A Survey of Operating Systems Infrastructure for Embedded Systems
... specify criteria that can be used to judge the operation of a system, rather than specific behaviors. In general, non-functional requirements define how a system is supposed to be. Non-functional requirements are often called qualities of a system. A system for Cardiac tele-monitoring may be require ...
... specify criteria that can be used to judge the operation of a system, rather than specific behaviors. In general, non-functional requirements define how a system is supposed to be. Non-functional requirements are often called qualities of a system. A system for Cardiac tele-monitoring may be require ...
Bee: A Best Effort Peer-to-Peer Delivery Protocol for Internet Data
... to disseminate it to other N peers, how can we minimize the time it takes for all peers to have the complete file? In the Internet environment, several characteristics make it hard to design a scalable protocol that configure resources (such as computing power and network bandwidth) for disseminatin ...
... to disseminate it to other N peers, how can we minimize the time it takes for all peers to have the complete file? In the Internet environment, several characteristics make it hard to design a scalable protocol that configure resources (such as computing power and network bandwidth) for disseminatin ...
course-file-distributed-system
... computational entities are called computers or nodes. A distributed system may have a common goal, such as solving a large computational problem. Alternatively, each computer may have its own user with individual needs, and the purpose of the distributed system is to coordinate the use of shared res ...
... computational entities are called computers or nodes. A distributed system may have a common goal, such as solving a large computational problem. Alternatively, each computer may have its own user with individual needs, and the purpose of the distributed system is to coordinate the use of shared res ...
Improving Gnutella Protocol: Protocol Analysis And Research Proposals
... incapacitated. In addition, this central point has a complete authority over the data distributed through the network and is solely responsible for its contents (Napster’s legal problems stem from this fact). A solution to providing QoS in the peer-to-peer environment is by using a decentralized mod ...
... incapacitated. In addition, this central point has a complete authority over the data distributed through the network and is solely responsible for its contents (Napster’s legal problems stem from this fact). A solution to providing QoS in the peer-to-peer environment is by using a decentralized mod ...
Slide - SmartLab
... • The overlay hop between peers on the surface resulted in many IP hops at the network layer which led to extremely long end-to-end delays • The design was adequate for large/medium implicit groups but required too much overhead for small groups ...
... • The overlay hop between peers on the surface resulted in many IP hops at the network layer which led to extremely long end-to-end delays • The design was adequate for large/medium implicit groups but required too much overhead for small groups ...
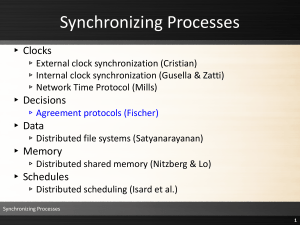
Lecture 14 - The University of Texas at Dallas
... ▸ Cache coherence is maintained by the use of callbacks ▸ Clients dynamically find files on servers and cache location information ▸ Token-based authentication and end-to-end encryption are used for security ...
... ▸ Cache coherence is maintained by the use of callbacks ▸ Clients dynamically find files on servers and cache location information ▸ Token-based authentication and end-to-end encryption are used for security ...
4.5 distributed mutual exclusion
... In software, a logical ring is constructed in which each process is assigned a position in the ring, as shown in the previous Fig. The ring positions may be allocated in numerical order of network addresses or some other means. It does not matter what the ordering is. All that matters is that each p ...
... In software, a logical ring is constructed in which each process is assigned a position in the ring, as shown in the previous Fig. The ring positions may be allocated in numerical order of network addresses or some other means. It does not matter what the ordering is. All that matters is that each p ...
SIP2007-keynote - Columbia University
... fair amount of not-invented-here syndrome • late to recognize wide usage of XML and web standards • late to deal with NATs • security tends to be per-protocol (silo) ...
... fair amount of not-invented-here syndrome • late to recognize wide usage of XML and web standards • late to deal with NATs • security tends to be per-protocol (silo) ...
PPT
... • The channel capacity between the relays and the destinations scales linearly with min(N,L), where N is the number of relays • How does R-DSM work in PHY? – Two-hop network: SISO transmission from source to relays first, followed by relays transmitting together to the destination using R-DSM. – Eac ...
... • The channel capacity between the relays and the destinations scales linearly with min(N,L), where N is the number of relays • How does R-DSM work in PHY? – Two-hop network: SISO transmission from source to relays first, followed by relays transmitting together to the destination using R-DSM. – Eac ...
2.6 Major Design Issues
... The problem of failures can be alleviated if there is redundancy in the system. The system should transparently handle failures ...
... The problem of failures can be alleviated if there is redundancy in the system. The system should transparently handle failures ...