Machine Learning Algorithms for In-Database Analytics
... written using standard C++ atomic types as well as vector and matrix types that are native to linear algebra operations. The C++ abstraction layer also provides memory management and exception handling support. Finally, it includes third-party libraries so that developers can write efficient code. ...
... written using standard C++ atomic types as well as vector and matrix types that are native to linear algebra operations. The C++ abstraction layer also provides memory management and exception handling support. Finally, it includes third-party libraries so that developers can write efficient code. ...
Confirm Task Processor
... ConfirmConnect™ product contains the following open source software: • Chromium Embedded Framework, version 3, which is licensed under the New BSD License. The license can be downloaded from http://opensource.org/licenses/BSD-3-Clause. The source code for this software is available from http://code. ...
... ConfirmConnect™ product contains the following open source software: • Chromium Embedded Framework, version 3, which is licensed under the New BSD License. The license can be downloaded from http://opensource.org/licenses/BSD-3-Clause. The source code for this software is available from http://code. ...
slides
... during that transaction are undone. That may not be what you want! – Suppose you want to add an audit record every time someone tries to make some specific kind of change. – You want to add that audit record even if the ...
... during that transaction are undone. That may not be what you want! – Suppose you want to add an audit record every time someone tries to make some specific kind of change. – You want to add that audit record even if the ...
Internship Opportunities in Netherlands, Norway and Denmark
... development. Acquire new skills in various programming languages and environments. Perform Programming and adhere to Programming standards and processes. Interact with Project Manager, Team Lead, System Architect, and Information Architect to develop and implement detailed technical design. Programm ...
... development. Acquire new skills in various programming languages and environments. Perform Programming and adhere to Programming standards and processes. Interact with Project Manager, Team Lead, System Architect, and Information Architect to develop and implement detailed technical design. Programm ...
Liu07 - ETIS publications
... models, because these statistics are used to derive the value of coefficients in cost formulas. It is often DBMS implementers who are able to give accurate cost formulas with indispensable sources statistics. When the data sources are autonomous, cost formulas and source statistics are unavailable. ...
... models, because these statistics are used to derive the value of coefficients in cost formulas. It is often DBMS implementers who are able to give accurate cost formulas with indispensable sources statistics. When the data sources are autonomous, cost formulas and source statistics are unavailable. ...
Relational Modeling
... May be worth 30 GB overhead to keep sales header records if this is a common query structure because both ease-of-use and performance will be enhanced (at some cost in storage)? ...
... May be worth 30 GB overhead to keep sales header records if this is a common query structure because both ease-of-use and performance will be enhanced (at some cost in storage)? ...
Relational Modeling
... May be worth 30 GB overhead to keep sales header records if this is a common query structure because both ease-of-use and performance will be enhanced (at some cost in storage)? ...
... May be worth 30 GB overhead to keep sales header records if this is a common query structure because both ease-of-use and performance will be enhanced (at some cost in storage)? ...
Table of Contents - Computer Science
... were used to keep track of the frequency with which requested data was found in the buffer, thus providing the buffer cache hit ratio. The results of the performance analysis show that several factors can influence the Linux and Oracle buffer cache hit ratios. The larger the database size, the great ...
... were used to keep track of the frequency with which requested data was found in the buffer, thus providing the buffer cache hit ratio. The results of the performance analysis show that several factors can influence the Linux and Oracle buffer cache hit ratios. The larger the database size, the great ...
4 Creating a Simple Query
... SELECT statement is always the same. ❖ Note Many database systems provide extensions to the SQL Standard to allow you to build complex programming statements (such as If . . . Then . . . Else) in functions and stored procedures, but the specific syntax is unique to each different product. It is far ...
... SELECT statement is always the same. ❖ Note Many database systems provide extensions to the SQL Standard to allow you to build complex programming statements (such as If . . . Then . . . Else) in functions and stored procedures, but the specific syntax is unique to each different product. It is far ...
X-FTL: Transactional FTL for SQLite Databases
... considered non-atomic by most contemporary database systems [4, 16]. Atomic propagation of one or more pages updated by a transaction can be implemented by shadow pages or physical logging. However, the cost will be considerable during normal processing. Most commercial database systems adopt a solu ...
... considered non-atomic by most contemporary database systems [4, 16]. Atomic propagation of one or more pages updated by a transaction can be implemented by shadow pages or physical logging. However, the cost will be considerable during normal processing. Most commercial database systems adopt a solu ...
lecture13 - Stanford InfoLab
... • Typically, distributed DBs: – Geographically distributed – Disconnected operation possible – Goal: Data sharing (heterogeneity, autonomy) ...
