Cloud Computing Tutorial Christophe Poulain Yogesh Simmhan Bora Beran
... © 2008 Microsoft Corporation. All rights reserved. Microsoft, Windows, Windows Vista and other product names are or may be registered trademarks and/or trademarks in the U.S. and/or other countries. The information herein is for informational purposes only and represents the current view of Microso ...
... © 2008 Microsoft Corporation. All rights reserved. Microsoft, Windows, Windows Vista and other product names are or may be registered trademarks and/or trademarks in the U.S. and/or other countries. The information herein is for informational purposes only and represents the current view of Microso ...
nAos - AB-CO Front-end
... The nAos needs to be re-written using standard components; The vscope application is now unmaintainable; We can share hardware and software with other groups (SiWG); nAos can be more than just curve visualisation (Contract ?) We need another way to trigger the scopes; ...
... The nAos needs to be re-written using standard components; The vscope application is now unmaintainable; We can share hardware and software with other groups (SiWG); nAos can be more than just curve visualisation (Contract ?) We need another way to trigger the scopes; ...
System development with Java
... DataReader vs. DataSet Examples • The DataSet's disconnected nature allows it to be transformed into XML and sent over the wire via HTTP if appropriate. • A connected DataReader cannot be serialized and thus cannot be passed between physical-tier boundaries where only string (XML) data can go. • A ...
... DataReader vs. DataSet Examples • The DataSet's disconnected nature allows it to be transformed into XML and sent over the wire via HTTP if appropriate. • A connected DataReader cannot be serialized and thus cannot be passed between physical-tier boundaries where only string (XML) data can go. • A ...
Nvarchar max
... the MAX as the length? May 07, 2013 Hi, whats the actual difference between varchar(max) and varchar(8000). Is the difference applies same for nvarchar(max) and nvarchar… If you use the default settings for NVARCHAR(MAX) then yes, your table will be larger, which can cause other performance problem ...
... the MAX as the length? May 07, 2013 Hi, whats the actual difference between varchar(max) and varchar(8000). Is the difference applies same for nvarchar(max) and nvarchar… If you use the default settings for NVARCHAR(MAX) then yes, your table will be larger, which can cause other performance problem ...
Databases 101 Matthew J. Graham CACR Methods of Computational Science
... as the file format properties Hollerith 1889 patent "Art of Compiling Statistics" describes how every US resident can be represented by a string of 80 characters and numbers Examples: delimited-separated data, HTML table matthew graham ...
... as the file format properties Hollerith 1889 patent "Art of Compiling Statistics" describes how every US resident can be represented by a string of 80 characters and numbers Examples: delimited-separated data, HTML table matthew graham ...
Entrez PubMed - cosmas
... thickness of the adsorbed layers and enthalpy of the adsorption were assessed. The close similarity in the conformation of the poly (ethylene oxide) (PEO) chains (molecular weight 5000 Da) in the adsorbed layers of these two copolymers was demonstrated by combining the adsorption data with the adsor ...
... thickness of the adsorbed layers and enthalpy of the adsorption were assessed. The close similarity in the conformation of the poly (ethylene oxide) (PEO) chains (molecular weight 5000 Da) in the adsorbed layers of these two copolymers was demonstrated by combining the adsorption data with the adsor ...
Lecture 29 - University of Virginia
... – Everything you can compute in Scheme you can compute in PHP – Everything you can compute in PHP, you can compute in Scheme – Friday we will explain why more convincingly ...
... – Everything you can compute in Scheme you can compute in PHP – Everything you can compute in PHP, you can compute in Scheme – Friday we will explain why more convincingly ...
The Ubiquitous DBMS - Database and Multimedia Lab, KAIST
... Advanced database applications require complex operations such as data mining that cannot be implemented by SQL. As ubiquitous devices are rapidly evolving, many advanced applications that have been used in servers will also be required of ubiquitous devices. Thus, a UDBMS should be able to support ...
... Advanced database applications require complex operations such as data mining that cannot be implemented by SQL. As ubiquitous devices are rapidly evolving, many advanced applications that have been used in servers will also be required of ubiquitous devices. Thus, a UDBMS should be able to support ...
