Operating System Extensions to Support Host Based Virtual Machines
... switches are more expensive than traps, applications using ptrace to implement services will suffer from poor performance. For example, UMLinux uses ptrace to redirect system calls from guest applications to the guest kernel. When a guest application makes a system call, the UMLinux VMM intercepts t ...
... switches are more expensive than traps, applications using ptrace to implement services will suffer from poor performance. For example, UMLinux uses ptrace to redirect system calls from guest applications to the guest kernel. When a guest application makes a system call, the UMLinux VMM intercepts t ...
DEGREE PROGRAM IN ELECTRICAL ENGINEERING LINUX
... the complexity of the system by controlling the hardware resources of the system; It hides hardware from software running the top of it by providing common services, such as filesystems, networking, and interfaces to use hardware via drivers. Linux also enables more powerful advanced wireless networ ...
... the complexity of the system by controlling the hardware resources of the system; It hides hardware from software running the top of it by providing common services, such as filesystems, networking, and interfaces to use hardware via drivers. Linux also enables more powerful advanced wireless networ ...
COS 318: Operating Systems Implementing Threads
... User-level thread package implements thread context switches OS doesn’t know the process has multiple threads Timer interrupt (signal facility) can introduce preemption When a user-level thread is blocked on an I/O event, the whole process is blocked Allows user-level code to build custom schedulers ...
... User-level thread package implements thread context switches OS doesn’t know the process has multiple threads Timer interrupt (signal facility) can introduce preemption When a user-level thread is blocked on an I/O event, the whole process is blocked Allows user-level code to build custom schedulers ...
Linux+ Guide to Linux Certification
... defined by the programming language in which it was written ...
... defined by the programming language in which it was written ...
... This includes long-term storage, the central processing unit (CPU), short-term memory and the input and output devices. When an application needs one of these resources, the kernel makes the resource available and completes the request. This handling of resources allows the operating systems to be b ...
Chapter 5
... Kernel Module Basics • Kernel is installed in directory /boot/ • Drivers can be compiled into the kernel – Or be loaded as kernel modules ...
... Kernel Module Basics • Kernel is installed in directory /boot/ • Drivers can be compiled into the kernel – Or be loaded as kernel modules ...
The Application Kernel Approach - a Novel Approach for Adding
... very costly and time consuming, and there has also been a surge of interest in alternative methods lately. For example, as an alternative to altering operating system code, Arpaci-Dusseau et al. [1] propose a method where “gray-box” knowledge about algorithms and the behavior of an operating system ...
... very costly and time consuming, and there has also been a surge of interest in alternative methods lately. For example, as an alternative to altering operating system code, Arpaci-Dusseau et al. [1] propose a method where “gray-box” knowledge about algorithms and the behavior of an operating system ...
the linux operating system
... of the kernel have access to all of its internal data structures and routines. If changes are made to any portion of a typical monolithic OS, all the modules and routines must be relinked and reinstalled and the system rebooted before the changes can take effect. As a result, any modification, such ...
... of the kernel have access to all of its internal data structures and routines. If changes are made to any portion of a typical monolithic OS, all the modules and routines must be relinked and reinstalled and the system rebooted before the changes can take effect. As a result, any modification, such ...
HPDC - Pitt Computer Science
... to maximize a set of design goals that conflict with those required to provide complete isolation. Specifically, commodity systems are almost always designed to maximize resource utilization, ensure fairness, and most importantly, gracefully degrade in the face of increasing loads. These goals often ...
... to maximize a set of design goals that conflict with those required to provide complete isolation. Specifically, commodity systems are almost always designed to maximize resource utilization, ensure fairness, and most importantly, gracefully degrade in the face of increasing loads. These goals often ...
Chapter 21 - Linux Operating System
... – when a time interrupt is received while a process is executing a kernel system service routine, the kernel’s need_resched flag is set so that the scheduler will run once the system call has completed and control is about to be returned to user mode 2. The second technique applies to critical secti ...
... – when a time interrupt is received while a process is executing a kernel system service routine, the kernel’s need_resched flag is set so that the scheduler will run once the system call has completed and control is about to be returned to user mode 2. The second technique applies to critical secti ...
