the call. Inefficient for bursty traffic. Data rate should be same because of fixed bandwidth. When load increases, some calls may be blocked. In data communication, traffic between terminal and server are not continuous. Sometimes more data may come or sometimes ...
How Voice Calls Affect Data in Operational LTE Networks
... *University of California, Los Angeles, US +Ohio State University, Columbus, US ...
... *University of California, Los Angeles, US +Ohio State University, Columbus, US ...
Network Technologies
... – Routers performing forwarding/routing in software were slow for large networks ...
... – Routers performing forwarding/routing in software were slow for large networks ...
Revision Notes - DCU School of Computing
... – Repeaters - when data travels over long distances, the signal sending the data can weaken over long distances, repeaters are used to amplify the data at intervals – Routers come into play when data is being sent between two different networks. It examines packets for destination and selects the qu ...
... – Repeaters - when data travels over long distances, the signal sending the data can weaken over long distances, repeaters are used to amplify the data at intervals – Routers come into play when data is being sent between two different networks. It examines packets for destination and selects the qu ...
Network Performance Troubleshooting
... In early days of the Internet packet loss usually meant a packet corruption due to bad links quality, the obvious remedy was to retransmit ...
... In early days of the Internet packet loss usually meant a packet corruption due to bad links quality, the obvious remedy was to retransmit ...
AppGate Distributed Device Firewall ™ Protecting user devices and the network
... on system classes and IP addresses: for example for user workstations and for corporate servers on different networks. Several Policy Managers can also work in parallel. This enables a high degree of redundancy as well as offering load sharing on very large networks. The AppGate Policy Manager is de ...
... on system classes and IP addresses: for example for user workstations and for corporate servers on different networks. Several Policy Managers can also work in parallel. This enables a high degree of redundancy as well as offering load sharing on very large networks. The AppGate Policy Manager is de ...
Comparison and Contrast between the OSI and TCP/IP Model
... not have much experience with the subject and did not have a good idea of which functionality to put in which layer. – Being general, the protocols in the OSI model are better hidden than in the TCP/IP model and can be replaced relatively easily as the technology changes. – Not so widespread as comp ...
... not have much experience with the subject and did not have a good idea of which functionality to put in which layer. – Being general, the protocols in the OSI model are better hidden than in the TCP/IP model and can be replaced relatively easily as the technology changes. – Not so widespread as comp ...
Switching Techniques: Circuit Switching
... Provide initial delay for setting up the call. Inefficient for bursty traffic. Data rate should be same because of fixed bandwidth. When load increases, some calls may be blocked. In data communication, traffic between terminal and server are not continuous. Sometimes more data may come or sometimes ...
... Provide initial delay for setting up the call. Inefficient for bursty traffic. Data rate should be same because of fixed bandwidth. When load increases, some calls may be blocked. In data communication, traffic between terminal and server are not continuous. Sometimes more data may come or sometimes ...
Chapter 1
... information about pathways with other networks. How and when error and system messages are ...
... information about pathways with other networks. How and when error and system messages are ...
Document
... dissimilar networks. A Backbone is central interconnecting structure that connects one or more networks just like the trunk of a tree or the spine of a human being ...
... dissimilar networks. A Backbone is central interconnecting structure that connects one or more networks just like the trunk of a tree or the spine of a human being ...
ppt - People @EECS
... – Need some way to make sure that packets actually make it to receiver » Every packet received at least once » Every packet received at most once ...
... – Need some way to make sure that packets actually make it to receiver » Every packet received at least once » Every packet received at most once ...