NAT - Hong Kong University of Science and Technology
... prevent denial of service attacks: SYN flooding: attacker establishes many bogus TCP connections, no resources left for “real” connections. prevent illegal modification/access of internal data. e.g., attacker replaces CIA’s homepage with something else allow only authorized access to inside netw ...
... prevent denial of service attacks: SYN flooding: attacker establishes many bogus TCP connections, no resources left for “real” connections. prevent illegal modification/access of internal data. e.g., attacker replaces CIA’s homepage with something else allow only authorized access to inside netw ...
How Ethernet becomes industrial
... office nor for the plant ! One standard solution for determinism and QoS issues (not yet ?) One standard solution for connecting in industrial environment (not yet ?) One standard solution for redundancy management A satisfying solution for accurate stations ...
... office nor for the plant ! One standard solution for determinism and QoS issues (not yet ?) One standard solution for connecting in industrial environment (not yet ?) One standard solution for redundancy management A satisfying solution for accurate stations ...
Reference Manual for the MR814v2 Cable/DSL Wireless Router
... Routing Information Protocol ................................................................................... B-2 IP Addresses and the Internet ....................................................................................... B-2 Netmask ..................................................... ...
... Routing Information Protocol ................................................................................... B-2 IP Addresses and the Internet ....................................................................................... B-2 Netmask ..................................................... ...
Document
... – Gateway gets its 48-bit prefix from upstream – 2001:d0be:7922:1:fc2d:aeb2:99d2:e2b4 – Network prefix is 2001:dObe:7922:1 /64 – ISP’s network prefix 2001:D0BE /32 – ISP adds 16-bit subnet: 2001:d0be:7922/48 – At your gateway, tech adds 160bit subnet – Result: 2001:d0be:7922:1 /64 ...
... – Gateway gets its 48-bit prefix from upstream – 2001:d0be:7922:1:fc2d:aeb2:99d2:e2b4 – Network prefix is 2001:dObe:7922:1 /64 – ISP’s network prefix 2001:D0BE /32 – ISP adds 16-bit subnet: 2001:d0be:7922/48 – At your gateway, tech adds 160bit subnet – Result: 2001:d0be:7922:1 /64 ...
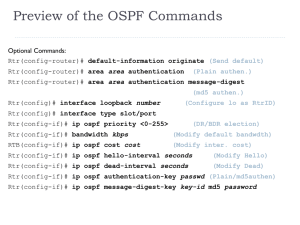
OSPF
... Cisco’s OSPF metric is based on bandwidth RIP is based on hop count IGRP/EIGRP bandwidth, delay, reliability, load OSPF only sends out changes when they occur. RIP sends entire routing table every 30 seconds, IGRP every 90 seconds Extra: With OSPF, a router does flood its own LSAs when it ag ...
... Cisco’s OSPF metric is based on bandwidth RIP is based on hop count IGRP/EIGRP bandwidth, delay, reliability, load OSPF only sends out changes when they occur. RIP sends entire routing table every 30 seconds, IGRP every 90 seconds Extra: With OSPF, a router does flood its own LSAs when it ag ...
1 Introduction
... “in flight” (data that has been transmitted, but not yet acknowledged) at any time to fully utilize the available channel capacity. The delay is the round trip time (RTT) and the bandwidth is the capacity of the bottleneck link in the path. For links with a large BDP, such as in geostationary satell ...
... “in flight” (data that has been transmitted, but not yet acknowledged) at any time to fully utilize the available channel capacity. The delay is the round trip time (RTT) and the bandwidth is the capacity of the bottleneck link in the path. For links with a large BDP, such as in geostationary satell ...
cis185-ROUTE-lecture2-EIGRP-Part2
... Note: R4 is not considered even if it’s FD was < or = R3’s FDv of 40 because it is not a FS The load in is balanced proportional to the bandwidth. FD of the route via router R2 is 30 FD of the route via router R3 is 20 Ratio of traffic between the two paths is via R2: 3/5 and via R3: 2/5 ...
