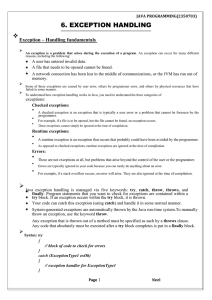
EXCEPTION HANDLING Exception
... Caused by bad array indexes Caused when a program tries to store the wrong type of data in an array Caused by an attempt to access a nonexistent file Caused by general I/O failures, such as inability to read from a file Caused by referencing a null object Caused when a conversion between strings and ...
... Caused by bad array indexes Caused when a program tries to store the wrong type of data in an array Caused by an attempt to access a nonexistent file Caused by general I/O failures, such as inability to read from a file Caused by referencing a null object Caused when a conversion between strings and ...
Constructor Methods
... a group of objects. Now in OOP we do not use the term nouns and verbs. You may hear many different terms being used but currently the more popular terms are attributes and methods. Attributes store program information, which is like a noun. Methods perform some actions on the information, which is l ...
... a group of objects. Now in OOP we do not use the term nouns and verbs. You may hear many different terms being used but currently the more popular terms are attributes and methods. Attributes store program information, which is like a noun. Methods perform some actions on the information, which is l ...
JBoss and Aspects for Middlware Components
... sometimes users want to integrate with it Users want “hooks” in different places of the application so that they can trigger things specific to their particular deployment If hooks are provided using OOP, it becomes tough to redesign or change API. By using pointcuts, the application designer ...
... sometimes users want to integrate with it Users want “hooks” in different places of the application so that they can trigger things specific to their particular deployment If hooks are provided using OOP, it becomes tough to redesign or change API. By using pointcuts, the application designer ...
Efficient and Reliable Lock-Free Memory Reclamation Based on
... For this reason, all threads’ deletion lists are accessible for reading by any thread. When the length of the deletion list reaches a certain threshold (THRESHOLD_1) the thread performs a clean-up of all the nodes in its deletion list. If all of the nodes are still prevented from reclamation, this m ...
... For this reason, all threads’ deletion lists are accessible for reading by any thread. When the length of the deletion list reaches a certain threshold (THRESHOLD_1) the thread performs a clean-up of all the nodes in its deletion list. If all of the nodes are still prevented from reclamation, this m ...
Chapter 2--Basic Data Structures
... – object replaceAtRank(integer r, object o): replace the element at rank with o and return the old element – insertAtRank(integer r, object o): insert a new element o to have rank r – object removeAtRank(integer r): removes and returns the element at rank r Additional operations size() and isEmpty() ...
... – object replaceAtRank(integer r, object o): replace the element at rank with o and return the old element – insertAtRank(integer r, object o): insert a new element o to have rank r – object removeAtRank(integer r): removes and returns the element at rank r Additional operations size() and isEmpty() ...
Generalized Symbolic Execution for Model Checking and Testing
... correctness; this builds on our previous work on the Korat framework [2] for specification-based testing. We also support partial correctness properties given as assertions in the program and temporal specifications. The main contributions of our work are: – Providing a two-fold generalization of sy ...
... correctness; this builds on our previous work on the Korat framework [2] for specification-based testing. We also support partial correctness properties given as assertions in the program and temporal specifications. The main contributions of our work are: – Providing a two-fold generalization of sy ...
Savitch Java Ch. 9 - University of Scranton: Computing Sciences Dept.
... » therefor any catch block that catches IOExceptions also catches FileNotFoundExceptions » errors can be isolated better if they have different messages » so create different catch blocks for each exception type » put the more specific one first (the derived one) so it catches specifically file-not- ...
... » therefor any catch block that catches IOExceptions also catches FileNotFoundExceptions » errors can be isolated better if they have different messages » so create different catch blocks for each exception type » put the more specific one first (the derived one) so it catches specifically file-not- ...
Exception
... a part of the program specifically written for the exception » also called handling an exception The normal case is handled in a try block The exceptional case is handled in a catch block The catch block takes a parameter of type Exception » it is called the catch-block parameter » e is a commonly u ...
... a part of the program specifically written for the exception » also called handling an exception The normal case is handled in a try block The exceptional case is handled in a catch block The catch block takes a parameter of type Exception » it is called the catch-block parameter » e is a commonly u ...
Catch block
... When a method might throw an exception but does not have a catch block to catch it, usually the exception class must be listed in the throws-clause for the method A try block may be followed by more than one catch block » more than one catch block may be capable of handling the exception » the first ...
... When a method might throw an exception but does not have a catch block to catch it, usually the exception class must be listed in the throws-clause for the method A try block may be followed by more than one catch block » more than one catch block may be capable of handling the exception » the first ...
Lecture 5 (linked lists and vectors)
... We compare the incremental strategy and the doubling strategy by analyzing the total time T(n) needed to perform a series of n push operations We assume that we start with an empty stack represented by an array of size 1 We call amortized time of a push operation the average time taken by a push ove ...
... We compare the incremental strategy and the doubling strategy by analyzing the total time T(n) needed to perform a series of n push operations We assume that we start with an empty stack represented by an array of size 1 We call amortized time of a push operation the average time taken by a push ove ...
CSci 161
... Random class and its nextInt(int n) method c) sort the array, using Arrays.sort() d) display the array, using Arrays.toString() to create something that is displayable CSci 161 ...
... Random class and its nextInt(int n) method c) sort the array, using Arrays.sort() d) display the array, using Arrays.toString() to create something that is displayable CSci 161 ...
