Network ID
... • Move data through a set of networks. • Logical Addressing, use a hierarchical addressing scheme. ...
... • Move data through a set of networks. • Logical Addressing, use a hierarchical addressing scheme. ...
Systems and methods for forwarding data units in a communications
... (110), determine one of the network interfaces (240) to trans mit the data unit When the data unit is ready to be transmitted by the network device (110), and forward the data unit to the determined network interface (240) for network When the determined network interface (240) is the identi?ed netw ...
... (110), determine one of the network interfaces (240) to trans mit the data unit When the data unit is ready to be transmitted by the network device (110), and forward the data unit to the determined network interface (240) for network When the determined network interface (240) is the identi?ed netw ...
Vodafone PowerPoint template
... In 2002, a group of engineers at Motorola in Swindon, England, started a skunkworks team, called the "AFG", to develop new technologies. Some of their major achievements included the world's smallest full-power UMTS base station, one of the first demonstrations of television to mobile, and the inven ...
... In 2002, a group of engineers at Motorola in Swindon, England, started a skunkworks team, called the "AFG", to develop new technologies. Some of their major achievements included the world's smallest full-power UMTS base station, one of the first demonstrations of television to mobile, and the inven ...
Serval: An End-Host Stack for Service-Centric Networking
... The rest of the traffic flows directly between end-points according to network-layer forwarding. The SAL performs signaling between end-points to establish additional flows (over different interfaces or paths) and can migrate them over time. In doing so, the SAL provides a transportagnostic solution ...
... The rest of the traffic flows directly between end-points according to network-layer forwarding. The SAL performs signaling between end-points to establish additional flows (over different interfaces or paths) and can migrate them over time. In doing so, the SAL provides a transportagnostic solution ...
Overview of Internet2 - CITI
... Seven strategic focus areas Advanced network and network services leadership Net+: services “above the network” U.S. UCAN NaTonal/Regional collaboraTon Global reach and leadership Research community development and ...
... Seven strategic focus areas Advanced network and network services leadership Net+: services “above the network” U.S. UCAN NaTonal/Regional collaboraTon Global reach and leadership Research community development and ...
Networks Oy - Roggeweck.net
... GPRS users have to be charged for the use of the network. In a GSM network, charging is based on the destination, duration, and time of call. However, GPRS offers connectionless service to users, so it not possible to charge subscribers on the connection duration. Charging has to be based on the vol ...
... GPRS users have to be charged for the use of the network. In a GSM network, charging is based on the destination, duration, and time of call. However, GPRS offers connectionless service to users, so it not possible to charge subscribers on the connection duration. Charging has to be based on the vol ...
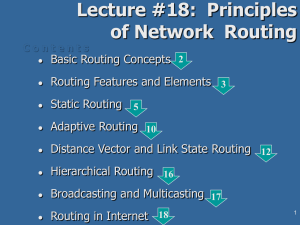
18. Principles of Network Routing
... service oriented (consider real-time and priority of the IP datagrames) congestion control (load balancing) considerations conservative: frequent alternative events are ignored! support of hierarchical routing: splitting of AS in areas and backbones security: routing table protection tunneling and t ...
... service oriented (consider real-time and priority of the IP datagrames) congestion control (load balancing) considerations conservative: frequent alternative events are ignored! support of hierarchical routing: splitting of AS in areas and backbones security: routing table protection tunneling and t ...
NETWORK TECHNOLOGIES AND APPLICATIONS
... networking devices, that functions as a single large network. Internetworking refers to the industry, products, and procedures that meet the challenge of creating and administering internetworks. Figure 1-1 illustrates some different kinds of network technologies that can be interconnected by router ...
... networking devices, that functions as a single large network. Internetworking refers to the industry, products, and procedures that meet the challenge of creating and administering internetworks. Figure 1-1 illustrates some different kinds of network technologies that can be interconnected by router ...
