Slides - Duke Computer Science
... • Example: – Policy #1: use C as egress point for traffic from AS X – Policy #2: enable ECMP for A-C flow ...
... • Example: – Policy #1: use C as egress point for traffic from AS X – Policy #2: enable ECMP for A-C flow ...
Security+ Guide to Network Security Fundamentals
... Encrypts and encapsulates a network protocol within packets carried by second network Best-known example: virtual private networks Replacing WAN links because of security and low cost An option for most IP connectivity requirements ...
... Encrypts and encapsulates a network protocol within packets carried by second network Best-known example: virtual private networks Replacing WAN links because of security and low cost An option for most IP connectivity requirements ...
Chap 11: Network Security Topologies
... Explain network perimeter’s importance to an organization’s security policies Identify place and role of the demilitarized zone in the network Explain how network address translation is used to help secure networks Spell out the role of tunneling in network security Describe security features of vir ...
... Explain network perimeter’s importance to an organization’s security policies Identify place and role of the demilitarized zone in the network Explain how network address translation is used to help secure networks Spell out the role of tunneling in network security Describe security features of vir ...
Document
... standards, and internet became reality • 1990’s - Commercial networks such as CompuServe and Prodigy became part of the internet; users of these networks could only communicate with those using the same service. ...
... standards, and internet became reality • 1990’s - Commercial networks such as CompuServe and Prodigy became part of the internet; users of these networks could only communicate with those using the same service. ...
chap4_presentation_sumana
... While at work, majority of the telephone calls made by employees are for intra-company communication! It is feasible for medium to large businesses to have their own telephone exchange. ...
... While at work, majority of the telephone calls made by employees are for intra-company communication! It is feasible for medium to large businesses to have their own telephone exchange. ...
notes
... EEC-484/584 Computer Networks Lecture 3 Wenbing Zhao [email protected] (Part of the slides are based on Drs. Kurose & Ross’s slides for their Computer Networking book) ...
... EEC-484/584 Computer Networks Lecture 3 Wenbing Zhao [email protected] (Part of the slides are based on Drs. Kurose & Ross’s slides for their Computer Networking book) ...
15-744: Computer Networking
... •R3 can tell R1 and R2 prefixes from R4 •R3 can tell R4 prefixes from R1 and R2 •R3 cannot tell R2 prefixes from R1 •R2 can only find these prefixes through a direct connection to R1 •Result: I-BGP routers must be fully connected (via TCP)! • contrast with E-BGP sessions that map to physical links ...
... •R3 can tell R1 and R2 prefixes from R4 •R3 can tell R4 prefixes from R1 and R2 •R3 cannot tell R2 prefixes from R1 •R2 can only find these prefixes through a direct connection to R1 •Result: I-BGP routers must be fully connected (via TCP)! • contrast with E-BGP sessions that map to physical links ...
Computer Network
... Abramson and colleagues at the University of Hawaii. In July 1976, Robert Metcalfe and David Boggs published their paper "Ethernet: Distributed Packet Switching for Local Computer Networks" and collaborated on several patents received in 1977 and 1978. In 1979, Robert Metcalfe pursued making Etherne ...
... Abramson and colleagues at the University of Hawaii. In July 1976, Robert Metcalfe and David Boggs published their paper "Ethernet: Distributed Packet Switching for Local Computer Networks" and collaborated on several patents received in 1977 and 1978. In 1979, Robert Metcalfe pursued making Etherne ...
Networks
... The message is split up into packets using notecards: Five words to a packet Each packet also contains the name of the sender and the receiver, as well as the packet number. The routers transmit these packets to the receiving host. They may lose packets or corrupt them by scribbling out or rewri ...
... The message is split up into packets using notecards: Five words to a packet Each packet also contains the name of the sender and the receiver, as well as the packet number. The routers transmit these packets to the receiving host. They may lose packets or corrupt them by scribbling out or rewri ...
WB_intro
... served traditional voice networks well, but gradually becoming outdated by new technology ...
