Peripherals 2 - computing.northampton.ac.uk
... program files that are not in use at a particular time, but we may want to use them later. We need storage methods that do not lose information when the power is turned off. The disk address uses sector and track. The data on a disk is stored in a binary form as magnetic dots along the tracks Floppy ...
... program files that are not in use at a particular time, but we may want to use them later. We need storage methods that do not lose information when the power is turned off. The disk address uses sector and track. The data on a disk is stored in a binary form as magnetic dots along the tracks Floppy ...
13_GLP_Data_Integrity_draft
... of full audit trails to show all changes to the data while retaining previous and original data. It should be possible to associate all changes to data with the persons making those changes, and changes should be time stamped and a reason given. Users should not have the ability to amend or switch o ...
... of full audit trails to show all changes to the data while retaining previous and original data. It should be possible to associate all changes to data with the persons making those changes, and changes should be time stamped and a reason given. Users should not have the ability to amend or switch o ...
Fraudulent Emails, Websites and Phishing Variations Fraudulent
... website, your bank statements, and those listed on your ATM, debit or credit card. Text-message phishing A phishing attempt sent via SMS (Short Message Service) or text message to a mobile phone or device. This tactic is also referred to as smishing, which is a combination of SMS and phishing. The p ...
... website, your bank statements, and those listed on your ATM, debit or credit card. Text-message phishing A phishing attempt sent via SMS (Short Message Service) or text message to a mobile phone or device. This tactic is also referred to as smishing, which is a combination of SMS and phishing. The p ...
Reporting Services Guru: Developing Reports - austin
... ◦ Requires a data source (shared or embedded) ◦ Fields are available for use in reports ...
... ◦ Requires a data source (shared or embedded) ◦ Fields are available for use in reports ...
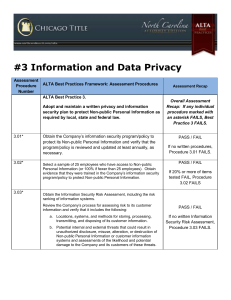
ALTA Assessment Procedures
... Information is restricted to authorized persons only. a. For the sample of employees tested in Assessment Procedure 3.02 above, test the user access provisioning process to determine if access is approved in accordance with policy prior to granting. o Obtain evidence (invoice/documentation in person ...
... Information is restricted to authorized persons only. a. For the sample of employees tested in Assessment Procedure 3.02 above, test the user access provisioning process to determine if access is approved in accordance with policy prior to granting. o Obtain evidence (invoice/documentation in person ...
Undergraduate Degree Programs in Data Science Abstract 1
... two courses that add 6 more credits towards the data science degree. Students also take one or more courses in software systems development as a capstone project that satisfies the writing requirement. Students take additional courses to satisfy general education and other departmental as well as un ...
... two courses that add 6 more credits towards the data science degree. Students also take one or more courses in software systems development as a capstone project that satisfies the writing requirement. Students take additional courses to satisfy general education and other departmental as well as un ...
IM-Ch01-DB-Systems-Ed10
... have a significant impact on a company's resources and culture. The changes introduced by the adoption of a database system must be properly managed to ensure that they help advance the company's objectives. Given the fact that databases systems hold crucial company data that are accessed from multi ...
... have a significant impact on a company's resources and culture. The changes introduced by the adoption of a database system must be properly managed to ensure that they help advance the company's objectives. Given the fact that databases systems hold crucial company data that are accessed from multi ...
What is SQL Injection?
... Modify database data (Insert/Update/Delete) Execute administration operations on the database (such as shutdown the DBMS) Recover the content of a given file present on the DBMS file system In some cases issue commands to the operating system. ...
... Modify database data (Insert/Update/Delete) Execute administration operations on the database (such as shutdown the DBMS) Recover the content of a given file present on the DBMS file system In some cases issue commands to the operating system. ...
Text S1.
... D. Handling of the samples from the Annual Sample Collection During the annual sample collection, there are two strategies, one in the Health Center auditorium and the other in the field. Study participants who come to the Health Center auditoium first pass through a station for identificaion and re ...
... D. Handling of the samples from the Annual Sample Collection During the annual sample collection, there are two strategies, one in the Health Center auditorium and the other in the field. Study participants who come to the Health Center auditoium first pass through a station for identificaion and re ...
Sample Chapter 4 Data Buffering - dFPUG
... Data buffering puts your table in a “just kidding” mode. You put your table in one of VFP’s buffering modes, and you can edit records without actually changing the table on disk. If your user decides to save, then you can tell VFP you were serious in one line of code. In the old days when you change ...
... Data buffering puts your table in a “just kidding” mode. You put your table in one of VFP’s buffering modes, and you can edit records without actually changing the table on disk. If your user decides to save, then you can tell VFP you were serious in one line of code. In the old days when you change ...
Question Bank
... Standard framework that intuitive and allows for high-performance access. It is inherently Dimensional and adheres to a discipline that uses the relational model with some important restrictions. What comprises of a dimensional model? Dimensional model is composed of one table with a multipart key c ...