Review, UTRAN Interfaces
... Review, Protocol Model for UTRAN Interfaces The UTRAN specific protocols include —Radio Access Network Application Part: Radio Network Signaling over the Iu. —Radio Network Subsystem Application Part: Radio Network Signaling over the Iur. ...
... Review, Protocol Model for UTRAN Interfaces The UTRAN specific protocols include —Radio Access Network Application Part: Radio Network Signaling over the Iu. —Radio Network Subsystem Application Part: Radio Network Signaling over the Iur. ...
Tema 1: Tecnologías de red. - GRC
... Initially, largely research organizations and universities, now mostly R&D labs of equipment vendors and ISPs International, but 2/3 United States meetings every four months about 300 companies participating in meetings but Cisco, Ericsson, Lucent, Nokia, etc. send large delegations ...
... Initially, largely research organizations and universities, now mostly R&D labs of equipment vendors and ISPs International, but 2/3 United States meetings every four months about 300 companies participating in meetings but Cisco, Ericsson, Lucent, Nokia, etc. send large delegations ...
EIGRP and OSPF Comparison
... Link-state routing protocols, such as Open Shortest Path First (OSPF), Intermediate Systemto-Intermediate System (IS-IS), and NetWare Link Services Protocol (NLSP), were designed to address the limitations of distance vector routing protocols (slow convergence and unnecessary bandwidth usage). Link- ...
... Link-state routing protocols, such as Open Shortest Path First (OSPF), Intermediate Systemto-Intermediate System (IS-IS), and NetWare Link Services Protocol (NLSP), were designed to address the limitations of distance vector routing protocols (slow convergence and unnecessary bandwidth usage). Link- ...
BitTorrent file sharing using Tor-like hidden services R.J. Ruigrok Technology
... This thesis proposes a design for implementing Tor-like hidden services in a decentralized peer-to-peer system, enabling the possibility of downloading and seeding anonymously. A proof-of-concept will be implemented into Tribler, a BitTorrent client developed at Delft University of Technology. Tribl ...
... This thesis proposes a design for implementing Tor-like hidden services in a decentralized peer-to-peer system, enabling the possibility of downloading and seeding anonymously. A proof-of-concept will be implemented into Tribler, a BitTorrent client developed at Delft University of Technology. Tribl ...
Chap 11 Routing
... routing update about Network 1 arrives from Router A, Router B or Router D cannot send information about Network 1 back to Router A ...
... routing update about Network 1 arrives from Router A, Router B or Router D cannot send information about Network 1 back to Router A ...
Issue - IETF
... Unicast encapsulation solutions such as 6rd or DS-lite do not apply to multicast. ...
... Unicast encapsulation solutions such as 6rd or DS-lite do not apply to multicast. ...
Ethernet frames - La Salle University
... • So before transmitting a large packet, Computer 1 issues a small control packet indicating it will transmit a larger packet. • The Computer 2 issues a reply packet which is read by all computers in its vicinity (including Computer 3) that it expects to receive a message from Computer 1. Computer 3 ...
... • So before transmitting a large packet, Computer 1 issues a small control packet indicating it will transmit a larger packet. • The Computer 2 issues a reply packet which is read by all computers in its vicinity (including Computer 3) that it expects to receive a message from Computer 1. Computer 3 ...
Activating an EVDO Wireless Card in a Cellular
... c Type the following command (where Secondary Home Address represents the value provided on the Sprint form) and press Enter. AT $QCMIP SHA = Secondary Home Address,1 For example, if your wireless card’s secondary home address is 68.25.x.x, type the following and press Enter. AT $QCMIP SHA = 68.28.x ...
... c Type the following command (where Secondary Home Address represents the value provided on the Sprint form) and press Enter. AT $QCMIP SHA = Secondary Home Address,1 For example, if your wireless card’s secondary home address is 68.25.x.x, type the following and press Enter. AT $QCMIP SHA = 68.28.x ...
