Lecture 6
... Polymorphism and Dynamic Binding Polymorphism refers to the ability to determine at runtime which code to run, given multiple methods with the same name but different operations in the same class or in different classes. This ability is also known as dynamic binding. ...
... Polymorphism and Dynamic Binding Polymorphism refers to the ability to determine at runtime which code to run, given multiple methods with the same name but different operations in the same class or in different classes. This ability is also known as dynamic binding. ...
Advanced Object Oriented Systems
... for a given method invocation, it is called the most specific method • If a most specific method cannot be found, there is ambiguity and the compiler reports an error. (There are a few esoteric exceptions to this last rule) ...
... for a given method invocation, it is called the most specific method • If a most specific method cannot be found, there is ambiguity and the compiler reports an error. (There are a few esoteric exceptions to this last rule) ...
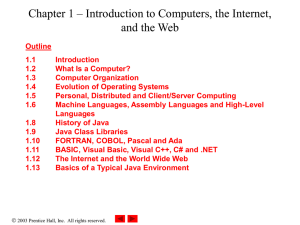
Chapter 1 – Introduction to Computers, the Internet, and the Web
... – Reusable software components that model real-world items – Look all around you • People, animals, plants, cars, etc. ...
... – Reusable software components that model real-world items – Look all around you • People, animals, plants, cars, etc. ...
Object Oriented Programming
... Although this seems just like an ordinary variable declaration, this is much more. The variable i now represents an instance of the counter type; a counter object. We can now communicate with this object by calling it's methods, for example we can set the counter to the value '50' by calling i.Initi ...
... Although this seems just like an ordinary variable declaration, this is much more. The variable i now represents an instance of the counter type; a counter object. We can now communicate with this object by calling it's methods, for example we can set the counter to the value '50' by calling i.Initi ...
CIS 265/506 Midterm Review
... 5. Comparing Strings: == vs. equals method; other String methods: charAt, compareTo, indexOf, concat, toUpper, toLower, substring (2 versions of this method). 6. Creating objects using new operator and constructor. 7. User-defined methods – methods have return type and parameters; primitive types ar ...
... 5. Comparing Strings: == vs. equals method; other String methods: charAt, compareTo, indexOf, concat, toUpper, toLower, substring (2 versions of this method). 6. Creating objects using new operator and constructor. 7. User-defined methods – methods have return type and parameters; primitive types ar ...
MODULE 5[1]
... The data hiding provides more security to data and its maintenance. The inheritance enables better and optimal organization of data in an hierarchical model. The program development can concentrate more on message passing between the objects rather than on the general code. The OOP paradigm is a mod ...
... The data hiding provides more security to data and its maintenance. The inheritance enables better and optimal organization of data in an hierarchical model. The program development can concentrate more on message passing between the objects rather than on the general code. The OOP paradigm is a mod ...
Introduction: chap. 1 - NYU Computer Science Department
... C was originally created in 1972 by Dennis Ritchie at Bell Labs= C is a relatively low-level high-level language; i.e. deals with numbers, characters, and memory addresses ...
... C was originally created in 1972 by Dennis Ritchie at Bell Labs= C is a relatively low-level high-level language; i.e. deals with numbers, characters, and memory addresses ...
Week 7 - Software Tools
... ! People are notoriously bad at predicting the most computationally expensive parts of a program " Rule of thumb (Pareto Principle): 80% of the time is spent in 20% of the code " No use improving the code that isn’t executed often " How do you determine where your program is spending its time? ...
... ! People are notoriously bad at predicting the most computationally expensive parts of a program " Rule of thumb (Pareto Principle): 80% of the time is spent in 20% of the code " No use improving the code that isn’t executed often " How do you determine where your program is spending its time? ...
Slides
... • Identified 23 classic software design patterns in OO programming • More than 1/2 million copies sold in 14 languages ...
... • Identified 23 classic software design patterns in OO programming • More than 1/2 million copies sold in 14 languages ...
Programming and Problem Solving with Java: Chapter 1
... • Know the three phases of the software life cycle • Understand what an algorithm is • Learn what a high-level programming language is • Understand the difference between machine code and Bytecode ...
... • Know the three phases of the software life cycle • Understand what an algorithm is • Learn what a high-level programming language is • Understand the difference between machine code and Bytecode ...
Our Graphics Environment
... Hardware • CPU • Modern CPUs are multicore processors that support programs that can run at the same time as other programs • The level of parallelism (as enabled by the number of CPU cores) is relatively low ...
... Hardware • CPU • Modern CPUs are multicore processors that support programs that can run at the same time as other programs • The level of parallelism (as enabled by the number of CPU cores) is relatively low ...