... • Typically, distributed DBs: – Geographically distributed – Disconnected operation possible – Goal: Data sharing (heterogeneity, autonomy) ...
Run Multiple Microsoft® Applications Simultaneously With Hitachi
... The Microsoft Lync Server 2913 environment consists of three front end Microsoft Lync 2013 servers and one backend Microsoft SQL Server 2014 database server. The environment used to validate this reference architecture also included a dedicated mediation server. A certificate authority server was de ...
... The Microsoft Lync Server 2913 environment consists of three front end Microsoft Lync 2013 servers and one backend Microsoft SQL Server 2014 database server. The environment used to validate this reference architecture also included a dedicated mediation server. A certificate authority server was de ...
StarTrack Next Generation: A Scalable Infrastructure for Track-Based Applications
... representing a set of tracks. Several functions in the API now operate on and return results as track collections. This change had several benefits. Apart from the obvious ease of programming, it afforded StarTrack opportunities to optimize the performance of specific operations through delayed and ...
... representing a set of tracks. Several functions in the API now operate on and return results as track collections. This change had several benefits. Apart from the obvious ease of programming, it afforded StarTrack opportunities to optimize the performance of specific operations through delayed and ...
Data Upload Workbook
... In this step, we'll configure deduplication rules to avoid the creation of duplicate records during data upload. In our case, it's quite sufficient to add just three rules using the Exact Match criterion for company name, person's first name, and person's last name. 1. Configure deduplication by com ...
... In this step, we'll configure deduplication rules to avoid the creation of duplicate records during data upload. In our case, it's quite sufficient to add just three rules using the Exact Match criterion for company name, person's first name, and person's last name. 1. Configure deduplication by com ...
Secure Programming in PHP
... of other files into a script. This section mainly takes care of the risks that the contents of these include files is exposed to attackers and the risk that attackers exploit improper usage of the include statement for injecting their own code. ...
... of other files into a script. This section mainly takes care of the risks that the contents of these include files is exposed to attackers and the risk that attackers exploit improper usage of the include statement for injecting their own code. ...
Sensor Observation Service for Environmental Monitoring Data
... environment, is foremost a Spatial Data Infrastructure (SDI), SWE standards can be used to see how they can contribute accessing to the spatial data in a standardized way. The objective of INSPIRE is to allow for increased accessibility and interoperability within and between organizations and natio ...
... environment, is foremost a Spatial Data Infrastructure (SDI), SWE standards can be used to see how they can contribute accessing to the spatial data in a standardized way. The objective of INSPIRE is to allow for increased accessibility and interoperability within and between organizations and natio ...
A Table with a View
... The Idea of Relationship • A relationship is a correspondence between rows of one table and the rows of another table – Because the key Student_ID is used in each table, can not only find the address for each student (Lives_At), but can also find the student for each address (Home_Of) ...
... The Idea of Relationship • A relationship is a correspondence between rows of one table and the rows of another table – Because the key Student_ID is used in each table, can not only find the address for each student (Lives_At), but can also find the student for each address (Home_Of) ...
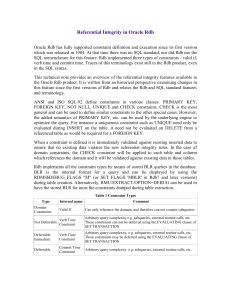
Referential Integrity in Oracle Rdb
... Oracle Rdb has fully supported constraint definition and execution since its first version which was released in 1984. At that time there was no SQL standard, nor did Rdb use the SQL nomenclature for this feature. Rdb implemented three types of constraints - valid if, verb time and commit time. Trac ...
... Oracle Rdb has fully supported constraint definition and execution since its first version which was released in 1984. At that time there was no SQL standard, nor did Rdb use the SQL nomenclature for this feature. Rdb implemented three types of constraints - valid if, verb time and commit time. Trac ...
Content providers Loaders CursorLoaders
... • Every application has its own sandbox and cannot access data from other applications – Content providers make sharing possible - if permission is granted ...
... • Every application has its own sandbox and cannot access data from other applications – Content providers make sharing possible - if permission is granted ...
Slide - CSE, IIT Bombay
... for their matching inner TIDS • An IO queue recording all pending AIO requests made by the node Used to poll for completion of AIO requests ...
... for their matching inner TIDS • An IO queue recording all pending AIO requests made by the node Used to poll for completion of AIO requests ...