Integrating Windows Clients and the SAS System into the Enterprise
... are stored in another store such as Microsoft SQL Server, Lotus Notes, or an ODBCcompliant application, a SAS/ACCESS product may be required. If SAS/ACCESS software can operate on the same machine as the data source, this may improve performance. the data by the client software may have give some fl ...
... are stored in another store such as Microsoft SQL Server, Lotus Notes, or an ODBCcompliant application, a SAS/ACCESS product may be required. If SAS/ACCESS software can operate on the same machine as the data source, this may improve performance. the data by the client software may have give some fl ...
Vembu BDR v2.1.1
... : Instant boot/drive mounting fails when an earlier boot session was interrupted Instant boot/drive mounting fails with “Error: The file or directory is corrupted and unreadable.” This often happens if an earlier instant boot session for the same VHD file was interrupted or did not proceed to com ...
... : Instant boot/drive mounting fails when an earlier boot session was interrupted Instant boot/drive mounting fails with “Error: The file or directory is corrupted and unreadable.” This often happens if an earlier instant boot session for the same VHD file was interrupted or did not proceed to com ...
Beginners Guide to EDI X12 (including HIPAA)
... If you look at the typical EDI X12 file, it is very hard to see that there are loops (blocks of repeating data) in it. Unlike XML format EDI X12 does not have such concept as “closing tag”. So it is not obvious where one block ends and another begins. Only by looking at EDI X12 standard documentatio ...
... If you look at the typical EDI X12 file, it is very hard to see that there are loops (blocks of repeating data) in it. Unlike XML format EDI X12 does not have such concept as “closing tag”. So it is not obvious where one block ends and another begins. Only by looking at EDI X12 standard documentatio ...
An Update on SAS Software and ODBC
... Thanks for Forrest Boozer of SAS Institute for reviewing my paper and providing insights on the future of ODBC at SAS. Thank you to Ed Roberts at Conceptual Software for proofreading my section on DBMS Copy, and for providing such a wonderful product. SAS is a registered trademark of SAS Institute I ...
... Thanks for Forrest Boozer of SAS Institute for reviewing my paper and providing insights on the future of ODBC at SAS. Thank you to Ed Roberts at Conceptual Software for proofreading my section on DBMS Copy, and for providing such a wonderful product. SAS is a registered trademark of SAS Institute I ...
Chapter 6
... which all of the database actions occur or none of them do. • A transaction consists of a series of steps. Each step must be successful for the transaction to be saved • This ensures that the transaction completes everything it intended to do before saving the changes KROENKE and AUER - DATABASE CON ...
... which all of the database actions occur or none of them do. • A transaction consists of a series of steps. Each step must be successful for the transaction to be saved • This ensures that the transaction completes everything it intended to do before saving the changes KROENKE and AUER - DATABASE CON ...
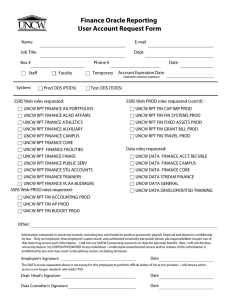
Finance Oracle Reporting User Account Request Form
... UNCW RPT FIN ACCOUNTING PROD UNCW RPT FIN AP PROD UNCW RPT FIN BUDGET PROD Other: Information contained in university records, including but not limited to student, personnel, payroll, financial and alumni is confidential by law. Only an employee, that employee's supervisor(s) and authorized univers ...
... UNCW RPT FIN ACCOUNTING PROD UNCW RPT FIN AP PROD UNCW RPT FIN BUDGET PROD Other: Information contained in university records, including but not limited to student, personnel, payroll, financial and alumni is confidential by law. Only an employee, that employee's supervisor(s) and authorized univers ...
DBC-e03-Chapter-06-PP
... • In reprocessing, all activities the since the backup was performed are redone • This is a brunt-force technique • This procedure is costly in the effort involved in re-entering the data • This procedure is risky in that human error is likely and in that paper record-keeping may not be accurate KRO ...
