15-744: Computer Networking
... • Communication between applications on different computers • Must understand application needs/demands • Traffic data rate • Traffic pattern (bursty or constant bit rate) • Traffic target (multipoint or single destination, mobile or fixed) ...
... • Communication between applications on different computers • Must understand application needs/demands • Traffic data rate • Traffic pattern (bursty or constant bit rate) • Traffic target (multipoint or single destination, mobile or fixed) ...
Sanjay Deshpande - 24 Frames Digital
... Internet Banking – add the users PC (hardware/OS) and the Browser to this list – and you will now visualize what one is dealing with! ...
... Internet Banking – add the users PC (hardware/OS) and the Browser to this list – and you will now visualize what one is dealing with! ...
Document
... An intranet is a set of networks, using the Internet Protocol and IP-based tools such as web browsers and file transfer applications, that is under the control of a single administrative entity. With in a LAN. And can’t be access from out side. Most commonly, an intranet is the internal network of a ...
... An intranet is a set of networks, using the Internet Protocol and IP-based tools such as web browsers and file transfer applications, that is under the control of a single administrative entity. With in a LAN. And can’t be access from out side. Most commonly, an intranet is the internal network of a ...
Document
... analogy: street address + zip code provide unique address for your house/dorm using this address, anyone in the world can send you a letter ...
... analogy: street address + zip code provide unique address for your house/dorm using this address, anyone in the world can send you a letter ...
The Network Layer
... Store-and-Forward Packet Switching Services Provided to the Transport Layer Implementation of Connectionless Service Implementation of Connection-Oriented Service Comparison of Virtual-Circuit and Datagram Subnets ...
... Store-and-Forward Packet Switching Services Provided to the Transport Layer Implementation of Connectionless Service Implementation of Connection-Oriented Service Comparison of Virtual-Circuit and Datagram Subnets ...
History_of_internet_1
... severely damages the entire network making communication nearly impossible. In Burans distributed communications model, communications would go from the origin point and then onto one of many different switching nodes rather than a single regional or national node. This would allow for safer communi ...
... severely damages the entire network making communication nearly impossible. In Burans distributed communications model, communications would go from the origin point and then onto one of many different switching nodes rather than a single regional or national node. This would allow for safer communi ...
Document
... Globally connected network that links various organisations and individuals. Web is not Internet. WWW is one particular usage of internet. Email, FTP (File Transfer Protocol) are other such uses. ...
... Globally connected network that links various organisations and individuals. Web is not Internet. WWW is one particular usage of internet. Email, FTP (File Transfer Protocol) are other such uses. ...
Recommending a Strategy
... • Started October 1996 with 34 members • Commitment to end-to-end enhancements University Corporation for Advanced ...
... • Started October 1996 with 34 members • Commitment to end-to-end enhancements University Corporation for Advanced ...
Digital Divide and PingER
... • Need measurements for both production networks & tesbeds: – Planning, setting expectations, policy/funding – Trouble-shooting: reliability & performance • Problems may not be logical, e.g. most Internet problems caused by operator error (Sci Am Jun’03), most LAN problems are Ethernet duplex, host ...
... • Need measurements for both production networks & tesbeds: – Planning, setting expectations, policy/funding – Trouble-shooting: reliability & performance • Problems may not be logical, e.g. most Internet problems caused by operator error (Sci Am Jun’03), most LAN problems are Ethernet duplex, host ...
VOIP - Archive - Peter Cochrane
... We can only guess/imagine what our networks will be expected to support in the next decade/s…and it is the customers who decide and not the companies Peter Cochrane ...
... We can only guess/imagine what our networks will be expected to support in the next decade/s…and it is the customers who decide and not the companies Peter Cochrane ...
Full article
... New advances in optic network technology are transforming the transport network – the delivery system which allows data to reach its destination. New networks are providing the capacity to accommodate soaring demands for bandwidth, while supporting future growth by many orders of magnitude. Solution ...
... New advances in optic network technology are transforming the transport network – the delivery system which allows data to reach its destination. New networks are providing the capacity to accommodate soaring demands for bandwidth, while supporting future growth by many orders of magnitude. Solution ...
Document
... The Internet • The Internet is a global system of interconnected computer networks that use the standard Internet Protocol Suite (TCP/IP) to serve billions of users worldwide. • It is a network of networks that consists of millions of private and public, academic, business, and government networks ...
... The Internet • The Internet is a global system of interconnected computer networks that use the standard Internet Protocol Suite (TCP/IP) to serve billions of users worldwide. • It is a network of networks that consists of millions of private and public, academic, business, and government networks ...
