Wireless MESH Networks
... To reach higher levels of redundancy, you may add an additional line of fiber next to an existing one. In a mesh network, the degree of redundancy is essentially a function of node density. A network can be deliberately over-designed for reliability simply by adding extra nodes, so each device has t ...
... To reach higher levels of redundancy, you may add an additional line of fiber next to an existing one. In a mesh network, the degree of redundancy is essentially a function of node density. A network can be deliberately over-designed for reliability simply by adding extra nodes, so each device has t ...
4G Neighborhood Area Networks
... A View of Small Cell vs. Large Cell Wireless Capital R = 3 km r = 1000’ (308 m), ~20% overlap by area There are ~125 NAN cells per 3 km MAN cell The Challenge: MANs have constructed economic models that meet current needs for maximum user throughput, teledensity, and cell coverage area. These models ...
... A View of Small Cell vs. Large Cell Wireless Capital R = 3 km r = 1000’ (308 m), ~20% overlap by area There are ~125 NAN cells per 3 km MAN cell The Challenge: MANs have constructed economic models that meet current needs for maximum user throughput, teledensity, and cell coverage area. These models ...
copyrighted material - Beck-Shop
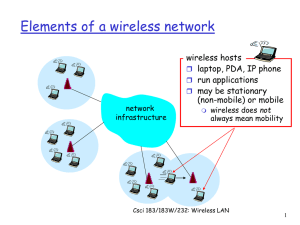
... A campus area network (CAN) includes a set of interconnected LANs, is basically a smaller version of a wide area network (WAN) within an office or school campus, and is usually within a limited geographical area. Each building within the campus would have a separate LAN, and the LANs are often conne ...
... A campus area network (CAN) includes a set of interconnected LANs, is basically a smaller version of a wide area network (WAN) within an office or school campus, and is usually within a limited geographical area. Each building within the campus would have a separate LAN, and the LANs are often conne ...
Understanding Computers, Chapter 7
... – Bridge: Usually connects wired LANs – Router: Connects networks and plans path (routes traffic) • Can be wired or wireless ...
... – Bridge: Usually connects wired LANs – Router: Connects networks and plans path (routes traffic) • Can be wired or wireless ...
Architecting a Robust Manufacturing Network for the Internet
... CIOs could oversee policies, which provided a reasonable level of control over who and what approved devices were connected to their networks. With the proliferation of smartphones and tablets, CIOs have needed to administer “bring your own device” (BYOD) policies to enable greater productivity. Add ...
... CIOs could oversee policies, which provided a reasonable level of control over who and what approved devices were connected to their networks. With the proliferation of smartphones and tablets, CIOs have needed to administer “bring your own device” (BYOD) policies to enable greater productivity. Add ...
Document
... • Wireless link is manually set at cost of 96 • Traffic from WPOP1 to WPOP2 will take the wireless PTP link if it’s available, else it will use T1s • Traffic from WPOP1 to Internet goes via the local T1, else via the wireless PTP link to WPOP2 and then via WPOP2’s T1 ...
... • Wireless link is manually set at cost of 96 • Traffic from WPOP1 to WPOP2 will take the wireless PTP link if it’s available, else it will use T1s • Traffic from WPOP1 to Internet goes via the local T1, else via the wireless PTP link to WPOP2 and then via WPOP2’s T1 ...
Unified Services Routers - D-Link
... As a responsible member of the global community, D-Link is devoted to providing ecofriendly products. D-Link Green Wi-Fi and D-Link Green Ethernet features save power and help cut energy costs. The D-Link Green WLAN Scheduler shuts down your wireless network automatically according to a schedule you ...
... As a responsible member of the global community, D-Link is devoted to providing ecofriendly products. D-Link Green Wi-Fi and D-Link Green Ethernet features save power and help cut energy costs. The D-Link Green WLAN Scheduler shuts down your wireless network automatically according to a schedule you ...
Hacking Wireless Networks
... interoperability of products that use WLAN standards. The consortium runs a certification program and recognizes products, which are implementing WLAN standards, as Wi-Fi certified products. FCC: Federal Communications Commission (FCC) is an independent US government agency. It regulates interstate ...
... interoperability of products that use WLAN standards. The consortium runs a certification program and recognizes products, which are implementing WLAN standards, as Wi-Fi certified products. FCC: Federal Communications Commission (FCC) is an independent US government agency. It regulates interstate ...