Multiuser Systems
... Because any module can be linked and unlinked at runtime, system programmers must introduce welldefined software interfaces to access the data structures handled by modules. This makes it easy to develop new modules. Platform independence Even if it may rely on some specific hardware features, a mo ...
... Because any module can be linked and unlinked at runtime, system programmers must introduce welldefined software interfaces to access the data structures handled by modules. This makes it easy to develop new modules. Platform independence Even if it may rely on some specific hardware features, a mo ...
ENEA® Linux
... software, ensuring compliance between all involved licenses and that proprietary context resides outside kernel space. Development Tools The Enea Linux tools suite consists solely of open source development tools covering all phases of the development process - from building Linux images to applicat ...
... software, ensuring compliance between all involved licenses and that proprietary context resides outside kernel space. Development Tools The Enea Linux tools suite consists solely of open source development tools covering all phases of the development process - from building Linux images to applicat ...
Isolating Operating System Components with Intel SGX
... the operating system as one compromised operating system component can easily compromise other components of the kernel without the need for further vulnerabilities. To enforce isolation of operating system components even in the event of a partially compromised kernel, trust needs to be rooted, for ...
... the operating system as one compromised operating system component can easily compromise other components of the kernel without the need for further vulnerabilities. To enforce isolation of operating system components even in the event of a partially compromised kernel, trust needs to be rooted, for ...
Chapter 1 PowerPoint
... • An operating system provides an interface between the computer hardware and the applications run by the user. • The Linux kernel was created by many talented individuals from around the world working under the leadership of Linus Torvalds • The Free Software Foundation, led by Richard Stallman, cr ...
... • An operating system provides an interface between the computer hardware and the applications run by the user. • The Linux kernel was created by many talented individuals from around the world working under the leadership of Linus Torvalds • The Free Software Foundation, led by Richard Stallman, cr ...
Web Site Development Tools
... • An operating system provides an interface between the computer hardware and the applications run by the user. • The Linux kernel was created by many talented individuals from around the world working under the leadership of Linus Torvalds • The Free Software Foundation, led by Richard Stallman, cr ...
... • An operating system provides an interface between the computer hardware and the applications run by the user. • The Linux kernel was created by many talented individuals from around the world working under the leadership of Linus Torvalds • The Free Software Foundation, led by Richard Stallman, cr ...
chap01
... • An operating system provides an interface between the computer hardware and the applications run by the user. • The Linux kernel was created by many talented individuals from around the world working under the leadership of Linus Torvalds • The Free Software Foundation, led by Richard Stallman, cr ...
... • An operating system provides an interface between the computer hardware and the applications run by the user. • The Linux kernel was created by many talented individuals from around the world working under the leadership of Linus Torvalds • The Free Software Foundation, led by Richard Stallman, cr ...
L11-thread-impl
... – Thread history isn’t taken into account by scheduler – Threads are co-‐opera(ve, not compe,,ve ...
... – Thread history isn’t taken into account by scheduler – Threads are co-‐opera(ve, not compe,,ve ...
Adopting and Commenting the Old Kernel Source Code for Education
... only theory leaves the student with a lopsided view of what an operating system is really like.” and “Subjects that really are important, such as I/O and file systems, are generally neglected because there is little theory about them.” As a result, one may not know the tricks involved in implementin ...
... only theory leaves the student with a lopsided view of what an operating system is really like.” and “Subjects that really are important, such as I/O and file systems, are generally neglected because there is little theory about them.” As a result, one may not know the tricks involved in implementin ...
LinuxOS-SGOSbookCh20
... need_resched flag is set so that the scheduler will run once the system call has completed and control is about to be returned to user mode 2. The second technique applies to critical sections that occur in an interrupt service routines – By using the processor’s interrupt control hardware to disabl ...
... need_resched flag is set so that the scheduler will run once the system call has completed and control is about to be returned to user mode 2. The second technique applies to critical sections that occur in an interrupt service routines – By using the processor’s interrupt control hardware to disabl ...
