free sample here
... Which of the following is a true statement about the OSI model layers? A. The layers cannot communicate with one another. B. Any layer can communicate directly with any other layer. C. Any layer can communicate only with the layer directly above or below it. D. Any layer can communicate only with th ...
... Which of the following is a true statement about the OSI model layers? A. The layers cannot communicate with one another. B. Any layer can communicate directly with any other layer. C. Any layer can communicate only with the layer directly above or below it. D. Any layer can communicate only with th ...
Chapter 5 Local Area Network Concepts and Architecture
... 10Base5 (thick coaxial cable RG-11) 100BaseT Fast Ethernet with 100-Mbps – 100BaseTX (2 pair of Category 5 UTP or 1 pair ...
... 10Base5 (thick coaxial cable RG-11) 100BaseT Fast Ethernet with 100-Mbps – 100BaseTX (2 pair of Category 5 UTP or 1 pair ...
slides (PowerPoint)
... Flash Worm – Conclusion based on above analysis is that a “tight” worm with a good hit-list could take down the population in 10’s of seconds. ...
... Flash Worm – Conclusion based on above analysis is that a “tight” worm with a good hit-list could take down the population in 10’s of seconds. ...
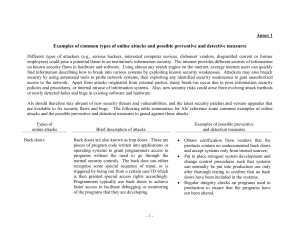
Annex 1
... Apply the latest security patches and updates to the operating systems and applications of the systems; Select hardware and software vendors who are able to keep abreast of the latest technology developments to protect from the latest attack techniques; Use scanning tools or perform penetration test ...
... Apply the latest security patches and updates to the operating systems and applications of the systems; Select hardware and software vendors who are able to keep abreast of the latest technology developments to protect from the latest attack techniques; Use scanning tools or perform penetration test ...
Chapter 1 Lecture Presentation
... networks Host computers prepare IP packets and transmit them over their attached network Routers forward IP packets across networks Best-effort IP transfer service, no retransmission ...
... networks Host computers prepare IP packets and transmit them over their attached network Routers forward IP packets across networks Best-effort IP transfer service, no retransmission ...
Transport
... – An AS may not be willing to carry traffic originating and destined to foreign ASs. – Example: phone companies are willing to carry traffic for their customers but not for others. ...
... – An AS may not be willing to carry traffic originating and destined to foreign ASs. – Example: phone companies are willing to carry traffic for their customers but not for others. ...
lecture17
... – 1: Hard-coded by system administrator in a file inside the host. – 2: DHCP: “Dynamic Host Configuration Protocol” • Dynamically get address: “plug-and-play”. ...
... – 1: Hard-coded by system administrator in a file inside the host. – 2: DHCP: “Dynamic Host Configuration Protocol” • Dynamically get address: “plug-and-play”. ...
Introduction to IPv6
... INTERNET world’s largest public data network, doubling in size every nine months IPv4, defines a 32-bit address - 232 (4,294,967,296) IPv4 addresses available The first problem is concerned with the eventual depletion of the IP address space. Traditional model of classful addressing does not allow ...
... INTERNET world’s largest public data network, doubling in size every nine months IPv4, defines a 32-bit address - 232 (4,294,967,296) IPv4 addresses available The first problem is concerned with the eventual depletion of the IP address space. Traditional model of classful addressing does not allow ...
Document
... again on March 11 1996. • ARPA was responsible for funding development of ARPANET (which grew into the Internet), as well as the Berkeley version of Unix (BSD) and TCP/IP. ...
... again on March 11 1996. • ARPA was responsible for funding development of ARPANET (which grew into the Internet), as well as the Berkeley version of Unix (BSD) and TCP/IP. ...
download
... brought to us courtesy of IEEE, offers a framework for authenticating and controlling user traffic to a protected network, as well as dynamically varying encryption keys (verses the easily cracked static encryption keys that WEP calls for). 802.1X ties a protocol called EAP (Extensible Authenticatio ...
... brought to us courtesy of IEEE, offers a framework for authenticating and controlling user traffic to a protected network, as well as dynamically varying encryption keys (verses the easily cracked static encryption keys that WEP calls for). 802.1X ties a protocol called EAP (Extensible Authenticatio ...
MOD02_SC
... • Bridges use “store and forward” to ensure no errors are passed onto another segment. • Bridges do not pass errors or collisions through to another segment. ...
... • Bridges use “store and forward” to ensure no errors are passed onto another segment. • Bridges do not pass errors or collisions through to another segment. ...
