Forcepoint Sidewinder Administration Guide
... Authenticating groups from an external group source . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .105 Authenticating groups from an internal group source . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ...
... Authenticating groups from an external group source . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .105 Authenticating groups from an internal group source . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ...
2. Principles governing the use of TCP/IP on the GTS
... Data exchange between non adjacent centres; Exchange of information that cannot readily be handled by message switching systems (MSSs). The full list of requirements to be fulfilled by the Main Telecommunications Network (MTN) of the GTS were agreed upon by CBS-Ext. 1994. The use of TCP/IP servi ...
... Data exchange between non adjacent centres; Exchange of information that cannot readily be handled by message switching systems (MSSs). The full list of requirements to be fulfilled by the Main Telecommunications Network (MTN) of the GTS were agreed upon by CBS-Ext. 1994. The use of TCP/IP servi ...
Defense
... Weak Wireless Encryption • Using PEAP/TTLS the data within the tunnel cannot be decrypted without the TLS master secret and the key is not shared with the Access point. Rogue/compromised access points cannot decrypt messages. ...
... Weak Wireless Encryption • Using PEAP/TTLS the data within the tunnel cannot be decrypted without the TLS master secret and the key is not shared with the Access point. Rogue/compromised access points cannot decrypt messages. ...
2930F TAA Switch Series Data Sheet
... administration by using a password authentication server • IEEE 802.1X, MAC, or Web authentication provides concurrent network access control and Web authentication of up to 24 clients per port • Secure shell encrypts all transmitted data for secure remote CLI access over IP networks • Secure Socket ...
... administration by using a password authentication server • IEEE 802.1X, MAC, or Web authentication provides concurrent network access control and Web authentication of up to 24 clients per port • Secure shell encrypts all transmitted data for secure remote CLI access over IP networks • Secure Socket ...
third edition
... and to see the big picture of networking. It is our experience that both students and professionals learning about networks for the first time often have the impression that network protocols are some sort of edict handed down from on high, and that their job is to learn as many TLAs (three-letter a ...
... and to see the big picture of networking. It is our experience that both students and professionals learning about networks for the first time often have the impression that network protocols are some sort of edict handed down from on high, and that their job is to learn as many TLAs (three-letter a ...
On peer-to-peer (P2P) content delivery
... popular P2P file sharing utilities, such as BitTorrent, eDonkey, FastTrack and Gnutella belongs to this mode. In the bulk download mode, the peer doesn’t care about the source characteristics (video file at 400 kbps). Its operation goal is simply to retrieve the file from the P2P network as fast as ...
... popular P2P file sharing utilities, such as BitTorrent, eDonkey, FastTrack and Gnutella belongs to this mode. In the bulk download mode, the peer doesn’t care about the source characteristics (video file at 400 kbps). Its operation goal is simply to retrieve the file from the P2P network as fast as ...
FIRETIDE RFP RESPONSE TEMPLATE
... HotView Pro provides advanced management software that enables centralized control of larger mesh environments and multiple mesh networks such as enterprise or metropolitan networks. SNMP management is included to allow network administrators to integrate management of HotPort mesh networks into a n ...
... HotView Pro provides advanced management software that enables centralized control of larger mesh environments and multiple mesh networks such as enterprise or metropolitan networks. SNMP management is included to allow network administrators to integrate management of HotPort mesh networks into a n ...
SMART WIRELESS GATEWAY HART MANUAL
... This section describes how to connect to the Gateway for the first time and what settings should be configured before placing it on a live control network. It is important to note that some Gateways are used in stand-alone applications and do not reside on a network. In these cases it is still impor ...
... This section describes how to connect to the Gateway for the first time and what settings should be configured before placing it on a live control network. It is important to note that some Gateways are used in stand-alone applications and do not reside on a network. In these cases it is still impor ...
KillerBee: Practical ZigBee Exploitation Framework or "Hacking the
... cipher and IV reuse (known plaintext recovery) • Each vendor makes their stack available as open source, and all have problems • Adoption will continue in critical technology areas – it's too attractive for embedded development to avoid ...
... cipher and IV reuse (known plaintext recovery) • Each vendor makes their stack available as open source, and all have problems • Adoption will continue in critical technology areas – it's too attractive for embedded development to avoid ...
PDF - ZTE Deutschland GmbH
... Competition is the driver for innovation and developments. Hurdles are the obstacles to develop technologies with freedom, i.e. technology neutrality for frequencies. This has to be liberalized in Belarus. Other markets with open policy have proven the huge positive value to end users and to the ent ...
... Competition is the driver for innovation and developments. Hurdles are the obstacles to develop technologies with freedom, i.e. technology neutrality for frequencies. This has to be liberalized in Belarus. Other markets with open policy have proven the huge positive value to end users and to the ent ...
M T ASTER’S HESIS
... Multicasting allows us to send a data packet to multiple sites at the same time. The key here is the ability to send one message to one or more nodes in a single operation. This provides a tremendous amount of savings in bandwidth when compared to traditional unicast transmission which sends message ...
