BLAST Command Line Applications User Manual
... 4.2.1 best_hit_overhang: Overhang value for Best-Hit algorithm. For more details, see the section Best-Hits filtering algorithm. 4.2.2 best_hit_score_edge: Score edge value for Best-Hit algorithm. For more details, see the section Best-Hits filtering algorithm. 4.2.3 db: File name of BLAST database ...
... 4.2.1 best_hit_overhang: Overhang value for Best-Hit algorithm. For more details, see the section Best-Hits filtering algorithm. 4.2.2 best_hit_score_edge: Score edge value for Best-Hit algorithm. For more details, see the section Best-Hits filtering algorithm. 4.2.3 db: File name of BLAST database ...
HPE Recovery Manager Central 4.0.0 for Oracle User
... User control icons................................................................................................................... 28 ...
... User control icons................................................................................................................... 28 ...
Greenplum Database 4.3 Installation Guide
... The master is the entry point to the Greenplum Database system. It is the database server process that accepts client connections and processes the SQL commands that system users issue. Users connect to Greenplum Database through the master using a PostgreSQL-compatible client program such as psql o ...
... The master is the entry point to the Greenplum Database system. It is the database server process that accepts client connections and processes the SQL commands that system users issue. Users connect to Greenplum Database through the master using a PostgreSQL-compatible client program such as psql o ...
Administering ArcSDE database servers - ArcGIS Resources
... Topics are originally created as Web documents, but have been published here to group them together, format them, and make it possible for you to print them all at once. Because these topics are Web help topics, they contain many links. Links to information contained in topics inside this PDF should ...
... Topics are originally created as Web documents, but have been published here to group them together, format them, and make it possible for you to print them all at once. Because these topics are Web help topics, they contain many links. Links to information contained in topics inside this PDF should ...
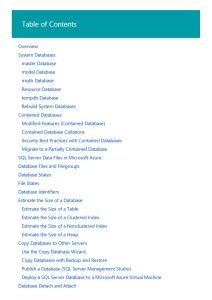
Databases | Microsoft Docs
... contains a collection of rows, also referred to as records or tuples, and columns, also referred to as attributes. Each column in the table is designed to store a certain type of information, for example, dates, names, dollar amounts, and numbers. ...
... contains a collection of rows, also referred to as records or tuples, and columns, also referred to as attributes. Each column in the table is designed to store a certain type of information, for example, dates, names, dollar amounts, and numbers. ...
Data-tier Applications | Microsoft Docs
... the package, the extract/export log will contain a summary of the issues via the messages noted above. This is to warn the user of potential data deployment issues with the package they created. The user will also see the following summary message in the log: These limitations do not affect the fide ...
... the package, the extract/export log will contain a summary of the issues via the messages noted above. This is to warn the user of potential data deployment issues with the package they created. The user will also see the following summary message in the log: These limitations do not affect the fide ...
Teradata QueryGrid: Teradata Database-to
... The information contained in this document is provided on an "as-is" basis, without warranty of any kind, either express or implied, including the implied warranties of merchantability, fitness for a particular purpose, or non-infringement. Some jurisdictions do not allow the exclusion of implied wa ...
... The information contained in this document is provided on an "as-is" basis, without warranty of any kind, either express or implied, including the implied warranties of merchantability, fitness for a particular purpose, or non-infringement. Some jurisdictions do not allow the exclusion of implied wa ...
Data Definition guide
... Defense, then it is delivered with Restricted Rights and the following legend is applicable: Restricted Rights Legend Use, duplication, or disclosure by the Government is subject to restrictions as set forth in subparagraph (c)(1)(ii) of DFARS 252.227-7013, Rights in Technical Data and Computer Soft ...
... Defense, then it is delivered with Restricted Rights and the following legend is applicable: Restricted Rights Legend Use, duplication, or disclosure by the Government is subject to restrictions as set forth in subparagraph (c)(1)(ii) of DFARS 252.227-7013, Rights in Technical Data and Computer Soft ...
About Log Shipping (SQL Server) | Microsoft Docs
... 1. Initialize the secondary database by restoring a full backup of the primary database on the secondary server. 2. On the primary server, execute sp_add_log_shipping_primary_database to add a primary database. The stored procedure returns the backup job ID and primary ID. 3. On the primary server, ...
... 1. Initialize the secondary database by restoring a full backup of the primary database on the secondary server. 2. On the primary server, execute sp_add_log_shipping_primary_database to add a primary database. The stored procedure returns the backup job ID and primary ID. 3. On the primary server, ...
JDBC Tutorial (PDF Version)
... Install Java ................................................................................................................................................ 8 Install Database ........................................................................................................................... ...
... Install Java ................................................................................................................................................ 8 Install Database ........................................................................................................................... ...
Data Definition Guide - Embarcadero Technologies Product
... Multiple privileges and multiple grantees . . . . . . 12-6 Granting multiple privileges . . . . . . . . . . . 12-6 Granting all privileges . . . . . . . . . . . . . . 12-6 Granting privileges to multiple users . . . . . . 12-7 Granting privileges to a list of users . . . . . 12-7 Granting privileges ...
... Multiple privileges and multiple grantees . . . . . . 12-6 Granting multiple privileges . . . . . . . . . . . 12-6 Granting all privileges . . . . . . . . . . . . . . 12-6 Granting privileges to multiple users . . . . . . 12-7 Granting privileges to a list of users . . . . . 12-7 Granting privileges ...
SQL Server - Toolbox.com
... covers the important topics of backup, recovery and high availability with Microsoft SQL Server. This is an exciting release that will fill an important gap in the Database Administration book market. Microsoft SQL Server is being increasingly used for large mission critical enterprise systems, whic ...
