TNS07%20PPP
... In reality, it is often the case that serial links can be clocked considerably faster than parallel links, and they achieve a higher data rate. ...
... In reality, it is often the case that serial links can be clocked considerably faster than parallel links, and they achieve a higher data rate. ...
18. Protocols for QoS Support
... Aggregate for group should reflect resources needed – Take into account common path to different members of group ...
... Aggregate for group should reflect resources needed – Take into account common path to different members of group ...
Full Text - International Journal of Application or Innovation in
... conferencing and chatting. In the practical networks, the internet service providers rely on dynamic routing protocols to update the routing table of routers. These routers are used to control and forward the data. While communicating, the routers must know to which direction it should forward the p ...
... conferencing and chatting. In the practical networks, the internet service providers rely on dynamic routing protocols to update the routing table of routers. These routers are used to control and forward the data. While communicating, the routers must know to which direction it should forward the p ...
Chapter 6 Dynamic Routing
... There are two main types of interior routing protocol Distance Vector Link State (Shortest Path First) They work in different ways but they have the same purposes Discover routes and put the best ones in the routing table Remove routes that are no longer available ...
... There are two main types of interior routing protocol Distance Vector Link State (Shortest Path First) They work in different ways but they have the same purposes Discover routes and put the best ones in the routing table Remove routes that are no longer available ...
SWIM: Scalable Weakly-consistent Infection-style Process Group Membership Protocol
... these group sizes is an increase in either the rate of false failure detections of processes, or the time to detect a failure. [12] identifies the quadratic increase in the message load imposed by such membership protocols as another symptom of the unscalability of traditional protocols for membersh ...
... these group sizes is an increase in either the rate of false failure detections of processes, or the time to detect a failure. [12] identifies the quadratic increase in the message load imposed by such membership protocols as another symptom of the unscalability of traditional protocols for membersh ...
Ch03
... The backbone networks in the Internet can be switched WANs. A switched WAN is a wide area network that covers a large area (a state or a country) and provides access at several points to the users. Inside the network, there is a mesh of pointto-point networks that connects switches. The switches, mu ...
... The backbone networks in the Internet can be switched WANs. A switched WAN is a wide area network that covers a large area (a state or a country) and provides access at several points to the users. Inside the network, there is a mesh of pointto-point networks that connects switches. The switches, mu ...
Underlying Technologies
... The backbone networks in the Internet can be switched WANs. A switched WAN is a wide area network that covers a large area (a state or a country) and provides access at several points to the users. Inside the network, there is a mesh of pointto-point networks that connects switches. The switches, mu ...
... The backbone networks in the Internet can be switched WANs. A switched WAN is a wide area network that covers a large area (a state or a country) and provides access at several points to the users. Inside the network, there is a mesh of pointto-point networks that connects switches. The switches, mu ...
Data Communication and Internet Technology
... The task of this layer is to display the data to be transmitted in a way that they can be handled from a lot of different systems. So computers code a string with ASCII characters, others use Unicode, some for integers the 1-, other the 2-complement. Instead of defining a new transmission syntax and ...
... The task of this layer is to display the data to be transmitted in a way that they can be handled from a lot of different systems. So computers code a string with ASCII characters, others use Unicode, some for integers the 1-, other the 2-complement. Instead of defining a new transmission syntax and ...
Performance Analysis of RIP, EIGRP, and OSPF using
... through interfaces that are connected. The second is the topology table, which contains the aggregation of the routing tables that are gathered from all neighbors that are directly connected. It contains a list of destination networks in the EIGRP routed network and their respective metrics. The thi ...
... through interfaces that are connected. The second is the topology table, which contains the aggregation of the routing tables that are gathered from all neighbors that are directly connected. It contains a list of destination networks in the EIGRP routed network and their respective metrics. The thi ...
Chapter 32 Security in the Internet: IPSec, SSL/TLS, PGP
... Security Fundamentales’, Wiley 2007. ...
... Security Fundamentales’, Wiley 2007. ...
Topic 10 – Protocol Concepts and Internet
... access protocol, to enforce network traffic control • If Y’s network access module has only limited buffer space it needs to exercise flow control over X’s network access module via the transport protocol • Even though Y’s network access module can control its data flow, Y’s application may be vulne ...
... access protocol, to enforce network traffic control • If Y’s network access module has only limited buffer space it needs to exercise flow control over X’s network access module via the transport protocol • Even though Y’s network access module can control its data flow, Y’s application may be vulne ...
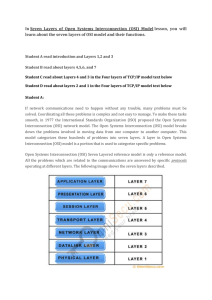
(Seven Layers of Open Systems Interconnection (OSI
... Transport layer. The Internet layer packs data into data packets known as IP datagrams, which contain a source and destination address (logical address or IP address) information that is used to forward the datagrams between hosts and across networks. The Internet layer is also responsible for the r ...
