Organizations That Use TLS/SSL
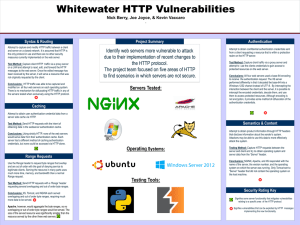
... exposed. Exposed data and session ID's can be intercepted which means the application is vulnerable to exploit. As OWASP states, "Applications frequently fail to authenticate, encrypt, and protect the confidentiality and integrity of sensitive network traffic. When they do, they sometimes support we ...
... exposed. Exposed data and session ID's can be intercepted which means the application is vulnerable to exploit. As OWASP states, "Applications frequently fail to authenticate, encrypt, and protect the confidentiality and integrity of sensitive network traffic. When they do, they sometimes support we ...
Chapter 6
... • The SSL system from Netscape that provides secure information transfer through the Internet. • The SSL works at the transport layer of Internet protocol. • The SSL encrypts and decrypts information flowing between the two computers. • All communication between SSL-enabled clients and servers is en ...
... • The SSL system from Netscape that provides secure information transfer through the Internet. • The SSL works at the transport layer of Internet protocol. • The SSL encrypts and decrypts information flowing between the two computers. • All communication between SSL-enabled clients and servers is en ...
How UTM Solutions Provide the Most Complete
... Many of these attacks emanate from large networks of innocent computers, known as botnets, which have been compromised with malicious code. The attacker (the botherder) remotely controls these zombie or slave computers through a communication channel, such as Internet Relay Chat (IRC), P2P, ...
... Many of these attacks emanate from large networks of innocent computers, known as botnets, which have been compromised with malicious code. The attacker (the botherder) remotely controls these zombie or slave computers through a communication channel, such as Internet Relay Chat (IRC), P2P, ...
COMPUTER INFORMATION TECHNOLOGY AT NKU
... applications that function correctly even when under attack. ...
... applications that function correctly even when under attack. ...
Proxy TechBrief – Basic Troubleshooting Procedures SG
... 2. Verify that your workstation is configured and working properly by connecting to other Web sites (such as www.bluecoat.com ). If your browser is configured to use the ProxySG as the proxy server (explicit proxy) and there is an internal problem with the appliance, this test might fail. Verify wit ...
... 2. Verify that your workstation is configured and working properly by connecting to other Web sites (such as www.bluecoat.com ). If your browser is configured to use the ProxySG as the proxy server (explicit proxy) and there is an internal problem with the appliance, this test might fail. Verify wit ...
Do`s and Don`ts for web application developers
... grouped by vulnerability categories. This is not an exhaustive list, but these slides and the included document references in the speaker notes should serve as a very good starting place for creating secure web applications. ...
... grouped by vulnerability categories. This is not an exhaustive list, but these slides and the included document references in the speaker notes should serve as a very good starting place for creating secure web applications. ...
Web Server Administration
... policy file to determine which files to monitor A default list of files is included but it will take time to refine the list A report can be produced to find out which files have been added, changed, and deleted ...
... policy file to determine which files to monitor A default list of files is included but it will take time to refine the list A report can be produced to find out which files have been added, changed, and deleted ...
Net+ Chapter 1
... Secure Sockets Layer (SSL) is a protocol that has been designed to provide a secure connection over an insecure network, such as the Internet. SSL runs above the TCP/IP protocol and below some of the higher-level protocols such as Hypertext Transfer Protocol (HTTP) and File Transfer Protocol (FTP). ...
... Secure Sockets Layer (SSL) is a protocol that has been designed to provide a secure connection over an insecure network, such as the Internet. SSL runs above the TCP/IP protocol and below some of the higher-level protocols such as Hypertext Transfer Protocol (HTTP) and File Transfer Protocol (FTP). ...
abstract - Chennaisunday.com
... successful PKI, such as insurance and legal aspects, have been greatly improved. The Public-key system makes it possible for two parties to communicate securely without either having to know or trust the other party. However, this is only possible because a third party that both the other parties tr ...