... Multicasting allows us to send a data packet to multiple sites at the same time. The key here is the ability to send one message to one or more nodes in a single operation. This provides a tremendous amount of savings in bandwidth when compared to traditional unicast transmission which sends message ...
GMPLS-based provisioning of Ethernet connections over WSON with Quality of Service Ph.D. Thesis
... processing at the higher layers, which require expensive optical-electrical-optical (OEO) conversions, reducing, thus, the overall network cost. On the other hand, next generation networks are expected to efficiently support packet-based services such as Ethernet transport, while keeping the same ca ...
... processing at the higher layers, which require expensive optical-electrical-optical (OEO) conversions, reducing, thus, the overall network cost. On the other hand, next generation networks are expected to efficiently support packet-based services such as Ethernet transport, while keeping the same ca ...
DutyCon: A dynamic duty-cycle control approach to end
... protocols, such as B-MAC [Polastre et al. 2004] and X-MAC [Buettner et al. 2006]. Nodes in these protocols wake up periodically to poll the channel for activities. If the channel is busy, they stay awake and prepare to get data. However, nodes using the channel polling approach are usually configure ...
... protocols, such as B-MAC [Polastre et al. 2004] and X-MAC [Buettner et al. 2006]. Nodes in these protocols wake up periodically to poll the channel for activities. If the channel is busy, they stay awake and prepare to get data. However, nodes using the channel polling approach are usually configure ...
Reference Manual for the 54 Mbps Wireless Router WGR614 v6 202-10099-01, April 2005
... Routing Information Protocol ................................................................................... B-2 IP Addresses and the Internet ....................................................................................... B-2 Netmask ..................................................... ...
... Routing Information Protocol ................................................................................... B-2 IP Addresses and the Internet ....................................................................................... B-2 Netmask ..................................................... ...
- TUCAA: The Ultimate Computer Acronyms Archive
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
- TUCAA: The Ultimate Computer Acronyms Archive
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
Before You Begin: Assign Information Classification
... abstraction of compute resources. Amazon’s Definition of ECU notes “We use several benchmarks and tests to manage the consistency and predictability of the performance of an EC2 Compute Unit. One EC2 Compute Unit provides the equivalent CPU capacity of a 1.0-1.2 GHz 2007 Opteron or 2007 Xeon process ...
... abstraction of compute resources. Amazon’s Definition of ECU notes “We use several benchmarks and tests to manage the consistency and predictability of the performance of an EC2 Compute Unit. One EC2 Compute Unit provides the equivalent CPU capacity of a 1.0-1.2 GHz 2007 Opteron or 2007 Xeon process ...
TUCAA: The Ultimate Computer Acronyms Archive
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
The Ultimate Computer Acronyms Archive
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
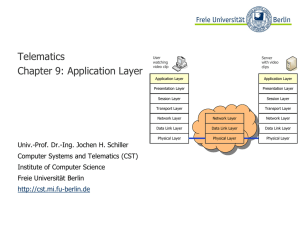
Application Layer - Freie Universität Berlin
... (e.g. Crash of a sender in the mid of the data transmission process) ● Synchronization points can be set on Layer 5 at arbitrary times ● If connection breaks down, transmission can restart at the last synchronization point ...
... (e.g. Crash of a sender in the mid of the data transmission process) ● Synchronization points can be set on Layer 5 at arbitrary times ● If connection breaks down, transmission can restart at the last synchronization point ...
Document
... 4 subnets can be represented with 2 bits (22 = 4) For a class B address, which already uses 16 bits for the network portion, the address would use 18 bits for the subnet portion ...
... 4 subnets can be represented with 2 bits (22 = 4) For a class B address, which already uses 16 bits for the network portion, the address would use 18 bits for the subnet portion ...
Kahu Compute.
... Software is eating the world, and the datacenter is next. How will your enterprise leverage the next product cycle to reduce costs and increase efficiency? What tools do you need to run tons of compute and storage at scale, while maximizing performance? How can you maintain your data sovereignty req ...
... Software is eating the world, and the datacenter is next. How will your enterprise leverage the next product cycle to reduce costs and increase efficiency? What tools do you need to run tons of compute and storage at scale, while maximizing performance? How can you maintain your data sovereignty req ...
MinBD: Minimally-Buffered Deflection Routing for Energy
... ensure that all traffic is eventually delivered. Removing buffers yields simpler and more energy-efficient NoC designs: e.g., CHIPPER [12] reduces average network power by 54.9% in a 64-node system compared to a conventional buffered router. Unfortunately, at high network load, deflection routing re ...
... ensure that all traffic is eventually delivered. Removing buffers yields simpler and more energy-efficient NoC designs: e.g., CHIPPER [12] reduces average network power by 54.9% in a 64-node system compared to a conventional buffered router. Unfortunately, at high network load, deflection routing re ...