... • In reprocessing, all activities the since the backup was performed are redone • This is a brunt-force technique • This procedure is costly in the effort involved in re-entering the data • This procedure is risky in that human error is likely and in that paper record-keeping may not be accurate KRO ...
Costing Systems and the Spare Capacity Conundrum
... quantity of capital facilities, taking management‟s operational policy decisions regarding setup, maintenance, and work shifts into account. Thus this predetermined practical capacity standard volume implies certain operational efficiency, not present in the other base denominators‟ activity used. M ...
... quantity of capital facilities, taking management‟s operational policy decisions regarding setup, maintenance, and work shifts into account. Thus this predetermined practical capacity standard volume implies certain operational efficiency, not present in the other base denominators‟ activity used. M ...
Non-Conventional Variance Analysis [Ncva], Its
... The extent to which the causes of variances are established depends upon the amount of time, effort and money a company is willing to spend in data collection as the variances occur. (iii) In variance analysis, a point is reached where incremental cost of data procurement does not commensurate its i ...
... The extent to which the causes of variances are established depends upon the amount of time, effort and money a company is willing to spend in data collection as the variances occur. (iii) In variance analysis, a point is reached where incremental cost of data procurement does not commensurate its i ...
Chapter 20: Entity Beans and Persistence
... conversational state isn't turned into transactional state, it can disappear when a component of the application disappears" ...
... conversational state isn't turned into transactional state, it can disappear when a component of the application disappears" ...
REDCap Technical Overview Introduction REDCap Infrastructure
... To help protect and secure the data stored in REDCap’s back end database, the software application employs various methods to protect against malicious users who may attempt to identify and exploit any security vulnerabilities in the system. Such methods will be described here in technical detail. I ...
... To help protect and secure the data stored in REDCap’s back end database, the software application employs various methods to protect against malicious users who may attempt to identify and exploit any security vulnerabilities in the system. Such methods will be described here in technical detail. I ...
sosftp - SOS
... No implicit mechanism to ensure successful transfer of a group of files. No implicit mechanism to specify secondary host/login credentials should an FTP server not be accessible or in case of any other FTP login ...
... No implicit mechanism to ensure successful transfer of a group of files. No implicit mechanism to specify secondary host/login credentials should an FTP server not be accessible or in case of any other FTP login ...
The Customer Marketing Database: Cutting Costs and Improving
... brands, the complexity of its build and ongoing operation increases exponentially. Business processes, campaign designs, and the overall complexity of ongoing tasks become greater. Multi-brand customer marketing databases have many benefits for developing and leveraging complete customer insights. B ...
... brands, the complexity of its build and ongoing operation increases exponentially. Business processes, campaign designs, and the overall complexity of ongoing tasks become greater. Multi-brand customer marketing databases have many benefits for developing and leveraging complete customer insights. B ...
Getting Started with Databases
... Use the WinMySQLAdmin interface (not simply c:\mysql\bin) Starts the database server for the first time Creates a userID and password (typically not used again) ...
... Use the WinMySQLAdmin interface (not simply c:\mysql\bin) Starts the database server for the first time Creates a userID and password (typically not used again) ...
Data Warehouse Design and Management: Theory and Practice
... 1) Relational databases: A database is called this way when the data elements and relationships that exist between them are recorded in tabular form. It is used both for transactional systems and DWs, but data are optimized differently because of different requirements that characterize the two type ...
... 1) Relational databases: A database is called this way when the data elements and relationships that exist between them are recorded in tabular form. It is used both for transactional systems and DWs, but data are optimized differently because of different requirements that characterize the two type ...
download
... • Presentation logic layer—processing that must be done to generate the presentation, such as editing input data or formatting output data. • Application logic layer—the logic and processing to support business rules, policies, and procedures • Data manipulation layer—to store and retrieve data to a ...
... • Presentation logic layer—processing that must be done to generate the presentation, such as editing input data or formatting output data. • Application logic layer—the logic and processing to support business rules, policies, and procedures • Data manipulation layer—to store and retrieve data to a ...