YN013853859
... synonymously with VoIP are IP telephony, Internet telephony, voice over broadband (VoBB), broadband telephony, and broadband phone. Internet telephony refers to communications services— Voice, fax, SMS, and/or voice-messaging applications—that are transported via the Internet, rather than the public ...
... synonymously with VoIP are IP telephony, Internet telephony, voice over broadband (VoBB), broadband telephony, and broadband phone. Internet telephony refers to communications services— Voice, fax, SMS, and/or voice-messaging applications—that are transported via the Internet, rather than the public ...
4 Threats and Vulnerabilities Compared to Wired LANs
... authentication mechanisms crucial for the security of the wireless LANs. In all cases the both parties of the transmission should be able to authenticate each others. The wireless LAN could be used as a launch pad to the transitive trust attack. If the attacker can fool our wireless LAN to trust the ...
... authentication mechanisms crucial for the security of the wireless LANs. In all cases the both parties of the transmission should be able to authenticate each others. The wireless LAN could be used as a launch pad to the transitive trust attack. If the attacker can fool our wireless LAN to trust the ...
RTX Telecom A/S
... • Rapid deployment where infrastructure is limited • Preconfigured ’Out-of-the box’ solution for dedicated requirements • Multiple interfaces to public network or PBX • Multiple systems can remotely be connected together via central Switch • Several applications e.g. systems for small communities, h ...
... • Rapid deployment where infrastructure is limited • Preconfigured ’Out-of-the box’ solution for dedicated requirements • Multiple interfaces to public network or PBX • Multiple systems can remotely be connected together via central Switch • Several applications e.g. systems for small communities, h ...
Exploration_LAN_Switching_Chapter7
... coverage area, if possible. Position access points in locations where users are expected to be. For example, conference rooms are typically a better location for access points than a hallway. ...
... coverage area, if possible. Position access points in locations where users are expected to be. For example, conference rooms are typically a better location for access points than a hallway. ...
Document
... High speed motion with real-time handoff is required for data connectivity at vehicular speeds. Real time handoff enables future applications such as Voice over IP and real time mobile video. Data rate drops as speed increases ...
... High speed motion with real-time handoff is required for data connectivity at vehicular speeds. Real time handoff enables future applications such as Voice over IP and real time mobile video. Data rate drops as speed increases ...
ユビキタスITの展望と課題
... ・[Standardization and development in Europe and Japan in mid 90s late 90s in Europe] Europe - HIPERLAN/HIPERLAN2 Japan - HiSWAN(AWA/MMAC) ・Market has been growing from IEEE802.11b, 11a to 11g, and 11n in the future. ・In the investigation of interworking of 3G(IMT-2000) and wireless LAN which started ...
... ・[Standardization and development in Europe and Japan in mid 90s late 90s in Europe] Europe - HIPERLAN/HIPERLAN2 Japan - HiSWAN(AWA/MMAC) ・Market has been growing from IEEE802.11b, 11a to 11g, and 11n in the future. ・In the investigation of interworking of 3G(IMT-2000) and wireless LAN which started ...
Networking Chapter 17
... • Use radio waves or infrared light – Useful in places where cables difficult to install ...
... • Use radio waves or infrared light – Useful in places where cables difficult to install ...
Coverage or Capacity—Making the Best Use of 802.11n
... not the solution for high capacity deployments. In fact, cranking up the power creates problems for sites that require high throughput—the most serious being adjacent channel interference, which increases exponentially as power output rises. An access point turned up to full power can pollute the tr ...
... not the solution for high capacity deployments. In fact, cranking up the power creates problems for sites that require high throughput—the most serious being adjacent channel interference, which increases exponentially as power output rises. An access point turned up to full power can pollute the tr ...
How To Configure a Wireless Portables Data Connection
... OS/2, or Win/NT PC; it doesn’t matter what it is. I promise, we can connect a wireless mobile device to it. Also, it usually doesn’t matter what kind of database the server is running. We’ll talk about the database later. Further, it doesn’t matter if the server is 10 feet or 2,000 miles away. We ca ...
... OS/2, or Win/NT PC; it doesn’t matter what it is. I promise, we can connect a wireless mobile device to it. Also, it usually doesn’t matter what kind of database the server is running. We’ll talk about the database later. Further, it doesn’t matter if the server is 10 feet or 2,000 miles away. We ca ...
