iSCSI SAN Topologies Version 3.2 Jonghoon (Jason) Jeong
... FITNESS FOR A PARTICULAR PURPOSE. Use, copying, and distribution of any EMC software described in this publication requires an applicable software license. EMC2, EMC, and the EMC logo are registered trademarks or trademarks of EMC Corporation in the United State and other countries. All other tradem ...
... FITNESS FOR A PARTICULAR PURPOSE. Use, copying, and distribution of any EMC software described in this publication requires an applicable software license. EMC2, EMC, and the EMC logo are registered trademarks or trademarks of EMC Corporation in the United State and other countries. All other tradem ...
Deploying iSCSI Storage Solutions on Microsoft
... Microsoft Windows Server environment. These solutions include iSCSI targets based on Microsoft’s iSCSI target software and storage partner hardware, and iSCSI targets based on storage partner iSCSI target software and hardware. This paper provides an update on the state of iSCSI storage technology, ...
... Microsoft Windows Server environment. These solutions include iSCSI targets based on Microsoft’s iSCSI target software and storage partner hardware, and iSCSI targets based on storage partner iSCSI target software and hardware. This paper provides an update on the state of iSCSI storage technology, ...
Virtualization Guide - Fedora Documentation
... Press Ctrl+Alt+F1 to switch to the first virtual terminal. Press Ctrl+Alt+F7 to return to your X-Windows session. The first paragraph highlights the particular keycap to press. The second highlights two key combinations (each a set of three keycaps with each set pressed simultaneously). If source co ...
... Press Ctrl+Alt+F1 to switch to the first virtual terminal. Press Ctrl+Alt+F7 to return to your X-Windows session. The first paragraph highlights the particular keycap to press. The second highlights two key combinations (each a set of three keycaps with each set pressed simultaneously). If source co ...
The 2016 SNIA Dictionary
... Advanced Encryption Standard (AES) [Data Security] A cryptographic algorithm designated by NIST as a replacement for DES. ...
... Advanced Encryption Standard (AES) [Data Security] A cryptographic algorithm designated by NIST as a replacement for DES. ...
PT1-2 Huawei Enterprise Overview-Strategy-Org
... Board Member of DMTF, Chairman of IETE, key member of IETF & TMF ...
... Board Member of DMTF, Chairman of IETE, key member of IETF & TMF ...
Efficient Way of iSCSI based Remote Storage Service for
... As mobile device prevails, requests about various services using mobile device have increased. Specially, requests of application services that need large data space such as multimedia, game, database [1] greatly increased. However, mobile appliance has difficulty in applying various services like w ...
... As mobile device prevails, requests about various services using mobile device have increased. Specially, requests of application services that need large data space such as multimedia, game, database [1] greatly increased. However, mobile appliance has difficulty in applying various services like w ...
Cloud Management Software/Platforms
... nova-volume manages the creation, attaching and detaching of z volumes to compute instances (similar functionality to Amazon’s Elastic Block Storage). It can use volumes from a variety of providers such as iSCSI or Rados Block Device in Ceph. A new OpenStack project, Cinder, will eventually replace ...
... nova-volume manages the creation, attaching and detaching of z volumes to compute instances (similar functionality to Amazon’s Elastic Block Storage). It can use volumes from a variety of providers such as iSCSI or Rados Block Device in Ceph. A new OpenStack project, Cinder, will eventually replace ...
FAS Systems System-Level Diagnostics Guide
... Each system being tested must be on a separate network. The network interface test assigns unique static IP addresses, beginning with 172.25.150.23, to all available network interfaces on a storage system. This results in network interface ports on different storage controllers being assigned the sa ...
... Each system being tested must be on a separate network. The network interface test assigns unique static IP addresses, beginning with 172.25.150.23, to all available network interfaces on a storage system. This results in network interface ports on different storage controllers being assigned the sa ...
