Servlet Mediator
... With using HTTP calls to simulate IIOP is relative slower than using firewalls dedicated for CORBA, as we need to do many extra works to initialize the servlet, to convert parameters to XML format, invoke the servlets to work, etc. ...
... With using HTTP calls to simulate IIOP is relative slower than using firewalls dedicated for CORBA, as we need to do many extra works to initialize the servlet, to convert parameters to XML format, invoke the servlets to work, etc. ...
American Health Care Association Members October 19, 2011 Page
... in place, but also may wish to implement analysis plans that avoid identification of particular Medicare beneficiaries in the results and aggregations. See Section #8a of the DUA setting forth CMS’s current cell size suppression policy. For assistance in completing this section, the Requestor may wi ...
... in place, but also may wish to implement analysis plans that avoid identification of particular Medicare beneficiaries in the results and aggregations. See Section #8a of the DUA setting forth CMS’s current cell size suppression policy. For assistance in completing this section, the Requestor may wi ...
Decision Support System Architecture, Hardware, and Operating System Platforms
... Jurnal Sistem Informasi Vol. 2 No. 1 Maret 2007 : 41-50 Direct usage of minicomputer by programmers only ...
... Jurnal Sistem Informasi Vol. 2 No. 1 Maret 2007 : 41-50 Direct usage of minicomputer by programmers only ...
Decision Support System Architecture, Hardware, and Operating
... Jurnal Sistem Informasi Vol. 2 No. 1 Maret 2007 : 41-50 Direct usage of minicomputer by programmers only ...
... Jurnal Sistem Informasi Vol. 2 No. 1 Maret 2007 : 41-50 Direct usage of minicomputer by programmers only ...
Conceptual Data Models for Database Design
... The entity type describes the intension, or schema for a set of entities that share the same structure. The collection of entities of a particular entity type is grouped into the entity set, called the extension. Key Attributes of an Entity Type An important constraint on entities of an entity typ ...
... The entity type describes the intension, or schema for a set of entities that share the same structure. The collection of entities of a particular entity type is grouped into the entity set, called the extension. Key Attributes of an Entity Type An important constraint on entities of an entity typ ...
Computational Complexity of Semantic Web Language
... • Whenever the complexity for a given problem is described as Open, with a star, (*), it is meant that its decidability is still an open question; if the star (*) is omitted, then the problem is known to be decidable but precise complexity bounds have not yet been established. If a problem is lab ...
... • Whenever the complexity for a given problem is described as Open, with a star, (*), it is meant that its decidability is still an open question; if the star (*) is omitted, then the problem is known to be decidable but precise complexity bounds have not yet been established. If a problem is lab ...
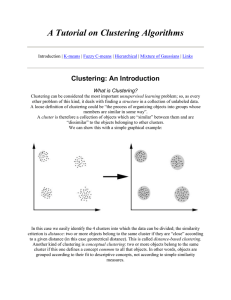
A Tutorial on Clustering Algorithms
... the well known clustering problem. The procedure follows a simple and easy way to classify a given data set through a certain number of clusters (assume k clusters) fixed a priori. The main idea is to define k centroids, one for each cluster. These centroids shoud be placed in a cunning way because ...
... the well known clustering problem. The procedure follows a simple and easy way to classify a given data set through a certain number of clusters (assume k clusters) fixed a priori. The main idea is to define k centroids, one for each cluster. These centroids shoud be placed in a cunning way because ...
Replication of Data in Database Systems for Backup and
... to a data at the primary site is synchronously replicated to a data volume at a secondary site. This ensures that the secondary site has an identical copy of the data at all times. Write I/O operation acknowledgement is sent to the application only after the write I/O operation is acknowledged by th ...
... to a data at the primary site is synchronously replicated to a data volume at a secondary site. This ensures that the secondary site has an identical copy of the data at all times. Write I/O operation acknowledgement is sent to the application only after the write I/O operation is acknowledged by th ...
Data Warehouse Design and Management: Theory and Practice
... B. Database models The easiest way of structuring data consists in a flat file, suitable only for very simple databases. This is for example the case of a spreadsheet in office automation software. From 1960 onwards four main types of models for databases were developed: Hierarchical. Suited for rep ...
