Fax and Modem Services over IP Overview
... network (PSTN) or telephony (fax) device. When a call comes into the IP network over a gateway, that gateway is called an originating gateway (OGW). Similarly, a gateway over which a call passes out of the IP network is called a terminating gateway (TGW). A traditional voice call over the PSTN uses ...
... network (PSTN) or telephony (fax) device. When a call comes into the IP network over a gateway, that gateway is called an originating gateway (OGW). Similarly, a gateway over which a call passes out of the IP network is called a terminating gateway (TGW). A traditional voice call over the PSTN uses ...
Comparative firewall study - Torsten Hoefler - Qucosa
... It is also important to examine the packets, passing the firewall, for defective content to avoid misuse or to filter for viruses in emails. Like a packet filter, a proxy is switched between sender and receiver. The difference is, that a proxy is not transparent for the user. The sender must adjust ...
... It is also important to examine the packets, passing the firewall, for defective content to avoid misuse or to filter for viruses in emails. Like a packet filter, a proxy is switched between sender and receiver. The difference is, that a proxy is not transparent for the user. The sender must adjust ...
Observer - Optrics Engineering
... Network Instruments, LLC. (Network Instruments) warrants this hardware product against defects in materials and workmanship for a period of 90 days (1 year for nTAPs) from the date of shipment of the product from Network Instruments, LLC. Warranty is for depot service at Network Instruments corporat ...
... Network Instruments, LLC. (Network Instruments) warrants this hardware product against defects in materials and workmanship for a period of 90 days (1 year for nTAPs) from the date of shipment of the product from Network Instruments, LLC. Warranty is for depot service at Network Instruments corporat ...
NGN_internship
... costs in voice backbone networks. However with many network operators facing eventual equipment obsolescence in their existing narrowband PSTN networks and with the drive to increase revenue by offering new and innovative multimedia services, the MSF expects that end-to-end VoIP solutions will be re ...
... costs in voice backbone networks. However with many network operators facing eventual equipment obsolescence in their existing narrowband PSTN networks and with the drive to increase revenue by offering new and innovative multimedia services, the MSF expects that end-to-end VoIP solutions will be re ...
JNCIA Study Guide - Open Shortest Path First (OSPF)
... best path to a destination. We follow this with a detailed discussion of the OSPF packet types and how two OSPF neighbors form an adjacency. We examine the evolution of an OSPF network and look at several methods that allow you to scale your OSPF deployment. This includes a review of OSPF link-state ...
... best path to a destination. We follow this with a detailed discussion of the OSPF packet types and how two OSPF neighbors form an adjacency. We examine the evolution of an OSPF network and look at several methods that allow you to scale your OSPF deployment. This includes a review of OSPF link-state ...
TDMoIP : IPR
... the following are not labels: telephone number (not fixed length, country-code+area-code+local-number) Ethernet address (too long, note vendor-code is not meaningful structure) IP address (too long, has fields) ATM address (has VP/VC) not explicit requirement, but normally only local in sign ...
... the following are not labels: telephone number (not fixed length, country-code+area-code+local-number) Ethernet address (too long, note vendor-code is not meaningful structure) IP address (too long, has fields) ATM address (has VP/VC) not explicit requirement, but normally only local in sign ...
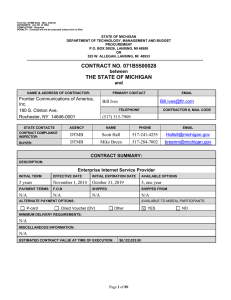
... Contract Administrator and DTMB must approve any tools, in writing, before use on any information technology project for New Work. It is recognized that technology changes rapidly. Either party may, subject to Contract Change Management request, in writing, a change in the standard environment Equip ...
Paper Title (use style: paper title)
... construct the multicast delivery tree should be optimized and well scheduled. In fact, multicast routers cannot trigger automatically a unidirectional or a bidirectional multicast routing protocol unless they are manually configured to use a specific routing protocol for a predetermined pool of IP ...
