public key cryptography
... • For both AH and ESP, source, destination handshake: – create network-layer logical channel called a service agreement (SA) • Each SA unidirectional. • Uniquely determined by: – security protocol (AH or ESP) – source IP address – 32-bit connection ID ...
... • For both AH and ESP, source, destination handshake: – create network-layer logical channel called a service agreement (SA) • Each SA unidirectional. • Uniquely determined by: – security protocol (AH or ESP) – source IP address – 32-bit connection ID ...
CS 3013 Operating Systems I
... Phone lines first, satellite and radio later – req: connect multiple networks seamlessly DoD ...
... Phone lines first, satellite and radio later – req: connect multiple networks seamlessly DoD ...
1_hProtocolsOSI
... • establishing a connection between end-to-end systems that defines the parameters of the connection • and ensuring that data actually gets to its destination in the correct order and error free • Examples of protocols found at this layer include TCP and UDP. ...
... • establishing a connection between end-to-end systems that defines the parameters of the connection • and ensuring that data actually gets to its destination in the correct order and error free • Examples of protocols found at this layer include TCP and UDP. ...
Topologies
... • Function of a segment is to act as an efficient local LAN that is part of a larger network • Segment, as applied to LANs, is completely different from the Layer 4 PDU known as a segment ...
... • Function of a segment is to act as an efficient local LAN that is part of a larger network • Segment, as applied to LANs, is completely different from the Layer 4 PDU known as a segment ...
Document
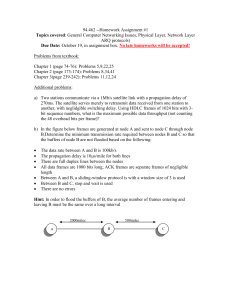
... B.Determine the minimum transmission rate required between nodes B and C so that the buffers of node B are not flooded based on the following: ...
... B.Determine the minimum transmission rate required between nodes B and C so that the buffers of node B are not flooded based on the following: ...
Document
... reliable transfer of data, and for grouping data together into frames. Frames are similar to data packets but are blocks of data specific to a single type of hardware architecture. Frames have checksums to detect errors in transmission. Corrupted frames are discarded so that they will not be passed ...
... reliable transfer of data, and for grouping data together into frames. Frames are similar to data packets but are blocks of data specific to a single type of hardware architecture. Frames have checksums to detect errors in transmission. Corrupted frames are discarded so that they will not be passed ...
Network Layers
... It allows communication across networks of the same and different types and carries out translations to deal with dissimilar data addressing schemes. IP (Internet Protocol) and ARP (Address Resolution Protocol) are both to be found at the Internet layer. ...
... It allows communication across networks of the same and different types and carries out translations to deal with dissimilar data addressing schemes. IP (Internet Protocol) and ARP (Address Resolution Protocol) are both to be found at the Internet layer. ...
Document
... TCP uses IP to send TCP segments, which contain additional information that allows it to order packets and resend them if they go astray. ...
... TCP uses IP to send TCP segments, which contain additional information that allows it to order packets and resend them if they go astray. ...
Part I: Introduction
... Rejaie et al “ RAP: end to end control for real time streams” Infocom 99 Tang et al “ RCS: Rate Control Scheme..for high bit error rates” ...
... Rejaie et al “ RAP: end to end control for real time streams” Infocom 99 Tang et al “ RCS: Rate Control Scheme..for high bit error rates” ...
Chapter 4
... • IPv6 slated to replace current IP protocol, IPv4 – More efficient header, better security, better prioritization – Billions of additional IP addresses ...
... • IPv6 slated to replace current IP protocol, IPv4 – More efficient header, better security, better prioritization – Billions of additional IP addresses ...
What computers talk about and how
... Internet is actually a bunch of connected computers called routers Packets hop from router to router until they reach destination ...
... Internet is actually a bunch of connected computers called routers Packets hop from router to router until they reach destination ...
What computers talk about and how. COS 116, Spring 2012 Adam Finkelstein
... Internet is actually a bunch of connected computers called routers Packets hop from router to router until they reach destination ...
