SMILA: SeMantic Information Logistics Architecture
... Data Source Management (integration and access): The objective is to make available a set of connectors (crawlers) for the most relevant data sources (e.g. file system, database systems, web). ...
... Data Source Management (integration and access): The objective is to make available a set of connectors (crawlers) for the most relevant data sources (e.g. file system, database systems, web). ...
Evaluating Databases for Cloud Applications
... rather how much of their business will be done with cloud applications. A cloud application is one with many endpoints including browsers, mobile devices, and/or machines that are geographically distributed. The application is intensely transactional (high velocity reads and/or writes), always avail ...
... rather how much of their business will be done with cloud applications. A cloud application is one with many endpoints including browsers, mobile devices, and/or machines that are geographically distributed. The application is intensely transactional (high velocity reads and/or writes), always avail ...
Effective Log Management - National Cyber Security Centre
... by local network administration. The following recommendations will still be relevant in situations where a third-party supplier provides a service, although the availability and accessibility of particular records may vary. Therefore, it is important that the availability of log data from these ser ...
... by local network administration. The following recommendations will still be relevant in situations where a third-party supplier provides a service, although the availability and accessibility of particular records may vary. Therefore, it is important that the availability of log data from these ser ...
TeraText DBS Frequently Asked Questions (FAQ) 13. All rights reserved.
... custom term weighting, boolean operators, ranking, sorting, field-based queries, wild cards (truncation) and saving of result sets for “search within” functionality. Queries can be saved and rerun at specified intervals for automated retrieval of new information. The TeraText DBS also provides a “sc ...
... custom term weighting, boolean operators, ranking, sorting, field-based queries, wild cards (truncation) and saving of result sets for “search within” functionality. Queries can be saved and rerun at specified intervals for automated retrieval of new information. The TeraText DBS also provides a “sc ...
View File - UET Taxila
... Two users with joint account trying to withdraw cash at the same time using ATM at different locations. ...
... Two users with joint account trying to withdraw cash at the same time using ATM at different locations. ...
Database Systems For XML Data Storing
... § In general, the XML data is mapped to database table by relationship between specific tag element and specific column in the table. § After storing the XML data in the relational database, following operations such as exclusion control, search, back up management will be easy. § There is a need to ...
... § In general, the XML data is mapped to database table by relationship between specific tag element and specific column in the table. § After storing the XML data in the relational database, following operations such as exclusion control, search, back up management will be easy. § There is a need to ...
solid state drive
... Reliability/Longevity The other major problem SSDs have is with longevity. As fast as the technology allows solid-state drives to be, it limits them in that each transistor may only be written to a certain number of times before it becomes “stuck” and cannot be written to any more. This is the solid ...
... Reliability/Longevity The other major problem SSDs have is with longevity. As fast as the technology allows solid-state drives to be, it limits them in that each transistor may only be written to a certain number of times before it becomes “stuck” and cannot be written to any more. This is the solid ...
Hampton Roads REALTORS ® Association Partners with RPR
... Hampton Roads REALTORS® Association Partners with RPR® Chesapeake, VA — Hampton Roads REALTORS® Association (HRRA) and Realtors Property Resource (RPR) are pleased to announce that they will be offering integrated MLS data to HRRA members in the RPR Application. Real Estate Information Network, Inc. ...
... Hampton Roads REALTORS® Association Partners with RPR® Chesapeake, VA — Hampton Roads REALTORS® Association (HRRA) and Realtors Property Resource (RPR) are pleased to announce that they will be offering integrated MLS data to HRRA members in the RPR Application. Real Estate Information Network, Inc. ...
CounterACT: Powerful, Automated Network Protection
... over 10 million PCs in just a few short weeks (over a million in a single 24-hour period) ... making it one of the most prolific, dangerous and widespread infections in recent times. Anyone using a Windows-based system was cautioned to verify that their system was free of the Conficker worm and was ...
... over 10 million PCs in just a few short weeks (over a million in a single 24-hour period) ... making it one of the most prolific, dangerous and widespread infections in recent times. Anyone using a Windows-based system was cautioned to verify that their system was free of the Conficker worm and was ...
Slide 1
... The Internet The Internet, sometimes called simply "the Net", connects users worldwide. To access the Internet, a user's computer must connect to a computer called a server, which has special software called TCP/IP (for Transmission Control Protocol/Internet Protocol) that allows different types of ...
... The Internet The Internet, sometimes called simply "the Net", connects users worldwide. To access the Internet, a user's computer must connect to a computer called a server, which has special software called TCP/IP (for Transmission Control Protocol/Internet Protocol) that allows different types of ...
Informatica Data Replication: Moving and Synchronizing Real
... bus or to any other Enterprise Service Bus (ESB) of choice. And because Informatica Data Replication uses log-based change data capture (CDC) techniques, the impact on the underlying database systems and user applications is minimized. Informatica Data Replication includes an efficient bulk data loa ...
... bus or to any other Enterprise Service Bus (ESB) of choice. And because Informatica Data Replication uses log-based change data capture (CDC) techniques, the impact on the underlying database systems and user applications is minimized. Informatica Data Replication includes an efficient bulk data loa ...