... Note: R4 is not considered even if it’s FD was < or = R3’s FDv of 40 because it is not a FS The load in is balanced proportional to the bandwidth. FD of the route via router R2 is 30 FD of the route via router R3 is 20 Ratio of traffic between the two paths is via R2: 3/5 and via R3: 2/5 ...
TRANSITION FROM IPv4 TO IPv6 LAHTI UNIVERSITY OF APPLIED
... global expansion of communications. As a result, the more users join the Internet, the better it would be to spread knowledge in every field around the world. However, this is also the problem as the IP address is not unlimited and the Internet community is witnessing the exhaust of IPv4 not year by ...
... global expansion of communications. As a result, the more users join the Internet, the better it would be to spread knowledge in every field around the world. However, this is also the problem as the IP address is not unlimited and the Internet community is witnessing the exhaust of IPv4 not year by ...
Computer Networking : Principles, Protocols and Practice
... a network, we often distinguish between three transmission modes. In TV and radio transmission, broadcast is often used to indicate a technology that sends a video or radio signal to all receivers in a given geographical area. Broadcast is sometimes used in computer networks, but only in local area ...
... a network, we often distinguish between three transmission modes. In TV and radio transmission, broadcast is often used to indicate a technology that sends a video or radio signal to all receivers in a given geographical area. Broadcast is sometimes used in computer networks, but only in local area ...
PDF
... Cisco Performance Routing removes this complexity from network operators and provides needed application performance when the network is operational but parts of the network are experiencing performance-degradation problems. Cisco PfR in its truest form is “application routing based on network perfo ...
... Cisco Performance Routing removes this complexity from network operators and provides needed application performance when the network is operational but parts of the network are experiencing performance-degradation problems. Cisco PfR in its truest form is “application routing based on network perfo ...
Sniffer University 1-3
... • We’ll show you how to: – Use the Monitor functions to check the health and performance of your networks – Troubleshoot problems by capturing traffic and using the Expert’s help – Analyze the issues by viewing the frames that were captured – Proactively manage the network with Sniffer Portable’s to ...
... • We’ll show you how to: – Use the Monitor functions to check the health and performance of your networks – Troubleshoot problems by capturing traffic and using the Expert’s help – Analyze the issues by viewing the frames that were captured – Proactively manage the network with Sniffer Portable’s to ...
Cost_Calculation
... Customer saves $$$$ (per mile backhaul cost) • Why is the backhaul much less with WR? What is new with WR? – Frame Selection is done at the WR. No duplicate traffic after the selection is done – The aggregation of voice and data traffic from multiple WRs enables better Statistical multiplexing and r ...
... Customer saves $$$$ (per mile backhaul cost) • Why is the backhaul much less with WR? What is new with WR? – Frame Selection is done at the WR. No duplicate traffic after the selection is done – The aggregation of voice and data traffic from multiple WRs enables better Statistical multiplexing and r ...
downloading
... - 1 km of optic fiber - Via satellite with a distance of 30 km between the base and the satellite ...
... - 1 km of optic fiber - Via satellite with a distance of 30 km between the base and the satellite ...
20100810-OSG-NPW-Diagnostics
... – perfSONAR works best when everyone participates, holes in deployment lead to holes in the problem solving phase ...
... – perfSONAR works best when everyone participates, holes in deployment lead to holes in the problem solving phase ...
Reference Manual for the 108 Mbps Wireless Firewall Router WGT624
... MAC Addresses and Address Resolution Protocol ................................................. B-8 Related Documents ................................................................................................. B-9 Domain Name Server ............................................................. ...
... MAC Addresses and Address Resolution Protocol ................................................. B-8 Related Documents ................................................................................................. B-9 Domain Name Server ............................................................. ...
Chapter5-NetworkLayer
... • Start with sink, set distance at other nodes to infinity • Relax distance to other nodes • Pick the lowest distance node, add it to sink tree • Repeat until all nodes are in the sink tree ...