61765 Computer Networks I
... Credits: 3.5; 3 lecture hours, 1 lab hour (2 hours every two weeks) Prerequisites: 61753 Algorithms in Graph Theory or 61713 Course Description This is an introductory course in computer networks and data communication methods. The TCP/IP layers are presented using a top-down approach, from the appl ...
... Credits: 3.5; 3 lecture hours, 1 lab hour (2 hours every two weeks) Prerequisites: 61753 Algorithms in Graph Theory or 61713 Course Description This is an introductory course in computer networks and data communication methods. The TCP/IP layers are presented using a top-down approach, from the appl ...
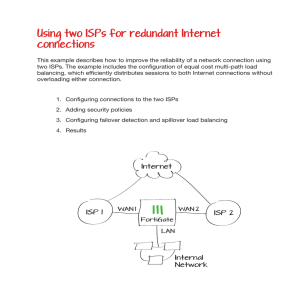
Using two ISPs for redundant Internet connections
... Using two ISPs for redundant Internet connections This example describes how to improve the reliability of a network connection using two ISPs. The example includes the configuration of equal cost multi-path load balancing, which efficiently distributes sessions to both Internet connections without ...
... Using two ISPs for redundant Internet connections This example describes how to improve the reliability of a network connection using two ISPs. The example includes the configuration of equal cost multi-path load balancing, which efficiently distributes sessions to both Internet connections without ...
Internet slides
... • Even though it was meant to be hierarchical, people like short names, and use it like a flat namespace ...
... • Even though it was meant to be hierarchical, people like short names, and use it like a flat namespace ...
ESX 2008 VoIP
... facilities that use the Internet Protocol (IP) to deliver voice information In general, this means sending voice information in digital form in discrete packets rather than in the traditional circuit-committed protocols of the public switched telephone network (PSTN) A major advantage of VoIP an ...
... facilities that use the Internet Protocol (IP) to deliver voice information In general, this means sending voice information in digital form in discrete packets rather than in the traditional circuit-committed protocols of the public switched telephone network (PSTN) A major advantage of VoIP an ...
Computer network
... – A domain name is separated into two or more sections that specify the organization, and possibly a subset of an organization, of which the computer is a part – Two organizations can have a computer named the same thing because the domain name makes it clear which one is being referred to ...
... – A domain name is separated into two or more sections that specify the organization, and possibly a subset of an organization, of which the computer is a part – Two organizations can have a computer named the same thing because the domain name makes it clear which one is being referred to ...
ppt - The Stanford University InfoLab
... • Even when no information is exchanged, a connection still ties up the system • Inefficient use of bandwidth even when information is exchanged • Absolutely guarantees a minimum amount of bandwidth and latency very good for interactivity ...
... • Even when no information is exchanged, a connection still ties up the system • Inefficient use of bandwidth even when information is exchanged • Absolutely guarantees a minimum amount of bandwidth and latency very good for interactivity ...
ppt
... • We will deal with: • Protocol rules and algorithms • Investigate protocol trade-offs • Why this way and not another? ...
... • We will deal with: • Protocol rules and algorithms • Investigate protocol trade-offs • Why this way and not another? ...
internet connection through isp
... information that describes the packet to network devices, such as routers, it passes through and also helps to control its behavior on the network. The IP packet is sometimes referred to as a datagram. IP addresses must be unique on the Internet. There are organizations responsible for controlling ...
... information that describes the packet to network devices, such as routers, it passes through and also helps to control its behavior on the network. The IP packet is sometimes referred to as a datagram. IP addresses must be unique on the Internet. There are organizations responsible for controlling ...
ABC`s of the Internet Cancer Registry
... registry server, rather than multiple applications at each reporting source location. 6.Increased compliance, since the data sources don’t need to purchase/develop reporting systems or worry about HL7 issues. 7. Automation of data receipt, diagnostic coding and database updating. 8.Superior tracking ...
... registry server, rather than multiple applications at each reporting source location. 6.Increased compliance, since the data sources don’t need to purchase/develop reporting systems or worry about HL7 issues. 7. Automation of data receipt, diagnostic coding and database updating. 8.Superior tracking ...
Document
... • A network of networks, joining many government, university and private computers together and providing an infrastructure for the use of E-mail, bulletin boards, file archives, hypertext documents, databases and other computational resources • The vast collection of computer networks which form an ...
... • A network of networks, joining many government, university and private computers together and providing an infrastructure for the use of E-mail, bulletin boards, file archives, hypertext documents, databases and other computational resources • The vast collection of computer networks which form an ...
Plutarch
... Key components to our architecture are contexts and IFs. Also important is the accompanying infrastructure to make it work. ...
... Key components to our architecture are contexts and IFs. Also important is the accompanying infrastructure to make it work. ...