Multimedia Data Streaming - Indian Institute of Science
... Receiver heterogeneity means that receivers have different or even varying latency requirements, visual quality requirements, and/or processing capability. ...
... Receiver heterogeneity means that receivers have different or even varying latency requirements, visual quality requirements, and/or processing capability. ...
OneConnect® OCe11101-N
... Universal Multi-Channel OneConnect Universal Multi-Channel (UMC) allows multiple PCI functions to be created. Each network interface card (NIC) function is presented to the operating system or hypervisor as a physical port with a separate MAC address and user-assigned bandwidth. This enables a singl ...
... Universal Multi-Channel OneConnect Universal Multi-Channel (UMC) allows multiple PCI functions to be created. Each network interface card (NIC) function is presented to the operating system or hypervisor as a physical port with a separate MAC address and user-assigned bandwidth. This enables a singl ...
Network Mobility
... The Mobile Router is the default gateway for the Mobile Network A Mobile Network can comprise of nested subnets, but the overhead is heavy A Mobile Router has a unique registered Home Address with its Home Agent. The Home Address is configured from a prefix aggregated and advertised by its Home Agen ...
... The Mobile Router is the default gateway for the Mobile Network A Mobile Network can comprise of nested subnets, but the overhead is heavy A Mobile Router has a unique registered Home Address with its Home Agent. The Home Address is configured from a prefix aggregated and advertised by its Home Agen ...
Strategic Directions - Vision for Cloud Operational Analytics
... Mobilization, DevOps, Micro-services, enterprises are in the new era of transformation for infrastructure and application delivery. With this trend, Application and Network Performance, IT service and Security Event Information Management vendors (APM, NPM, ITSM, SEIM) must evolve their tools to kee ...
... Mobilization, DevOps, Micro-services, enterprises are in the new era of transformation for infrastructure and application delivery. With this trend, Application and Network Performance, IT service and Security Event Information Management vendors (APM, NPM, ITSM, SEIM) must evolve their tools to kee ...
Slide
... with prob. p: randomly selected node with prob. 1-p: copied target from selected ‘prototye node’ 2. Attaching to edges: : after adding new node, instead of selecting target node, select target edges and connect new node to end point of the edges. ...
... with prob. p: randomly selected node with prob. 1-p: copied target from selected ‘prototye node’ 2. Attaching to edges: : after adding new node, instead of selecting target node, select target edges and connect new node to end point of the edges. ...
Chapter 8 Communications and Networks
... A document management system provides for storage and management of a company’s documents ...
... A document management system provides for storage and management of a company’s documents ...
ip-basics
... a protocol that works in the same way with any underlying network Call it the network layer (IP) IP routers operate at the network layer There are defined ways of using: » IP over Ethernet » IP over ATM » IP over FDDI » IP over serial lines (PPP) » IP over almost anything ...
... a protocol that works in the same way with any underlying network Call it the network layer (IP) IP routers operate at the network layer There are defined ways of using: » IP over Ethernet » IP over ATM » IP over FDDI » IP over serial lines (PPP) » IP over almost anything ...
1 - Jolata
... Both the network architecture and the application landscape for communication service providers (CSP) and enterprise network operators are changing rapidly. Traditionally, the large majority of traffic on most operator networks is video streams, which account for 50% of the overall traffic. While th ...
... Both the network architecture and the application landscape for communication service providers (CSP) and enterprise network operators are changing rapidly. Traditionally, the large majority of traffic on most operator networks is video streams, which account for 50% of the overall traffic. While th ...
NCL1135 Configuration
... • Determined by the configured size of the CAP, the available backhaul infrastructure and spectrum in the service area, and the distance between the CAP and the NAP • Consult WaveRider System Engineer for ...
... • Determined by the configured size of the CAP, the available backhaul infrastructure and spectrum in the service area, and the distance between the CAP and the NAP • Consult WaveRider System Engineer for ...
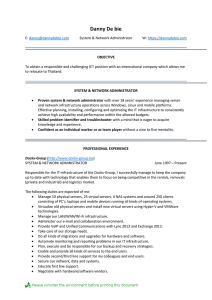
1992-1995: Bachelor degree in Information Technology with
... Globe NV (former ISP) WEB DEVELOPER ...
... Globe NV (former ISP) WEB DEVELOPER ...
ppt
... A source could send through many unicast However, sender may not know individual receivers and efficiency ...
... A source could send through many unicast However, sender may not know individual receivers and efficiency ...
