Type of Technology
... accordingly divided into three different parts: content creation tools, content management tools and content delivery. The Section provides an overview about administrative tools used to develop the Fes Egov portal. The term “Administrative Tools“ has to be understood as applications for retrieving, ...
... accordingly divided into three different parts: content creation tools, content management tools and content delivery. The Section provides an overview about administrative tools used to develop the Fes Egov portal. The term “Administrative Tools“ has to be understood as applications for retrieving, ...
Overview of Transaction Management
... identify all transactions that were active, and all dirty pages in the buffer pool at the time of the crash. Redo: Redo all updates to dirty pages in the buffer pool, as needed, to ensure that all logged updates are in fact carried out and written to disk. Undo: The writes of all transactions that w ...
... identify all transactions that were active, and all dirty pages in the buffer pool at the time of the crash. Redo: Redo all updates to dirty pages in the buffer pool, as needed, to ensure that all logged updates are in fact carried out and written to disk. Undo: The writes of all transactions that w ...
ppt
... The SQL data-definition language (DDL) allows the specification of information about relations, including: The schema for each relation. The domain of values associated with each attribute. Integrity constraints ...
... The SQL data-definition language (DDL) allows the specification of information about relations, including: The schema for each relation. The domain of values associated with each attribute. Integrity constraints ...
Oracle Database 10g
... The relational database uses the concept of linked two-dimensional tables consisting of rows and columns, as shown in Figure 1-2. Unlike the hierarchical approach, no predetermined relationship exists between distinct tables. This means that the data needed to link together the different areas of th ...
... The relational database uses the concept of linked two-dimensional tables consisting of rows and columns, as shown in Figure 1-2. Unlike the hierarchical approach, no predetermined relationship exists between distinct tables. This means that the data needed to link together the different areas of th ...
REAL TIME DATABASE COMPRESSION OPTIMIZATION USING
... database systems have not heavily utilized compression techniques on data stored in relational tables. A typical compression technique may offer space savings, but only at a cost of much increased query time against the data. Global domain provider used to take the backup of their database multiple ...
... database systems have not heavily utilized compression techniques on data stored in relational tables. A typical compression technique may offer space savings, but only at a cost of much increased query time against the data. Global domain provider used to take the backup of their database multiple ...
transaction
... A policy in which only one transaction can execute at a time generates serial schedules, but provides a poor degree of concurrency. Concurrency-control schemes tradeoff between the amount of concurrency they allow and the amount of overhead that they incur. Some schemes allow only conflict-serializa ...
... A policy in which only one transaction can execute at a time generates serial schedules, but provides a poor degree of concurrency. Concurrency-control schemes tradeoff between the amount of concurrency they allow and the amount of overhead that they incur. Some schemes allow only conflict-serializa ...
Prezentacja programu PowerPoint
... JDBC driver translates calls written in the Java programming language into the specific format required by the server. Most database vendors supply free JDBC drivers for their databases, but there are many third-party vendors of drivers for older databases. An up-to-date list is avaliable at: http:/ ...
... JDBC driver translates calls written in the Java programming language into the specific format required by the server. Most database vendors supply free JDBC drivers for their databases, but there are many third-party vendors of drivers for older databases. An up-to-date list is avaliable at: http:/ ...
CAMEO DATA MODELER PLUGIN
... UML terminology (covering / not covering) is used for completeness property name in Specification window. Other names, more familiar for data modelers, are total / partial and complete / incomplete. These terms are analogous and can be used interchangeably. ...
... UML terminology (covering / not covering) is used for completeness property name in Specification window. Other names, more familiar for data modelers, are total / partial and complete / incomplete. These terms are analogous and can be used interchangeably. ...
Designing BIRT Information Objects - BIRT Developer Center
... Information in this document is subject to change without notice. Examples provided are fictitious. No part of this document may be reproduced or transmitted in any form, or by any means, electronic or mechanical, for any purpose, in whole or in part, without the express written permission of Actua ...
... Information in this document is subject to change without notice. Examples provided are fictitious. No part of this document may be reproduced or transmitted in any form, or by any means, electronic or mechanical, for any purpose, in whole or in part, without the express written permission of Actua ...
ppt
... where one node may be running relational database system under UNIX, another may be running object-oriented system under Windows and so on. • A transaction may run in a distributed fashion at multiple nodes. • In this execution scenario the transaction commits only when all these multiple nodes agre ...
... where one node may be running relational database system under UNIX, another may be running object-oriented system under Windows and so on. • A transaction may run in a distributed fashion at multiple nodes. • In this execution scenario the transaction commits only when all these multiple nodes agre ...