... covers the important topics of backup, recovery and high availability with Microsoft SQL Server. This is an exciting release that will fill an important gap in the Database Administration book market. Microsoft SQL Server is being increasingly used for large mission critical enterprise systems, whic ...
Performance Modeling and Access Methods for Temporal
... time-varying aspects of the real world. The need for temporal support has been recognized for over ten years, and recent progress in secondary storage technology is making such support practically feasible. There are three distinct kinds of time in databases: transaction time, valid time, and user-d ...
... time-varying aspects of the real world. The need for temporal support has been recognized for over ten years, and recent progress in secondary storage technology is making such support practically feasible. There are three distinct kinds of time in databases: transaction time, valid time, and user-d ...
Content Manager 8.3
... Resolving the problem Set DB2_JDBC_DRIVER_PATH = d:\ibm\sqllib\java for allscopes Check the database provider and data source configuration to see if the WebSphere Application Server JDBC driver path system variable is used in the classpath in the JDBC Provider and ensure the variable is set for the ...
... Resolving the problem Set DB2_JDBC_DRIVER_PATH = d:\ibm\sqllib\java for allscopes Check the database provider and data source configuration to see if the WebSphere Application Server JDBC driver path system variable is used in the classpath in the JDBC Provider and ensure the variable is set for the ...
KEMI-TORNIO UNIVERSITY OF APPLIED
... There are plenty of articles can be found in Internet about comparison between PostgreSQL and MySQL. They both are technique strong, open sources database and many supporters. They both have large numbers of users, their supporters have listed their benefits against each other. It is impossible to c ...
... There are plenty of articles can be found in Internet about comparison between PostgreSQL and MySQL. They both are technique strong, open sources database and many supporters. They both have large numbers of users, their supporters have listed their benefits against each other. It is impossible to c ...
Database Systems for Mangement
... This book provides an introduction to management information systems with an emphasis on special technologies and techniques for designing and managing organizational database systems. After studying the material in this book, you should have mastered at least the basic principles underlying informa ...
... This book provides an introduction to management information systems with an emphasis on special technologies and techniques for designing and managing organizational database systems. After studying the material in this book, you should have mastered at least the basic principles underlying informa ...
DB2 Command Line Processor Commands - McGraw-Hill
... If an add node operation fails while creating a database partition locally, it enters a cleanup phase, in which it locally drops all databases that were created. This means that the database partitions are removed only from the node being added (that is, the local node). Existing database partitions ...
... If an add node operation fails while creating a database partition locally, it enters a cleanup phase, in which it locally drops all databases that were created. This means that the database partitions are removed only from the node being added (that is, the local node). Existing database partitions ...
Aster Client Guide - Information Products
... The information contained in this document may contain references or cross-references to features, functions, products, or services that are not announced or available in your country. Such references do not imply that Teradata Corporation intends to announce such features, functions, products, or s ...
... The information contained in this document may contain references or cross-references to features, functions, products, or services that are not announced or available in your country. Such references do not imply that Teradata Corporation intends to announce such features, functions, products, or s ...
Puredata Systems for Analytics: Concurrency and Workload
... performance is directly linked to the allocation of system resources on a database management system. The heart of the Netezza appliance, Field-Programmable Gate Array (FPGA) plays a key role in boosting the overall performance of a server. I/O operations are always a bottleneck in any database serv ...
... performance is directly linked to the allocation of system resources on a database management system. The heart of the Netezza appliance, Field-Programmable Gate Array (FPGA) plays a key role in boosting the overall performance of a server. I/O operations are always a bottleneck in any database serv ...
Database Tuning Principles
... discusses the principles of concurrency control, recovery, and query processing to the extent needed. If you are using this book as a primary text for a portion of your classes, we can provide you with lecture notes if you e-mail us at [email protected] or [email protected]. ...
... discusses the principles of concurrency control, recovery, and query processing to the extent needed. If you are using this book as a primary text for a portion of your classes, we can provide you with lecture notes if you e-mail us at [email protected] or [email protected]. ...
Enterprise Option for SAP R/3 for Oracle Guide
... Among the options Arcserve Backup offers is the Arcserve Backup Enterprise Option for SAP R/3 for Oracle (the option). This option helps you manage Oracle databases in your SAP R/3 for Oracle environment by letting you remotely manage backups, schedule your backups, and back up to a wide array of me ...
... Among the options Arcserve Backup offers is the Arcserve Backup Enterprise Option for SAP R/3 for Oracle (the option). This option helps you manage Oracle databases in your SAP R/3 for Oracle environment by letting you remotely manage backups, schedule your backups, and back up to a wide array of me ...
SKF @ptitude Analyst Installation
... technology that created an adverse impact on the operation, functioning, or performance of the Software. ...
... technology that created an adverse impact on the operation, functioning, or performance of the Software. ...
Module 2: Managing and Monitoring Dynamic Host
... Non-Microsoft DHCP server software does not include the authorization feature that is included in Windows 2000 and Windows Server 2003 ...
... Non-Microsoft DHCP server software does not include the authorization feature that is included in Windows 2000 and Windows Server 2003 ...
JADE Database Administration Guide
... Jade Software Corporation Limited cannot accept any financial or other responsibilities that may be the result of your use of this information or software material, including direct, indirect, special or consequential damages, or loss of profits. There are no warranties extended or granted by this ...
... Jade Software Corporation Limited cannot accept any financial or other responsibilities that may be the result of your use of this information or software material, including direct, indirect, special or consequential damages, or loss of profits. There are no warranties extended or granted by this ...