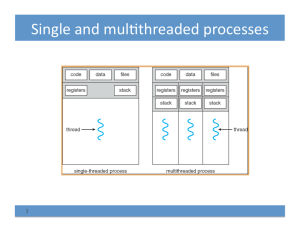
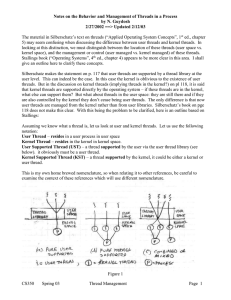
Notes by Guydosh on Thread managment
... In a “pure” UST scheme, all thread management for user threads is done by the application in user space. The kernel is oblivious to the user threads, all it sees is the user process. This is depicted in Fig. 1a. All thread support code is in the threads library in user space. The library contains co ...
... In a “pure” UST scheme, all thread management for user threads is done by the application in user space. The kernel is oblivious to the user threads, all it sees is the user process. This is depicted in Fig. 1a. All thread support code is in the threads library in user space. The library contains co ...
ppt
... and one or more group IDs that determine the process’s rights to access system resources and files Personality - Not traditionally found on UNIX systems, but under Linux each process has an associated personality identifier that can slightly modify the semantics of certain system calls Used prim ...
... and one or more group IDs that determine the process’s rights to access system resources and files Personality - Not traditionally found on UNIX systems, but under Linux each process has an associated personality identifier that can slightly modify the semantics of certain system calls Used prim ...
threads
... communication mechanism from the kernel to the thread library • This communication allows an application to maintain the correct number kernel threads ...
... communication mechanism from the kernel to the thread library • This communication allows an application to maintain the correct number kernel threads ...
A Real-Time Linux
... and the behavior of other processes. These problems are compounded in Linux and most other UNIX derivatives, because kernel mode execution is non-preemptable [6] and because disabling interrupts is used as the primary means of synchronization. By locking process pages into memory and requiring use o ...
... and the behavior of other processes. These problems are compounded in Linux and most other UNIX derivatives, because kernel mode execution is non-preemptable [6] and because disabling interrupts is used as the primary means of synchronization. By locking process pages into memory and requiring use o ...
A Real-Time Linux
... and the behavior of other processes. These problems are compounded in Linux and most other UNIX derivatives, because kernel mode execution is non-preemptable [6] and because disabling interrupts is used as the primary means of synchronization. By locking process pages into memory and requiring use o ...
... and the behavior of other processes. These problems are compounded in Linux and most other UNIX derivatives, because kernel mode execution is non-preemptable [6] and because disabling interrupts is used as the primary means of synchronization. By locking process pages into memory and requiring use o ...
Linux kernel
The Linux kernel is a Unix-like computer operating system kernel. It is widely used world-wide; the Linux operating system is based on it and deployed on both traditional computer systems such as personal computers and servers, usually in the form of Linux distributions, and on various embedded devices such as routers and NAS appliances. The Android operating system for tablet computers, smartphones and smartwatches is also based atop the Linux kernel.The Linux kernel was initially conceived and created in 1991 by Finnish computer science student Linus Torvalds, for his personal computer and with no cross-platform intentions, but has since expanded to support a huge array of computer architectures, many more than other operating systems or kernels. Linux rapidly attracted developers and users who adapted code from other free software projects for use with the new operating system. The Linux kernel has received contributions from nearly 12,000 programmers from more than 1,200 companies, including some of the largest software and hardware vendors.The Linux kernel API, the application programming interface (API) through which user programs interact with the kernel, is meant to be very stable and to not break userspace programs (some programs, such as those with GUIs, rely on other APIs as well). As part of the kernel's functionality, device drivers control the hardware; ""mainlined"" device drivers are also meant to be very stable. However, the interface between the kernel and loadable kernel modules (LKMs), unlike in many other kernels and operating systems, is not meant to be very stable by design.The Linux kernel, developed by contributors worldwide, is a prominent example of free and open source software. Day-to-day development discussions take place on the Linux kernel mailing list (LKML). The Linux kernel is released under the GNU General Public License version 2 (GPLv2), with some firmware images released under various non-free licenses.