Actiontec MI424WR Revision E Wireless Broadband Router
... be first rate, and the Wireless Broadband Router doesn’t disappoint. The router ships with wireless encryption using WEP turned on by default and supports WPA and WPA2 encryptions. The router offers enterprise-level security, including a fully customizable firewall with Stateful Packet Inspection, d ...
... be first rate, and the Wireless Broadband Router doesn’t disappoint. The router ships with wireless encryption using WEP turned on by default and supports WPA and WPA2 encryptions. The router offers enterprise-level security, including a fully customizable firewall with Stateful Packet Inspection, d ...
In this project, we plan to establish a complete communications loop:
... it worthwhile implementing in a wireless situation. Solution such as Indirect TCP (ITCP) [8] suggests that a base station actually maintains two separate types of connections, between the wireless connection on one side, and the wired connection on the other, and two separate protocols on these conn ...
... it worthwhile implementing in a wireless situation. Solution such as Indirect TCP (ITCP) [8] suggests that a base station actually maintains two separate types of connections, between the wireless connection on one side, and the wired connection on the other, and two separate protocols on these conn ...
Solution proposal for self-organising network use case: Load/Time
... • The application of autonomic self-management functionalities would allow for • A reduced need for human control and intervention • The capability of adaptation in presence of new nodes (self-configuration) • The possibility of increasing performances, by optimizing network parameters (selfoptimiza ...
... • The application of autonomic self-management functionalities would allow for • A reduced need for human control and intervention • The capability of adaptation in presence of new nodes (self-configuration) • The possibility of increasing performances, by optimizing network parameters (selfoptimiza ...
Introduction to Computer Networking - PDST
... With switching, each connection gets "dedicated bandwidth" and can operate at full speed. In contrast, a hub shares bandwidth across multiple connections such that activity from one PC or server can slow down the effective speed of other connections on the hub. ...
... With switching, each connection gets "dedicated bandwidth" and can operate at full speed. In contrast, a hub shares bandwidth across multiple connections such that activity from one PC or server can slow down the effective speed of other connections on the hub. ...
What is wireless networking?
... session participants. Such a description is then used to negotiate the characteristics of the session so that all the devices can participate (negotiation of codecs used to encode media so all participants will be able to decode it). SIP is based on HTTP protocol. SIP is used to carry the descriptio ...
... session participants. Such a description is then used to negotiate the characteristics of the session so that all the devices can participate (negotiation of codecs used to encode media so all participants will be able to decode it). SIP is based on HTTP protocol. SIP is used to carry the descriptio ...
Wi-Fi
Wi-Fi (or WiFi) is a local area wireless computer networking technology that allows electronic devices to network, mainly using the 2.4 gigahertz (12 cm) UHF and 5 gigahertz (6 cm) SHF ISM radio bands.The Wi-Fi Alliance defines Wi-Fi as any ""wireless local area network"" (WLAN) product based on the Institute of Electrical and Electronics Engineers' (IEEE) 802.11 standards. However, the term ""Wi-Fi"" is used in general English as a synonym for ""WLAN"" since most modern WLANs are based on these standards. ""Wi-Fi"" is a trademark of the Wi-Fi Alliance. The ""Wi-Fi Certified"" trademark can only be used by Wi-Fi products that successfully complete Wi-Fi Alliance interoperability certification testing.Many devices can use Wi-Fi, e.g. personal computers, video-game consoles, smartphones, digital cameras, tablet computers and digital audio players. These can connect to a network resource such as the Internet via a wireless network access point. Such an access point (or hotspot) has a range of about 20 meters (66 feet) indoors and a greater range outdoors. Hotspot coverage can be as small as a single room with walls that block radio waves, or as large as many square kilometres achieved by using multiple overlapping access points. Wi-Fi can be less secure than wired connections, such as Ethernet, precisely because an intruder does not need a physical connection. Web pages that use TLS are secure, but unencrypted internet access can easily be detected by intruders. Because of this, Wi-Fi has adopted various encryption technologies. The early encryption WEP proved easy to break. Higher quality protocols (WPA, WPA2) were added later. An optional feature added in 2007, called Wi-Fi Protected Setup (WPS), had a serious flaw that allowed an attacker to recover the router's password. The Wi-Fi Alliance has since updated its test plan and certification program to ensure all newly certified devices resist attacks.