Nishkam Ravi - Graduate Computing Resources
... use of dual connectivity on phones that allow communication with local embedded systems as well as the internet. We are also exploring the application of phone sensors, such as camera, to pervasive computing. SmartMessages : The goal of this project is to develop a distributed computing platform for ...
... use of dual connectivity on phones that allow communication with local embedded systems as well as the internet. We are also exploring the application of phone sensors, such as camera, to pervasive computing. SmartMessages : The goal of this project is to develop a distributed computing platform for ...
Affective percept and voluntary action: A hypothesis
... systems. Accordingly, we will distinguish food affective stimuli, esthetic affective stimuli, etc. Different affective stimuli evoke the corresponding affective percepts and the latter can be divided according to the same four criteria. The division of affective percepts according to criteria 1 and ...
... systems. Accordingly, we will distinguish food affective stimuli, esthetic affective stimuli, etc. Different affective stimuli evoke the corresponding affective percepts and the latter can be divided according to the same four criteria. The division of affective percepts according to criteria 1 and ...
Digital Steganalysis: Computational Intelligence Approach
... On the other hand, natural language steganography is the art of using natural language to conceal secret message [27]. It focuses on hiding information in text by using steganography [28-34] and linguistic steganography [35-39]. The crucial requirement for steganography is perceptual and algorithmic ...
... On the other hand, natural language steganography is the art of using natural language to conceal secret message [27]. It focuses on hiding information in text by using steganography [28-34] and linguistic steganography [35-39]. The crucial requirement for steganography is perceptual and algorithmic ...
One-class to multi-class model update using the class
... AI Researcher Symposium (STAIRS). The papers from PAIS are included in this volume, while the papers from STAIRS are published in a separate volume. ECAI 2016 also featured a special topic on Artificial Intelligence for Human Values, with a dedicated track and a public event in the Peace Palace in T ...
... AI Researcher Symposium (STAIRS). The papers from PAIS are included in this volume, while the papers from STAIRS are published in a separate volume. ECAI 2016 also featured a special topic on Artificial Intelligence for Human Values, with a dedicated track and a public event in the Peace Palace in T ...
Artificial Intelligence and Other Approaches to Speech Understanding
... that more knowledge is better. In order to bring more knowledge to bear on specific decisions, integration of knowledge sources is considered essential. For speech, this means, most typically, wanting to use the full inventory of higher-level knowledge, including knowledge of syntax, semantics, doma ...
... that more knowledge is better. In order to bring more knowledge to bear on specific decisions, integration of knowledge sources is considered essential. For speech, this means, most typically, wanting to use the full inventory of higher-level knowledge, including knowledge of syntax, semantics, doma ...
Machine Learning in Computer Vision – Tutorial
... from unlabeled data, ICML, 2007. [6] A. Goldberg, Xi. Zhu, A. Singh, Z. Xu, and R. Nowak. Multi-manifold semi-supervised learning. In Twelfth International Conference on Artificial Intelligence and Statistics ...
... from unlabeled data, ICML, 2007. [6] A. Goldberg, Xi. Zhu, A. Singh, Z. Xu, and R. Nowak. Multi-manifold semi-supervised learning. In Twelfth International Conference on Artificial Intelligence and Statistics ...
Complete Issue
... software engineering paradigm for building intelligent information systems (see [1] and [2] for comprehensive reviews). Some recent application areas include industrial processes [3], agriculture [4] and marine technology [5]. The World Wide Web has increased the reach and accessibility of informati ...
... software engineering paradigm for building intelligent information systems (see [1] and [2] for comprehensive reviews). Some recent application areas include industrial processes [3], agriculture [4] and marine technology [5]. The World Wide Web has increased the reach and accessibility of informati ...
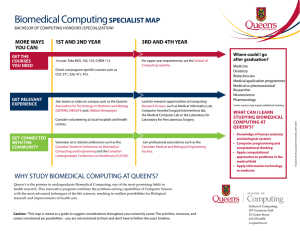
Computing Major Map Addendum
... computer game development while retaining core Software Design requirements that ensure your qualifications in the software industry or graduate studies. Game Development is a creative activity, requiring inspiration to spark new ideas, and collaboration among the many types of professionals require ...
... computer game development while retaining core Software Design requirements that ensure your qualifications in the software industry or graduate studies. Game Development is a creative activity, requiring inspiration to spark new ideas, and collaboration among the many types of professionals require ...
An Overview of the Assisted Cognition Project
... handle the challenges of everyday life. But there is a limit to any person’s capability to provide such help: physical and emotional ‘burnout” of caregivers, often with serious health consequences, is a common phenomena (Hooyman & Kiyak 2001). The goal of Assisted Cognition is to develop computer sy ...
