Database Replication – an Overview of Replication Techniques in Patrik Rantanen
... This thesis was requested by the HAAGA-HELIA thesis group on databases and the DBTech EXT project for a workshop where one of the topics is database replication. Its purpose was to test and document database replication techniques in most common database systems. The thesis was done in two parts. Th ...
... This thesis was requested by the HAAGA-HELIA thesis group on databases and the DBTech EXT project for a workshop where one of the topics is database replication. Its purpose was to test and document database replication techniques in most common database systems. The thesis was done in two parts. Th ...
Enterprise eTIME Database Administrator`s Guide
... All other trademarks or registered trademarks used herein are the property of their respective owners and are used for identification purposes only. When using and applying the information generated by ADP products, customers should ensure that they comply with the applicable requirements of federal ...
... All other trademarks or registered trademarks used herein are the property of their respective owners and are used for identification purposes only. When using and applying the information generated by ADP products, customers should ensure that they comply with the applicable requirements of federal ...
Chapter 7: Relational Database Design
... tuples that could be useful for a later operation. Generating the result of r1 r2 r3 sorted on the attributes common with r4 or r5 may be useful, but generating it sorted on the attributes common only r1 and r2 is not useful. Using merge-join to compute r1 r2 r3 may be costlier, but may provide ...
... tuples that could be useful for a later operation. Generating the result of r1 r2 r3 sorted on the attributes common with r4 or r5 may be useful, but generating it sorted on the attributes common only r1 and r2 is not useful. Using merge-join to compute r1 r2 r3 may be costlier, but may provide ...
DataBlade Module Installation and Registration Guide Version 4.0
... This manual describes Version 4.0 of BladeManager. BladeManager requires Informix Dynamic Server and the Informix Client Software Developer’s Kit. See the BladeManager Read Me First sheet for version compatibility and system requirements. BladeManager is available as both a graphical user interface ...
... This manual describes Version 4.0 of BladeManager. BladeManager requires Informix Dynamic Server and the Informix Client Software Developer’s Kit. See the BladeManager Read Me First sheet for version compatibility and system requirements. BladeManager is available as both a graphical user interface ...
DESERVE: A FRAMEWORK FOR DETECTING PROGRAM SECURITY VULNERABILITY EXPLOITATIONS
... exploitable ones. Dynamic taint analysis marks a user input and tracks it at run time. It is ...
... exploitable ones. Dynamic taint analysis marks a user input and tracks it at run time. It is ...
Chapter 3
... For binary many-to-one relationship sets, the primary key of the “many” entity set becomes the relation’s primary key. For one-to-one relationship sets, the relation’s primary key can be that of either entity set. ...
... For binary many-to-one relationship sets, the primary key of the “many” entity set becomes the relation’s primary key. For one-to-one relationship sets, the relation’s primary key can be that of either entity set. ...
The Complete Placement Guide- 2nd edition
... C++ Interview Questions ............................................................................................................................................5 C++ Object-Oriented Interview Questions And Answers .................................................................................. ...
... C++ Interview Questions ............................................................................................................................................5 C++ Object-Oriented Interview Questions And Answers .................................................................................. ...
Implementing Oracle9i Data Guard
... Recover Standby Database (Pri,Sec) ....................................................................................................................................................... 29 Enable Data Guard Broker (Pri+Sec) ........................................................................... ...
... Recover Standby Database (Pri,Sec) ....................................................................................................................................................... 29 Enable Data Guard Broker (Pri+Sec) ........................................................................... ...
db2 sql procedural unix, and windows
... creation of a new third-generation (3GL) programming language. The language was based on the existing SQL syntax and used a simple structured programming language very similar to early BASIC™. This new language allowed programmers to quickly develop and build stored procedures without having to know ...
... creation of a new third-generation (3GL) programming language. The language was based on the existing SQL syntax and used a simple structured programming language very similar to early BASIC™. This new language allowed programmers to quickly develop and build stored procedures without having to know ...
Chapter 2: Relational Model - Internet Database Lab.
... While Chapter 3 provides a basic introduction to SQL, Chapter 4 describes more advanced features of SQL, including how to interface between a programming language and a database supporting SQL. ...
... While Chapter 3 provides a basic introduction to SQL, Chapter 4 describes more advanced features of SQL, including how to interface between a programming language and a database supporting SQL. ...
Derby Tools and Utilities Guide Version 10.13 Derby Document build:
... to cause the direction or management of such entity, whether by contract or otherwise, or (ii) ownership of fifty percent (50%) or more of the outstanding shares, or (iii) beneficial ownership of such entity. "You" (or "Your") shall mean an individual or Legal Entity exercising permissions granted b ...
... to cause the direction or management of such entity, whether by contract or otherwise, or (ii) ownership of fifty percent (50%) or more of the outstanding shares, or (iii) beneficial ownership of such entity. "You" (or "Your") shall mean an individual or Legal Entity exercising permissions granted b ...