Chapter 1
... routing packets to Network 1. • But Routers B, C, and D continue to do so because they have not yet been informed about the failure. • Router A sends out its update. • Routers B and D stop routing to network1, (via Router A). • However, Router C is still not updated. To router C, network 1 is still ...
... routing packets to Network 1. • But Routers B, C, and D continue to do so because they have not yet been informed about the failure. • Router A sends out its update. • Routers B and D stop routing to network1, (via Router A). • However, Router C is still not updated. To router C, network 1 is still ...
IEEE 802 March 2011 workshop - LMSC, LAN/MAN Standards
... • When used with the Traffic Filtering Service, can provide significant station power savings, and provide a “Wake on WLAN” service. Flexible Broadcast/Multicast service • Enables multicast frames to be sent at longer delivery intervals and higher data rates, improving performance of multicast appli ...
... • When used with the Traffic Filtering Service, can provide significant station power savings, and provide a “Wake on WLAN” service. Flexible Broadcast/Multicast service • Enables multicast frames to be sent at longer delivery intervals and higher data rates, improving performance of multicast appli ...
Deployment of IPSec Virtual Private Network Solutions
... Transport ESP (IP/port50) AH (IP/port51) Network address translation (NAT) ...
... Transport ESP (IP/port50) AH (IP/port51) Network address translation (NAT) ...
3 What is MMS? - ECO Documentation Database
... MMS has been standardized by 3GPP [1, 2] and the standards have been published by ETSI. WAP is an industry standard produced by the WAP-forum, which has been integrated into the Open Mobile Alliance (OMA, http://www.openmobilealliance.org/). The work of the WAP Forum continues in the different Worki ...
... MMS has been standardized by 3GPP [1, 2] and the standards have been published by ETSI. WAP is an industry standard produced by the WAP-forum, which has been integrated into the Open Mobile Alliance (OMA, http://www.openmobilealliance.org/). The work of the WAP Forum continues in the different Worki ...
paper
... packets to the router, which XORs the two packets and broadcasts the XOR-ed version. Alice and Bob can obtain each other’s packet by XOR-ing again with their own packet. This process takes 3 transmissions instead of 4. Saved transmissions can be used to send new data, increasing the wireless through ...
... packets to the router, which XORs the two packets and broadcasts the XOR-ed version. Alice and Bob can obtain each other’s packet by XOR-ing again with their own packet. This process takes 3 transmissions instead of 4. Saved transmissions can be used to send new data, increasing the wireless through ...
Modern Internet architecture & technology
... RFC 1958: “An end-to-end protocol design should not rely on the maintenance of state (i.e., information about the state of the end-to-end communication) inside the network. Such state should be maintained only in the endpoints, in such a way that the state can only be destroyed when the endpoint its ...
... RFC 1958: “An end-to-end protocol design should not rely on the maintenance of state (i.e., information about the state of the end-to-end communication) inside the network. Such state should be maintained only in the endpoints, in such a way that the state can only be destroyed when the endpoint its ...
slides - Network and Systems Laboratory
... An Experimental Study of the Skype Peer-to-Peer VoIP System Saikat Guha, Cornell University Neil DasWani, Google Ravi Jain, Google IPTPS’06 Presenter: Te-Yuan ...
... An Experimental Study of the Skype Peer-to-Peer VoIP System Saikat Guha, Cornell University Neil DasWani, Google Ravi Jain, Google IPTPS’06 Presenter: Te-Yuan ...
Element Management Systems (EMSs)
... interface an intuitive operation. A well-designed user interface can combine technically diverse yet logically related functions onto a single screen that offers a simple workflow and includes default values and selectable options to save time and reduce errors. Figure 5 is for an HFC–cable telephon ...
... interface an intuitive operation. A well-designed user interface can combine technically diverse yet logically related functions onto a single screen that offers a simple workflow and includes default values and selectable options to save time and reduce errors. Figure 5 is for an HFC–cable telephon ...