Document
... base data that is summarized for a data warehouse. The ODS may also be used to audit the data warehouse to assure summarized and derived data is calculated properly. The ODS may further become the enterprise shared operational database, allowing operational systems that are being reengineered to use ...
... base data that is summarized for a data warehouse. The ODS may also be used to audit the data warehouse to assure summarized and derived data is calculated properly. The ODS may further become the enterprise shared operational database, allowing operational systems that are being reengineered to use ...
Mobule 1 - Intro to Database and File Structures
... Random access files consist of records that can be accessed in any sequence. This means the data is stored exactly as it appears in memory, thus saving processing time (because no translation is necessary) both in when the file is written and in when it is read. Random files are a better solution to ...
... Random access files consist of records that can be accessed in any sequence. This means the data is stored exactly as it appears in memory, thus saving processing time (because no translation is necessary) both in when the file is written and in when it is read. Random files are a better solution to ...
A Sample Event Consumer Program For Updating Netezza with DB2... Introduction This article introduces a sample program that retrieves DB2 changed...
... accumulating in the WebSphere MQ queue on site 2 while Q Apply is stopped but they will be picked up by Q Apply when it comes back up. ...
... accumulating in the WebSphere MQ queue on site 2 while Q Apply is stopped but they will be picked up by Q Apply when it comes back up. ...
UNCERTAINTY MANAGEMENT: KEEPING BATTLESPACE VISUALIZATION HONEST
... logistics movements, this prediction would provide commanders and staffs the ability to plan actions to take timely actions to reduce or eliminate the peak in the threat. However, if the enemy takes COA 2, an economy of force decision might be made to avoid the threat conditions along routes A and C ...
... logistics movements, this prediction would provide commanders and staffs the ability to plan actions to take timely actions to reduce or eliminate the peak in the threat. However, if the enemy takes COA 2, an economy of force decision might be made to avoid the threat conditions along routes A and C ...
TEchnology INTEGRATIONS AND THE GENERIC firegrid SYSTEM
... fire and its movement from the point of origin throughout the building. Furthermore, the use of Type 3 sensors in wireless sensor networks is potentially feasible. For example the open source TinyOS [10] operating system supports limited memory for the wireless sensors and also enables inter-node co ...
... fire and its movement from the point of origin throughout the building. Furthermore, the use of Type 3 sensors in wireless sensor networks is potentially feasible. For example the open source TinyOS [10] operating system supports limited memory for the wireless sensors and also enables inter-node co ...
Early Experience Prototyping a Science Data Server for
... by a researcher Server Sets are maintained on behalf of all researchers in the collaboration Accessible to all researchers Set change policy decisions determined by the server (administrator) on behalf of the collaboration Researcher Sets are maintained by a specific researcher or small subs ...
... by a researcher Server Sets are maintained on behalf of all researchers in the collaboration Accessible to all researchers Set change policy decisions determined by the server (administrator) on behalf of the collaboration Researcher Sets are maintained by a specific researcher or small subs ...
BACHELOR OF COMPUTER APPLICATIONS
... Note: Examiner will be required to set Nine Questions in all. First Question will be compulsory, consisting of objective type/short-answer type questions covering the entire syllabus. In addition to that eight more questions will be set, two questions from each Unit. A candidate will be required to ...
... Note: Examiner will be required to set Nine Questions in all. First Question will be compulsory, consisting of objective type/short-answer type questions covering the entire syllabus. In addition to that eight more questions will be set, two questions from each Unit. A candidate will be required to ...
No Slide Title - University of Connecticut
... RBAC vs. MAC vs. DAC Unique Characteristics of DCP Security Design with UML Role Slice Diagram + AOP/Enforcement Code Generation Model and Framework for Security in Distributed Setting Incorporation of RBAC, MAC, Constraints What is Role of Assurance in Security? Relationship to Othe ...
... RBAC vs. MAC vs. DAC Unique Characteristics of DCP Security Design with UML Role Slice Diagram + AOP/Enforcement Code Generation Model and Framework for Security in Distributed Setting Incorporation of RBAC, MAC, Constraints What is Role of Assurance in Security? Relationship to Othe ...
