Fully-Functional Succinct Trees
... RAM with word length Θ(log n) in which arithmetic and logical operations on Θ(log n)-bit integers and Θ(log n)-bit memory accesses can be done in constant time. Under this model, there exist many succinct representations of ordinal trees achieving 2n + o(n) bits of space. Basically there exist three ...
... RAM with word length Θ(log n) in which arithmetic and logical operations on Θ(log n)-bit integers and Θ(log n)-bit memory accesses can be done in constant time. Under this model, there exist many succinct representations of ordinal trees achieving 2n + o(n) bits of space. Basically there exist three ...
Data Structures Lab Manual – BE II/IV – I Sem
... Front fixed and Rear Variable: in this representation, rear pointer is variable, whereas front pointer is fixed, which means that front always point to the array index 0. Hence each deletion on a queue causes the elements from index 1 to rear to move one position down, backward movement of data. Fro ...
... Front fixed and Rear Variable: in this representation, rear pointer is variable, whereas front pointer is fixed, which means that front always point to the array index 0. Hence each deletion on a queue causes the elements from index 1 to rear to move one position down, backward movement of data. Fro ...
Do Individual Behavioral Biases Affect Financial Markets and the
... investors increases the price of risk, reduces asset prices, and distorts growth. We find that for reasonable parameter values these effects are substantial. The single key assumption in our model, that investors hold poorly-diversified portfolios, is one for which economists have gathered a great d ...
... investors increases the price of risk, reduces asset prices, and distorts growth. We find that for reasonable parameter values these effects are substantial. The single key assumption in our model, that investors hold poorly-diversified portfolios, is one for which economists have gathered a great d ...
strukture for the decree on minimum capital requirements for market
... (e) "expected positive exposure (EPE)" means the weighted average over time of expected exposures where the weights are the proportion that an individual expected exposure represents of the entire time interval. When calculating the minimum capital requirement, the average is taken over the first ye ...
... (e) "expected positive exposure (EPE)" means the weighted average over time of expected exposures where the weights are the proportion that an individual expected exposure represents of the entire time interval. When calculating the minimum capital requirement, the average is taken over the first ye ...
Chapter 7 Bequests and the modified golden rule
... require bt+i = 0: The condition (7.8) is an extension of this principle to an in…nite horizon.1 The optimality conditions (7.6), (7.7), and (7.8) illustrate a general principle of intertemporal optimization. First, no gain should be achievable by a reallocation of resources between two periods or be ...
... require bt+i = 0: The condition (7.8) is an extension of this principle to an in…nite horizon.1 The optimality conditions (7.6), (7.7), and (7.8) illustrate a general principle of intertemporal optimization. First, no gain should be achievable by a reallocation of resources between two periods or be ...
View
... Determine whether the stack is empty or not Determine whether the stack is full or not Find the size of the stack (how many items are in it) PUSH a new entry onto the top of the stack providing it is not full Copy the top entry from the stack providing it is not empty POP the entry off the top of th ...
... Determine whether the stack is empty or not Determine whether the stack is full or not Find the size of the stack (how many items are in it) PUSH a new entry onto the top of the stack providing it is not full Copy the top entry from the stack providing it is not empty POP the entry off the top of th ...
Data and Data Structures
... A limited set of symbols is used. Each symbol has its own inherent numerical value. These values are zero, one, two, etc. A number is represented by a sequence of symbols. Each sequence is bounded in length (“finite”) but no upper limit is placed on that length. A positional value is associa ...
... A limited set of symbols is used. Each symbol has its own inherent numerical value. These values are zero, one, two, etc. A number is represented by a sequence of symbols. Each sequence is bounded in length (“finite”) but no upper limit is placed on that length. A positional value is associa ...
IPE EDHEC-Risk Research Insights Spring 2014
... To obtain a better understanding of the true meaning of risk factor allocation, it is useful to go back to the foundations of asset pricing theory. Asset pricing theory suggests that individual securities earn their risk premium through their exposures to rewarded factors (see Merton [1973] Intertem ...
