Nominet template
... Oracle think initially think this ORA-600 error was hardware related – There are NO indications of any hardware fault - the primary keeps running ...
... Oracle think initially think this ORA-600 error was hardware related – There are NO indications of any hardware fault - the primary keeps running ...
Database Notes (full version) - The ELCHK Yuen Long Lutheran
... Many databases designed to run on personal computers are expected to be used by one user at a time. We usually referred them as single-user databases. Earlier versions of Microsoft FoxPro and Access belong to such a type. More sophisticated databases like MySQL, Microsoft SQL Server, IBM DB2 and Ora ...
... Many databases designed to run on personal computers are expected to be used by one user at a time. We usually referred them as single-user databases. Earlier versions of Microsoft FoxPro and Access belong to such a type. More sophisticated databases like MySQL, Microsoft SQL Server, IBM DB2 and Ora ...
... provided by IBM under terms of the IBM Customer Agreement, IBM International Program License Agreement or any equivalent agreement between us. Any performance data contained herein was determined in a controlled environment. Therefore, the results obtained in other operating environments may vary si ...
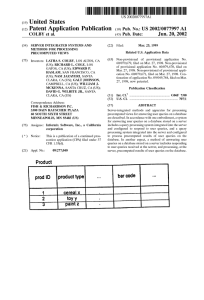
Server integrated systems and methods for processing precomputed
... is typically done by specifying one or more predicates that are used to ?lter a table to identify roWs for Which the ...
... is typically done by specifying one or more predicates that are used to ?lter a table to identify roWs for Which the ...
EMC VSPEX FOR VIRTUALIZED MICROSOFT SQL SERVER 2012 WITH VMWARE VSPHERE
... EMC® VSPEX® Proven Infrastructure is optimized for virtualizing business-critical applications. VSPEX gives partners the ability to design and implement the virtual resources necessary to satisfy the requirements for deploying Microsoft SQL Server on any VSPEX Private Cloud. EMC VSPEX for virtualize ...
... EMC® VSPEX® Proven Infrastructure is optimized for virtualizing business-critical applications. VSPEX gives partners the ability to design and implement the virtual resources necessary to satisfy the requirements for deploying Microsoft SQL Server on any VSPEX Private Cloud. EMC VSPEX for virtualize ...
Chapter 5: Other Relational Languages
... bank, but do not have a loan from the bank. range of t is depositor range of u is borrower retrieve unique (t.customer-name) where any (u.loan-number by t.customer-name where u.customer-name = t.customer-name) = 0 The use of a comparison with any is analogous to the “there ...
... bank, but do not have a loan from the bank. range of t is depositor range of u is borrower retrieve unique (t.customer-name) where any (u.loan-number by t.customer-name where u.customer-name = t.customer-name) = 0 The use of a comparison with any is analogous to the “there ...
(A) R
... R could have been generated when converting E-R diagram to a set of tables. R could have been a single relation containing all attributes that are of interest (called universal relation). Normalization breaks R into smaller relations. ...
... R could have been generated when converting E-R diagram to a set of tables. R could have been a single relation containing all attributes that are of interest (called universal relation). Normalization breaks R into smaller relations. ...
The State of the Art in Distributed Query Processing
... distributed system changes rapidly because the load of sites varies over time and new sites are added to the system; (3) legacy systems need to be integrated—such legacy systems usually have not been designed for distributed data processing and now need to interact with other (modern) systems in a d ...
... distributed system changes rapidly because the load of sites varies over time and new sites are added to the system; (3) legacy systems need to be integrated—such legacy systems usually have not been designed for distributed data processing and now need to interact with other (modern) systems in a d ...
... 6 Getting started with DB2 application development The licensed program described in this document and all licensed material available for it are provided by IBM under terms of the IBM Customer Agreement, IBM International Program License Agreement or any equivalent agreement between us. Any perfor ...
Oracle to DB2 Migration Comparison White Paper
... MAPPING OF ORACLE AND DB2 UDB TERMINOLOGY............................................................................... 18 DATA TYPES............................................................................................................................................. 19 MAPPING ORACLE DATA T ...
... MAPPING OF ORACLE AND DB2 UDB TERMINOLOGY............................................................................... 18 DATA TYPES............................................................................................................................................. 19 MAPPING ORACLE DATA T ...
r – s
... Example: {customer-name} is a candidate key for Customer, since it is a superkey (assuming no two customers can possibly have the same name), and no subset of it is a superkey. ...
... Example: {customer-name} is a candidate key for Customer, since it is a superkey (assuming no two customers can possibly have the same name), and no subset of it is a superkey. ...