... served traditional voice networks well, but gradually becoming outdated by new technology ...
Chapter1R
... Internet transfer of individual block of information Internet reliable transfer of a stream of bytes Real-time transfer of a voice signal E-mail & web build on reliable stream service Fax and modems build on basic telephone service ...
... Internet transfer of individual block of information Internet reliable transfer of a stream of bytes Real-time transfer of a voice signal E-mail & web build on reliable stream service Fax and modems build on basic telephone service ...
Network_Hist
... and Portal were formed to provide service to the regional research networks and provide alternate network access (like UUCP-based email and Usenet News) to the public The first dial-up ISP, world.std.com, opened in 1989 By 1994, the NSFNet lost its standing as the backbone of the Internet. Other com ...
... and Portal were formed to provide service to the regional research networks and provide alternate network access (like UUCP-based email and Usenet News) to the public The first dial-up ISP, world.std.com, opened in 1989 By 1994, the NSFNet lost its standing as the backbone of the Internet. Other com ...
Internet Architecture
... Each application is effectively setting up its own network. But until now there is little work on simultaneous routing on many overlapping graphs Discovery How do applications discover and bind to a set of resources? ...
... Each application is effectively setting up its own network. But until now there is little work on simultaneous routing on many overlapping graphs Discovery How do applications discover and bind to a set of resources? ...
514-25-Wrap
... • Route target – tag routes for import/export • Route distinguisher – distinguish routes of separate customers – A customer’s address space may overlap with another’s, without interfering – E.g. private addresses ...
... • Route target – tag routes for import/export • Route distinguisher – distinguish routes of separate customers – A customer’s address space may overlap with another’s, without interfering – E.g. private addresses ...
Chapter 1 Introduction 1.1
... A network is a set of devices (often referred to as nodes) connected by communication links. A node can be a computer, printer, or any other device capable of sending and/or receiving data generated by other nodes on the network. Topics discussed in this section: Distributed Processing Network Crite ...
... A network is a set of devices (often referred to as nodes) connected by communication links. A node can be a computer, printer, or any other device capable of sending and/or receiving data generated by other nodes on the network. Topics discussed in this section: Distributed Processing Network Crite ...
Computer network
... Verizon, GTE, British Telecom, and IBM Internet service provider (ISP) An organization providing access to the Internet ...
... Verizon, GTE, British Telecom, and IBM Internet service provider (ISP) An organization providing access to the Internet ...
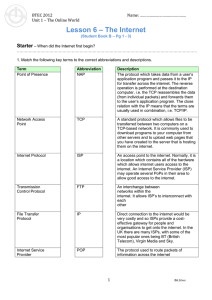
The Internet
... Internet Service Provider An Internet Service Provider (ISP) is a company which provides access to the internet for individuals or other companies (e.g. BT). An ISP will have many servers to do different things depending on the size of the company and amount of customers, e.g. one for outgoing email ...
... Internet Service Provider An Internet Service Provider (ISP) is a company which provides access to the internet for individuals or other companies (e.g. BT). An ISP will have many servers to do different things depending on the size of the company and amount of customers, e.g. one for outgoing email ...
Telecommunications and Networking - University of Baltimore Home
... productivity. “No laptop” policies for important meetings. Enormous pressure within companies to provide Wi-Fi in all areas of the company. Which employees have compelling needs for Wi-Fi access Cost exceeds the benefit to be gained by providing Wi-Fi such as in a manufacturing plant that would ...
... productivity. “No laptop” policies for important meetings. Enormous pressure within companies to provide Wi-Fi in all areas of the company. Which employees have compelling needs for Wi-Fi access Cost exceeds the benefit to be gained by providing Wi-Fi such as in a manufacturing plant that would ...
Communications & Networks
... people in remote areas • Some people can’t afford the cost so a gap could form between the “Information Rich” and the “Information Poor” • Some people believe that computers ...
... people in remote areas • Some people can’t afford the cost so a gap could form between the “Information Rich” and the “Information Poor” • Some people believe that computers ...