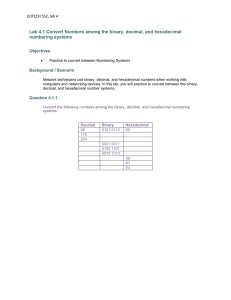
EDTECH 552, lab 4 Lab 4.1 Convert Numbers among the binary
... The host portion of the IPv6 address is called the Interface ID, because it does not identify the actual host, but rather the host’s network interface card. Each network interface can have multiple IPv6 addresses, and therefore, can also have multiple interface IDs. ...
... The host portion of the IPv6 address is called the Interface ID, because it does not identify the actual host, but rather the host’s network interface card. Each network interface can have multiple IPv6 addresses, and therefore, can also have multiple interface IDs. ...
- IEEE Mentor
... The WLAN must be able to collect charging information and send it across this interface to the home AAA server. There is a suggestion, however, that the Packet Data Gateway (PDGW) should collect charging information. This would require all user plane traffic to go across the Wn interface, which woul ...
... The WLAN must be able to collect charging information and send it across this interface to the home AAA server. There is a suggestion, however, that the Packet Data Gateway (PDGW) should collect charging information. This would require all user plane traffic to go across the Wn interface, which woul ...
3GPP TSG-SA2 Meeting #30
... The WLAN must be able to collect charging information and send it across this interface to the home AAA server. There is a suggestion, however, that the Packet Data Gateway (PDGW) should collect charging information. This would require all user plane traffic to go across the Wn interface, which woul ...
... The WLAN must be able to collect charging information and send it across this interface to the home AAA server. There is a suggestion, however, that the Packet Data Gateway (PDGW) should collect charging information. This would require all user plane traffic to go across the Wn interface, which woul ...
CCNA2 Chapter 1 Wide Area Networks and Routers
... An internetwork must include: • switching • dynamic or static routing • consistent end-to-end addressing ...
... An internetwork must include: • switching • dynamic or static routing • consistent end-to-end addressing ...
Digi One TS/ PortServer TS 2/4 Setup Card
... limits for Class A digital devices pursuant to Part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential environment. This equipment generates, uses, and can radiate radio frequency energy, and if not installed and used in acco ...
... limits for Class A digital devices pursuant to Part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential environment. This equipment generates, uses, and can radiate radio frequency energy, and if not installed and used in acco ...
PPT Version
... • The E.164 Numbering Plan guaranties that every endpoint can be reached globally from any other end-point • Therefore the E.164 Numbering Plan has a hierarchical structure used for routing (and billing) • Digit analysis in one network provides the route to the next network, to the area, to the dest ...
... • The E.164 Numbering Plan guaranties that every endpoint can be reached globally from any other end-point • Therefore the E.164 Numbering Plan has a hierarchical structure used for routing (and billing) • Digit analysis in one network provides the route to the next network, to the area, to the dest ...
appendix a: wlan-related terminology - University of Houston
... a. Manual Key Management: Keys need to be entered manually on all the clients and Access Points. Such key management overhead may result in WEP keys that are not changed frequently. b. Key Size: The IEEE 802.11 design community blames 40-bit RC4 keys for this and recommends using 104 or 128-bit RC4 ...
... a. Manual Key Management: Keys need to be entered manually on all the clients and Access Points. Such key management overhead may result in WEP keys that are not changed frequently. b. Key Size: The IEEE 802.11 design community blames 40-bit RC4 keys for this and recommends using 104 or 128-bit RC4 ...
Group 1C
... • Allowing the Network to be further exposed by the Decoy system (preventing jump-off attacks) – Need to consider where in the system architecture the decoy system is placed • We are assuming that intruders are ‘hacking in’, rather than the perpetrator being inside the organisation. • Can Either pla ...
... • Allowing the Network to be further exposed by the Decoy system (preventing jump-off attacks) – Need to consider where in the system architecture the decoy system is placed • We are assuming that intruders are ‘hacking in’, rather than the perpetrator being inside the organisation. • Can Either pla ...
