Introduction to Forensic Science
... •The private labs perform a service to the criminal justice system by providing resources for those accused of crimes ...
... •The private labs perform a service to the criminal justice system by providing resources for those accused of crimes ...
Forensic Science EOC Review
... Albert S. Osborn (1858-1946) Developed fundamental principles of document examination Walter C. McCrone (1916-2002) Used microscopy and analytical methodologies to examine evidence Hans Gross (1847-1915) Described application of scientific disciplines to the field of criminal investigation Edmond Lo ...
... Albert S. Osborn (1858-1946) Developed fundamental principles of document examination Walter C. McCrone (1916-2002) Used microscopy and analytical methodologies to examine evidence Hans Gross (1847-1915) Described application of scientific disciplines to the field of criminal investigation Edmond Lo ...
sample
... The Washing Away of Wrongs. The field of forensic science evolved in fits and spurts over the centuries that followed. Some techniques developed early and progressed rapidly, others lagged behind, and still others are truly modern. No forensic technique simply jumped into existence; it followed its ...
... The Washing Away of Wrongs. The field of forensic science evolved in fits and spurts over the centuries that followed. Some techniques developed early and progressed rapidly, others lagged behind, and still others are truly modern. No forensic technique simply jumped into existence; it followed its ...
physical evidence - Armstrong State University
... database contains chemical and color information pertaining to original automotive paints. • SICAR (shoeprint image capture and retrieval) is a shoeprint database. ...
... database contains chemical and color information pertaining to original automotive paints. • SICAR (shoeprint image capture and retrieval) is a shoeprint database. ...
Crime Lab Forensics - Fairfield Public Schools
... Crime Lab Forensics, which is a laboratory-based course, will promote and cultivate the development of student’s scientific inquiry and scientific method skills, which are important critical thinking skills. Crime Lab Forensics applies concepts and skills acquired in grades nine and ten to look at t ...
... Crime Lab Forensics, which is a laboratory-based course, will promote and cultivate the development of student’s scientific inquiry and scientific method skills, which are important critical thinking skills. Crime Lab Forensics applies concepts and skills acquired in grades nine and ten to look at t ...
Chapter 1: Introduction to Forensic Science
... society to administer a system of order that people can live harmoniously in. But as there is that element of society that refuses to live by these rules, there must be part of society willing to enforce the rules and administer judgment to the law breakers. In being dedicated to do this, law enforc ...
... society to administer a system of order that people can live harmoniously in. But as there is that element of society that refuses to live by these rules, there must be part of society willing to enforce the rules and administer judgment to the law breakers. In being dedicated to do this, law enforc ...
Bloodstain Pattern Presentation - Kristin`s E
... science is an essential part of the criminal justice system. Forensic science relies on a number of wide ranging disciplines and methods in order to achieve its goals; bloodstain pattern analysis is one small part of a much larger group of individuals that come together for the purposes of crime sce ...
... science is an essential part of the criminal justice system. Forensic science relies on a number of wide ranging disciplines and methods in order to achieve its goals; bloodstain pattern analysis is one small part of a much larger group of individuals that come together for the purposes of crime sce ...
Digital Evidence Slideshow, Fall 2003
... Computer Image Verification At least two copies are taken of the evidential computer. One of these is sealed in the presence of the computer owner and then placed in secure storage. This is the master copy and it will only be opened for examination under instruction from the Court in the event of a ...
... Computer Image Verification At least two copies are taken of the evidential computer. One of these is sealed in the presence of the computer owner and then placed in secure storage. This is the master copy and it will only be opened for examination under instruction from the Court in the event of a ...
THE CRIME SCENE
... • Standard/Reference Sample—Physical evidence whose origin is known, such as blood or hair from a suspect, that can be compared to crime-scene evidence. • The examination of evidence, whether it is soil, blood, glass, hair, fibers, and so on, often requires comparison with a known standard/reference ...
... • Standard/Reference Sample—Physical evidence whose origin is known, such as blood or hair from a suspect, that can be compared to crime-scene evidence. • The examination of evidence, whether it is soil, blood, glass, hair, fibers, and so on, often requires comparison with a known standard/reference ...
Introduction to Forensic Science and Fingerprints
... criminal came into contact with an object or person, a cross-transfer of ...
... criminal came into contact with an object or person, a cross-transfer of ...
