Sybase IQ
... This publication pertains to Sybase software and to any subsequent release until otherwise indicated in new editions or technical notes. Information in this document is subject to change without notice. The software described herein is furnished under a license agreement, and it may be used or copie ...
... This publication pertains to Sybase software and to any subsequent release until otherwise indicated in new editions or technical notes. Information in this document is subject to change without notice. The software described herein is furnished under a license agreement, and it may be used or copie ...
SQLBase SQL Language Reference
... trademarks of Centura Software Corporation and may be registered in the United States of America and/or other countries. SQLWindows is a registered trademark and TeamWindows, ReportWindows and EditWindows are trademarks exclusively used and licensed by Centura Software Corporation. Microsoft, Win32, ...
... trademarks of Centura Software Corporation and may be registered in the United States of America and/or other countries. SQLWindows is a registered trademark and TeamWindows, ReportWindows and EditWindows are trademarks exclusively used and licensed by Centura Software Corporation. Microsoft, Win32, ...
CONSTRAINT-BASED GENERATION OF
... fault-based software testing technique that is intensively studied for evaluating the adequacy of tests [19]. The original program under test is mutated into a set of new programs, called mutants, caused by syntactic changes following a set of rules. The mutants are (strongly) killed if running the ...
... fault-based software testing technique that is intensively studied for evaluating the adequacy of tests [19]. The original program under test is mutated into a set of new programs, called mutants, caused by syntactic changes following a set of rules. The mutants are (strongly) killed if running the ...
Using Explicit Cursors
... The Oracle server uses work areas (called private SQL areas) to execute SQL statements and to store processing information. You can use explicit cursors to name a private SQL area and to access its stored information. Cursor Type ...
... The Oracle server uses work areas (called private SQL areas) to execute SQL statements and to store processing information. You can use explicit cursors to name a private SQL area and to access its stored information. Cursor Type ...
Implementing Secure Transactions With PHP and MySQL Wen An Bachelor’s thesis
... programming language, PHP is a program embedded into HTML document to execute, the efficiency of the execution is much higher than completely genereting HTML marked CGI, PHP can also perform compiled code,code can achieve encryption and optimize the operation of code, making the code running faster. ...
... programming language, PHP is a program embedded into HTML document to execute, the efficiency of the execution is much higher than completely genereting HTML marked CGI, PHP can also perform compiled code,code can achieve encryption and optimize the operation of code, making the code running faster. ...
Data Sheet: Oracle Exadata Database Machine X6-2
... keeping infrequently accessed data on disk. This provides the performance of flash with the capacity and low cost of disk. The Exadata Smart Flash Cache uniquely understands database workloads and knows when to avoid caching data that the database will rarely access or is too big to fit in the cache ...
... keeping infrequently accessed data on disk. This provides the performance of flash with the capacity and low cost of disk. The Exadata Smart Flash Cache uniquely understands database workloads and knows when to avoid caching data that the database will rarely access or is too big to fit in the cache ...
Brio Intelligence Administrator`s Guide
... The Brio Intelligence Administrator’s Guide is written for Explorer and Designer users who have access to more advanced features and who may have responsibility for implementing the Brio Intelligence application in an enterprise environment. ...
... The Brio Intelligence Administrator’s Guide is written for Explorer and Designer users who have access to more advanced features and who may have responsibility for implementing the Brio Intelligence application in an enterprise environment. ...
HyperSQL User Guide - HyperSQL Database Engine 2.4.0
... Copyright 2002-2017 Blaine Simpson, Fred Toussi and The HSQL Development Group. Permission is granted to distribute this document without any alteration under the terms of the HSQLDB license. You are not allowed to distribute or display this document on the web in an altered form. ...
... Copyright 2002-2017 Blaine Simpson, Fred Toussi and The HSQL Development Group. Permission is granted to distribute this document without any alteration under the terms of the HSQLDB license. You are not allowed to distribute or display this document on the web in an altered form. ...
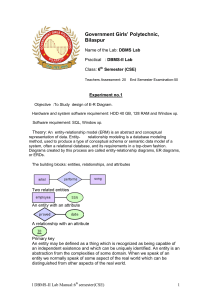
l DBMS-II Lab Manual
... method, used to produce a type of conceptual schema or semantic data model of a system, often a relational database, and its requirements in a top-down fashion. Diagrams created by this process are called entity-relationship diagrams, ER diagrams, or ERDs. The building blocks: entities, relationship ...
... method, used to produce a type of conceptual schema or semantic data model of a system, often a relational database, and its requirements in a top-down fashion. Diagrams created by this process are called entity-relationship diagrams, ER diagrams, or ERDs. The building blocks: entities, relationship ...
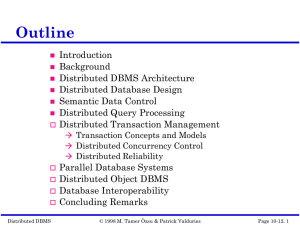
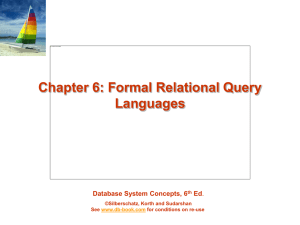
ppt - FCN
... 1. r, s must have the same arity (same number of attributes) 2. The attribute domains must be compatible (example: 2nd column of r deals with the same type of values as does the 2nd column of s) Example: to find all courses taught in the Fall 2009 semester, or in the ...