... • Start with sink, set distance at other nodes to infinity • Relax distance to other nodes • Pick the lowest distance node, add it to sink tree • Repeat until all nodes are in the sink tree ...
About the Presentations
... • Work at the Application layer • Control the way applications inside the network access external networks by setting up proxy services • Minimize the effect of viruses, worms, Trojan horses, and other malware • Run special software that enable them to act as a proxy for a specific service request ...
... • Work at the Application layer • Control the way applications inside the network access external networks by setting up proxy services • Minimize the effect of viruses, worms, Trojan horses, and other malware • Run special software that enable them to act as a proxy for a specific service request ...
Scap: Stream-Oriented Network Traffic Capture and
... packet copy identifies these packets and does not bring them in main memory at all: they are dropped by the network interface card (NIC) before reaching the main memory. To accommodate heavy loads, Scap introduces the notion of prioritized packet loss (PPL). Under heavy load, traditional monitoring ...
... packet copy identifies these packets and does not bring them in main memory at all: they are dropped by the network interface card (NIC) before reaching the main memory. To accommodate heavy loads, Scap introduces the notion of prioritized packet loss (PPL). Under heavy load, traditional monitoring ...
NetApp CN1610 Switch Administrator`s Guide
... NetApp reserves the right to change any products described herein at any time, and without notice. NetApp assumes no responsibility or liability arising from the use of products described herein, except as expressly agreed to in writing by NetApp. The use or purchase of this product does not convey ...
... NetApp reserves the right to change any products described herein at any time, and without notice. NetApp assumes no responsibility or liability arising from the use of products described herein, except as expressly agreed to in writing by NetApp. The use or purchase of this product does not convey ...
SonicWALL TZ 170 Getting Started Guide Page 7
... “Configuring Computers for Your Network with DHCP” on page 20 for instructions on changing your Local Area Connection settings. • Do you have the Ethernet cable connected to your computer and to one of the LAN ports (1 through 5) on your SonicWALL TZ 170? • Some browsers may not launch the Setup Wiz ...
... “Configuring Computers for Your Network with DHCP” on page 20 for instructions on changing your Local Area Connection settings. • Do you have the Ethernet cable connected to your computer and to one of the LAN ports (1 through 5) on your SonicWALL TZ 170? • Some browsers may not launch the Setup Wiz ...
DNSCatProxy: A Pluggable Transport based on DNS Tunneling Irvin Zhan Abstract
... the Tor Browser [30]. The GetTor project was created in response to allow users to download the Tor using email; by sending a quick email to a specific email with the operating system in the body of the text, the email robot will reply with links to download the Tor Browser from popular Cloud servic ...
... the Tor Browser [30]. The GetTor project was created in response to allow users to download the Tor using email; by sending a quick email to a specific email with the operating system in the body of the text, the email robot will reply with links to download the Tor Browser from popular Cloud servic ...
ip-shiv2004-routing-I
... Can assume that a chosen route is available as the signaling proceeds through the network Component reliability drove system reliability and hence acceptance of service by customers Simplified topology: Very highly connected network Hierarchy + full mesh at each level: simple routing Hig ...
... Can assume that a chosen route is available as the signaling proceeds through the network Component reliability drove system reliability and hence acceptance of service by customers Simplified topology: Very highly connected network Hierarchy + full mesh at each level: simple routing Hig ...
Reference Manual for the Model RP614 Web Safe Router
... Routing Information Protocol ................................................................................... B-2 IP Addresses and the Internet ................................................................................. B-2 Netmask ........................................................... ...
... Routing Information Protocol ................................................................................... B-2 IP Addresses and the Internet ................................................................................. B-2 Netmask ........................................................... ...
PDF
... Buffer Requirements for Data Center Network Access Layer ............................................................................. 3 Cisco Nexus 9300 Platform Buffer Structure ........................................................................................................ 3 Buffer on Net ...
... Buffer Requirements for Data Center Network Access Layer ............................................................................. 3 Cisco Nexus 9300 Platform Buffer Structure ........................................................................................................ 3 Buffer on Net ...