... Internet is actually a bunch of connected computers called routers Packets hop from router to router until they reach destination ...
Internet:Overview - CSE Labs User Home Pages
... Once connected, consistently good quality, unless using cell phones ...
... Once connected, consistently good quality, unless using cell phones ...
Document
... which contain additional information that allows it to order packets and resend them if they go astray. ...
... which contain additional information that allows it to order packets and resend them if they go astray. ...
1-Introduction :
... The Data Link layer prepares a packet for transport across the local media by encapsulating it with a header and a trailer to create a frame. Unlike the other PDUs that have been discussed in this course, the Data Link layer frame includes: • Data - The packet from the Network layer • Header - Conta ...
... The Data Link layer prepares a packet for transport across the local media by encapsulating it with a header and a trailer to create a frame. Unlike the other PDUs that have been discussed in this course, the Data Link layer frame includes: • Data - The packet from the Network layer • Header - Conta ...
ip-basics
... use IP Addresses but Humans find names easier to remember DNS provides a mapping of IP Addresses to names and vice versa Computers may be moved between networks, in which case their IP address will change BUT their names can remain the same ...
... use IP Addresses but Humans find names easier to remember DNS provides a mapping of IP Addresses to names and vice versa Computers may be moved between networks, in which case their IP address will change BUT their names can remain the same ...
Week 1 - cda college
... which computers, printers, and other devices are connected Describes the layout of the wire and devices as well as the paths used by data ...
... which computers, printers, and other devices are connected Describes the layout of the wire and devices as well as the paths used by data ...
What is a protocol?
... In the early days of the network there was a perceived need for users at one computer to log into another computer. The protocol that was used in the original ARPAnet, the 1822 protocol, was inadequate for this and another protocol, NCP, was devised and implemented. By 1973 it became clear that N ...
... In the early days of the network there was a perceived need for users at one computer to log into another computer. The protocol that was used in the original ARPAnet, the 1822 protocol, was inadequate for this and another protocol, NCP, was devised and implemented. By 1973 it became clear that N ...
Network Models
... The layers in the TCP/IP protocol suite do not exactly match those in the OSI model. The original TCP/IP protocol suite was defined as having four layers: host-tonetwork, internet, transport, and application. However, when TCP/IP is compared to OSI, we can say that the TCP/IP protocol suite is made ...
... The layers in the TCP/IP protocol suite do not exactly match those in the OSI model. The original TCP/IP protocol suite was defined as having four layers: host-tonetwork, internet, transport, and application. However, when TCP/IP is compared to OSI, we can say that the TCP/IP protocol suite is made ...
Lecture 1 and 2
... • Protocols – set of rules that governs data communications – defines what is communicated, how it is communicated and when it is communicated • Protocol elements are: – Syntax – structure or format of the data (order of the bits) – Semantics – meaning of each section of bits – how to interpret the ...
... • Protocols – set of rules that governs data communications – defines what is communicated, how it is communicated and when it is communicated • Protocol elements are: – Syntax – structure or format of the data (order of the bits) – Semantics – meaning of each section of bits – how to interpret the ...
The Architecture of the World Wide Web Min Song IS
... Circuit-switching: Normal telephone service is based on a circuit-switching technology ...
... Circuit-switching: Normal telephone service is based on a circuit-switching technology ...
Recursive InterNetwork Architecture (RINA)

The Recursive InterNetwork Architecture (RINA) is a computer network architecture that unifies distributed computing and telecommunications. RINA's fundamental principle is that computer networking is just Inter-Process Communication or IPC. RINA reconstructs the overall structure of the Internet, forming a model that comprises a single repeating layer, the DIF (Distributed IPC Facility), which is the minimal set of components required to allow distributed IPC between application processes. RINA inherently supports mobility, multi-homing and Quality of Service without the need for extra mechanisms, provides a secure and programmable environment, motivates for a more competitive marketplace, and allows for a seamless adoption.