... successful PKI, such as insurance and legal aspects, have been greatly improved. The Public-key system makes it possible for two parties to communicate securely without either having to know or trust the other party. However, this is only possible because a third party that both the other parties tr ...
Hardware Building Blocks and Encoding
... SET is a cryptographic protocol developed by a group of companies that included Visa, Microsoft, IBM, RSA, Netscape, MasterCard and others. It is a highly specialized system with complex specifications contained in three books with book one dealing with the business description, book two a programme ...
... SET is a cryptographic protocol developed by a group of companies that included Visa, Microsoft, IBM, RSA, Netscape, MasterCard and others. It is a highly specialized system with complex specifications contained in three books with book one dealing with the business description, book two a programme ...
Security & Privacy on the WWW
... user name, public key, serial number, expiration date, signature of trusted CA (message encrypted by CA’s private key) Receipt of a valid certificate is proof of identity – can be checked at CAs sight www.verisign.com is major player ...
... user name, public key, serial number, expiration date, signature of trusted CA (message encrypted by CA’s private key) Receipt of a valid certificate is proof of identity – can be checked at CAs sight www.verisign.com is major player ...
Detailed Overview of Security and Privacy lecture slides
... user name, public key, serial number, expiration date, signature of trusted CA (message encrypted by CA’s private key) Receipt of a valid certificate is proof of identity – can be checked at CAs sight www.verisign.com is major player ...
... user name, public key, serial number, expiration date, signature of trusted CA (message encrypted by CA’s private key) Receipt of a valid certificate is proof of identity – can be checked at CAs sight www.verisign.com is major player ...
Session 2 notes - FAU College of Engineering
... Server with MVC framework such as Model2 Component-based frameworks ...
... Server with MVC framework such as Model2 Component-based frameworks ...
Lock down security exposures in your Domino web
... Name and password access • User submits name and password, which Domino compares to Person document in a Domino directory or to a record in an LDAP directory • Easy to set up and administer. Just create Person and Group documents. • Problem: Name and password cross network as plain text with every U ...
... Name and password access • User submits name and password, which Domino compares to Person document in a Domino directory or to a record in an LDAP directory • Easy to set up and administer. Just create Person and Group documents. • Problem: Name and password cross network as plain text with every U ...
Web Design and Database Technical Standards
... b. SQL Server Management studio should be installed for 2005. Database Support For Database application support, database standards recommendations are as follows: 1) MS Access 2007/2003 databases a. Files should be located on a shared space. b. Data should not have Social Security numbers or credit ...
... b. SQL Server Management studio should be installed for 2005. Database Support For Database application support, database standards recommendations are as follows: 1) MS Access 2007/2003 databases a. Files should be located on a shared space. b. Data should not have Social Security numbers or credit ...
Hacking, Security, and Information War
... GS69.ppt&ei=EN1jVazjKsbpsAXJ9YGACA&usg=AFQjCNEcKho927WDCTtP4ZvlwbcPcAQ75Q&bvm=bv.93990622,d.b2w ...
... GS69.ppt&ei=EN1jVazjKsbpsAXJ9YGACA&usg=AFQjCNEcKho927WDCTtP4ZvlwbcPcAQ75Q&bvm=bv.93990622,d.b2w ...
Edgenuity SSL Protocols
... SSL encrypts information to create secure transactions online. X.509 certificates and asymmetric cryptography are used to verify the counterparty with whom they are communicating with, and to exchange a symmetric key. The session key is then used to encrypt data being exchanged between the Edgenuity ...
... SSL encrypts information to create secure transactions online. X.509 certificates and asymmetric cryptography are used to verify the counterparty with whom they are communicating with, and to exchange a symmetric key. The session key is then used to encrypt data being exchanged between the Edgenuity ...
Here is the Original File
... the only protocol in use and there are no other security measures currently implemented on the web server. Test Method: Capture client HTTP traffic via a proxy server on a LAN and attempt to read, edit, and forward the HTTP messages to the web server. Once the edited message has been received by the ...