CS 46B: Introduction to Data Structures
... Databases Illuminated, 3rd ed. by Ricardo & Urban Jones & Bartlett Learning, 2017 ISBN 978-1-284-05694-5 ...
... Databases Illuminated, 3rd ed. by Ricardo & Urban Jones & Bartlett Learning, 2017 ISBN 978-1-284-05694-5 ...
DATABASE DEPENDENCIES
... (in each application, new variables are substituted for existential variables); in the case of an equality-generating dependency, variables are equated until the dependency is satisfied. The result, chase(C), which may be infinite, can be seen as a model for C. It is the case that C |= c if and only ...
... (in each application, new variables are substituted for existential variables); in the case of an equality-generating dependency, variables are equated until the dependency is satisfied. The result, chase(C), which may be infinite, can be seen as a model for C. It is the case that C |= c if and only ...
Practical Wide-Area Database Replication
... while assuring global system consistency. The problem is magnified for wide area replication due to the high latency and the increased likelihood of network partitions in wide area settings. In this paper, we explore a novel replication architecture and system for local and wide area networks. We in ...
... while assuring global system consistency. The problem is magnified for wide area replication due to the high latency and the increased likelihood of network partitions in wide area settings. In this paper, we explore a novel replication architecture and system for local and wide area networks. We in ...
A Conceptual Model and Predicate Language for Data Selection
... provenance information (e.g., "What is the provenance of this tuple?"). However, anecdotal evidence from several domains tells us that users often want to select data based on its provenance and either use it immediately (for example in reports), or further analyze it and combine it with other data. ...
... provenance information (e.g., "What is the provenance of this tuple?"). However, anecdotal evidence from several domains tells us that users often want to select data based on its provenance and either use it immediately (for example in reports), or further analyze it and combine it with other data. ...
L - Fuzzy Structured Query Language
... than even the spreadsheet softwares [18]. Structured Query Language (SQL), which is the standard language used to interact with RDBMS, is one of the fountainheads of the success, and predominate for relational databases in the commercial world of database systems. RDBMS and SQL are based on crisp co ...
... than even the spreadsheet softwares [18]. Structured Query Language (SQL), which is the standard language used to interact with RDBMS, is one of the fountainheads of the success, and predominate for relational databases in the commercial world of database systems. RDBMS and SQL are based on crisp co ...
Normalization-Anomalies
... A table is in first normal form (1NF) if and only if it faithfully represents a relation.[3] Given that database tables embody a relationlike form, the defining characteristic of one in first normal form is that it does not allow duplicate rows or nulls. Simply put, a table with a unique key (which ...
... A table is in first normal form (1NF) if and only if it faithfully represents a relation.[3] Given that database tables embody a relationlike form, the defining characteristic of one in first normal form is that it does not allow duplicate rows or nulls. Simply put, a table with a unique key (which ...
Whois queries in RIPE database v3.0
... in the form of inetnum and route objects, among others. Both inetnum and route objects store information about ranges of IP addresses. Route objects use prefix notation to specify the range of IP addresses that they contain information about. This type of notation specifies ranges using two componen ...
... in the form of inetnum and route objects, among others. Both inetnum and route objects store information about ranges of IP addresses. Route objects use prefix notation to specify the range of IP addresses that they contain information about. This type of notation specifies ranges using two componen ...
Oracle: HTMLDB - Northern California Oracle Users Group
... objects such as tables and procedures. Each application is a collection of pages linked together using tabs, buttons, or hypertext links. A page is the basic building block of an application. Each page contains user interface elements, such as ...
... objects such as tables and procedures. Each application is a collection of pages linked together using tabs, buttons, or hypertext links. A page is the basic building block of an application. Each page contains user interface elements, such as ...
Chapter 17: Parallel Databases
... join algorithm on the local partitions ri and s of r and s to produce a partition of the final result of the hash-join. Note: Hash-join optimizations can be applied to the parallel case ...
... join algorithm on the local partitions ri and s of r and s to produce a partition of the final result of the hash-join. Note: Hash-join optimizations can be applied to the parallel case ...
Second Normal Form - Department of Computer Science
... PDT is a superkey, and FD is a superkey. Is PDT a candidate key? PD is not a superkey, nor is DT, nor is PT. So, PDT is a candidate key. FD is also a candidate key, since neither F or D ...
... PDT is a superkey, and FD is a superkey. Is PDT a candidate key? PD is not a superkey, nor is DT, nor is PT. So, PDT is a candidate key. FD is also a candidate key, since neither F or D ...