... B. Database models The easiest way of structuring data consists in a flat file, suitable only for very simple databases. This is for example the case of a spreadsheet in office automation software. From 1960 onwards four main types of models for databases were developed: Hierarchical. Suited for rep ...
Executive Summary
... The system is highly secure. The entire fabric of the SAN is smoothly integrated with Cisco network security and the firewalls of Cisco’s outside counsel, enabling discovery partners to share data without concern. Cisco has reduced its expenses for legal discovery. As of the writing of this case stu ...
... The system is highly secure. The entire fabric of the SAN is smoothly integrated with Cisco network security and the firewalls of Cisco’s outside counsel, enabling discovery partners to share data without concern. Cisco has reduced its expenses for legal discovery. As of the writing of this case stu ...
Understanding Data Locality in Virtual SAN: VMware, Inc.
... we observe with the ESX network stack. In the case of Virtual SAN this happens on the VMkernel network adapter. One may argue that given the low access latencies of flash devices, network latencies may become apparent when data is accessed remotely. However, a deeper look shows this not to be the ca ...
... we observe with the ESX network stack. In the case of Virtual SAN this happens on the VMkernel network adapter. One may argue that given the low access latencies of flash devices, network latencies may become apparent when data is accessed remotely. However, a deeper look shows this not to be the ca ...
View PDF - CiteSeerX
... that are satis able by tuples in just one class. The d(Av) term is used to select those attribute-value pairs that will require the fewest additional constraints to create a ParkaDB query that is satis ed by tuples in a single class. d(Av) ranges from 0, indicating and even distribution, to 1, indic ...
... that are satis able by tuples in just one class. The d(Av) term is used to select those attribute-value pairs that will require the fewest additional constraints to create a ParkaDB query that is satis ed by tuples in a single class. d(Av) ranges from 0, indicating and even distribution, to 1, indic ...
Immutability Changes Everything
... In some ways, the ability to work across immutable DataSets and relational databases is surprising. Immutable DataSets are defined with an identity and an optional version. Their schema is the schema that describes the shape and form of the DataSet at the time of its creation. It has descriptive sch ...
... In some ways, the ability to work across immutable DataSets and relational databases is surprising. Immutable DataSets are defined with an identity and an optional version. Their schema is the schema that describes the shape and form of the DataSet at the time of its creation. It has descriptive sch ...
OGSA-DAI-RDF & Its Ontology Interfaces Isao Kojima and Masahiro Kimoto
... – We think it is very convenient to cover them in a single framework. ...
... – We think it is very convenient to cover them in a single framework. ...
model-based engineering for laser weapons
... National Defense Industry Association (NDIA) [Bergenthal 2011] and by the Office of the Director, Defense Science and Engineering and as one of four potentially “game-changing” technologies that could bring about revolutionary advances across the entire DoD research and development and procurement c ...
... National Defense Industry Association (NDIA) [Bergenthal 2011] and by the Office of the Director, Defense Science and Engineering and as one of four potentially “game-changing” technologies that could bring about revolutionary advances across the entire DoD research and development and procurement c ...
relation schemas
... • For a frequently updated file, B+Tree index is almost always superior to a sorted file – For small amount of space, we get all the advantages of sorted files plus efficient insertion and deletion ...
... • For a frequently updated file, B+Tree index is almost always superior to a sorted file – For small amount of space, we get all the advantages of sorted files plus efficient insertion and deletion ...
JV3118261831
... Normalization is carried out manually in many of the organizations, which demand for skilled personnel with expertise in Normalization. As the database grows, it becomes difficult to manually handle the normalization process. Thus in this paper, a tool is proposed which aims to automate the most com ...
... Normalization is carried out manually in many of the organizations, which demand for skilled personnel with expertise in Normalization. As the database grows, it becomes difficult to manually handle the normalization process. Thus in this paper, a tool is proposed which aims to automate the most com ...
Churn Analysis Case Study
... customer will churn away before the company can fully recoup its acquisition costs. It is clear that spending money holding on to existing customers is more efficient than acquiring new customers. Consequently, churn management has emerged as a crucial competitive weapon, and a foundation for an en ...