... 1. r, s must have the same arity (same number of attributes) 2. The attribute domains must be compatible (example: 2nd column of r deals with the same type of values as does the 2nd column of s) Example: to find all courses taught in the Fall 2009 semester, or in the ...
comlab.ox.ac.uk - Department of Computer Science, Oxford
... The main contributions of this paper are as follows: • We define a data safe query plan, which is a query plan P that can be evaluated using extensional semantics on a database instance D; in contrast, the standard definition of a safe plan is one where the extensional semantics is correct on any in ...
... The main contributions of this paper are as follows: • We define a data safe query plan, which is a query plan P that can be evaluated using extensional semantics on a database instance D; in contrast, the standard definition of a safe plan is one where the extensional semantics is correct on any in ...
CPS Backup and Restore Guide
... topology diagrams, and other figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses or phone numbers in illustrative content is unintentional and coincidental. Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affi ...
... topology diagrams, and other figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses or phone numbers in illustrative content is unintentional and coincidental. Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affi ...
Oracle Database 2 Day + Data Warehousing Guide
... on behalf of the U.S. Government, the following notice is applicable: U.S. GOVERNMENT RIGHTS Programs, software, databases, and related documentation and technical data delivered to U.S. Government customers are "commercial computer software" or "commercial technical data" pursuant to the applicable ...
... on behalf of the U.S. Government, the following notice is applicable: U.S. GOVERNMENT RIGHTS Programs, software, databases, and related documentation and technical data delivered to U.S. Government customers are "commercial computer software" or "commercial technical data" pursuant to the applicable ...
Transparent Data Encryption Best Practices
... In TDE column encryption, both the master key and table keys can be individually re-keyed, providing for a granular implementation of various security policies. Re-keying of the master key does not impact performance or availability of your application, because it requires only decryption and re-enc ...
... In TDE column encryption, both the master key and table keys can be individually re-keyed, providing for a granular implementation of various security policies. Re-keying of the master key does not impact performance or availability of your application, because it requires only decryption and re-enc ...
Videoscape Control Suite 3.5.0 Database User Guide
... A logical entity which is always associated with one or more physical data files. All base-level objects which consume space, such as a non-partitioned table or index, reside in one, and one only, tablespace. The data of such a base-level object can reside in multiple datafiles, all of which must be ...
... A logical entity which is always associated with one or more physical data files. All base-level objects which consume space, such as a non-partitioned table or index, reside in one, and one only, tablespace. The data of such a base-level object can reside in multiple datafiles, all of which must be ...
PDF - Microsoft Docs
... Easier package management for data scientists You no longer have to rely on the database administrator to install the R packages you need on SQL Server. New package install and uninstall functions in RevoScaleR let you easily install and update packages in R Services from a client computer. For the ...
... Easier package management for data scientists You no longer have to rely on the database administrator to install the R packages you need on SQL Server. New package install and uninstall functions in RevoScaleR let you easily install and update packages in R Services from a client computer. For the ...
Document
... 2. Information about the updates carried out by the transaction and written to disk is sufficient to enable the database to reconstruct the updates when the database system is restarted after the failure. Ensuring durability is the responsibility of a component of the database system called the reco ...
... 2. Information about the updates carried out by the transaction and written to disk is sufficient to enable the database to reconstruct the updates when the database system is restarted after the failure. Ensuring durability is the responsibility of a component of the database system called the reco ...
Blue Stack - Setting up DB2 Guideline Product(s): IBM Cognos 8
... an IBM Company. While every attempt has been made to ensure that the information in this document is accurate and complete, some typographical errors or technical inaccuracies may exist. Cognos does not accept responsibility for any kind of loss resulting from the use of information contained in thi ...
... an IBM Company. While every attempt has been made to ensure that the information in this document is accurate and complete, some typographical errors or technical inaccuracies may exist. Cognos does not accept responsibility for any kind of loss resulting from the use of information contained in thi ...
"Installing Museum, Library and Archive A5"
... Writing from right to left With the Unified version of adlwin and adloan (these are the most relevant core software executables), from 5.0.2 it is possible to mirror screens and menus in Adlib applications and to enter text from right to left automatically in the entry fields. This is necessary for ...
... Writing from right to left With the Unified version of adlwin and adloan (these are the most relevant core software executables), from 5.0.2 it is possible to mirror screens and menus in Adlib applications and to enter text from right to left automatically in the entry fields. This is necessary for ...
Corporate PPT Template
... since SQL.” “ASM alone makes 10g worth while.” “Storage has become a commodity, I only need to present it to 10g and ASM does the rest.” Laurence Grant, Dir. of Enterprise Computing Systems ...
... since SQL.” “ASM alone makes 10g worth while.” “Storage has become a commodity, I only need to present it to 10g and ASM does the rest.” Laurence Grant, Dir. of Enterprise Computing Systems ...