... construct the multicast delivery tree should be optimized and well scheduled. In fact, multicast routers cannot trigger automatically a unidirectional or a bidirectional multicast routing protocol unless they are manually configured to use a specific routing protocol for a predetermined pool of IP ...
ProSafe VPN Firewall 50 FVS338 Reference Manual
... Using Rules to Block or Allow Specific Kinds of Traffic ..................................................4-2 Services-Based Rules ..............................................................................................4-2 Viewing the Firewall Rules ............................................ ...
... Using Rules to Block or Allow Specific Kinds of Traffic ..................................................4-2 Services-Based Rules ..............................................................................................4-2 Viewing the Firewall Rules ............................................ ...
OSPF
... 2. DBD - The Database Description (DBD) packet contains an abbreviated list of the sending router's link-state database and is used by receiving routers to check against the local link-state database. 3. LSR - Receiving routers can then request more information about any entry in the DBD by sending ...
... 2. DBD - The Database Description (DBD) packet contains an abbreviated list of the sending router's link-state database and is used by receiving routers to check against the local link-state database. 3. LSR - Receiving routers can then request more information about any entry in the DBD by sending ...
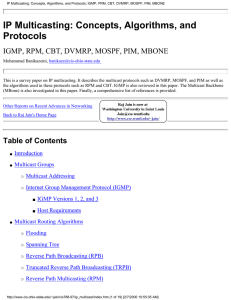
IP Multicasting: Concepts, Algorithms, and Protocols
... sending the query to those hosts which are potentially capable of providing this service would be of great help. Although some applications use multicast messages to transmit a packet to a group of hosts residing on the same network, there is no reason to impose this limitation. Discovering the loca ...
... sending the query to those hosts which are potentially capable of providing this service would be of great help. Although some applications use multicast messages to transmit a packet to a group of hosts residing on the same network, there is no reason to impose this limitation. Discovering the loca ...
VLAN Trunking
... • Cost savings result from less need for expensive network upgrades and more efficient use of existing bandwidth and uplinks. ...
... • Cost savings result from less need for expensive network upgrades and more efficient use of existing bandwidth and uplinks. ...
AltitudeTM 35x0 Access Point Product Reference Guide, Software
... Chapter 1: About This Guide............................................................................................................. 7 Introduction ...............................................................................................................................7 Document Convention ...
... Chapter 1: About This Guide............................................................................................................. 7 Introduction ...............................................................................................................................7 Document Convention ...
Application Notes for HP ProCurve Networking Switches connected
... the IP Office site-to-site trunk and verifying voice quality in a converged VoIP and Data network scenario. Quality of Service (QoS) based on 802.1p (Layer 2 Priority) and Layer 3 Differentiated Services (DiffServ) was implemented across the network to prioritize voice and SNC traffic over the LAN. ...
... the IP Office site-to-site trunk and verifying voice quality in a converged VoIP and Data network scenario. Quality of Service (QoS) based on 802.1p (Layer 2 Priority) and Layer 3 Differentiated Services (DiffServ) was implemented across the network to prioritize voice and SNC traffic over the LAN. ...
ospf_1 - D-Link
... Typically referred to as LSDB Contains all routers and their attached links in the area or network Identical LSDB for all routers within an area – Routing table: ...
... Typically referred to as LSDB Contains all routers and their attached links in the area or network Identical LSDB for all routers within an area – Routing table: ...
BCM Handbook
... This is the Way. This is Nortel, Nortel, the Nortel logo, the Globemark, Norstar, Call Pilot and Meridian 1 are trademarks of Nortel Networks. All other trademarks are the property of their owners. Copyright © 2005 Nortel Networks. All rights reserved. Information in this document is subject to cha ...
... This is the Way. This is Nortel, Nortel, the Nortel logo, the Globemark, Norstar, Call Pilot and Meridian 1 are trademarks of Nortel Networks. All other trademarks are the property of their owners. Copyright © 2005 Nortel Networks. All rights reserved. Information in this document is subject to cha ...