... To obtain a better understanding of the true meaning of risk factor allocation, it is useful to go back to the foundations of asset pricing theory. Asset pricing theory suggests that individual securities earn their risk premium through their exposures to rewarded factors (see Merton [1973] Intertem ...
Open Data Structures (in C++)
... Processor speeds: At the time of writing, even a very fast desktop computer can not do more than one billion (109 ) operations per second.1 This means that this application will take at least 1012 /109 = 1000 seconds, or roughly 16 minutes and 40 seconds. 16 minutes is an eon in computer time, but a ...
... Processor speeds: At the time of writing, even a very fast desktop computer can not do more than one billion (109 ) operations per second.1 This means that this application will take at least 1012 /109 = 1000 seconds, or roughly 16 minutes and 40 seconds. 16 minutes is an eon in computer time, but a ...
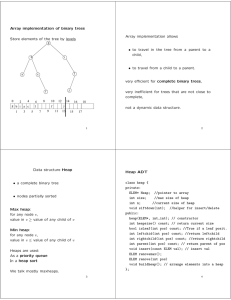
Array implementation of binary trees
... are clustered together. It reacts very dynamically to changes of access patterns. Easy to implement for linked lists only. Transpose is easy to implement for both, arrays and linked lists. There are always some access patterns that make any of the above rather bad. A self-organizing list can perform ...
... are clustered together. It reacts very dynamically to changes of access patterns. Easy to implement for linked lists only. Transpose is easy to implement for both, arrays and linked lists. There are always some access patterns that make any of the above rather bad. A self-organizing list can perform ...
Why firms issue callable bonds: Hedging
... In the first part of the paper, we develop a theory on a firm's ex ante choice between issuing a callable or non-callable bond, its ex post decisions whether to call back a callable bond, and whether to refund it. On the one hand, our theory explains the existing empirical findings in the current liter ...
... In the first part of the paper, we develop a theory on a firm's ex ante choice between issuing a callable or non-callable bond, its ex post decisions whether to call back a callable bond, and whether to refund it. On the one hand, our theory explains the existing empirical findings in the current liter ...
C Data Structures
... Figure 12.5 illustrates the insertion of a node containing the character 'C' into an ordered list. Part (a) of the figure shows the list and the new node just before the insertion. Part (b) of the figure shows the result of inserting the new node. The reassigned pointers are dotted arrows. For simpl ...
... Figure 12.5 illustrates the insertion of a node containing the character 'C' into an ordered list. Part (a) of the figure shows the list and the new node just before the insertion. Part (b) of the figure shows the result of inserting the new node. The reassigned pointers are dotted arrows. For simpl ...
DATA STRUCTURES The term data structure is used to describe the
... The design of a data structure involves more than just its organization. You also need to plan for the way the data will be accessed and processed – that is, how the data will be interpreted actually, non-contiguous structures – including lists, tree and graphs – can be implemented either contiguous ...
... The design of a data structure involves more than just its organization. You also need to plan for the way the data will be accessed and processed – that is, how the data will be interpreted actually, non-contiguous structures – including lists, tree and graphs – can be implemented either contiguous ...
Lattice model (finance)

For other meanings, see lattice model (disambiguation)In finance, a lattice model [1] is a technique applied to the valuation of derivatives, where, because of path dependence in the payoff, 1) a discretized model is required and 2) Monte Carlo methods fail to account for optimal decisions to terminate the derivative by early exercise. For equity options, a typical example would be pricing an American option, where a decision as to option exercise is required at ""all"" times (any time) before and including maturity. A continuous model, on the other hand, such as Black Scholes, would only allow for the valuation of European options, where exercise is on the option's maturity date. For interest rate derivatives lattices are additionally useful in that they address many of the issues encountered with continuous models, such as pull to par.