Series 90-30 Programming with Logicmaster Part 1
... Describe the Programmable Controller components & the functional operation of a PLC. Install Logicmaster 90 software and Series 90-30 hardware. Configure the power supply, CPU, input/output modules, and optional modules into the Series 90-30 system. Describe the operation and use of the Series 90-30 ...
... Describe the Programmable Controller components & the functional operation of a PLC. Install Logicmaster 90 software and Series 90-30 hardware. Configure the power supply, CPU, input/output modules, and optional modules into the Series 90-30 system. Describe the operation and use of the Series 90-30 ...
lecture9
... System Programming Languages • System programming languages replaced assembly languages – Benefits: » The compiler hides unnecessary details, so these languages have a higher level of abstraction, increasing productivity » They are strongly typed, i.e. meaning of information is specified before its ...
... System Programming Languages • System programming languages replaced assembly languages – Benefits: » The compiler hides unnecessary details, so these languages have a higher level of abstraction, increasing productivity » They are strongly typed, i.e. meaning of information is specified before its ...
lecture 1
... • Basic hardware and software concepts. • The different types of programming languages. • Which programming languages are most widely used. • The history of the Visual C# programming language. • Some basics of object technology. ...
... • Basic hardware and software concepts. • The different types of programming languages. • Which programming languages are most widely used. • The history of the Visual C# programming language. • Some basics of object technology. ...
Optimizing Matrix Stability and Controllability
... of the JDK, make using Java much more convenient. We will use Eclipse (free, from IBM). • The JDK compiles programs to “Java byte code”, which are then executed on the Java Virtual Machine by translating to “native” machine language. ...
... of the JDK, make using Java much more convenient. We will use Eclipse (free, from IBM). • The JDK compiles programs to “Java byte code”, which are then executed on the Java Virtual Machine by translating to “native” machine language. ...
Railway Foundation - Sheffield Hallam University
... • Other devices include hardware timers and counters • Digital data can also be in a serial format (e.g. RS232, RS 485 are serial standards) ...
... • Other devices include hardware timers and counters • Digital data can also be in a serial format (e.g. RS232, RS 485 are serial standards) ...
Lecture slides
... Non-template class topics • java.lang.Cloneable • Marker interface that says (to humans and tools), “Objects of this interface provide a public clone() method. • See java.lang.Object.clone() • clone() returns a new copy of its object. • Its implementation often uses a private constructor to build t ...
... Non-template class topics • java.lang.Cloneable • Marker interface that says (to humans and tools), “Objects of this interface provide a public clone() method. • See java.lang.Object.clone() • clone() returns a new copy of its object. • Its implementation often uses a private constructor to build t ...
Programming Development Environment
... Either in a general purpose programming language Or a special programming language controlling a connected board Can be external or inserted internal into backplane of a computer But you will program (verb) eventually ...
... Either in a general purpose programming language Or a special programming language controlling a connected board Can be external or inserted internal into backplane of a computer But you will program (verb) eventually ...
COP2212 Intro. to Programming in C
... – A partially completed design that can be extended to solve a problem in a domain • Horizontal vs. vertical – Example: Microsoft’s MFC for Windows apps using C++ ...
... – A partially completed design that can be extended to solve a problem in a domain • Horizontal vs. vertical – Example: Microsoft’s MFC for Windows apps using C++ ...
The Program Life Cycle. - Concordia University Wisconsin
... 1) We need to understand the idea / concept of a data structure before we can implement it. 2) We then have the freedom to implement the ADT in the best way (e.g. most efficient / most flexible) for a given application. 3) We can focus on a standardized interface independent of implementation. ...
... 1) We need to understand the idea / concept of a data structure before we can implement it. 2) We then have the freedom to implement the ADT in the best way (e.g. most efficient / most flexible) for a given application. 3) We can focus on a standardized interface independent of implementation. ...
Conventions for Arithmetic Operations in Java
... defend the omission of overloaded operators from Java on the grounds that it prevents a misguided programmer from defining operators with bizarre or misleading semantics. Presumably that’s what Flanagan5 and others in the “Java community” are worrying about. But that’s no concern for serious softwar ...
... defend the omission of overloaded operators from Java on the grounds that it prevents a misguided programmer from defining operators with bizarre or misleading semantics. Presumably that’s what Flanagan5 and others in the “Java community” are worrying about. But that’s no concern for serious softwar ...


![MODULE 5[1]](http://s1.studyres.com/store/data/009692512_1-2a2bcf0a603b7a1faa77dac782242019-300x300.png)