... Standard framework that intuitive and allows for high-performance access. It is inherently Dimensional and adheres to a discipline that uses the relational model with some important restrictions. What comprises of a dimensional model? Dimensional model is composed of one table with a multipart key c ...
Databases
... Distinguish between the physical and logical views of data. Describe how data is organized: characters, fields, records, tables, and databases. Define key fields and how they are used to integrate data in a database. Define and compare batch processing and real-time processing. ...
... Distinguish between the physical and logical views of data. Describe how data is organized: characters, fields, records, tables, and databases. Define key fields and how they are used to integrate data in a database. Define and compare batch processing and real-time processing. ...
ppt
... – Dynamic casts check additional information at run-time (e.g., if polymorphic) may throw exception, return 0 pointer, etc. CSE 425: Data Types I ...
... – Dynamic casts check additional information at run-time (e.g., if polymorphic) may throw exception, return 0 pointer, etc. CSE 425: Data Types I ...
IOT Multiprotocols in Application layer - Iot-Inc.
... – In the IoT context, XMPP offers an easy way to address a device. This is especially handy if that data is going between distant, mostly unrelated points, just like the person-to-person case. It’s not designed to be fast. In fact, most implementations use polling, or checking for updates only on de ...
... – In the IoT context, XMPP offers an easy way to address a device. This is especially handy if that data is going between distant, mostly unrelated points, just like the person-to-person case. It’s not designed to be fast. In fact, most implementations use polling, or checking for updates only on de ...
CAD/GIS Integration Workgroup - Indiana Geographic Information
... carry information that would be better stored as Object Data tables. Although end users will of course use additional layer names for specific end uses, it is understood that this imposes a separate need for translation to other platforms and uses. ...
... carry information that would be better stored as Object Data tables. Although end users will of course use additional layer names for specific end uses, it is understood that this imposes a separate need for translation to other platforms and uses. ...
Combat a range of potential data leakage threats with these ultra
... For added security, users can request an authentication certificate; when requested, it is sent separately from the switch. With it, users verify the firmware status of the KVM switch to ensure it has not been compromised. In addition, the VGA card reader versions include active authentication verif ...
... For added security, users can request an authentication certificate; when requested, it is sent separately from the switch. With it, users verify the firmware status of the KVM switch to ensure it has not been compromised. In addition, the VGA card reader versions include active authentication verif ...
Cubes by design
... defines information such as location of data, cube structure, cube-based security permissions and calculated measure definitions. The navigation files are used to help understand how information of the input data translates to the structure of the cube; for example, how members relate to each other ...
... defines information such as location of data, cube structure, cube-based security permissions and calculated measure definitions. The navigation files are used to help understand how information of the input data translates to the structure of the cube; for example, how members relate to each other ...
DataMIME: Component Based Data mining System Architecture
... Net [CGG+02] provides an architecture for building and managing KDD processes on a Grid. Most of the projects are implemented as prototypes. In this paper we attempt to address some of the major issues related to distributed data mining. The solutions suggested were implemented as part of DataMIME™. ...
... Net [CGG+02] provides an architecture for building and managing KDD processes on a Grid. Most of the projects are implemented as prototypes. In this paper we attempt to address some of the major issues related to distributed data mining. The solutions suggested were implemented as part of DataMIME™. ...
kap. 26-36 extra notes about web basics and searching
... pages and return up recursively. This is a narrow but deep search. Crawlers can use much bandwidth. Priorities and restrictions might be set on their use. Crawlers are also referred to as Spiders. ...
... pages and return up recursively. This is a narrow but deep search. Crawlers can use much bandwidth. Priorities and restrictions might be set on their use. Crawlers are also referred to as Spiders. ...
Parallelism and Business Intelligence (cont…)
... At this point it makes sense to review the value of parallelism with respect to a number of the BI-related applications. In each of these applications, a significant speedup can be achieved by exploiting parallelism. • Query Processing Relational database management systems will most likely have tak ...
... At this point it makes sense to review the value of parallelism with respect to a number of the BI-related applications. In each of these applications, a significant speedup can be achieved by exploiting parallelism. • Query Processing Relational database management systems will most likely have tak ...
Analysis Services Schema Rowsets | Microsoft Docs
... a reporting application that retrieves the list of available dimensions that can be used to create a report). NOTE If you are using schema rowsets in XML/A script, the information that is returned in the Result parameter of the Discover method is structured according to the rowset column layouts des ...
... a reporting application that retrieves the list of available dimensions that can be used to create a report). NOTE If you are using schema rowsets in XML/A script, the information that is returned in the Result parameter of the Discover method is structured according to the rowset column layouts des ...
Oracle: From Client Server to the Grid and beyond Oracle Corporation Graham Wood
... Software installed and configured ...
... Software installed and configured ...
Data Warehouses, Data Marts, and Data Warehousing
... A department-oriented data warehouse is a subject-oriented, integrated, time-variant, non-volatile collection of data in support of management's decision making process about any and all departments, and their interactions with one another and with the external world. A business process data mart is ...
... A department-oriented data warehouse is a subject-oriented, integrated, time-variant, non-volatile collection of data in support of management's decision making process about any and all departments, and their interactions with one another and with the external world. A business process data mart is ...