Slide 1 - University of Dayton
... media, using packet switching. Packet switching - individual packets are routed through the network based on the destination address contained in each packet. With packet switching, the same data path can be shared among many computers in the network, and if a computer on the network is inoperable ...
... media, using packet switching. Packet switching - individual packets are routed through the network based on the destination address contained in each packet. With packet switching, the same data path can be shared among many computers in the network, and if a computer on the network is inoperable ...
Network+ Guide to Networks, Fourth Edition
... • A physical topology is the basic physical layout of a network; it does not specify devices, connectivity methods, or addresses on the network • A bus topology consists of a single cable connecting all nodes on a network without intervening connectivity devices • In a ring topology, each node is co ...
... • A physical topology is the basic physical layout of a network; it does not specify devices, connectivity methods, or addresses on the network • A bus topology consists of a single cable connecting all nodes on a network without intervening connectivity devices • In a ring topology, each node is co ...
ppt - Computer Science Division
... • Each packet is independently switched – Each packet header contains destination address ...
... • Each packet is independently switched – Each packet header contains destination address ...
click here to
... Early circuit-switched networks did not automatically establish alternative circuits in the event of circuit failure. Circuit-switched technologies required that an open circuit between network endpoints be established even if data was not being actively transferred between locations. ...
... Early circuit-switched networks did not automatically establish alternative circuits in the event of circuit failure. Circuit-switched technologies required that an open circuit between network endpoints be established even if data was not being actively transferred between locations. ...
Internet Routing Protocols
... Multiple same-cost paths allowed (only one path in RIP) For each link, multiple cost metrics for different TOS (e.g., satellite link cost set “low” for best effort; high for real time) Integrated uni- and multicast support: Multicast OSPF (MOSPF) uses same topology data base as OSPF Hierarchical O ...
... Multiple same-cost paths allowed (only one path in RIP) For each link, multiple cost metrics for different TOS (e.g., satellite link cost set “low” for best effort; high for real time) Integrated uni- and multicast support: Multicast OSPF (MOSPF) uses same topology data base as OSPF Hierarchical O ...
Plugging the Leaks Without Unplugging Your Network in the Midst of
... has been studied extensively and the security implications of this behavior are relatively well understood. Security practices have concentrated on barring unauthorized parties from access to the network. Unfortunately, security at the network boundary often breaks down under a catastrophic event. D ...
... has been studied extensively and the security implications of this behavior are relatively well understood. Security practices have concentrated on barring unauthorized parties from access to the network. Unfortunately, security at the network boundary often breaks down under a catastrophic event. D ...
Computer Networks
... Computer Network standards • Standards play an important role in networking. Without standards, manufacturers of networking products have no common ground on which to build their systems. Interconnecting products from various vendors would be difficult, if not impossible. • It is necessary to have ...
... Computer Network standards • Standards play an important role in networking. Without standards, manufacturers of networking products have no common ground on which to build their systems. Interconnecting products from various vendors would be difficult, if not impossible. • It is necessary to have ...
USER IDENTIFICATION SYSTEM (UIS) By: Abhishek Sharma
... To develop a system to provide seamless interaction between users at different locations attending the same meeting independent of their personal contact information ...
... To develop a system to provide seamless interaction between users at different locations attending the same meeting independent of their personal contact information ...
Chapter 4 : TCP/IP and OSI
... • Most TCP/IP applications use TCP for transport layer • TCP provides a connection (logical association) between two entities to regulate flow check errors • UDP (User Datagram Protocol) does not maintain a connection, and therefore does not guarantee delivery, preserve sequences, or protect ...
... • Most TCP/IP applications use TCP for transport layer • TCP provides a connection (logical association) between two entities to regulate flow check errors • UDP (User Datagram Protocol) does not maintain a connection, and therefore does not guarantee delivery, preserve sequences, or protect ...
Protocol Stack
... Physical: how to transmit bits Data link: how to transmit frames Network: how to route packets Transport: how to send packets end2end Session: how to tie flows together ...
... Physical: how to transmit bits Data link: how to transmit frames Network: how to route packets Transport: how to send packets end2end Session: how to tie flows together ...
new1
... Addressable Network). Node identified by hyper-rectangle in d-dimensional space Key hashed to a point, stored in corresponding node. Routing Table of neighbours is maintained. O(d) ...
... Addressable Network). Node identified by hyper-rectangle in d-dimensional space Key hashed to a point, stored in corresponding node. Routing Table of neighbours is maintained. O(d) ...