Sams Teach Yourself Beginning Programming in
... Use of a term in this book should not be regarded as affecting the validity of any trademark or service mark. ...
... Use of a term in this book should not be regarded as affecting the validity of any trademark or service mark. ...
Chapter 1
... • A program is a set of instructions a computer follows in order to perform a task. • A programming language is a special language used to write computer programs. • A computer program is a set of instructions that enable the computer to solve a problem or perform a task. • Collectively, these instr ...
... • A program is a set of instructions a computer follows in order to perform a task. • A programming language is a special language used to write computer programs. • A computer program is a set of instructions that enable the computer to solve a problem or perform a task. • Collectively, these instr ...
Slide 1
... In C++ standard library, there is a set of vector-based algorithms. You can think of a vector as an array. The algorithms just need a range (begin, end). Note where end is. ...
... In C++ standard library, there is a set of vector-based algorithms. You can think of a vector as an array. The algorithms just need a range (begin, end). Note where end is. ...
Arrays - CIS @ Temple University
... Summary • Entire array can be passed as parameter to a method • Method return value can be an array • Partially filled array usually stores values in initial segment, use an int to track how many are used • Privacy leak caused by returning array corresponding to private instance variable JAVA: An I ...
... Summary • Entire array can be passed as parameter to a method • Method return value can be an array • Partially filled array usually stores values in initial segment, use an int to track how many are used • Privacy leak caused by returning array corresponding to private instance variable JAVA: An I ...
Lecture slides for Chapter 9
... Reference counts • Cycles defeat reference counts – Cyclic reference boosts the count of each member plus one member has an outside reference. – If outside reference goes away, cycle still has references internally but no access from anywhere else in program – Allowing cycles is an open issue CSE 3 ...
... Reference counts • Cycles defeat reference counts – Cyclic reference boosts the count of each member plus one member has an outside reference. – If outside reference goes away, cycle still has references internally but no access from anywhere else in program – Allowing cycles is an open issue CSE 3 ...
02history - Department of Computer Science and Electrical
... Ada Contributions: 1. Packages - support for data abstraction 2. Exception handling - elaborate 3. Generic program units 4. Concurrency - through the tasking model Comments: • Competitive design • Included all that was then known about software engineering and language design • First compilers were ...
... Ada Contributions: 1. Packages - support for data abstraction 2. Exception handling - elaborate 3. Generic program units 4. Concurrency - through the tasking model Comments: • Competitive design • Included all that was then known about software engineering and language design • First compilers were ...
TDC561 Network Programming
... » output doesn't end up in another session. » ignore SIGINT (such as terminal generated signals - ^C – since is not associated with any terminal uses » file system » central logging facility – daemons should close all unnecessary descriptors » often including stdin, stdout, stderr. – daemons often c ...
... » output doesn't end up in another session. » ignore SIGINT (such as terminal generated signals - ^C – since is not associated with any terminal uses » file system » central logging facility – daemons should close all unnecessary descriptors » often including stdin, stdout, stderr. – daemons often c ...
Security in Java: Real or Decaf? - University of Virginia, Department
... express certain computations considered insecure. A few attempt to do this: PLAN, packet filters ...
... express certain computations considered insecure. A few attempt to do this: PLAN, packet filters ...
GUI Construction
... should be implemented by all the classes using this interface. The invokeLater method schedule the GUI creations taks to execute the run method a synchronously by the event-handling thread after all the pending events are completed. ...
... should be implemented by all the classes using this interface. The invokeLater method schedule the GUI creations taks to execute the run method a synchronously by the event-handling thread after all the pending events are completed. ...
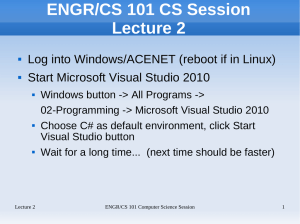
ENGR/CS 101 Lecture 2
... index of plaintext letter (i.e., where in the alphabet it is when we start counting at 0) using a similar method, then add the shift number. This will be the index of the ciphertext letter, except that the number may be greater than 26. To make it circular, we compute the modulus with respect to 26. ...
... index of plaintext letter (i.e., where in the alphabet it is when we start counting at 0) using a similar method, then add the shift number. This will be the index of the ciphertext letter, except that the number may be greater than 26. To make it circular, we compute the modulus with respect to 26. ...
Functions 1 - Portal UniMAP
... To use function in a program, it has to be declared at the beginning of a program, using function prototype. Function prototype has the following form: ...
... To use function in a program, it has to be declared at the beginning of a program, using function prototype. Function prototype has the following form: ...