Q58 Generation Interconnection
... Point of Interconnection (POI) for this project would be at the proposed future Qx 500kV switchyard. The IC has chosen to interconnect as an Energy Resource. Delivery of the Q58 output beyond the POI would be on an “as-available” basis only. There are three participants in the Hassayampa – North Gil ...
... Point of Interconnection (POI) for this project would be at the proposed future Qx 500kV switchyard. The IC has chosen to interconnect as an Energy Resource. Delivery of the Q58 output beyond the POI would be on an “as-available” basis only. There are three participants in the Hassayampa – North Gil ...
Internet & Web Protocols - University of Liverpool
... • a domain name server (DNS) is a machine that keeps a table of names and corresponding IP addresses (i.e. this performs the “look up” to match domain names to their corresponding IP address) there are 13 root servers in the world while there are only 13 root servers, there are multiple physical ...
... • a domain name server (DNS) is a machine that keeps a table of names and corresponding IP addresses (i.e. this performs the “look up” to match domain names to their corresponding IP address) there are 13 root servers in the world while there are only 13 root servers, there are multiple physical ...
Peer-to-Peer network systems
... • Direct connect clients connect to a central hub and can download files directly from one another • Hubs feature a list of clients or users connected to them. Users can search for files and download them from other clients, as well as chat with other users. ...
... • Direct connect clients connect to a central hub and can download files directly from one another • Hubs feature a list of clients or users connected to them. Users can search for files and download them from other clients, as well as chat with other users. ...
2006-05-Digital Signage Glossary
... demonstration, education (consumers, sales staff, etc.) profile through media, events, etc., co-branding, etc. The measures of branding success include revenues, customer base, share of category revenues, category growth, awareness and perception of brand. Business Model: (see also Ad model, Venue M ...
... demonstration, education (consumers, sales staff, etc.) profile through media, events, etc., co-branding, etc. The measures of branding success include revenues, customer base, share of category revenues, category growth, awareness and perception of brand. Business Model: (see also Ad model, Venue M ...
Internet basic definitions - An
... on a host (port 80 by default; see List of TCP and UDP port numbers .)An HTTP server listening on that port waits for the client to send a request message. Upon receiving the request, the server sends back a status line, such as "HTTP/1.1 200 OK", and a message of its own, the body of which is perha ...
... on a host (port 80 by default; see List of TCP and UDP port numbers .)An HTTP server listening on that port waits for the client to send a request message. Upon receiving the request, the server sends back a status line, such as "HTTP/1.1 200 OK", and a message of its own, the body of which is perha ...
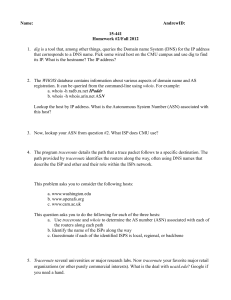
doc - Andrew.cmu.edu
... Systems (ASes). Our hacker has each AS “hijack” several IP blocks. That is, each AS under his or her control announces via BGP that it owns IP blocks for which it does not. For example, our hacker has AS (CMU) announce a one-hop path to the IP block 18.0.0.0/8 (MIT). (a) Assuming that the AS graph s ...
... Systems (ASes). Our hacker has each AS “hijack” several IP blocks. That is, each AS under his or her control announces via BGP that it owns IP blocks for which it does not. For example, our hacker has AS (CMU) announce a one-hop path to the IP block 18.0.0.0/8 (MIT). (a) Assuming that the AS graph s ...
Storage Aware Protocols For heterogeneous networks
... • Send each batch using hop by hop reliability • Exchange end-to-end acknowledgements to maintain states at ...
... • Send each batch using hop by hop reliability • Exchange end-to-end acknowledgements to maintain states at ...
Content delivery network interconnection

Content delivery network interconnection (CDNI) is a set of interfaces and mechanisms required for interconnecting two independent content delivery networks (CDNs) that enables one to deliver content on behalf of the other. Interconnected CDNs offer many benefits, such as footprint extension, reduced infrastructure costs, higher availability, etc., for content service providers (CSPs), CDNs, and end users. Among its many use cases, it allows small CDNs to interconnect and provides services for CSPs that allows them to compete against the CDNs of global CSPs.