... handle the challenges of everyday life. But there is a limit to any person’s capability to provide such help: physical and emotional ‘burnout” of caregivers, often with serious health consequences, is a common phenomena (Hooyman & Kiyak 2001). The goal of Assisted Cognition is to develop computer sy ...
Lecture 45 - KDD - Kansas State University
... – Topic: Decision Support Systems and Bayesian User Modeling – Title: The Lumiere Project: Bayesian User Modeling for Inferring the Goals and Needs of Software Users – Authors: Horvitz, Breese, Heckerman, Hovel, Rommelse – Presenter: Yuhui (Cathy) Liu ...
... – Topic: Decision Support Systems and Bayesian User Modeling – Title: The Lumiere Project: Bayesian User Modeling for Inferring the Goals and Needs of Software Users – Authors: Horvitz, Breese, Heckerman, Hovel, Rommelse – Presenter: Yuhui (Cathy) Liu ...
Soft Computing: Constituent and Applications of Soft
... programming, or probabilistic reasoning but in all of the associated methodologies, though not necessarily to the same degree. II. Applications of Soft Computing In many cases a problem can be solved most effectively by using Fuzzy Logic, Neural Networks, Evolutionary Computation in combination rath ...
... programming, or probabilistic reasoning but in all of the associated methodologies, though not necessarily to the same degree. II. Applications of Soft Computing In many cases a problem can be solved most effectively by using Fuzzy Logic, Neural Networks, Evolutionary Computation in combination rath ...
IDA: A Cognitive Agent Architecture
... constructs and that ultimately perform all of IDA’s actions. We’ve mentioned the codelets that underlie behaviors. Others underlie slipnet nodes and perform actions necessary for constructing IDA’s understanding of an email message or of a database screen (Zhang et al 1998). Still other codelets wil ...
... constructs and that ultimately perform all of IDA’s actions. We’ve mentioned the codelets that underlie behaviors. Others underlie slipnet nodes and perform actions necessary for constructing IDA’s understanding of an email message or of a database screen (Zhang et al 1998). Still other codelets wil ...
Aladdin Ayesh - Curriculum Vitae
... I have gained grants from various sources including HEFCE, EPSRC, EU and Royal Society mounting nearly to £300K. In addition, I have gained support in kind from institutes and industrial partners. I have also had wide international collaborations with Universities and researchers in Germany, France, ...
... I have gained grants from various sources including HEFCE, EPSRC, EU and Royal Society mounting nearly to £300K. In addition, I have gained support in kind from institutes and industrial partners. I have also had wide international collaborations with Universities and researchers in Germany, France, ...
Book Recommending Using Text Categorization
... binary prediction on Data Set 1, the difference between any of the modelsis not statistically significant. Though from about 55 examples to about 150 examples, the Binary model outperforms both others by a statistically significant amount. Although even in this early region, the statistical signific ...
... binary prediction on Data Set 1, the difference between any of the modelsis not statistically significant. Though from about 55 examples to about 150 examples, the Binary model outperforms both others by a statistically significant amount. Although even in this early region, the statistical signific ...
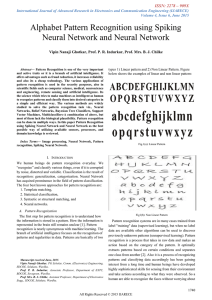
Alphabet Pattern Recognition using Spiking Neural
... and active traits or it is a branch of artificial intelligence. It offers advantages such as fraud reduction, it increases reliability and also its a cheap technology. The various applications of pattern recognition is used in the security purposes, also in scientific fields such as computer science ...
... and active traits or it is a branch of artificial intelligence. It offers advantages such as fraud reduction, it increases reliability and also its a cheap technology. The various applications of pattern recognition is used in the security purposes, also in scientific fields such as computer science ...
Information Extraction
... strings that refer to the same entity and then replacing sets of equivalent strings with canonical entity names. Another approach to handling heterogeneity is to mine”soft matching” rules directly from the “dirty” data extracted from text. ...
... strings that refer to the same entity and then replacing sets of equivalent strings with canonical entity names. Another approach to handling heterogeneity is to mine”soft matching” rules directly from the “dirty” data extracted from text. ...
Future Computing and Robotics: A Report from the HBP Foresight Lab
... not only embody previously unimaginable miniaturised computing powers, but link wirelessly into the internet and can connect to multiple previously dumb devices, such as home heating systems and domestic machinery, guide us through unfamiliar territory via connections with geographic information sys ...
... not only embody previously unimaginable miniaturised computing powers, but link wirelessly into the internet and can connect to multiple previously dumb devices, such as home heating systems and domestic machinery, guide us through unfamiliar territory via connections with geographic information sys ...