Transactions
... E.g. Oracle and PostgreSQL by default support a level of consistency called snapshot isolation (not part of the SQL standard) ...
... E.g. Oracle and PostgreSQL by default support a level of consistency called snapshot isolation (not part of the SQL standard) ...
The object-oriented database and processing of electronic warfare data Lee, J. J.
... • DOD representatives have requested our database reengineering research with object-oriented methodology and technology on the EWIR data. In conducting this research, the following goals are achieved: • Determine whether the object-oriented EWIR database is more effective, efficient, and intuitive ...
... • DOD representatives have requested our database reengineering research with object-oriented methodology and technology on the EWIR data. In conducting this research, the following goals are achieved: • Determine whether the object-oriented EWIR database is more effective, efficient, and intuitive ...
chapter 7_ database administration
... Because part number BV06 already exists in the PART table, the system must reject this attempt. Because this part is not in item class HW (and therefore is not in the HOUSEWARES view), this rejection certainly will seem strange to the user, because there is no such part in the user’s view. On the ot ...
... Because part number BV06 already exists in the PART table, the system must reject this attempt. Because this part is not in item class HW (and therefore is not in the HOUSEWARES view), this rejection certainly will seem strange to the user, because there is no such part in the user’s view. On the ot ...
Document
... R could have been generated when converting E-R diagram to a set of tables. R could have been a single relation containing all attributes that are of interest (called universal relation). R could have been the result of some ad hoc design of relations, which we then test/convert to normal form ...
... R could have been generated when converting E-R diagram to a set of tables. R could have been a single relation containing all attributes that are of interest (called universal relation). R could have been the result of some ad hoc design of relations, which we then test/convert to normal form ...
Temporal data, temporal data models, temporal data languages and
... systems are time-constrained and temporally constituted. Solutions in temporal database systems can contribute to the design of real-time military applications using temporal databc ...
... systems are time-constrained and temporally constituted. Solutions in temporal database systems can contribute to the design of real-time military applications using temporal databc ...
Keyword-based Search in a Relational Database
... 3.5 Retrieving occurrences of keywords from the indices given the query Jan Cornelis Nantes 1744……………….…………….........8 3.6 Intersecting vertices for the query IJsbrand Hanning Riga 1744……………………..………………………………….…………………….….. 10 5.7 System-generated SQL queries and their answers………………………………………………………………… ...
... 3.5 Retrieving occurrences of keywords from the indices given the query Jan Cornelis Nantes 1744……………….…………….........8 3.6 Intersecting vertices for the query IJsbrand Hanning Riga 1744……………………..………………………………….…………………….….. 10 5.7 System-generated SQL queries and their answers………………………………………………………………… ...
Preparing for and Tuning the SQL Query Engine on DB2 for i5/OS
... as completely as possible, the examples include the names of individuals, companies, brands, and products. All of these names are fictitious and any similarity to the names and addresses used by an actual business enterprise is entirely coincidental. COPYRIGHT LICENSE: This information contains samp ...
... as completely as possible, the examples include the names of individuals, companies, brands, and products. All of these names are fictitious and any similarity to the names and addresses used by an actual business enterprise is entirely coincidental. COPYRIGHT LICENSE: This information contains samp ...
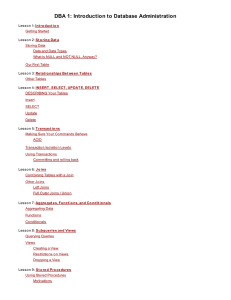
DBA 1: Introduction to Database Administration
... experimentatio n. If yo u do break so mething, that's an indicatio n to us that we need to impro ve o ur system! T ake yo ur t im e . Learning takes time. Rushing can have negative effects o n yo ur pro gress. Slo w do wn and let yo ur brain abso rb the new info rmatio n tho ro ughly. Taking yo ur t ...
... experimentatio n. If yo u do break so mething, that's an indicatio n to us that we need to impro ve o ur system! T ake yo ur t im e . Learning takes time. Rushing can have negative effects o n yo ur pro gress. Slo w do wn and let yo ur brain abso rb the new info rmatio n tho ro ughly. Taking yo ur t ...
Chapter 9
... application, the application prompts for a username and associated password. Oracle then authenticates the connection request using the user account information managed by the database. Password authentication is common in distributed processing environments when users work with client PCs and conne ...
... application, the application prompts for a username and associated password. Oracle then authenticates the connection request using the user account information managed by the database. Password authentication is common in distributed processing environments when users work with client PCs and conne ...