Chapter 13
... Compare and contrast skid marks and yaw marks. Explain the importance of the law of conservation of momentum and law of conservation of energy in accident reconstruction. Evaluate factors that can lead to incorrect reconstruction. ...
... Compare and contrast skid marks and yaw marks. Explain the importance of the law of conservation of momentum and law of conservation of energy in accident reconstruction. Evaluate factors that can lead to incorrect reconstruction. ...
1.3--POWERPOINT--Crime Labs 2
... Part I: History of Crime Labs in the US • 1923: Los Angeles PD crime lab created by August Vollmer (police chief) at Univ. of California, Berkley • 1932: FBI, under direction of J. Edgar Hoover, organizes national lab offering forensic services to all law enforcement agencies in the US • FBI lab is ...
... Part I: History of Crime Labs in the US • 1923: Los Angeles PD crime lab created by August Vollmer (police chief) at Univ. of California, Berkley • 1932: FBI, under direction of J. Edgar Hoover, organizes national lab offering forensic services to all law enforcement agencies in the US • FBI lab is ...
SWGDE Model SOP for Computer Forensics
... This modular approach will enable a lab to include sections they may choose to implement (e.g. Cell Phone Analysis or Macintosh Forensics). Each module of the SOP is focused on the methodology to conduct an exam properly. It is assumed that the examiner is properly trained and competent in digital f ...
... This modular approach will enable a lab to include sections they may choose to implement (e.g. Cell Phone Analysis or Macintosh Forensics). Each module of the SOP is focused on the methodology to conduct an exam properly. It is assumed that the examiner is properly trained and competent in digital f ...
Forensic Science
... be done by analyzing the development of the teeth, bone growth, and the length of specific bones, such as the femur. Determining the race of a victim can be done by analyzing the skull for specific characteristics that are common among people of different races. ...
... be done by analyzing the development of the teeth, bone growth, and the length of specific bones, such as the femur. Determining the race of a victim can be done by analyzing the skull for specific characteristics that are common among people of different races. ...
Forensic Science
... be done by analyzing the development of the teeth, bone growth, and the length of specific bones, such as the femur. Determining the race of a victim can be done by analyzing the skull for specific characteristics that are common among people of different races. ...
... be done by analyzing the development of the teeth, bone growth, and the length of specific bones, such as the femur. Determining the race of a victim can be done by analyzing the skull for specific characteristics that are common among people of different races. ...
Lecture 28 - The University of Texas at Dallas
... Onsite/Offsite services Cost and risks – major consideration Example: Computer Forensics Services Corporation - http://www.computer-forensic.com/ - As stated in the above web site, this company provides “expert, court approved, High Tech Investigations, litigation support and IT Consulting.” T ...
... Onsite/Offsite services Cost and risks – major consideration Example: Computer Forensics Services Corporation - http://www.computer-forensic.com/ - As stated in the above web site, this company provides “expert, court approved, High Tech Investigations, litigation support and IT Consulting.” T ...
course objectives - Metropolitan Community College
... Identify the common ridge characteristics of a fingerprint. List the three major fingerprint patterns and their respective subclasses. Distinguish visible, plastic, and latent fingerprint. Describe the concept of an automated fingerprint identification system (AFIS). List the techniques fo ...
... Identify the common ridge characteristics of a fingerprint. List the three major fingerprint patterns and their respective subclasses. Distinguish visible, plastic, and latent fingerprint. Describe the concept of an automated fingerprint identification system (AFIS). List the techniques fo ...
Introduction to Forensic Science
... http://www.nlm.nih.gov/visibleproofs/galleries/media /autopsy/index.html Return organs and suture ...
... http://www.nlm.nih.gov/visibleproofs/galleries/media /autopsy/index.html Return organs and suture ...
HANDOUT 3: Forensic Science
... blood and semen, collected at crime scenes and from articles of physical evidence. These types of physiological fluids are frequently generated during the commission of violent crimes such as homicides, rapes, assaults, and hit and run fatalities. In some cases, the biologist may have to testify in ...
... blood and semen, collected at crime scenes and from articles of physical evidence. These types of physiological fluids are frequently generated during the commission of violent crimes such as homicides, rapes, assaults, and hit and run fatalities. In some cases, the biologist may have to testify in ...
