Using SAS Software to Analyze Sybase Performance on the Web
... access point to the database. Common Gateway Interface (CGI) programming requires the definition of name=value pairs that are part of the interactive portion of web application. The name=value pairs in SAS are passed using the macro facility’s “call symput” function. In our web interface application ...
... access point to the database. Common Gateway Interface (CGI) programming requires the definition of name=value pairs that are part of the interactive portion of web application. The name=value pairs in SAS are passed using the macro facility’s “call symput” function. In our web interface application ...
Grid Portal System Based on GPIR - Digital Science Center
... We designed a Grid portal architecture based on GPIR, it has three layers[2]. The bottom layer is Information Providers, called resource layer; the middle layer is database, the top layer is client layer. The resource layer provides the resources, it is on the Grid environment. The resources of bott ...
... We designed a Grid portal architecture based on GPIR, it has three layers[2]. The bottom layer is Information Providers, called resource layer; the middle layer is database, the top layer is client layer. The resource layer provides the resources, it is on the Grid environment. The resources of bott ...
Secure Coding Practices
... separate through the use of placeholders. The query structure is defined with place holders and then the application specifies the contents of each placeholder. Utilize input validation and if validation fails, do not run the database command. Ensure that variables are strongly typed. Escape m ...
... separate through the use of placeholders. The query structure is defined with place holders and then the application specifies the contents of each placeholder. Utilize input validation and if validation fails, do not run the database command. Ensure that variables are strongly typed. Escape m ...
School management system
... School timetabling is a major administrative activity in any school. A number of subjects taught by the corresponding teachers are allocated into a number of available classrooms and a number of timeslots, subject to constraints. The tasks that are considered in constructing the timetable are: ...
... School timetabling is a major administrative activity in any school. A number of subjects taught by the corresponding teachers are allocated into a number of available classrooms and a number of timeslots, subject to constraints. The tasks that are considered in constructing the timetable are: ...
Student Grading System Using ASP.NET Framework
... workflow (including keeping track of session data); (3) Managing all data access for the presentation tier. Data access layer (DAL) provides simplified access to data stored in persistent storage of an entity-relationship database. The DAL encapsulates the complexity of the underlying data store fro ...
... workflow (including keeping track of session data); (3) Managing all data access for the presentation tier. Data access layer (DAL) provides simplified access to data stored in persistent storage of an entity-relationship database. The DAL encapsulates the complexity of the underlying data store fro ...
Natix - Al Akhawayn University
... all the fragments of one list and to search on contentens of nodes control insertions and deletions on this list CSC 5370 XML and Data Management ...
... all the fragments of one list and to search on contentens of nodes control insertions and deletions on this list CSC 5370 XML and Data Management ...
ASP Databases - Mark Dixon`s web site
... Database Management Systems • DBMS provides facilities for: – creating and changing databases • add/remove records • add/remove fields • add/remove data ...
... Database Management Systems • DBMS provides facilities for: – creating and changing databases • add/remove records • add/remove fields • add/remove data ...
VeriCentre 3.0 - Verifone DevNet
... • Simplifies application updates — Application downloads occur in the background — No need for merchant to interface with terminal for download — Will only download if in off hours and other applications allow — Robust error correction (e.g. re-attempt if communication down, mitigation of conflictin ...
... • Simplifies application updates — Application downloads occur in the background — No need for merchant to interface with terminal for download — Will only download if in off hours and other applications allow — Robust error correction (e.g. re-attempt if communication down, mitigation of conflictin ...
CCLRC PowerPoint Template
... Data Access over Heterogeneous Sources Data Model for an ‘ideal’ CRIS CERIF in Use ...
... Data Access over Heterogeneous Sources Data Model for an ‘ideal’ CRIS CERIF in Use ...
Block oriented processing of relational database
... In related work, several papers have proposed new cache-conscious techniques for specific database operations and indexing [5, 15, 171. Techniques such as blocking, loop fusion, and data clustering were found to be important for improving cache locality and performance of aggregation and join algori ...
... In related work, several papers have proposed new cache-conscious techniques for specific database operations and indexing [5, 15, 171. Techniques such as blocking, loop fusion, and data clustering were found to be important for improving cache locality and performance of aggregation and join algori ...
Chapter 0
... - Information gathering, seeking, filtering, collaborative filtering, sense making and visual analytics. - Data mining from data warehouses and data marts. - Knowledge networks or semantic webs. • All the above is complicated by the volume of material to search. ...
... - Information gathering, seeking, filtering, collaborative filtering, sense making and visual analytics. - Data mining from data warehouses and data marts. - Knowledge networks or semantic webs. • All the above is complicated by the volume of material to search. ...
A Building Block for a Model
... panel, a schematic located at the top of the image that shows the entire chromosome (or, in the case of unfinished genomes, a contig) and a number of landmark features such as well-known genetic markers, cytogenetic bands, or sequence scaffolds. He can make finer adjustments by scrolling and zooming ...
... panel, a schematic located at the top of the image that shows the entire chromosome (or, in the case of unfinished genomes, a contig) and a number of landmark features such as well-known genetic markers, cytogenetic bands, or sequence scaffolds. He can make finer adjustments by scrolling and zooming ...
Tuning I/O Subsystem: A Key Component in RDBMS Performance
... should happen during the design stage. Different types of systems have different I/O patterns and require different I/O designs. Once the system is built, you should first tune for memory and then tune for disk I/O. The reason you tune in this order is to make sure that you are not dealing with exce ...
... should happen during the design stage. Different types of systems have different I/O patterns and require different I/O designs. Once the system is built, you should first tune for memory and then tune for disk I/O. The reason you tune in this order is to make sure that you are not dealing with exce ...