Acadia - IT, Sligo
... post office box and will store all e-mail messages. The update DNS process will flow from the individual school server to the Hub server and to the district server. All regional servers will be able to communicate between themselves, building reducdancy in the system. ADMINISTRATIVE SERVER : This wi ...
... post office box and will store all e-mail messages. The update DNS process will flow from the individual school server to the Hub server and to the district server. All regional servers will be able to communicate between themselves, building reducdancy in the system. ADMINISTRATIVE SERVER : This wi ...
IP Addresses - Paladin Group LLC
... encryption and proper authentication practices. • If possible restrict network management to “management network IP addresses” ...
... encryption and proper authentication practices. • If possible restrict network management to “management network IP addresses” ...
NTW T2 Protocol Stack
... » what is the minimum number of host bits needed to address each router with a unique IP address? » what is the corresponding prefix length? » what is the corresponding netmask (in decimal)? » how many hosts could be handled with that ...
... » what is the minimum number of host bits needed to address each router with a unique IP address? » what is the corresponding prefix length? » what is the corresponding netmask (in decimal)? » how many hosts could be handled with that ...
eStadium Project Lab 8: Wireless Mesh Network Setup with DD-WRT
... Version 24 of DD‐WRT firmware has a wireless mode that is used for mesh networking called Wireless Distributed System (WDS). WDS AP can connect to multiple other nodes and forward packets between them. WDS station is an end node of the mesh network. A WDS station connects to a WDS AP and sends it ...
... Version 24 of DD‐WRT firmware has a wireless mode that is used for mesh networking called Wireless Distributed System (WDS). WDS AP can connect to multiple other nodes and forward packets between them. WDS station is an end node of the mesh network. A WDS station connects to a WDS AP and sends it ...
CSCI-1305 Introduction To Information Technology
... LAN – Local Area Network • A local area network (LAN) connects computers and devices in a limited area, such as a home, an office building, an office complex, or a school ...
... LAN – Local Area Network • A local area network (LAN) connects computers and devices in a limited area, such as a home, an office building, an office complex, or a school ...
Denial of Service Attacks
... Consider deploying host-based Intrusion Detection Systems or other system monitoring tools that can warn you when your system resources are getting low. ...
... Consider deploying host-based Intrusion Detection Systems or other system monitoring tools that can warn you when your system resources are getting low. ...
CPE 400: Computer Communication Networks
... classes) • Protocol architecture, TCP/IP, and Internet-based applications (2 classes) • Data transmission principle and transmission media (4 classes) • Signal encoding techniques and multiplexing (4 classes) • Digital data communication techniques and data link protocols (4 classes) • Circuit switc ...
... classes) • Protocol architecture, TCP/IP, and Internet-based applications (2 classes) • Data transmission principle and transmission media (4 classes) • Signal encoding techniques and multiplexing (4 classes) • Digital data communication techniques and data link protocols (4 classes) • Circuit switc ...
Slide - ICNP
... Directories and Mobility Directories are required to determine destination network addresses ...
... Directories and Mobility Directories are required to determine destination network addresses ...
security_6
... web site (where visitors are coming from, how often they return, how they navigate through a site and data from shopping cart) ...
... web site (where visitors are coming from, how often they return, how they navigate through a site and data from shopping cart) ...
Topics discussed in this section
... A protocol is a set of rules that govern data communications. A protocol defines what is communicated, how it is communicated, and when it is communicated. The key elements of a protocol are syntax, semantics, and timing. Syntax refers to the structure or format of the data, meaning the order in whi ...
... A protocol is a set of rules that govern data communications. A protocol defines what is communicated, how it is communicated, and when it is communicated. The key elements of a protocol are syntax, semantics, and timing. Syntax refers to the structure or format of the data, meaning the order in whi ...
networking and internetworking
... Transfers data packets between computers in a specific network. In a WAN or an internetwork this involves the generation of a route passing through routers. In a single LAN no routing is required. Responsible for transmission of packets between nodes that are directly connected by a physical link. I ...
... Transfers data packets between computers in a specific network. In a WAN or an internetwork this involves the generation of a route passing through routers. In a single LAN no routing is required. Responsible for transmission of packets between nodes that are directly connected by a physical link. I ...
Intro to UDP and TCP
... 3-way handshaking for connection setup Error checking Flow control Congestion control Error-free, in-order delivery of data to application layer ...
... 3-way handshaking for connection setup Error checking Flow control Congestion control Error-free, in-order delivery of data to application layer ...
Lec-12 - PCT Research Group
... Its primary function is routing It deals with end-end to transmission It involves at the source host, destination host and all routers in the path ...
... Its primary function is routing It deals with end-end to transmission It involves at the source host, destination host and all routers in the path ...