IOSR Journal of Electrical and Electronics Engineering (IOSR-JEEE)
... There is an important role for information theory in the development of new wireless networked systems. Wireless networking is a very different and significantly more complex field compared to point-topoint wireless systems that have been addressed so successfully by information theorists. Whereas o ...
... There is an important role for information theory in the development of new wireless networked systems. Wireless networking is a very different and significantly more complex field compared to point-topoint wireless systems that have been addressed so successfully by information theorists. Whereas o ...
Elements of a Small PC Network
... • Required if wires are run through air conditioning ducts • Not needed in false ceilings ...
... • Required if wires are run through air conditioning ducts • Not needed in false ceilings ...
Throughput Scaling in Wideband Sensory Relay Networks
... I) From model abstraction to problem formulation: How to model different functionality modules and the interdependence? - Often times disparate methods are used for cyber systems and physical systems, e.g., differential equations for power systems whereas graph models for communication networks - In ...
... I) From model abstraction to problem formulation: How to model different functionality modules and the interdependence? - Often times disparate methods are used for cyber systems and physical systems, e.g., differential equations for power systems whereas graph models for communication networks - In ...
SMC1255TX / SMC1255TX/LP www.smc.com
... network. SMC Etherguard, the personal firewall application, records both the IP address of individuals attempting to access your network and previously visited websites. In addition, this software will also block Trojan Horses from destroying your files. The WinEtool Sniffer application monitors and ...
... network. SMC Etherguard, the personal firewall application, records both the IP address of individuals attempting to access your network and previously visited websites. In addition, this software will also block Trojan Horses from destroying your files. The WinEtool Sniffer application monitors and ...
CSE 461 - University of Washington
... • Designates subnets within the IP address space • IP address of subnet followed by the number of bits that are used for routing (32 minus the number of bits free for subnet addressing) • Note: the first address in a subnet is used as the subnet address (seldom actually used), and the last address i ...
... • Designates subnets within the IP address space • IP address of subnet followed by the number of bits that are used for routing (32 minus the number of bits free for subnet addressing) • Note: the first address in a subnet is used as the subnet address (seldom actually used), and the last address i ...
Distributed Image Mining using Small World Indexes
... This value was then averaged over N for different values of F. The retrieval agent’s behavior is illustrated in Figure 4. Therein, search path lengths are compared to a linear search which would require ...
... This value was then averaged over N for different values of F. The retrieval agent’s behavior is illustrated in Figure 4. Therein, search path lengths are compared to a linear search which would require ...
csci4220-week01 - Computer Science at RPI
... between layers (on the same endpoint) Peer-to-peer protocols describe communication between two endpoints at the same layer Q ...
... between layers (on the same endpoint) Peer-to-peer protocols describe communication between two endpoints at the same layer Q ...
EE 122: Computer Networks
... want to diagnose problems but IP hides federation want to block unwanted traffic but the network doesn’t authenticate can’t optimize for different applications or customers complex and buggy protocols upgrading protocols is deeply painful ...
... want to diagnose problems but IP hides federation want to block unwanted traffic but the network doesn’t authenticate can’t optimize for different applications or customers complex and buggy protocols upgrading protocols is deeply painful ...
Quality of Service (QoS)
... • To obtain the required QoS from a network, end-systems need to signal the network the desired QoS as well as the anticipated offered traffic profile • This has been a fundamental part of various connection-oriented networks • For connectionless networks, this is relatively new ...
... • To obtain the required QoS from a network, end-systems need to signal the network the desired QoS as well as the anticipated offered traffic profile • This has been a fundamental part of various connection-oriented networks • For connectionless networks, this is relatively new ...
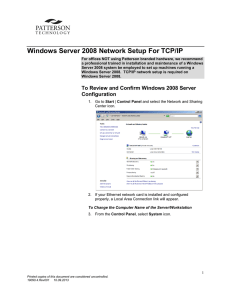
Windows Server 2008 Network Setup For TCP/IP
... 4. On the right-hand side of the screen, select Change Settings. 5. To change the Computer Name or Workgroup name, select Change. 6. Click in the Computer Name box to edit the computer name. 7. Select the Workgroup radio button. Click in the Workgroup box to edit the Workgroup name. 8. Select OK. Y ...
... 4. On the right-hand side of the screen, select Change Settings. 5. To change the Computer Name or Workgroup name, select Change. 6. Click in the Computer Name box to edit the computer name. 7. Select the Workgroup radio button. Click in the Workgroup box to edit the Workgroup name. 8. Select OK. Y ...