... customer will churn away before the company can fully recoup its acquisition costs. It is clear that spending money holding on to existing customers is more efficient than acquiring new customers. Consequently, churn management has emerged as a crucial competitive weapon, and a foundation for an en ...
X-2E Modernize - Fresche Legacy
... a proprietary file format, it becomes portable — i.e., it is now viable to consider ...
... a proprietary file format, it becomes portable — i.e., it is now viable to consider ...
Dell Storage Center OS 7.0 Data Reduction with
... addition, old data that is archival in nature may need to be retained for years, or even indefinitely, based on company policies, regulations, or service level agreements. Traditionally, a common strategy is to archive old data to tape in order to free up disk space. However, this can negatively aff ...
... addition, old data that is archival in nature may need to be retained for years, or even indefinitely, based on company policies, regulations, or service level agreements. Traditionally, a common strategy is to archive old data to tape in order to free up disk space. However, this can negatively aff ...
Synchronization and replication in the context of mobile applications
... behave like servers, that are not replicated. This strict requirement can not always be fulfilled since the mechanism to solve this problem - synchronous replication or eager replication, where every transaction updates all replicas - produces heavy distributed transaction load. Therefore synchronou ...
... behave like servers, that are not replicated. This strict requirement can not always be fulfilled since the mechanism to solve this problem - synchronous replication or eager replication, where every transaction updates all replicas - produces heavy distributed transaction load. Therefore synchronou ...
PostgreSQL vs NoSQL Why structure matters Cybertec, 2013 Hans-Jürgen Schönig
... - “well, developers have to stick to the rules” => did you ever get caught speeding? => do you always separate your waste before you throw it away? ...
... - “well, developers have to stick to the rules” => did you ever get caught speeding? => do you always separate your waste before you throw it away? ...
Symfony2 Tutorial
... After a model update the model notifies its associated views and controllers, so that the views can produce updated output, and the controllers to change the available set of commands A view requests from the model information needed to generate an output representation ...
... After a model update the model notifies its associated views and controllers, so that the views can produce updated output, and the controllers to change the available set of commands A view requests from the model information needed to generate an output representation ...
Towards Social Webtops Using Semantic Wiki
... • The data layer : it refers to internally stored data including the normal wiki contents and the RDF triples parsed from wiki articles, and imported online data such as Google Map and RSS feeds. • The wiki layer : wiki provides collaborative and extensible programming facilities including the PHP- ...
... • The data layer : it refers to internally stored data including the normal wiki contents and the RDF triples parsed from wiki articles, and imported online data such as Google Map and RSS feeds. • The wiki layer : wiki provides collaborative and extensible programming facilities including the PHP- ...
Frequently Asked Questions
... subsetting techniques. The goal can be a relative table-size such as extracting 1% subset of a table containing 10 billion rows for testing. Condition based subsetting can minimize risk exposure by discarding all user records created prior to a specific date, for example. ...
... subsetting techniques. The goal can be a relative table-size such as extracting 1% subset of a table containing 10 billion rows for testing. Condition based subsetting can minimize risk exposure by discarding all user records created prior to a specific date, for example. ...
Data model
A data model organizes data elements and standardizes how the data elements relate to one another. Since data elements document real life people, places and things and the events between them, the data model represents reality, for example a house has many windows or a cat has two eyes. Computers are used for the accounting of these real life things and events and therefore the data model is a necessary standard to ensure exact communication between human beings.Data models are often used as an aid to communication between the business people defining the requirements for a computer system and the technical people defining the design in response to those requirements. They are used to show the data needed and created by business processes.Precise accounting and communication is a large expense and organizations traditionally paid the cost by having employees translate between themselves on an ad hoc basis. In critical situations such as air travel, healthcare and finance, it is becoming commonplace that the accounting and communication must be precise and therefore requires the use of common data models to obviate risk.According to Hoberman (2009), ""A data model is a wayfinding tool for both business and IT professionals, which uses a set of symbols and text to precisely explain a subset of real information to improve communication within the organization and thereby lead to a more flexible and stable application environment.""A data model explicitly determines the structure of data. Data models are specified in a data modeling notation, which is often graphical in form.A data model can be sometimes referred to as a data structure, especially in the context of programming languages. Data models are often complemented by function models, especially in the context of enterprise models.