Using Databases – OpenOffice.org Base
... One record of the first table can be linked with several records in the list of this band’s albums. Such a relationship is called “one-to-many” and denoted by 1 – n. Databases also use a “one-to-one” relationship, which means that a table record can be linked with only a single field in another tabl ...
... One record of the first table can be linked with several records in the list of this band’s albums. Such a relationship is called “one-to-many” and denoted by 1 – n. Databases also use a “one-to-one” relationship, which means that a table record can be linked with only a single field in another tabl ...
Querying XML Database Using Relational Database System
... Combine information from multiple sources to create one unifies ...
... Combine information from multiple sources to create one unifies ...
(A) R
... We can show that if none of the dependencies in F causes a violation of BCNF, then none of the dependencies in F+ will cause a violation of BCNF ...
... We can show that if none of the dependencies in F causes a violation of BCNF, then none of the dependencies in F+ will cause a violation of BCNF ...
About Log Shipping (SQL Server) | Microsoft Docs
... The warm standby copy of the primary database. The secondary database may be in either the RECOVERING state or the STANDBY state, which leaves the database available for limited read-only access. monitor server An optional instance of SQL Server that tracks all of the details of log shipping, includ ...
... The warm standby copy of the primary database. The secondary database may be in either the RECOVERING state or the STANDBY state, which leaves the database available for limited read-only access. monitor server An optional instance of SQL Server that tracks all of the details of log shipping, includ ...
FREE Sample Here - We can offer most test bank and
... 2. As a general rule, database developers should use a personal database only for applications that are not mission critical. What are some of the reasons for this? ANS: In a personal database system, when a client workstation requests a data file, data within the file is locked and unavailable to o ...
... 2. As a general rule, database developers should use a personal database only for applications that are not mission critical. What are some of the reasons for this? ANS: In a personal database system, when a client workstation requests a data file, data within the file is locked and unavailable to o ...
Joins for Hybrid Warehouses: Exploiting Massive Parallelism in Hadoop and Enterprise Data Warehouses.
... stored in HDFS. Federation [21, 2, 34, 40, 30] is a solution to integrate data stored in autonomous databases, while exploiting the query processing power of all systems involved. However, existing federation solutions use a client-server model to access the remote databases and move the data. In pa ...
... stored in HDFS. Federation [21, 2, 34, 40, 30] is a solution to integrate data stored in autonomous databases, while exploiting the query processing power of all systems involved. However, existing federation solutions use a client-server model to access the remote databases and move the data. In pa ...
A Generic Provenance Middleware for Database Queries, Updates
... GProm is the first system capable of computing provenance for queries, update operations, transactions, and across transaction boundaries. Provenance computation for updates and transactions is implemented in the transaction reenactment module of the system. We can retroactively compute the provenan ...
... GProm is the first system capable of computing provenance for queries, update operations, transactions, and across transaction boundaries. Provenance computation for updates and transactions is implemented in the transaction reenactment module of the system. We can retroactively compute the provenan ...
Database Tuning Principles
... aggregates well, so they are taking over the data warehouse market from some of the specialized vendors. Further, they have extended their transactional models to support ecommerce. Because relational systems are such an important part of the database world, this book concentrates on the major ones: ...
... aggregates well, so they are taking over the data warehouse market from some of the specialized vendors. Further, they have extended their transactional models to support ecommerce. Because relational systems are such an important part of the database world, this book concentrates on the major ones: ...
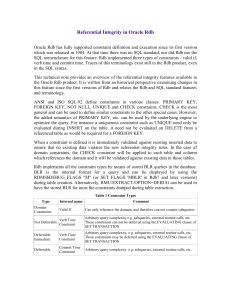
Referential Integrity in Oracle Rdb
... SQL nomenclature for this feature. Rdb implemented three types of constraints - valid if, verb time and commit time. Traces of this terminology exist still in the Rdb product, even in the SQL syntax. This technical note provides an overview of the referential integrity features available in the Orac ...
... SQL nomenclature for this feature. Rdb implemented three types of constraints - valid if, verb time and commit time. Traces of this terminology exist still in the Rdb product, even in the SQL syntax. This technical note provides an overview of the referential integrity features available in the Orac ...
Document
... Whether you remove duplicate rows from result or not, it is up to you since relations are sets, and could have contained duplicate rows themselves E.g. To eliminate the branch-name attribute of account ...
... Whether you remove duplicate rows from result or not, it is up to you since relations are sets, and could have contained duplicate rows themselves E.g. To eliminate the branch-name attribute of account ...
Identity Manager 4.0.2 Driver for JDBC Implementation Guide
... Novell, Inc. makes no representations or warranties with respect to the contents or use of this documentation, and specifically disclaims any express or implied warranties of merchantability or fitness for any particular purpose. Further, Novell, Inc. reserves the right to revise this publication an ...
... Novell, Inc. makes no representations or warranties with respect to the contents or use of this documentation, and specifically disclaims any express or implied warranties of merchantability or fitness for any particular purpose. Further, Novell, Inc. reserves the right to revise this publication an ...