Creation of anti DDOS network in Moldova
... - Users can access every overlay node even one of the nodes is under attack. -Every node have possibility to identify legacy users - request of the user that passed the CAPTHCA are processed as secured. - There are possibility to increase number of nodes in your network. - One overlay network can of ...
... - Users can access every overlay node even one of the nodes is under attack. -Every node have possibility to identify legacy users - request of the user that passed the CAPTHCA are processed as secured. - There are possibility to increase number of nodes in your network. - One overlay network can of ...
Module 1 - Home - KSU Faculty Member websites
... had been created with a variety of different hardware and software implementations. • Each company that created network hardware and software used its own company standards. • These individual standards were developed because of competition with other companies. • Consequently, many of the new netwo ...
... had been created with a variety of different hardware and software implementations. • Each company that created network hardware and software used its own company standards. • These individual standards were developed because of competition with other companies. • Consequently, many of the new netwo ...
Physical Layer Repeater
... transceiver. The FR-50 receives LONTALK™ packets from one channel segment and then passes them immediately to another channel segment. A repeater does not perform any routing, switching or filtering of LONTALK packets and will not increase the bandwidth of a network segment by reducing unnecessary n ...
... transceiver. The FR-50 receives LONTALK™ packets from one channel segment and then passes them immediately to another channel segment. A repeater does not perform any routing, switching or filtering of LONTALK packets and will not increase the bandwidth of a network segment by reducing unnecessary n ...
Multi Node Label Routing Protocol
... • Convergence Time is equal to the number of hello times required to determine a link failure plus the time to update the affected nodes’ neighbor tables (2 second hello times, 3 hellos for link failure) ...
... • Convergence Time is equal to the number of hello times required to determine a link failure plus the time to update the affected nodes’ neighbor tables (2 second hello times, 3 hellos for link failure) ...
SkyMesh™ 1/2/4200 Series Satellite Router Terminal
... of available transponder bandwidth. Network structure can be programmed to support mul ple topologies simulta‐ neously in a single network, and can be changed from one topology to another on the fly. SkyMesh™ smart terminals deliver all user traffic via single‐hop link to their final des na ons. SkyMe ...
... of available transponder bandwidth. Network structure can be programmed to support mul ple topologies simulta‐ neously in a single network, and can be changed from one topology to another on the fly. SkyMesh™ smart terminals deliver all user traffic via single‐hop link to their final des na ons. SkyMe ...
Quality Of Service
... Quality Of Service Why Is It Necessary? “Becauszzzz wit_o_t it _sers w__l be unha_py!” PSTN has set the bar - VoIP as a replacement technology must offer the same quality experience ...
... Quality Of Service Why Is It Necessary? “Becauszzzz wit_o_t it _sers w__l be unha_py!” PSTN has set the bar - VoIP as a replacement technology must offer the same quality experience ...
Lec_1: Syllabus
... A large number of resources exist on the Internet. These include book chapters, academic papers, FAQs, online workshops, programs and other relevant material from academic institutes around the world. ...
... A large number of resources exist on the Internet. These include book chapters, academic papers, FAQs, online workshops, programs and other relevant material from academic institutes around the world. ...
CiscoS3C5 - YSU Computer Science & Information Systems
... • Holddown – used when router learns that a network is a greater distance than previously known or a network is down – advertisements from other routers are ignored – helps avoid routing loop • Holddown period is greater than period of time necessary to update entire network ...
... • Holddown – used when router learns that a network is a greater distance than previously known or a network is down – advertisements from other routers are ignored – helps avoid routing loop • Holddown period is greater than period of time necessary to update entire network ...
Information Technology Management
... The platform/structural organizer of value network Portable programming languages Software/Data can interacts each other smartly under a delegation world Distributed objects and standards ...
... The platform/structural organizer of value network Portable programming languages Software/Data can interacts each other smartly under a delegation world Distributed objects and standards ...
Networking
... The purpose of this basic IP technology training is to explain video over an IP network. This training describes how video can be used on a network using IP protocol and enables individuals to understand how the IP network can respond to today’s increasing need of sharing video at any time and from ...
... The purpose of this basic IP technology training is to explain video over an IP network. This training describes how video can be used on a network using IP protocol and enables individuals to understand how the IP network can respond to today’s increasing need of sharing video at any time and from ...
Chapter 5 - YSU Computer Science & Information Systems
... • Bits’ are actually packets containing many bits • Result of too much network traffic (the more nodes the more work being done the more traffic) • Domain – area within network where data packets originated and collided • All of layer 1 connections are part of collision domain ...
... • Bits’ are actually packets containing many bits • Result of too much network traffic (the more nodes the more work being done the more traffic) • Domain – area within network where data packets originated and collided • All of layer 1 connections are part of collision domain ...