Crime Solving Microflora
... By age 3, everyone, even identical twins, has a unique coat of it that changes somewhat but remains largely consistent at its core and over time. In scientific studies, researchers have successfully matched smartphones and keyboards to the people who used them by analyzing their microbial signature ...
... By age 3, everyone, even identical twins, has a unique coat of it that changes somewhat but remains largely consistent at its core and over time. In scientific studies, researchers have successfully matched smartphones and keyboards to the people who used them by analyzing their microbial signature ...
forensic science chapter 1 notes
... 1-1 Definition and Scope of Forensic Science < The word forensics means to verbally debate in public. < Forensic science is the application of science to matters of law. It applies the knowledge and technology of science for the definition and enforcement of such laws. < Each year science merges mor ...
... 1-1 Definition and Scope of Forensic Science < The word forensics means to verbally debate in public. < Forensic science is the application of science to matters of law. It applies the knowledge and technology of science for the definition and enforcement of such laws. < Each year science merges mor ...
for Crime Scene Basics & Examples of Evidence
... Latent Prints - Identification and comparison of fingerprints or other hidden impressions from sources like feet, shoes, ears, lips or the tread on vehicle tires. Ballistics (Firearms) – Study of bullets and ammunition through the comparison of fired bullets, cartridges, guns, and gunpowder patterns ...
... Latent Prints - Identification and comparison of fingerprints or other hidden impressions from sources like feet, shoes, ears, lips or the tread on vehicle tires. Ballistics (Firearms) – Study of bullets and ammunition through the comparison of fired bullets, cartridges, guns, and gunpowder patterns ...
Forensics applications with Phenom desktop SEM
... standards. From the entry level pure series through to the high-end pro series, all Phenom electron microscopes share ease of use, unmatched time to results, and worry-free system ownership. The Phenom desktop SEM is a true walk-up tool for many forensic experts who investigate their own samples in ...
... standards. From the entry level pure series through to the high-end pro series, all Phenom electron microscopes share ease of use, unmatched time to results, and worry-free system ownership. The Phenom desktop SEM is a true walk-up tool for many forensic experts who investigate their own samples in ...
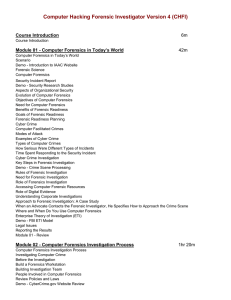
Computer Hacking Forensic Investigator Version 4 (CHFI)
... B.1: Accurately and Particularly Describe the Property to be Seized in the Warrant and/or Attachments to the Warrant B.1.a: Defending Computer Search Warrants Against Challenges Based on the Description of the “Things to be Seized” B.2: Establish Probable Cause in the Affidavit B.3: In the Affidavit ...
... B.1: Accurately and Particularly Describe the Property to be Seized in the Warrant and/or Attachments to the Warrant B.1.a: Defending Computer Search Warrants Against Challenges Based on the Description of the “Things to be Seized” B.2: Establish Probable Cause in the Affidavit B.3: In the Affidavit ...
Digital forensics

Digital forensics (sometimes known as digital forensic science) is a branch of forensic science encompassing the recovery and investigation of material found in digital devices, often in relation to computer crime. The term digital forensics was originally used as a synonym for computer forensics but has expanded to cover investigation of all devices capable of storing digital data. With roots in the personal computing revolution of the late 1970s and early '80s, the discipline evolved in a haphazard manner during the 1990s, and it was not until the early 21st century that national policies emerged.Digital forensics investigations have a variety of applications. The most common is to support or refute a hypothesis before criminal or civil (as part of the electronic discovery process) courts. Forensics may also feature in the private sector; such as during internal corporate investigations or intrusion investigation (a specialist probe into the nature and extent of an unauthorized network intrusion).The technical aspect of an investigation is divided into several sub-branches, relating to the type of digital devices involved; computer forensics, network forensics, forensic data analysis and mobile device forensics. The typical forensic process encompasses the seizure, forensic imaging (acquisition) and analysis of digital media and the production of a report into collected evidence.As well as identifying direct evidence of a crime, digital forensics can be used to attribute evidence to specific suspects, confirm alibis or statements, determine intent, identify sources (for example, in copyright cases), or authenticate documents. Investigations are much broader in scope than other areas of forensic analysis (where the usual aim is to provide answers to a series of simpler questions) often involving complex time-lines or hypotheses.