IGRP Timers
... IGRP also advertises three types of routes: – interior, system, and exterior. Interior routes are routes between subnets in the network attached to a router interface. If the network attached to a router is not subnetted, IGRP does not advertise interior routes. ...
... IGRP also advertises three types of routes: – interior, system, and exterior. Interior routes are routes between subnets in the network attached to a router interface. If the network attached to a router is not subnetted, IGRP does not advertise interior routes. ...
15. Interior Routing Protocols
... Area – Collection of contiguous networks and hosts plus routers connected to any included network Backbone – contiguous collection of networks not contained in any area, their attached routers and routers belonging to multiple areas ...
... Area – Collection of contiguous networks and hosts plus routers connected to any included network Backbone – contiguous collection of networks not contained in any area, their attached routers and routers belonging to multiple areas ...
Leading the 10T era TextStart Dialogue with Chen Junhua, VP of
... offers a 2.56T port capacity to meet the service requirements in the upcoming two to three years. It can be smoothly upgraded to support cluster routers with more frames, and is currently the best selection for the two-frame cluster system. The NE5000E is now the only cluster router in the industry ...
... offers a 2.56T port capacity to meet the service requirements in the upcoming two to three years. It can be smoothly upgraded to support cluster routers with more frames, and is currently the best selection for the two-frame cluster system. The NE5000E is now the only cluster router in the industry ...
Static Routes
... After hearing a poisoned route, start a holddown timer for that one route. Until the timer expires, do not believe any other routing information about the failed route, because believing that information may cause a routing loop. However, information learned from the neighbor that originally adverti ...
... After hearing a poisoned route, start a holddown timer for that one route. Until the timer expires, do not believe any other routing information about the failed route, because believing that information may cause a routing loop. However, information learned from the neighbor that originally adverti ...
Philip Schoene, PBS
... of the signal as it inspected traffic Resolution – Bypass IDS LTN is responsible for security of the appliances • Only outbound connections allowed • Traffic restricted to specific ports ...
... of the signal as it inspected traffic Resolution – Bypass IDS LTN is responsible for security of the appliances • Only outbound connections allowed • Traffic restricted to specific ports ...
CCNA3 Chapter 1 Introduction to Classless Routing
... CISCO NETWORKING ACADEMY PROGRAM CCNA3: Switching Basics and Intermediate Routing v3.0 ...
... CISCO NETWORKING ACADEMY PROGRAM CCNA3: Switching Basics and Intermediate Routing v3.0 ...
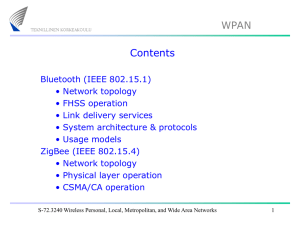
Lecture 2: WPAN
... superframe structure. The format of the superframe is defined by the coordinator. The superframe is bounded by network beacons, sent by the coordinator, and is divided into 16 equally sized slots. The beacon frame is transmitted in the first slot of each superframe. If a coordinator does not wish to ...
... superframe structure. The format of the superframe is defined by the coordinator. The superframe is bounded by network beacons, sent by the coordinator, and is divided into 16 equally sized slots. The beacon frame is transmitted in the first slot of each superframe. If a coordinator does not wish to ...
Design and Implementation of a Fiber to the Home FTTH Access
... WDM PONs are the next generation in the development of access networks. Two flavors of WDM-PON are being studied by Study Group 15 (SG15) of the International Telecommunication Union–Telecommunication Standardization Sector (ITU–T) [15]. The first one is time and wavelength division multiplexing PON ...
... WDM PONs are the next generation in the development of access networks. Two flavors of WDM-PON are being studied by Study Group 15 (SG15) of the International Telecommunication Union–Telecommunication Standardization Sector (ITU–T) [15]. The first one is time and wavelength division multiplexing PON ...
Optical Control Plane Standardization
... • User Network Interface (UNI) 1.0 Signaling Specification (IA, OIF2001.125.7) • NNI Implementation Agreement Proposal for OFC 2003 (OIF2002.476) Connections are established dynamically over • an UNI initiated interface (switched connections) or • an EMS/NMS initiated interface (soft permanent conne ...
... • User Network Interface (UNI) 1.0 Signaling Specification (IA, OIF2001.125.7) • NNI Implementation Agreement Proposal for OFC 2003 (OIF2002.476) Connections are established dynamically over • an UNI initiated interface (switched connections) or • an EMS/NMS initiated interface (soft permanent conne ...
Chapter 1
... • The loop can be a result of: • Incorrectly configured static routes. • Inconsistent routing tables not being updated because of slow convergence in a changing network. • Distance vector routing protocols are simple in their implementation and configuration, but this comes at a price. • Pure distan ...
... • The loop can be a result of: • Incorrectly configured static routes. • Inconsistent routing tables not being updated because of slow convergence in a changing network. • Distance vector routing protocols are simple in their implementation and configuration, but this comes at a price. • Pure distan ...
ch4
... number (64 is current default) which the routers would then decrement, until it reached 0. It purpose is to discard packets that have been circling around and to discard them. • Protocol field identifies the higher level protocol (TCP, UDP) to which this packet should be passed. • Checksum- add the ...