... the only protocol in use and there are no other security measures currently implemented on the web server. Test Method: Capture client HTTP traffic via a proxy server on a LAN and attempt to read, edit, and forward the HTTP messages to the web server. Once the edited message has been received by the ...
Implementing Security for Electronic Commerce
... IN case of downloaded software containing a digital ID, it identifies the software publisher, i.e., it assures that the holder of the software is a trusted name. A certification authority (CA) issues a digital certificate to an organization or an individual when provided with required information. A ...
... IN case of downloaded software containing a digital ID, it identifies the software publisher, i.e., it assures that the holder of the software is a trusted name. A certification authority (CA) issues a digital certificate to an organization or an individual when provided with required information. A ...
Using port pairing to simplify transparent mode
... Using port pairing to simplify transparent mode When you create a port pair, all traffic accepted by one of the paired ports can only exit out the other port. Restricting traffic in this way simplifies your FortiGate configuration because security policies between these interfaces are preconfigured. ...
... Using port pairing to simplify transparent mode When you create a port pair, all traffic accepted by one of the paired ports can only exit out the other port. Restricting traffic in this way simplifies your FortiGate configuration because security policies between these interfaces are preconfigured. ...
security
... decryption key or pass-phrase by searching a large number of possibilities • Remote access to a user’s account allows files to be copied or corrupted. • Hacking used to be a game – now it is done by criminals for theft. ...
... decryption key or pass-phrase by searching a large number of possibilities • Remote access to a user’s account allows files to be copied or corrupted. • Hacking used to be a game – now it is done by criminals for theft. ...
VPNs, PKIs, ISSs, SSLs with narration
... certificate, • The verifier must check the certificate revocation list CRL PKI Server ...
... certificate, • The verifier must check the certificate revocation list CRL PKI Server ...
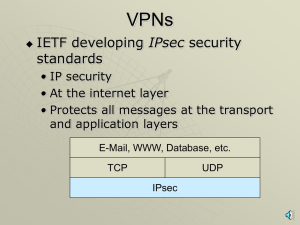
Remote Access - York Technical College
... Symmetric – same key is used to encrypt/decrypt Asymmetric – two keys – public key encrypts the message; the private key decrypts. ...
... Symmetric – same key is used to encrypt/decrypt Asymmetric – two keys – public key encrypts the message; the private key decrypts. ...
Security
... signature of trusted CA (message encrypted by CA’s private key) Receipt of a valid certificate is proof of identity – can be checked at CAs sight www.verisign.com is major player ...
... signature of trusted CA (message encrypted by CA’s private key) Receipt of a valid certificate is proof of identity – can be checked at CAs sight www.verisign.com is major player ...
HTTPS

HTTPS (also called HTTP over TLS, HTTP over SSL, and HTTP Secure) is a protocol for secure communication over a computer network which is widely used on the Internet. HTTPS consists of communication over Hypertext Transfer Protocol (HTTP) within a connection encrypted by Transport Layer Security or its predecessor, Secure Sockets Layer. The main motivation for HTTPS is authentication of the visited website and to protect the privacy and integrity of the exchanged data.In its popular deployment on the internet, HTTPS provides authentication of the website and associated web server with which one is communicating, which protects against man-in-the-middle attacks. Additionally, it provides bidirectional encryption of communications between a client and server, which protects against eavesdropping and tampering with and/or forging the contents of the communication. In practice, this provides a reasonable guarantee that one is communicating with precisely the website that one intended to communicate with (as opposed to an impostor), as well as ensuring that the contents of communications between the user and site cannot be read or forged by any third party.Historically, HTTPS connections were primarily used for payment transactions on the World Wide Web, e-mail and for sensitive transactions in corporate information systems. In the late 2000s and early 2010s, HTTPS began to see widespread use for protecting page authenticity on all types of websites, securing accounts and keeping user communications, identity and web browsing private.