... Transport layer. The Internet layer packs data into data packets known as IP datagrams, which contain a source and destination address (logical address or IP address) information that is used to forward the datagrams between hosts and across networks. The Internet layer is also responsible for the r ...
Chapter 10
... and Microsoft Windows NT. Use WINIPCFG.EXE on Microsoft Windows 95, Microsoft Windows 98, and Microsoft Windows Me. ...
... and Microsoft Windows NT. Use WINIPCFG.EXE on Microsoft Windows 95, Microsoft Windows 98, and Microsoft Windows Me. ...
Chapter 2
... not all members need all sub-flows – if multiple sources are transmitting for same group, receiver may want to select source – In general, QoS needs of different receivers may differ due to equipment, link speed, processing speed/power or other differences ...
... not all members need all sub-flows – if multiple sources are transmitting for same group, receiver may want to select source – In general, QoS needs of different receivers may differ due to equipment, link speed, processing speed/power or other differences ...
Overview of Scalable Networks
... At a minimum the algorithm must specify: – A procedure for passing reachability information about networks to other routers. – A procedure for receiving reachability information from other routers. – A procedure for determining optimal routes based on the reachability information it has and for reco ...
... At a minimum the algorithm must specify: – A procedure for passing reachability information about networks to other routers. – A procedure for receiving reachability information from other routers. – A procedure for determining optimal routes based on the reachability information it has and for reco ...
Powerpoint - Chapter 10
... and Microsoft Windows NT. Use WINIPCFG.EXE on Microsoft Windows 95, Microsoft Windows 98, and Microsoft Windows Me. ...
... and Microsoft Windows NT. Use WINIPCFG.EXE on Microsoft Windows 95, Microsoft Windows 98, and Microsoft Windows Me. ...
A Probabilistically Correct Leader Election Protocol for Large Groups
... unity at small values of K. This convergence is independent of N and is dependent only on the process failure, message delivery failure and view probabilities. If the Ni ’s are the same for all members, each member Mi can calculate the set of members {Mj }i in its view that will satisfy the filter co ...
... unity at small values of K. This convergence is independent of N and is dependent only on the process failure, message delivery failure and view probabilities. If the Ni ’s are the same for all members, each member Mi can calculate the set of members {Mj }i in its view that will satisfy the filter co ...
Data communications and enterprise networking
... consistent structure to each chapter. Each chapter has sections on services, interfaces, functions and protocols. In this part of the subject, we will follow an unconventional approach. Material will be presented in a top-down fashion. Most courses in the subject start with the physics of data trans ...
... consistent structure to each chapter. Each chapter has sections on services, interfaces, functions and protocols. In this part of the subject, we will follow an unconventional approach. Material will be presented in a top-down fashion. Most courses in the subject start with the physics of data trans ...
Sample Chapter
... Another advantage of protocol layering, which cannot be seen in our simple examples but reveals itself when we discuss protocol layering in the Internet, is that communication does not always use only two end systems; there are intermediate systems that need only some layers, but not all layers. If ...
... Another advantage of protocol layering, which cannot be seen in our simple examples but reveals itself when we discuss protocol layering in the Internet, is that communication does not always use only two end systems; there are intermediate systems that need only some layers, but not all layers. If ...
Slide 1
... Three-Way Handshake • TCP is a connection-oriented protocol. • TCP requires connection establishment before data transfer begins. • For a connection to be established or initialized, the two hosts must synchronize their Initial Sequence Numbers (ISNs). • Each side must also receive the INS from the ...
... Three-Way Handshake • TCP is a connection-oriented protocol. • TCP requires connection establishment before data transfer begins. • For a connection to be established or initialized, the two hosts must synchronize their Initial Sequence Numbers (ISNs). • Each side must also receive the INS from the ...
Introduction & Course overview
... provides facilities to organise and synchronise dialogues, i.e. communications that consist of several strands such as audio and video components. ...
... provides facilities to organise and synchronise dialogues, i.e. communications that consist of several strands such as audio and video components. ...
nmea protocol - Stefano Trivellini
... wiring is a shielded twisted pair, with the shield grounded only at the talker. The standard dos not specify the use of a particular connector. Note: The new 0183-HS standard (HS = high speed) introduced in version 3.0 uses a 3-wire interface and a baud rate of 38400. This type of interface is not d ...
... wiring is a shielded twisted pair, with the shield grounded only at the talker. The standard dos not specify the use of a particular connector. Note: The new 0183-HS standard (HS = high speed) introduced in version 3.0 uses a 3-wire interface and a baud rate of 38400. This type of interface is not d ...