Performance Evaluation of Commodity iSCSI-based - ICS
... extensively for building storage area networks, many problems have emerged due to changes in underlying technologies. First, these interconnects use custom network components and thus are not able to take advantage of the steep technology curves and dropping costs of commodity, IP-based networks. Mo ...
... extensively for building storage area networks, many problems have emerged due to changes in underlying technologies. First, these interconnects use custom network components and thus are not able to take advantage of the steep technology curves and dropping costs of commodity, IP-based networks. Mo ...
01_FC_and_Host_Supported_Configurations_v1
... Locality: The degree that I/O is confined to a particular switch or segment of a fabric. If two devices that need to communicate with each other are located on the same switch or segment, then these two devices are said to have high locality. If these same devices are located on different switches ...
... Locality: The degree that I/O is confined to a particular switch or segment of a fabric. If two devices that need to communicate with each other are located on the same switch or segment, then these two devices are said to have high locality. If these same devices are located on different switches ...
Introduction Guide to the IBM Elastic Storage Server (ESS)
... manner serve as an endorsement of those websites. The materials at those websites are not part of the materials for this IBM product and use of those websites is at your own risk. IBM may use or distribute any of the information you supply in any way it believes appropriate without incurring any obl ...
... manner serve as an endorsement of those websites. The materials at those websites are not part of the materials for this IBM product and use of those websites is at your own risk. IBM may use or distribute any of the information you supply in any way it believes appropriate without incurring any obl ...
hp-storage- sales - training
... – Industry-standard building blocks: Intel processors, SATA/SAS drives, and SAS interconnects – It’s Windows, so it integrates seamlessly into your existing Windows environment, runs antivirus/backup on the box, and has a familiar management look and feel – Optional data services software integrates ...
... – Industry-standard building blocks: Intel processors, SATA/SAS drives, and SAS interconnects – It’s Windows, so it integrates seamlessly into your existing Windows environment, runs antivirus/backup on the box, and has a familiar management look and feel – Optional data services software integrates ...
VMWare 101 - WordPress.com
... – Traditionally, if you had some number of ESX hosts in a cluster, each could be overloaded with VM’s. – DRS looks at each ESX host in the cluster, and then VMotion will move VM’s around the cluster in order to balance out performance of each ESX host. This can be configured in multiple ways, but VM ...
... – Traditionally, if you had some number of ESX hosts in a cluster, each could be overloaded with VM’s. – DRS looks at each ESX host in the cluster, and then VMotion will move VM’s around the cluster in order to balance out performance of each ESX host. This can be configured in multiple ways, but VM ...
PRAISE FOR IP STORAGE NETWORKING: STRAIGHT
... Straight to the Core goes beyond technical descriptions to the business reasons and justifications for implementing a storage architecture.” —Doug Ingraham, Senior Manager of Product Management in Cisco's Storage Technology Group “As today's enterprise continues to become more data-intensive, custom ...
... Straight to the Core goes beyond technical descriptions to the business reasons and justifications for implementing a storage architecture.” —Doug Ingraham, Senior Manager of Product Management in Cisco's Storage Technology Group “As today's enterprise continues to become more data-intensive, custom ...
Storage Fundamentals 101
... With initiatives such as server consolidation and e−business, the need for SANs will increase, making the importance of storage in the network greater. ...
... With initiatives such as server consolidation and e−business, the need for SANs will increase, making the importance of storage in the network greater. ...
XSAN - MOVES Institute
... • “serverless backups”--just send command to copy blocks from disk A to disk B. Snapshots easier, shortened backup windows-you can have a SAN particpant handle moving a volume to tape ...
... • “serverless backups”--just send command to copy blocks from disk A to disk B. Snapshots easier, shortened backup windows-you can have a SAN particpant handle moving a volume to tape ...
