TSHOOT Chapter 9 - Faculty Website Directory
... answer to the following questions: What security policies have been implemented for management access to the devices? From which IP addresses or networks can the network devices be accessed? What type of authentication, authorization, and accounting is used on the network? If centralized AAA ...
... answer to the following questions: What security policies have been implemented for management access to the devices? From which IP addresses or networks can the network devices be accessed? What type of authentication, authorization, and accounting is used on the network? If centralized AAA ...
NetScreen-Hardware Security Client
... Juniper Networks NetScreen-Hardware Security Client The Juniper Networks NetScreen-Hardware Security Client, combined with NetScreen-Security Manager, is Juniper’s most cost effective security solution for the fixed telecommuter and small remote office. It can easily be deployed and managed in large ...
... Juniper Networks NetScreen-Hardware Security Client The Juniper Networks NetScreen-Hardware Security Client, combined with NetScreen-Security Manager, is Juniper’s most cost effective security solution for the fixed telecommuter and small remote office. It can easily be deployed and managed in large ...
TR50-20101006-011_ALU__TR
... Location Specific Trigger – Used to trigger M2M devices that are known by the M2M Application to be in a particular area or location. ...
... Location Specific Trigger – Used to trigger M2M devices that are known by the M2M Application to be in a particular area or location. ...
ccna4-mod1-ScalingIPAddress
... • NAT is designed to conserve IP addresses and enable networks to use ...
... • NAT is designed to conserve IP addresses and enable networks to use ...
Presentation - Constantia Fibre
... play” connectivity is attractive to licensed service providers and enables competition, greater choice, and ultimately the consumer benefits from this. Route Redundancy – Link Africa is the only company legally able to offer fibre in sewer and storm water drains. For telecommunications operators, wh ...
... play” connectivity is attractive to licensed service providers and enables competition, greater choice, and ultimately the consumer benefits from this. Route Redundancy – Link Africa is the only company legally able to offer fibre in sewer and storm water drains. For telecommunications operators, wh ...
MPLS QoS - Lyle School of Engineering
... • When IP packet traverses domain #2, it will contain two labels, encoded as a “label stack” • Higher level label used between routers C and D, which is encapsulated inside a lower level label used within Domain #2 • Operation at C ...
... • When IP packet traverses domain #2, it will contain two labels, encoded as a “label stack” • Higher level label used between routers C and D, which is encapsulated inside a lower level label used within Domain #2 • Operation at C ...
Document
... please feel free to email me at [email protected] (I really don’t mind helping.) Also, if you run across any typos or errors in my ...
... please feel free to email me at [email protected] (I really don’t mind helping.) Also, if you run across any typos or errors in my ...
Part I: Introduction - Bad Request
... Tutorial: TCP 101 r The Transmission Control Protocol (TCP) is ...
... Tutorial: TCP 101 r The Transmission Control Protocol (TCP) is ...
About the Presentations
... the state of the connection between the internal and the external computer – State table • Kept in a memory location called the cache. ...
... the state of the connection between the internal and the external computer – State table • Kept in a memory location called the cache. ...
Data types
... They can also create subnets • IFI has subnets of UiO’s address space • E.g. 129.250.69.0/24 • 129.250.69.0 can’t be used for a computer, it’s the network’s address • 129.250.69.255 can’t be used for a computer, it’s an address for all computers in the network, the broadcast address Socket example ...
... They can also create subnets • IFI has subnets of UiO’s address space • E.g. 129.250.69.0/24 • 129.250.69.0 can’t be used for a computer, it’s the network’s address • 129.250.69.255 can’t be used for a computer, it’s an address for all computers in the network, the broadcast address Socket example ...
Voice over IP
... the lack of such access. 2. When a communications provider begins selling in a particular area, it should discuss with the local PSAPs or their coordinator (as identified on the NENA website) the approach to providing access. (For example, if routing to 10-digit number, confirm the correct number wi ...
... the lack of such access. 2. When a communications provider begins selling in a particular area, it should discuss with the local PSAPs or their coordinator (as identified on the NENA website) the approach to providing access. (For example, if routing to 10-digit number, confirm the correct number wi ...
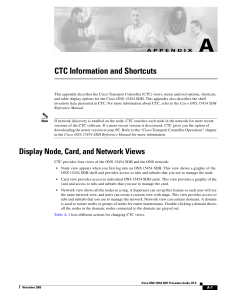
CTC Information and Shortcuts
... Network view shows all the nodes in a ring. A Superuser can set up this feature so each user will see the same network view, and users can create a custom view with maps. This view provides access to tabs and subtabs that you use to manage the network. Network view can contain domains. A domain is u ...
... Network view shows all the nodes in a ring. A Superuser can set up this feature so each user will see the same network view, and users can create a custom view with maps. This view provides access to tabs and subtabs that you use to manage the network. Network view can contain domains. A domain is u ...
IT Management System Scalability for the Enterprise
... capabilities based on their individual SolarWinds Orion instances, which are then rolled up into an MSP-level NOC view using SolarWinds Enterprise Operations Console. ...
... capabilities based on their individual SolarWinds Orion instances, which are then rolled up into an MSP-level NOC view using SolarWinds Enterprise Operations Console. ...