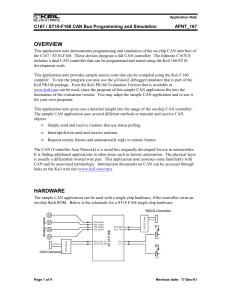
apnt_167.pdf
... straightforward. You may adapt this sample CAN application for your own software projects. You may also convert this application software for other on-chip CAN controllers. The Keil C166/ST10 development tools allow you fast and reliable development of complete applications. With the µVision2 simula ...
... straightforward. You may adapt this sample CAN application for your own software projects. You may also convert this application software for other on-chip CAN controllers. The Keil C166/ST10 development tools allow you fast and reliable development of complete applications. With the µVision2 simula ...
General Index Design Guidelines SQL Server 2005 Experienced
... An xml data type can only be a key column only in an XML index. For more information, see Indexes on xml Data Type Columns. Examine column uniqueness. A unique index instead of a nonunique index on the same combination of columns provides additional information for the query optimizer that makes the ...
... An xml data type can only be a key column only in an XML index. For more information, see Indexes on xml Data Type Columns. Examine column uniqueness. A unique index instead of a nonunique index on the same combination of columns provides additional information for the query optimizer that makes the ...
managing a data warehouse
... The fundamental level of safety that must be put in place is a backup system that automates the process and guarantees that the database can be restored with full data integrity in a timely manner. The first step is to ensure that all of the data sources from which the data warehouse is created are ...
... The fundamental level of safety that must be put in place is a backup system that automates the process and guarantees that the database can be restored with full data integrity in a timely manner. The first step is to ensure that all of the data sources from which the data warehouse is created are ...
Optimizing Data Analysis with a Semi-structured Time Series Database Splunk Inc. Abstract
... timestamped, heterogeneous, and difficult to fit into traditional SQL database. Traditionally, datasets represent state information. They snapshot properties of real-world or virtual objects at some point in time. Some well-known examples of such stateful datasets include store inventories, airline ...
... timestamped, heterogeneous, and difficult to fit into traditional SQL database. Traditionally, datasets represent state information. They snapshot properties of real-world or virtual objects at some point in time. Some well-known examples of such stateful datasets include store inventories, airline ...
Document
... • In the query datasheet, click the arrow on the column heading for the field you want to sort • In the menu that opens, click Sort A to Z for an ascending sort, or click Sort Z to A for a descending sort or • In the query datasheet, select the column or adjacent columns on which you want to sort • ...
... • In the query datasheet, click the arrow on the column heading for the field you want to sort • In the menu that opens, click Sort A to Z for an ascending sort, or click Sort Z to A for a descending sort or • In the query datasheet, select the column or adjacent columns on which you want to sort • ...
Using predictive analytics to improve sales processes and forecasting
... do you have for sellers on similar (same competitor, same product) opportunities? What was the primary factor in winning the deal? Other factors? Impact of Microsoft partners? We then merged the dataset from the past two to three years, ranked survey comments as high impact and high frequency, creat ...
... do you have for sellers on similar (same competitor, same product) opportunities? What was the primary factor in winning the deal? Other factors? Impact of Microsoft partners? We then merged the dataset from the past two to three years, ranked survey comments as high impact and high frequency, creat ...
General
... State A Recognizes that user is requesting data from State B and transmits to the Webtool the Address for State B Webtool Accesses State B User Selects Query to run Based on the query selected, ADAM Server dynamically provides parameter options for the user to select from User selects from parameter ...
... State A Recognizes that user is requesting data from State B and transmits to the Webtool the Address for State B Webtool Accesses State B User Selects Query to run Based on the query selected, ADAM Server dynamically provides parameter options for the user to select from User selects from parameter ...
ch22 - Pearson
... possibly different underlying data models. Occurs when sites have implemented their own databases and integration is considered later. Translations required to allow for: – Different hardware. – Different DBMS products. – Different hardware and products. Typical ...
... possibly different underlying data models. Occurs when sites have implemented their own databases and integration is considered later. Translations required to allow for: – Different hardware. – Different DBMS products. – Different hardware and products. Typical ...
Contributions from Class of 2008
... Our research philosophy involved developing a tool that would not only automate the classification of MIS research, but also offer a lasting repository of seminal MIS literature that future classes could build upon. Our team determined that the best way to accomplish this goal was to develop a relat ...
... Our research philosophy involved developing a tool that would not only automate the classification of MIS research, but also offer a lasting repository of seminal MIS literature that future classes could build upon. Our team determined that the best way to accomplish this goal was to develop a relat ...
Section 6: Database Security - Computer Science
... Statistical database goal: provide aggregate information about groups of individuals E.g., average grade point of students Security risk in statistical database: disclosure of specific information about a particular individual E.g., grade point of student John Smith ...
... Statistical database goal: provide aggregate information about groups of individuals E.g., average grade point of students Security risk in statistical database: disclosure of specific information about a particular individual E.g., grade point of student John Smith ...
Fuzzy Key Linkage: Robust Data Mining Methods for Real Databases
... "Positive", yet does not trigger a referential integrity constraint. The ROBMS validation scheme fails and the error remains unnoticed. Key linkage errors such as these undermine the efforts of data miners to extract interesting and important information from data warehouses and distributed database ...
... "Positive", yet does not trigger a referential integrity constraint. The ROBMS validation scheme fails and the error remains unnoticed. Key linkage errors such as these undermine the efforts of data miners to extract interesting and important information from data warehouses and distributed database ...