Architectures and Algorithms for IPv4/IPv6
... other departments within Siemens S.A. in Portugal and with Siemens AG (Germany) was frequent. The focus of its research activities ranged from the transport to the protocol layers of network science. The research group included Physicists, Electrotechnical Engineers, Informatic Engineers and Mathema ...
... other departments within Siemens S.A. in Portugal and with Siemens AG (Germany) was frequent. The focus of its research activities ranged from the transport to the protocol layers of network science. The research group included Physicists, Electrotechnical Engineers, Informatic Engineers and Mathema ...
APNIC Tutorial: IPv6 Essentials
... • IPv6 routers no longer perform fragmentation. IPv6 host use a discovery process [Path MTU Discovery] to determine most optimum MTU size before creating end to end session • In this discovery process, the source IPv6 device attempts to send a packet at the size specified by the upper IP layers [i ...
... • IPv6 routers no longer perform fragmentation. IPv6 host use a discovery process [Path MTU Discovery] to determine most optimum MTU size before creating end to end session • In this discovery process, the source IPv6 device attempts to send a packet at the size specified by the upper IP layers [i ...
SnapGear Administration Guide Firmware Version 3.1.5
... Software Product, including all computer programs and documentation, and erasing any copies residing on computer equipment. This Agreement also will automatically terminate if you do not comply with any terms or conditions of this Agreement. Upon such termination you agree to destroy the Software Pr ...
... Software Product, including all computer programs and documentation, and erasing any copies residing on computer equipment. This Agreement also will automatically terminate if you do not comply with any terms or conditions of this Agreement. Upon such termination you agree to destroy the Software Pr ...
Slide 1
... When using these configurations the Blaster Manager on the customer site controls the operations, it shows test results and provides a test report. The Blaster Manager uses a license system based on phone loading levels. Licenses can be for a specified phone loading level or they can be Pay As You G ...
... When using these configurations the Blaster Manager on the customer site controls the operations, it shows test results and provides a test report. The Blaster Manager uses a license system based on phone loading levels. Licenses can be for a specified phone loading level or they can be Pay As You G ...
FortiOS™ Handbook - Advanced Routing for FortiOS 5.2
... computers. Routing tables may also include information about the quality of service (QoS) of the route, and the interface associated with the route if the device has multiple interfaces. Looking at routing as delivering letters is more simple than reality. In reality, routers loose power or have bad ...
... computers. Routing tables may also include information about the quality of service (QoS) of the route, and the interface associated with the route if the device has multiple interfaces. Looking at routing as delivering letters is more simple than reality. In reality, routers loose power or have bad ...
Ingate Firewall & SIParator Training
... priority traffic will always be let through before lower priority traffic is allowed (but see also the Loose Priority setting). ...
... priority traffic will always be let through before lower priority traffic is allowed (but see also the Loose Priority setting). ...
CoreBuilder 3500 Implementation Guide
... in any form or by any means or used to make any derivative work (such as translation, transformation, or adaptation) without written permission from 3Com Corporation. 3Com Corporation reserves the right to revise this documentation and to make changes in content from time to time without obligation ...
... in any form or by any means or used to make any derivative work (such as translation, transformation, or adaptation) without written permission from 3Com Corporation. 3Com Corporation reserves the right to revise this documentation and to make changes in content from time to time without obligation ...
Preparing for an IPv6 World with LXI Instruments
... LXI IPv6 requires Instruments accept IPv6 connect requests. However, IPv6 connections require coordinated IPv6 support Operating System, Firewalls, Routers, Corporate LAN infrastructure, Internet Service Providers IPv6 support is getting better Firewalls and Corporate LANs don’t block IPv6 by de ...
... LXI IPv6 requires Instruments accept IPv6 connect requests. However, IPv6 connections require coordinated IPv6 support Operating System, Firewalls, Routers, Corporate LAN infrastructure, Internet Service Providers IPv6 support is getting better Firewalls and Corporate LANs don’t block IPv6 by de ...