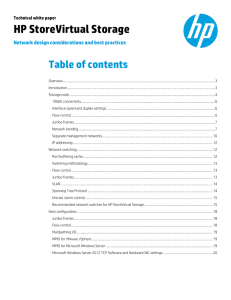
HP StoreVirtual Storage: Network design considerations and best
... servers. HP StoreVirtual uses a distributed scale-out architecture and clusters two or more storage nodes into a flexible pool of storage, a storage cluster. The iSCSI protocol enables the block level data transfers over Ethernet between an initiator (application server) and a target (storage system ...
... servers. HP StoreVirtual uses a distributed scale-out architecture and clusters two or more storage nodes into a flexible pool of storage, a storage cluster. The iSCSI protocol enables the block level data transfers over Ethernet between an initiator (application server) and a target (storage system ...
Is Your Storage Area Network Secure? An Overview
... security breach might occur and to include these into consideration when designing SAN security solutions. Ability to identify the points of vulnerability and implement a reliable security solution is the key to securing a SAN fabric infrastructure.Ref#12). Clearly, physical isolation of the SAN is ...
... security breach might occur and to include these into consideration when designing SAN security solutions. Ability to identify the points of vulnerability and implement a reliable security solution is the key to securing a SAN fabric infrastructure.Ref#12). Clearly, physical isolation of the SAN is ...
User Manual v.4
... that can be directly connected to the network without a server or host. It is the perfect storage and networking solution for the home, home office, workgroup and small / medium size businesses. NetDisk™ provides a cost-effective network / storage solution: an external Hard Disk Drive to store all o ...
... that can be directly connected to the network without a server or host. It is the perfect storage and networking solution for the home, home office, workgroup and small / medium size businesses. NetDisk™ provides a cost-effective network / storage solution: an external Hard Disk Drive to store all o ...
DCNA - Cisco Systems, Inc
... Virtualization is no longer just an early adopter phenomenon.2 Orchestrated Dynamic Static server, Virtualization storage, network Virtualization ...
... Virtualization is no longer just an early adopter phenomenon.2 Orchestrated Dynamic Static server, Virtualization storage, network Virtualization ...
Insert Module Title Here
... Locally attached storage – Internal or external storage disks or arrays attached to the host through a direct connection Fibre Channel – A high-speed SCSI transport protocol used for storage area networking (SAN): Fibre Channel switches interconnect multiple nodes to form the “fabric” in a Fibre C ...
... Locally attached storage – Internal or external storage disks or arrays attached to the host through a direct connection Fibre Channel – A high-speed SCSI transport protocol used for storage area networking (SAN): Fibre Channel switches interconnect multiple nodes to form the “fabric” in a Fibre C ...
Best Practices for Building a Virtualized SPARC Computing
... members of the server pool. Guests’ root disks must be on shared LUNs using either Fibre Channel (FC) or iSCSI SAN storage. In addition, Enterprise Manager Ops Center requires the use of a small NFS shared library to store guest metadata, which also must be accessible to all the members of the serve ...
... members of the server pool. Guests’ root disks must be on shared LUNs using either Fibre Channel (FC) or iSCSI SAN storage. In addition, Enterprise Manager Ops Center requires the use of a small NFS shared library to store guest metadata, which also must be accessible to all the members of the serve ...
Data Sheet: QLogic FastLinQ QL4521x Series
... © 2016-2017 QLogic Corporation. QLogic Corporation is a wholly owned subsidiary of Cavium, Inc. All rights reserved worldwide. QLogic, the QLogic logo, VMflex, QConvergeConsole, and FastLinQ are trademarks or registered trademarks of QLogic Corporation. Linux is a registered trademark of Linus Torva ...
... © 2016-2017 QLogic Corporation. QLogic Corporation is a wholly owned subsidiary of Cavium, Inc. All rights reserved worldwide. QLogic, the QLogic logo, VMflex, QConvergeConsole, and FastLinQ are trademarks or registered trademarks of QLogic Corporation. Linux is a registered trademark of Linus Torva ...