Content-peering Dynamics of Autonomous Caches in a
... contents, which in principle should enable them to decrease their Recent proposals to re-design the Internet with the aim of transit traffic costs. The interaction between the caches could, facilitating content delivery share the common characteristic that however, lead to unforeseen instability and ...
... contents, which in principle should enable them to decrease their Recent proposals to re-design the Internet with the aim of transit traffic costs. The interaction between the caches could, facilitating content delivery share the common characteristic that however, lead to unforeseen instability and ...
Tier-1 ISP - Universidad Carlos III de Madrid
... Networking: A Top Down Approach” generously made available by their authors (see copyright below). The slides have been adapted, where required, to the teaching needs of the subject above. ...
... Networking: A Top Down Approach” generously made available by their authors (see copyright below). The slides have been adapted, where required, to the teaching needs of the subject above. ...
Network Hacking: Exploits, Intrusions and Defenses
... Bellovin writes on it, also notes that Berkley’s r-utils (rsh etc.) depend on domain name from rDNS tree. Does not publish. ...
... Bellovin writes on it, also notes that Berkley’s r-utils (rsh etc.) depend on domain name from rDNS tree. Does not publish. ...
Firewall - Gadjah Mada University
... • People don’t just put up a thick front door for their sensitive belongings, you shouldn’t for your network either. • Firewalls are an effective start to securing a network. Not a finish. • Care must be taken to construct an appropriate set of rules that will enforce ...
... • People don’t just put up a thick front door for their sensitive belongings, you shouldn’t for your network either. • Firewalls are an effective start to securing a network. Not a finish. • Care must be taken to construct an appropriate set of rules that will enforce ...
The Great Firewall of China
... the filtering itself can be when directed at an advanced target such as the Tor anonymity network. The GFC is only a small part of the legal, regulatory, and technical mechanisms China has put in place for Internet censorship [6], but it is an important part because it helps to separate China’s Inte ...
... the filtering itself can be when directed at an advanced target such as the Tor anonymity network. The GFC is only a small part of the legal, regulatory, and technical mechanisms China has put in place for Internet censorship [6], but it is an important part because it helps to separate China’s Inte ...
peering - Workshops
... operation and troubleshooting The dominant topology used in the Internet today ...
... operation and troubleshooting The dominant topology used in the Internet today ...
Anderson
... Or if AS5 wants to swap its primary/backup provider from 4 -‐> 1, or 1-‐>4, a loop is formed ...
... Or if AS5 wants to swap its primary/backup provider from 4 -‐> 1, or 1-‐>4, a loop is formed ...
Kohsuke Kawaguchi's ppaper, "Economic Viability of the Internet"
... postal mail, I need to pay maybe 50 cents per a mail. These are understandable, as the person who receives a service (that is, me) is paying the cost, and that’s how our society works. However, surprisingly, sending e-mail costs me nothing. To be precise, I need to pay around $40 to ISP per month, b ...
... postal mail, I need to pay maybe 50 cents per a mail. These are understandable, as the person who receives a service (that is, me) is paying the cost, and that’s how our society works. However, surprisingly, sending e-mail costs me nothing. To be precise, I need to pay around $40 to ISP per month, b ...
ppt - Computer Science Division - University of California, Berkeley
... Need to create public Internet service providers - Back to the future..... ...
... Need to create public Internet service providers - Back to the future..... ...
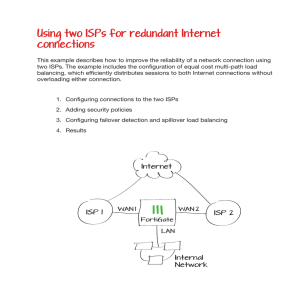
Using two ISPs for redundant Internet connections
... This example describes how to improve the reliability of a network connection using two ISPs. The example includes the configuration of equal cost multi-path load balancing, which efficiently distributes sessions to both Internet connections without overloading either connection. ...
... This example describes how to improve the reliability of a network connection using two ISPs. The example includes the configuration of equal cost multi-path load balancing, which efficiently distributes sessions to both Internet connections without overloading either connection. ...
L02 - Bad Request
... • Pakistan using IP-based blocking for YouTube address ranges • Can interfere with other Google services • China • Some reports of IP blocking • Many URLs redirected to small set of IP-addresses, possibly this is the set used for ACLs • UK • Uses IP blocking of the Pirate Bay’s IP address • Australi ...
... • Pakistan using IP-based blocking for YouTube address ranges • Can interfere with other Google services • China • Some reports of IP blocking • Many URLs redirected to small set of IP-addresses, possibly this is the set used for ACLs • UK • Uses IP blocking of the Pirate Bay’s IP address • Australi ...