Dr Java has a definitions pane
... How do you develop software? • Start with concept • use a development process, e.g. design-code-test • produce a good design † – procedural abstraction and data abstraction – high cohesion, low coupling • produce readable code - self-documenting code using consistent coding conventions † Covered in ...
... How do you develop software? • Start with concept • use a development process, e.g. design-code-test • produce a good design † – procedural abstraction and data abstraction – high cohesion, low coupling • produce readable code - self-documenting code using consistent coding conventions † Covered in ...
COS260Day7 - Ecom and COS classes
... Programming Assignment 1 feedback • Problems with declaring variables to be a certain type and using them as another type. examples declare aVar as double and then using nextInt() • Names of identifiers should always start with lower case letter • Making sure output is exactly as specified • Commen ...
... Programming Assignment 1 feedback • Problems with declaring variables to be a certain type and using them as another type. examples declare aVar as double and then using nextInt() • Names of identifiers should always start with lower case letter • Making sure output is exactly as specified • Commen ...
call
... names to be used later in the program • Imperative statements: describe the steps in the underlying algorithms • Comments: enhance the readability of a program for handy explanation • Directives: assist compiler/interpreter to ...
... names to be used later in the program • Imperative statements: describe the steps in the underlying algorithms • Comments: enhance the readability of a program for handy explanation • Directives: assist compiler/interpreter to ...
Document
... Even more features of Erlang: • Garbage Collection - As a real time system, bounded-time garbage techniques are critical. ...
... Even more features of Erlang: • Garbage Collection - As a real time system, bounded-time garbage techniques are critical. ...
Spark
... By calling SparkContext’s parallelize method on an existing Scala collection (a Seq obj) ...
... By calling SparkContext’s parallelize method on an existing Scala collection (a Seq obj) ...
Loops
... break exits the loop immediately. continue stops the current pass through the loop and starts a new one. while () {
if () continue;
if () break;
...
... break exits the loop immediately. continue stops the current pass through the loop and starts a new one. while (
ppt
... control • t1 calls the withdraw method which withdraws $100 from the balance variable. • Balance is now -100 • t1 goes to sleep • t0 ...
... control • t1 calls the withdraw method which withdraws $100 from the balance variable. • Balance is now -100 • t1 goes to sleep • t0 ...
Kennesaw State University: AP Computer Science A
... III. A. 3. Testing: perform integration testing. III. C. Understand and modify existing code. I. A. 2. Program design; apply data abstraction and encapsulation. I. B. 1. Class design; design and implement a class. ...
... III. A. 3. Testing: perform integration testing. III. C. Understand and modify existing code. I. A. 2. Program design; apply data abstraction and encapsulation. I. B. 1. Class design; design and implement a class. ...
An Introduction to Control Structures
... Programming I/O • In stream I/O, characters or bytes are read or written sequentially • The Java platform includes two dual hierarchies of classes that support streams: – byte-oriented input and output – character-oriented input and output ...
... Programming I/O • In stream I/O, characters or bytes are read or written sequentially • The Java platform includes two dual hierarchies of classes that support streams: – byte-oriented input and output – character-oriented input and output ...
CS 340 Data Structures
... JVM: Java Virtual Machine J2EE: Java Platform, Enterprise Edition. A widely used platform for server programming. ...
... JVM: Java Virtual Machine J2EE: Java Platform, Enterprise Edition. A widely used platform for server programming. ...
9781285081953_PPT_ch14
... • When clicked, no resulting actions occur – The code has not yet been written to handle user-initiated events ...
... • When clicked, no resulting actions occur – The code has not yet been written to handle user-initiated events ...
Sailing around Java: Experiences implementing SAS/IntrNet software in the global controlling arena
... By default SCL entries which are executed on the application Dispatcher are loaded to the cache of the server the first time they are executed. Therefore they will not be loaded again from disk on subsequent calls. After the first execution of an SCL entry, the catalog it resides in is blocked and c ...
... By default SCL entries which are executed on the application Dispatcher are loaded to the cache of the server the first time they are executed. Therefore they will not be loaded again from disk on subsequent calls. After the first execution of an SCL entry, the catalog it resides in is blocked and c ...
Structured programming

Structured programming is a programming paradigm aimed at improving the clarity, quality, and development time of a computer program by making extensive use of subroutines, block structures and for and while loops—in contrast to using simple tests and jumps such as the goto statement which could lead to ""spaghetti code"" which is difficult both to follow and to maintain.It emerged in the 1960s—particularly from a famous letter, Go To Statement Considered Harmful.—and was bolstered theoretically by the structured program theorem, and practically by the emergence of languages such as ALGOL with suitably rich control structures.