... number (64 is current default) which the routers would then decrement, until it reached 0. It purpose is to discard packets that have been circling around and to discard them. • Protocol field identifies the higher level protocol (TCP, UDP) to which this packet should be passed. • Checksum- add the ...
IPv4
... • IPv4 packets are forwarded by Hitachi proprietary hardware. •Main Processor forward IPv6 packets • IPv6 forwarding is based on software with some hardware logic. • No performance penalty to IPv4 network • Low cost to start for early adopters with investment protection • Flexibility to add IPv6 add ...
... • IPv4 packets are forwarded by Hitachi proprietary hardware. •Main Processor forward IPv6 packets • IPv6 forwarding is based on software with some hardware logic. • No performance penalty to IPv4 network • Low cost to start for early adopters with investment protection • Flexibility to add IPv6 add ...
ZIGBEE GATEWAYS
... All devices in the ZigBee network must have unique 64 bit IEEE addresses. Short 16 bit address can be allocated to reduce packet size. With using this local addresses, simple network have more than 65000 nodes, which they can be configured with reduced address overhead. Only the 16 bit address is us ...
... All devices in the ZigBee network must have unique 64 bit IEEE addresses. Short 16 bit address can be allocated to reduce packet size. With using this local addresses, simple network have more than 65000 nodes, which they can be configured with reduced address overhead. Only the 16 bit address is us ...
Peer-to-Peer Systems
... HHU – Technology of Social Networks – JProf. Dr. Kalman Graffi – Peer-to-Peer Systems – http://tsn.hhu.de/teaching/lectures/2014ws/p2p.html ...
... HHU – Technology of Social Networks – JProf. Dr. Kalman Graffi – Peer-to-Peer Systems – http://tsn.hhu.de/teaching/lectures/2014ws/p2p.html ...
Deployment Status in Singapore
... STATUS (GOVT) Infocomm Development Authority of Singapore, IDA Vision for Infocomm Technology Roadmap “For home technologies to take off, these technologies ….., and that deployment of IPv6 is critical to meet the demand for address, QoS and security” ...
... STATUS (GOVT) Infocomm Development Authority of Singapore, IDA Vision for Infocomm Technology Roadmap “For home technologies to take off, these technologies ….., and that deployment of IPv6 is critical to meet the demand for address, QoS and security” ...
- Mitra.ac.in
... Q.6] Define Enterprise network. Explain in brief Gateway Address and Network Segments. Q.7] What happens if a MAC address is not stored in CAM on a switch ? Explain the difference in store-and-forward and cut-through mode on a switch. Q.8] What is Network Switch? What are modes used to forward Frame ...
... Q.6] Define Enterprise network. Explain in brief Gateway Address and Network Segments. Q.7] What happens if a MAC address is not stored in CAM on a switch ? Explain the difference in store-and-forward and cut-through mode on a switch. Q.8] What is Network Switch? What are modes used to forward Frame ...
The Network Layer
... the same: one hop count per network. c) Each router/node maintains a vector (table) of minimum distances to every node. (the least-cost route btw any nodes is the route with the minimum number of hop-count). d) The hop-count is the number of networks that a packet encounters to reach its destination ...
... the same: one hop count per network. c) Each router/node maintains a vector (table) of minimum distances to every node. (the least-cost route btw any nodes is the route with the minimum number of hop-count). d) The hop-count is the number of networks that a packet encounters to reach its destination ...
group7
... The default router will check the hop count to the Routing Controller and send a GetContent() broadcast message on all the nodes with a TTL = Distance to Routing Controller – 1 The router will flood its connected hosts for a response , If a router that is closer than to the host than the Routing Con ...
... The default router will check the hop count to the Routing Controller and send a GetContent() broadcast message on all the nodes with a TTL = Distance to Routing Controller – 1 The router will flood its connected hosts for a response , If a router that is closer than to the host than the Routing Con ...
Cisco tcs2 - Liberty High School
... is Royal Palm and we will be working it into Shaw Butte as much as possible. There will be data connectivity between all schools. The WAN will be based on a 2-layer hierarchical model. Regional hubs will be established for Shaw Butte, the District Office/Data Center, and Service Center to form a ver ...
... is Royal Palm and we will be working it into Shaw Butte as much as possible. There will be data connectivity between all schools. The WAN will be based on a 2-layer hierarchical model. Regional hubs will be established for Shaw Butte, the District Office/Data Center, and Service Center to form a ver ...
module10-rip
... • Routing between AS’s • Assumes that the Internet consists of a collection of interconnected AS’s • Normally, there is one dedicated router in each AS that handles interdomain traffic. • Protocols for interdomain routing are also called Exterior Gateway Protocols or EGP’s. • Routing protocols: – EG ...
... • Routing between AS’s • Assumes that the Internet consists of a collection of interconnected AS’s • Normally, there is one dedicated router in each AS that handles interdomain traffic. • Protocols for interdomain routing are also called Exterior Gateway Protocols or EGP’s. • Routing protocols: – EG ...