Text files
... » BufferedReader has no methods to read numbers directly, so read numbers as Strings and then convert them » read a char with read Java: an Introduction to Computer Science & Programming - Walter Savitch ...
... » BufferedReader has no methods to read numbers directly, so read numbers as Strings and then convert them » read a char with read Java: an Introduction to Computer Science & Programming - Walter Savitch ...
Built-in Coloring for Highly-Concurrent Doubly
... rely on strong primitives [15], e.g., CAS (compare and swap) and its multi-location variant, k CAS. Lock-free implementations are often complex and hard to get right; even for relatively simple, key data structures, like deques, they suffer from signi£cant drawbacks: Some implementations may contai ...
... rely on strong primitives [15], e.g., CAS (compare and swap) and its multi-location variant, k CAS. Lock-free implementations are often complex and hard to get right; even for relatively simple, key data structures, like deques, they suffer from signi£cant drawbacks: Some implementations may contai ...
EJB Architecture - classes.cs.uchicago.edu
... architecture for building distributed object-oriented business applications in the Java Programming Language.” Sun EJB Specification 1.1 • “Application developers will not have to understand lowlevel transaction and state management details, multithreading, connection pooling and other complex low-l ...
... architecture for building distributed object-oriented business applications in the Java Programming Language.” Sun EJB Specification 1.1 • “Application developers will not have to understand lowlevel transaction and state management details, multithreading, connection pooling and other complex low-l ...
Runtime Translation of the Java Bytecode to OpenCL and GPU
... The serialized data and the heap space for dynamic memory allocation are provided in a single buffer referred as the OpenCL global memory space or heap. All data references are converted in offsets in this heap. The kernel accesses data with a heap based indexing, similar with an array access. This ...
... The serialized data and the heap space for dynamic memory allocation are provided in a single buffer referred as the OpenCL global memory space or heap. All data references are converted in offsets in this heap. The kernel accesses data with a heap based indexing, similar with an array access. This ...
A Comparison of Dictionary Implementations
... Hash tables were first suggested by H. P. Luhn, in an internal IBM memo in 1953 [?]. Hash tables use a hash function h : K → V to compute the location of a given value v in a table. The function is called a ’hash function’ because it ’mixes’ the data of its input, so that the output for similar inpu ...
... Hash tables were first suggested by H. P. Luhn, in an internal IBM memo in 1953 [?]. Hash tables use a hash function h : K → V to compute the location of a given value v in a table. The function is called a ’hash function’ because it ’mixes’ the data of its input, so that the output for similar inpu ...
24slide - KSU Web Home
... Implementing Stacks and Queues Using an array list to implement Stack Use a linked list to implement Queue Since the insertion and deletion operations on a stack are made only at the end of the stack, using an array list to implement a stack is more efficient than a linked list. Since deletions are ...
... Implementing Stacks and Queues Using an array list to implement Stack Use a linked list to implement Queue Since the insertion and deletion operations on a stack are made only at the end of the stack, using an array list to implement a stack is more efficient than a linked list. Since deletions are ...
CSE 331. Computer Organization
... The system is not asked to retrieve tuples based on information about their storage location; rather, it has to find all tuples the attribute values of which fulfill certain conditions – associative access. ...
... The system is not asked to retrieve tuples based on information about their storage location; rather, it has to find all tuples the attribute values of which fulfill certain conditions – associative access. ...
Self Adjusting Contention Friendly Concurrent Binary Search Tree
... Moreover, as the re-structuring of the tree creates the accessive contention, separating this process from abstract modification produces less contention during concurrency and the lazy splaying resolves the standard splaying root-bottleneck, making this technique efficient, scalabale and highly con ...
... Moreover, as the re-structuring of the tree creates the accessive contention, separating this process from abstract modification produces less contention during concurrency and the lazy splaying resolves the standard splaying root-bottleneck, making this technique efficient, scalabale and highly con ...
24slide - KSU Web Home
... still use array to implement dynamic data structures. The trick is to create a new larger array to replace the current array if the current array cannot hold new elements in the list. Initially, an array, say data of Object[] type, is created with a default size. When inserting a new element into th ...
... still use array to implement dynamic data structures. The trick is to create a new larger array to replace the current array if the current array cannot hold new elements in the list. Initially, an array, say data of Object[] type, is created with a default size. When inserting a new element into th ...
Simultaneous Pipelining in QPipe: Exploiting Work Sharing
... overlap, e.g., they access the same relations on disk, compute similar aggregates, or share intermediate results. Unfortunately, run-time sharing in modern database engines is limited by the paradigm of invoking an independent set of operator instances per query, potentially missing sharing opportun ...
... overlap, e.g., they access the same relations on disk, compute similar aggregates, or share intermediate results. Unfortunately, run-time sharing in modern database engines is limited by the paradigm of invoking an independent set of operator instances per query, potentially missing sharing opportun ...
Chapter 6 - Gettysburg College Computer Science
... Java: an Introduction to Computer Science & Programming - Walter Savitch ...
... Java: an Introduction to Computer Science & Programming - Walter Savitch ...
The SprayList: A Scalable Relaxed Priority Queue
... average length of a Spray with the expected number of thread collisions on elements in the bottom list. We now give an overview of the parameter choices for our implementation. For simplicity, consider a SkipList on which no removes have yet occurred due to Spray operations. We assume that the data ...
... average length of a Spray with the expected number of thread collisions on elements in the bottom list. We now give an overview of the parameter choices for our implementation. For simplicity, consider a SkipList on which no removes have yet occurred due to Spray operations. We assume that the data ...