6 E - Commerce Systems Technology Infrastructure
... framework. The power of CORBA thus lies in enabling the building of distributed and object-oriented applications and facilitating interoperability between software objects regardless of their implementation details. The object-oriented approach of the CORBA specification facilitates simpler integrat ...
... framework. The power of CORBA thus lies in enabling the building of distributed and object-oriented applications and facilitating interoperability between software objects regardless of their implementation details. The object-oriented approach of the CORBA specification facilitates simpler integrat ...
document-centric XML - McGraw Hill Higher Education
... • A relational database is a database in which related information is stored in tables, and data is linked between tables. • Each individual item and the information collected about it is known as a record. • Each record should be assigned a unique number. • Relational databases contain more than on ...
... • A relational database is a database in which related information is stored in tables, and data is linked between tables. • Each individual item and the information collected about it is known as a record. • Each record should be assigned a unique number. • Relational databases contain more than on ...
REDCap General Security Overview Introduction REDCap
... and their user account will only have access to REDCap projects that they themselves have created or to projects which other users have granted them access. Some of the general user privileges in the application are dictated by the customizable settings that each institution can adjust, such as whet ...
... and their user account will only have access to REDCap projects that they themselves have created or to projects which other users have granted them access. Some of the general user privileges in the application are dictated by the customizable settings that each institution can adjust, such as whet ...
SCT Operational Data Store / Banner to the ODS Implementation
... formats, and fields requiring additional verification against rule tables. After the values are properly checked, the data is committed (or written) to the database table that will ‘house’ the information. During the ‘commit’ action, any Oracle triggers on the database table being written to are ‘fi ...
... formats, and fields requiring additional verification against rule tables. After the values are properly checked, the data is committed (or written) to the database table that will ‘house’ the information. During the ‘commit’ action, any Oracle triggers on the database table being written to are ‘fi ...
“Counting Your Customers” the Easy Way: An
... the frequency and timing of transactions for a list of customers, it is natural to try to make forecasts about future purchasing. These projections often range from aggregate sales trajectories (e.g., for the next 52 weeks), to individual-level conditional expectations (i.e., the best guess about a ...
... the frequency and timing of transactions for a list of customers, it is natural to try to make forecasts about future purchasing. These projections often range from aggregate sales trajectories (e.g., for the next 52 weeks), to individual-level conditional expectations (i.e., the best guess about a ...
Informatica Data Replication: Moving and Synchronizing Real
... quality and governance, data virtualization, high-speed messaging, complex event processing, and delivery into the cloud. It should participate in and with these capabilities in an integrated fashion while maintaining consistency with what a replication solution is intended to provide. ...
... quality and governance, data virtualization, high-speed messaging, complex event processing, and delivery into the cloud. It should participate in and with these capabilities in an integrated fashion while maintaining consistency with what a replication solution is intended to provide. ...
What is LDAP (Lightweight Directory Access Protocol
... accessing online directory information. LDAP is an open industry standard. A directory such as a telephone directory is a listing of entries (objects) and information about these entries. LDAP directories are used to store data like white pages, user profiles, and devices available on the company ne ...
... accessing online directory information. LDAP is an open industry standard. A directory such as a telephone directory is a listing of entries (objects) and information about these entries. LDAP directories are used to store data like white pages, user profiles, and devices available on the company ne ...
Connecting SAS
... SAS is an integral part of the work we do with clients at the RAND Corporation. Additionally, in our group at RAND, we keep our data warehousing environment and our analytical environment on separate platforms to maximize resources for both, which has made communication between SAS and MS SQL Server ...
... SAS is an integral part of the work we do with clients at the RAND Corporation. Additionally, in our group at RAND, we keep our data warehousing environment and our analytical environment on separate platforms to maximize resources for both, which has made communication between SAS and MS SQL Server ...




![Non-Conventional Variance Analysis [Ncva], Its](http://s1.studyres.com/store/data/021071783_1-bb904c7603a6036415d5a30b0b0c19af-300x300.png)