XM-500 XM to Ethernet Gateway Module Users Guide
... In no event will Rockwell Automation, Inc. be responsible or liable for indirect or consequential damages resulting from the use or application of this equipment. The examples and diagrams in this manual are included solely for illustrative purposes. Because of the many variables and requirements as ...
... In no event will Rockwell Automation, Inc. be responsible or liable for indirect or consequential damages resulting from the use or application of this equipment. The examples and diagrams in this manual are included solely for illustrative purposes. Because of the many variables and requirements as ...
Slide 1
... Network Management History • Network management didn’t exist in its current form until the 1980’s – From the ’40s to ’70s, networks were typically very homogeneous (proprietary-only), so network management tools were specific to that insular environment, if used at all – The advent of the PC and Ma ...
... Network Management History • Network management didn’t exist in its current form until the 1980’s – From the ’40s to ’70s, networks were typically very homogeneous (proprietary-only), so network management tools were specific to that insular environment, if used at all – The advent of the PC and Ma ...
Basics of network lab - PolyU
... able to observe name resolution occurrences using DNS servers. Introduction An IP address is a unique network layer numbering system that end systems use in order to identify and communicate with each other. It is a dotted decimal notation with four numbers ranging from 0 to 255 separated by periods ...
... able to observe name resolution occurrences using DNS servers. Introduction An IP address is a unique network layer numbering system that end systems use in order to identify and communicate with each other. It is a dotted decimal notation with four numbers ranging from 0 to 255 separated by periods ...
Linux+ Guide to Linux Certification
... MAC Frame Formats (continued) • Frame control field identifies: – Specific 802.11 protocol version – Frame type – Indicators that show WLAN configuration ...
... MAC Frame Formats (continued) • Frame control field identifies: – Specific 802.11 protocol version – Frame type – Indicators that show WLAN configuration ...
Cisco IOS Quality of Service Update
... How Is QoS Optimally Deployed? 1. Strategically define the business objectives to be achieved via QoS 2. Analyze the service-level requirements of the various traffic classes to be provisioned for 3. Design and test the QoS policies prior to productionnetwork rollout 4. Roll-out the tested QoS desi ...
... How Is QoS Optimally Deployed? 1. Strategically define the business objectives to be achieved via QoS 2. Analyze the service-level requirements of the various traffic classes to be provisioned for 3. Design and test the QoS policies prior to productionnetwork rollout 4. Roll-out the tested QoS desi ...
3.5 Reverse Address Resolution Protocol (RARP) 3.5.1 RARP concept
... • ARP only assumes that every host knows the mapping between its own hardware address and protocol address. RARP requires one or more server hosts on the network to maintain a database of mappings between hardware addresses and protocol addresses so that they will be able to reply to requests from c ...
... • ARP only assumes that every host knows the mapping between its own hardware address and protocol address. RARP requires one or more server hosts on the network to maintain a database of mappings between hardware addresses and protocol addresses so that they will be able to reply to requests from c ...
21-04-0164-01-0000-Freescale
... • It provides 3 views potentially triggering HO • The final list parameters may vary slightly based on Link & Event Triggers and, possibly, other metrics to be agreed upon (location, movement speed, rate of signal or QoS change, etc.) • Other factors are NOT shown in this table (weighting, priority, ...
... • It provides 3 views potentially triggering HO • The final list parameters may vary slightly based on Link & Event Triggers and, possibly, other metrics to be agreed upon (location, movement speed, rate of signal or QoS change, etc.) • Other factors are NOT shown in this table (weighting, priority, ...
pdf
... collected data often fails to represent the entire population of the torrent swarm [1]. In studying the effect of the torrent attacks initiated by media corporate and movie production studio, a group of people have used a crawling based technique to discover all the participating peers of a given to ...
... collected data often fails to represent the entire population of the torrent swarm [1]. In studying the effect of the torrent attacks initiated by media corporate and movie production studio, a group of people have used a crawling based technique to discover all the participating peers of a given to ...
Document
... • can be compared to TRAU function in GSM • generally located in the BSC • heart of the packet transmission in BSS network • allow the dynamic traffic allocation ...
... • can be compared to TRAU function in GSM • generally located in the BSC • heart of the packet transmission in BSS network • allow the dynamic traffic allocation ...
IPV6 Essentials - AFCEA International
... – Distinguish packets from different classes or priorities – Same functionality as type of service field in IPv4 header ...
... – Distinguish packets from different classes or priorities – Same functionality as type of service field in IPv4 header ...
Recursive InterNetwork Architecture (RINA)

The Recursive InterNetwork Architecture (RINA) is a computer network architecture that unifies distributed computing and telecommunications. RINA's fundamental principle is that computer networking is just Inter-Process Communication or IPC. RINA reconstructs the overall structure of the Internet, forming a model that comprises a single repeating layer, the DIF (Distributed IPC Facility), which is the minimal set of components required to allow distributed IPC between application processes. RINA inherently supports mobility, multi-homing and Quality of Service without the need for extra mechanisms, provides a secure and programmable environment, motivates for a more competitive marketplace, and allows for a seamless adoption.