Communication and Network - International University of Japan
... Suck down all available resources on the network, resulting in network congestion ...
... Suck down all available resources on the network, resulting in network congestion ...
01_tcom5272_intro
... shared printers through a Microsoft-based network, which are made accessible, in part, through the redirector. Your network needs to have at least one workgroup (or domain) of computers, shared folders, and shared printers to fully view the work of the redirector. ...
... shared printers through a Microsoft-based network, which are made accessible, in part, through the redirector. Your network needs to have at least one workgroup (or domain) of computers, shared folders, and shared printers to fully view the work of the redirector. ...
Interconnect Networks - Brock Computer Science
... A generalized star interconnection network has the property that for a given integer N, we have exactly N! processors. Each processor is labeled with the permutation to which it corresponds. Two processors Pi and Pj are connected if the label I can be transformed into label j by switching the first ...
... A generalized star interconnection network has the property that for a given integer N, we have exactly N! processors. Each processor is labeled with the permutation to which it corresponds. Two processors Pi and Pj are connected if the label I can be transformed into label j by switching the first ...
An Overview of MANET: History, Challenges and Applications
... Opposed to the infrastructure wireless networks where each user directly communicates with an access point or base station, a mobile ad hoc network, or MANET is a kind of wireless ad hoc network [1]. It is a self configuring network of mobile routers connected by wireless links with no access point. ...
... Opposed to the infrastructure wireless networks where each user directly communicates with an access point or base station, a mobile ad hoc network, or MANET is a kind of wireless ad hoc network [1]. It is a self configuring network of mobile routers connected by wireless links with no access point. ...
Powerpoint - Chapter 3
... new frame using the data-link layer protocol of the outgoing network. Routing tables can be created manually by a network administrator or automatically by a routing protocol. ...
... new frame using the data-link layer protocol of the outgoing network. Routing tables can be created manually by a network administrator or automatically by a routing protocol. ...
Secure Threshold Sensitive Energy Efficient Sensor Network Protocol
... tell that nodes in the Sec-TEEN tend to consume their energy at a slower rate if compared to the SecLEACH nodes. Consequently, as can be seen from the Fig. 3, a WSN of 100 nodes using Sec-TEEN have consumed all of their energy at time 246. However, the nodes have consumed the energy at time 224 for ...
... tell that nodes in the Sec-TEEN tend to consume their energy at a slower rate if compared to the SecLEACH nodes. Consequently, as can be seen from the Fig. 3, a WSN of 100 nodes using Sec-TEEN have consumed all of their energy at time 246. However, the nodes have consumed the energy at time 224 for ...
2007z
... The organization and communication activities among alumni was worked out for about six weeks by using the rule as described in the previous section. The yielded topology of the network is then becoming an interesting part of our discussion. It is interesting that the yielded graph ...
... The organization and communication activities among alumni was worked out for about six weeks by using the rule as described in the previous section. The yielded topology of the network is then becoming an interesting part of our discussion. It is interesting that the yielded graph ...
Network Topologies
... stronger and can cover larger area than some topologies, No hubs / switches required to connect the devices together, If a cable stops working easy to find out where, Can add more computers but need to break the ring and be placed in-between two computers which can be a hassle, Quite a bit of cable ...
... stronger and can cover larger area than some topologies, No hubs / switches required to connect the devices together, If a cable stops working easy to find out where, Can add more computers but need to break the ring and be placed in-between two computers which can be a hassle, Quite a bit of cable ...
FMAudit Technical White Paper Product Line Overview
... the exchange of information between network devices; extracting data from the Management Information Base (MIB) and other locations within the print device. The MIB is basically an internal database that all network connected devices have, that contains information like the model name, toner levels ...
... the exchange of information between network devices; extracting data from the Management Information Base (MIB) and other locations within the print device. The MIB is basically an internal database that all network connected devices have, that contains information like the model name, toner levels ...
Embedded Networked Sensing Systems: motivations and challenges
... Channel models • Simplistic circular channel models can be very deceiving so experimentation and emulation are critical ...
... Channel models • Simplistic circular channel models can be very deceiving so experimentation and emulation are critical ...
IRIS Project
... • The system is broken into a vertical hierarchy of protocols • The service provided by one layer is based solely on the service provided by layer below ...
... • The system is broken into a vertical hierarchy of protocols • The service provided by one layer is based solely on the service provided by layer below ...
Network Topologies
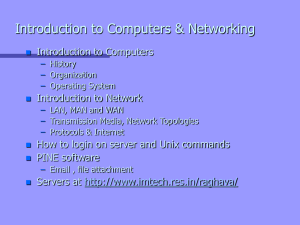
... Introduction to Network – LAN, MAN and WAN – Transmission Media, Network Topologies – Protocols & Internet ...
... Introduction to Network – LAN, MAN and WAN – Transmission Media, Network Topologies – Protocols & Internet ...