ATLAS DB Operations - Indico
... – CPU used – Cache hit ratio for the session setting the standard session audit is enough to extract them. 1. Overall machine/database behavior for I/O and CPU: – using the standard OS metrics collected by Oracle this can be easily obtained, might need some saving to tables periodically, as these ma ...
... – CPU used – Cache hit ratio for the session setting the standard session audit is enough to extract them. 1. Overall machine/database behavior for I/O and CPU: – using the standard OS metrics collected by Oracle this can be easily obtained, might need some saving to tables periodically, as these ma ...
Sample Interview Questions Senior Oracle DBA Interview Questions
... times, are willing to work with other people, and enjoy the job you do. Many times people see DBA types as stuffy and pointed, not willing to work with others, and only concerned with the database and its day-today operational needs. Put aside the needs of the database and talk about how you work wi ...
... times, are willing to work with other people, and enjoy the job you do. Many times people see DBA types as stuffy and pointed, not willing to work with others, and only concerned with the database and its day-today operational needs. Put aside the needs of the database and talk about how you work wi ...
Architectural Frameworks in Web Development
... architectural description. These languages needs to have a well-defined semantic and there also needs to be a collection of rules, properties and invariants to govern their use. The forming/constituting elements of an architectural description also have a description, as well as a definition on what ...
... architectural description. These languages needs to have a well-defined semantic and there also needs to be a collection of rules, properties and invariants to govern their use. The forming/constituting elements of an architectural description also have a description, as well as a definition on what ...
RIPE Database Operations Update
... • Provides easy way of mapping resources • May be linked to any object type, by “org:” attribute • Queries – Lookup by handle or name – Inverse queries – Referenced organisations are returned by default ...
... • Provides easy way of mapping resources • May be linked to any object type, by “org:” attribute • Queries – Lookup by handle or name – Inverse queries – Referenced organisations are returned by default ...
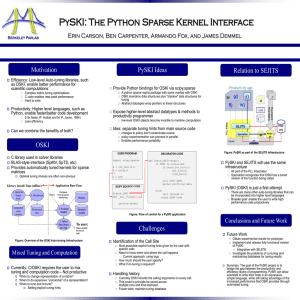
PySKI: The Python Sparse Kernel Interface Motivation PySKI Ideas Relation to SEJITS
... There are many other auto-tuning libraries that can be incorporated into higher level languages Broader goal: enable the user to write high performance code productively ...
... There are many other auto-tuning libraries that can be incorporated into higher level languages Broader goal: enable the user to write high performance code productively ...
Python and MySQL
... db.commit() #this is the CRUCIAL line that needs to be here to COMMIT the changes to the database db.close() #this closes the database to anymore changes The bits highlighted in blue are the ones you need to be aware of. The bits highlighted in yellow are my internal comments The other bits are fair ...
... db.commit() #this is the CRUCIAL line that needs to be here to COMMIT the changes to the database db.close() #this closes the database to anymore changes The bits highlighted in blue are the ones you need to be aware of. The bits highlighted in yellow are my internal comments The other bits are fair ...
Examples of GIS websites
... • grid of cells • cell size defines resolution • each cell has a unique reference that is used to attribute data ...
... • grid of cells • cell size defines resolution • each cell has a unique reference that is used to attribute data ...
On Efficient Part-match Querying of XML Data
... books,book,id; books,book,title and books,book,author. Points (0,1,2); (0,1,4) and (0,1,6) are created using idT of element and attribute names, idLP = 0, 1 and 2. For example, the path to value The Two Towers. The labelled path books,book,title with idLP 1 belongs. Vector (1,0,1,3,5) is created usi ...
... books,book,id; books,book,title and books,book,author. Points (0,1,2); (0,1,4) and (0,1,6) are created using idT of element and attribute names, idLP = 0, 1 and 2. For example, the path to value The Two Towers. The labelled path books,book,title with idLP 1 belongs. Vector (1,0,1,3,5) is created usi ...