Preserving Indonesia's heritage
... ancient pundek (stair-like) terraces in highly detailed accuracy – and all with great success. The scanner was also applied to assist other related cultural institutions to document and collect data of prehistoric bas-relief art. A loss of our cultural heritage would be unthinkable. With the help of ...
... ancient pundek (stair-like) terraces in highly detailed accuracy – and all with great success. The scanner was also applied to assist other related cultural institutions to document and collect data of prehistoric bas-relief art. A loss of our cultural heritage would be unthinkable. With the help of ...
Decision Support Systems
... an engineering firm that has bids on several projects and wants to know if they can be competitive with their costs. DSS is extensively used in business and management. Executive dashboards and other business performance software allow faster decision making, identification of negative trends, a ...
... an engineering firm that has bids on several projects and wants to know if they can be competitive with their costs. DSS is extensively used in business and management. Executive dashboards and other business performance software allow faster decision making, identification of negative trends, a ...
Databases - McMaster University
... Like programming languages, databases allow to process and store data. However: ¡ data is stored in dedicated files and loaded as needed: data can be much larger than the available memory (retailer catalogue, bank accounts, personnel records); there is no need to explicitly open files and read ...
... Like programming languages, databases allow to process and store data. However: ¡ data is stored in dedicated files and loaded as needed: data can be much larger than the available memory (retailer catalogue, bank accounts, personnel records); there is no need to explicitly open files and read ...
ACC - Access Denied!
... and Combatant Commands. However, as the effort progresses from the planning stage to a more technical focus, the membership may require greater technical and functional representation. For example, if you think your COI will impact acquisition, then acquisition organizations should be ...
... and Combatant Commands. However, as the effort progresses from the planning stage to a more technical focus, the membership may require greater technical and functional representation. For example, if you think your COI will impact acquisition, then acquisition organizations should be ...
COPERTINA_TEC_6.qxd:Layout 1
... organization to understand its business (processes, customers, sources, systems and market opportunity areas), in order to take prompt and suitable strategic decisions. Nowadays, BI solutions, whose purpose is to “provide the right information to the right person at the right moment”, are adopted by ...
... organization to understand its business (processes, customers, sources, systems and market opportunity areas), in order to take prompt and suitable strategic decisions. Nowadays, BI solutions, whose purpose is to “provide the right information to the right person at the right moment”, are adopted by ...
Lesson 1: Access Basics
... Computer and information systems managers ensure that information is available to those who need it and blocked for those who should not have access to it. ...
... Computer and information systems managers ensure that information is available to those who need it and blocked for those who should not have access to it. ...
Bio and Abstract
... combined with data analyses methods from the global/earthquake seismology community allow more subsurface information to be extracted from industry seismic exploration data. This presentation reviews selected case histories, current research, current practices, and some speculation on future trends ...
... combined with data analyses methods from the global/earthquake seismology community allow more subsurface information to be extracted from industry seismic exploration data. This presentation reviews selected case histories, current research, current practices, and some speculation on future trends ...
Immutability Changes Everything
... ambiguity by using immutable data in some very fun ways. We will explore how apps use immutability in their ongoing work, how apps generate immutable DataSets for later offline analysis, how SQL can expose and process immutable snapshots, how massively parallel “Big Data” work relies on immutable Da ...
... ambiguity by using immutable data in some very fun ways. We will explore how apps use immutability in their ongoing work, how apps generate immutable DataSets for later offline analysis, how SQL can expose and process immutable snapshots, how massively parallel “Big Data” work relies on immutable Da ...
Data Encryption Standard - gozips.uakron.edu
... properties, users, and important assets Monitoring applications – utilities and applications used to monitor network traffic and Internet activities, downloads, uploads, and other network activities Auditing procedures and tools – checks and controls to ensure that security measures are working ...
... properties, users, and important assets Monitoring applications – utilities and applications used to monitor network traffic and Internet activities, downloads, uploads, and other network activities Auditing procedures and tools – checks and controls to ensure that security measures are working ...
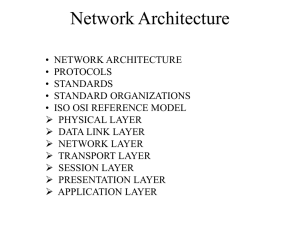
Network Architecture - Electrical Engineering and Computer Science
... products on the rise, networking is pervasive, so governments must do something. • They decided to select this model and issue a Government OSI Profile, usually called a GOSIP. • This means that if a vendor wants to sell communications system to, for example, U.S., UK. French, or German government d ...
... products on the rise, networking is pervasive, so governments must do something. • They decided to select this model and issue a Government OSI Profile, usually called a GOSIP. • This means that if a vendor wants to sell communications system to, for example, U.S., UK. French, or German government d ...
Summary Workshop D
... Statistic Denmark has not yet decided on its spatial architecture. A few experiences using Oracle locator/spatial is going on. E.g. address coordinates are stored in Oracle Spatial using the data type Sdo_geometry. Unlike the other Nordic Statistics, Statistic Denmark have no long tradition for usin ...
... Statistic Denmark has not yet decided on its spatial architecture. A few experiences using Oracle locator/spatial is going on. E.g. address coordinates are stored in Oracle Spatial using the data type Sdo_geometry. Unlike the other Nordic Statistics, Statistic Denmark have no long tradition for usin ...