1-up PPT
... • The system is broken into a vertical hierarchy of protocols • The service provided by one layer is based solely on the service provided by layer below ...
... • The system is broken into a vertical hierarchy of protocols • The service provided by one layer is based solely on the service provided by layer below ...
ch01 - Montana State University
... Reproduction or translation of this work beyond that named in Section 117 of the United States Copyright Act without the express written consent of the copyright owner is unlawful. Requests for further information should be addressed to the Permissions Department, John Wiley & Sons, Inc. Adopters of ...
... Reproduction or translation of this work beyond that named in Section 117 of the United States Copyright Act without the express written consent of the copyright owner is unlawful. Requests for further information should be addressed to the Permissions Department, John Wiley & Sons, Inc. Adopters of ...
Week 5 Link Layer & Local Area Networking
... Asynchronous Transfer Mode is a cell relay network protocol which encodes data traffic into small fixed sized (53 byte) cells instead of variable sized packets as in packet-switched networks (such as IP or Ethernet) ATM was intended to provide a single unified networking standard that could supp ...
... Asynchronous Transfer Mode is a cell relay network protocol which encodes data traffic into small fixed sized (53 byte) cells instead of variable sized packets as in packet-switched networks (such as IP or Ethernet) ATM was intended to provide a single unified networking standard that could supp ...
arpn-jeas-icstartemplate
... opportunistically. One solution to achieve the spectrum efficiency is by using less-spectrum in backbone, backhaul and access connections. The recent development of interconnection system in mobile communication has been able to provide the connection between the Base Station Subsystem (BSS) and mob ...
... opportunistically. One solution to achieve the spectrum efficiency is by using less-spectrum in backbone, backhaul and access connections. The recent development of interconnection system in mobile communication has been able to provide the connection between the Base Station Subsystem (BSS) and mob ...
International Telecommunication Union
... -Problems with current Internet (routing failures, scalability, insecurity, mobility, QoS, lack of efficient media distribution, packet switching, …) - Design goals and high level requirements: • Scalability (routing architecture, multi-homing) • Naming & addressing scheme (separation of user identi ...
... -Problems with current Internet (routing failures, scalability, insecurity, mobility, QoS, lack of efficient media distribution, packet switching, …) - Design goals and high level requirements: • Scalability (routing architecture, multi-homing) • Naming & addressing scheme (separation of user identi ...
Document - Oman College of Management & Technology
... Header includes addressing and other fields. ...
... Header includes addressing and other fields. ...
tr-5a series - Baltic Networks
... maximum application bandwidth at the lowest total cost of ownership. The EN404 is a wireless mesh router specifically designed for outdoor applications. The dual-radio EN404 serves as a WiFi access point with a dedicated 802.11b/g radio, an intra-network repeater and router with a dedicated 802.11a ...
... maximum application bandwidth at the lowest total cost of ownership. The EN404 is a wireless mesh router specifically designed for outdoor applications. The dual-radio EN404 serves as a WiFi access point with a dedicated 802.11b/g radio, an intra-network repeater and router with a dedicated 802.11a ...
1.1 Chapter 1 Introduction Data Communication Objectives
... A network is a set of devices (often referred to as nodes) connected by communication links. A node can be a computer, printer, or any other device capable of sending and/or receiving data generated by other nodes on the network. A link can be a cable, air, optical fiber, or any medium which can tra ...
... A network is a set of devices (often referred to as nodes) connected by communication links. A node can be a computer, printer, or any other device capable of sending and/or receiving data generated by other nodes on the network. A link can be a cable, air, optical fiber, or any medium which can tra ...
Document
... A computer network is a communication system Connects two or more computers Allows information exchange ...
... A computer network is a communication system Connects two or more computers Allows information exchange ...
lecture_1
... Network Programming • Network allows arbitrary applications to communicate • Programmer does not need to understand network technologies • Network facilities accessed through an Application Program Interface ...
... Network Programming • Network allows arbitrary applications to communicate • Programmer does not need to understand network technologies • Network facilities accessed through an Application Program Interface ...
Network Security - University of Northampton
... Router Considerations The router is the very first line of defense. It provides packet routing, It can also be configured to block or filter the forwarding of packet types that are known to be vulnerable or used maliciously, such as ICMP ...
... Router Considerations The router is the very first line of defense. It provides packet routing, It can also be configured to block or filter the forwarding of packet types that are known to be vulnerable or used maliciously, such as ICMP ...
Networks Now and Future
... Global networking: TCP/IP and ATM • Internetworking: connecting one network to another to get a “network of networks” • TCP/IP, aka “The Internet”, is based on bouncing “packets” around the world, each one finding its’ own route from one place to another. Rather random, but simple. • ATM, asynchron ...
... Global networking: TCP/IP and ATM • Internetworking: connecting one network to another to get a “network of networks” • TCP/IP, aka “The Internet”, is based on bouncing “packets” around the world, each one finding its’ own route from one place to another. Rather random, but simple. • ATM, asynchron ...